This post provides details on the malicious Mac process called Maftask (Maf-Task), explains what it has to do with Spchlpr, Hlpradc, hiprade, helperamc and helpermcp viruses, and includes removal steps.
Update:
| Threat Profile | |
|---|---|
| Name | Mac Auto Fixer fake system utility |
| Category | Mac scareware, rogue system cleaner |
| Malicious process name | Maftask |
| Detection | Avast: MacOS:AMC-DK [PUP], BitDefender: Adware.MAC.Generic.12496, ESET: A Variant Of OSX/GT32SupportGeeks.B, Microsoft: PUA:MacOS/AMCleaner.B!MTB, Sophos: AdvancedMacCleaner (PUA), Symantec: OSX.Trojan.Gen.2 |
| Symptoms | Displays misleading scan reports and follow-up alerts, deteriorates system performance, redirects web browser to unwanted sites |
| Distribution Techniques | Freeware bundles, torrents, booby-trapped software updates, misleading popup ads, spam |
| Severity Level | Medium |
| Damage | Mac slowdown, obtrusive alerts, privacy issues due to Internet activity tracking, browser redirects, redundant online ads |
| Removal | Scan your Mac with Combo Cleaner to detect all files related to the browser hijacker. Use the tool to remove the infection if found. |
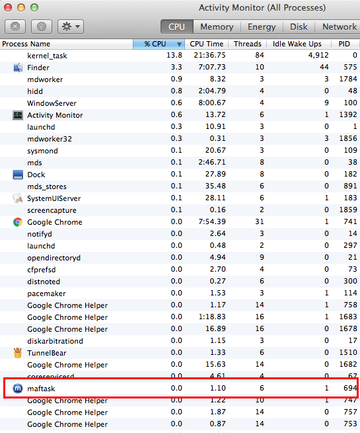
Underestimating the capabilities and complexity of Mac malware is a slippery slope. The threat actors who zero in on the Apple ecosystem are becoming increasingly tech-savvy, and their malicious code can assume different shapes to evade detection and prevent termination. Mac Auto Fixer, one of the fairly sophisticated samples from that category, injects its tentacles deep inside a host system and sprinkles concomitant files and processes in order to persevere. Some victims fail to notice these extra fragments of the infection, but those who look for them typically spot an executable file named “maftask” or "maf-task". It is listed among the running processes in the contaminated Mac’s Activity Monitor, and another entry “com.techyutil.maftask.plist” is going to end up in the LaunchDaemons.
So, the actual culprit’s name is Mac Auto Fixer, and it’s embodied on the system level as the Maftask process – no wonder some users refer to the latter as the troublemaker. The conspicuously misbehaving application is a mix of a rogue optimization tool and pseudo security software. It pretends to find a bevy of macOS performance issues as well as privacy and malware problems, thus attempting to persuade the victim that purchasing its license is certainly on their to-do list. It boasts sleek GUI design and triggers trustworthy-looking system scans over and over.
Maftask may re-infect your Mac multiple times unless you delete all of its fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.The reports enumerate hundreds of items that should supposedly be deleted or fixed at once, including duplicates, unnecessary login items, failed downloads and memory issues. To top it all off, the Maftask virus will state there is too little available space left and urge the user to have memory released in one click.
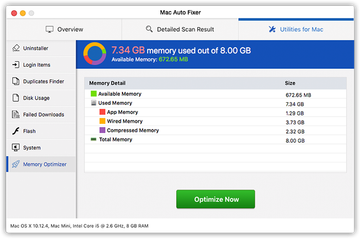
The pseudo scanning activity of Mac Auto Fixer (Maf-task) malware is accompanied by numerous popups that further pressure the user into taking immediate action. The alerts typically mention the number of threats and issues spotted in specific system areas and recommend the victim to sort them all out by registering the full version of the program. The infection can also impact the web surfing facet of Mac usage by rerouting traffic to spoof warning pages. The motivation behind this adverse effect is two-pronged. One the one hand, the threat tries to complement its activity with extra pressure by making the victim visit sites reporting various system performance issues and malware. On the other hand, its operators may want to monetize their foothold in the Mac by generating unique hits to legit search providers, such as Yahoo or Bing, via advertising networks. Long story short, Maftask deploys a great deal of brainwashing to dupe and intimidate the owner of the infected computer into coughing up a registration fee. Therefore, following those annoying prompts is a bad idea because most of the problems are phony and the only real adversary is the alleged Mac performance booster itself.
Another massive surge of Maftask infections after the original outbreak of the Mac Auto Fixer malware took root in early October 2019 and has been a consistently serious concern ever since. According to the victims’ reports, this twist in the dodgy campaign is accompanied by malicious activity of the following processes:
- hlpradc
- spchlpr
- hiprade
- helperamc
- helpermcp
- ummhlpr
- sspchlpr
- APMHelper
- smbstrhlpr
- MapsAndDirections-1668307
- ProntoApp
- WebSocketServerApp
- FocusReportingService
- CellularService
- EasyConverter-955179
- freeForm-959837
- macalive
- tonictasks
- mohip
- source.app
- kernel_task
- mds_stores
- WindowServer
Most of the above-mentioned files are executables used by widespread adware apps and counterfeit system cleaners, including Smart Mac Booster, Unpollute My Mac, Mac Cleanup Pro, Mac Ads Cleaner, and Advanced Mac Cleaner. These harmful programs often tailgate into Macs along with Mac Auto Fixer, coming in the same bundle that conceals the opportunistic infections. Therefore, it is important to check your Mac for these dangerous extras in case maftask is on board.
The main symptom is an emergence of popup alerts saying, “maftask will damage your computer. You should move it to the Trash”, where the name of the perpetrating executable can be either one of the above-mentioned harmful processes (“[harmful process name] will damage your computer”). By the way, Spchlpr is the name of the binary used by Similar Photo Cleaner, a notorious fake optimization tool for Mac.
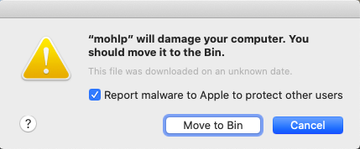
It’s worth mentioning that all of these incidents have one thing in common: they co-occured with an upgrade to macOS Catalina 10.15, the latest major release of the operating system. These alerts may be a response of the brand-new macOS version to the viruses that ran undetected prior to the installation of Catalina on pre-infected computers. The good news is that Apple appears to be improving the malware identification features of their platform, but the infected users are stuck with the annoying alerts anyway.
The Maftask virus penetrates into a Mac by means of tricky installation clients. Their nasty gist boils down to combining benign apps with harmful ones under a single umbrella. The regular program is the only one clearly indicated in the setup wizard, while the Mac Auto Fixer baddie lurks down in its settings that you have to spend time toggling. In summary, Maftask is a component of a dangerous and obnoxious Mac scareware, so it should be treated accordingly. Continue reading this entry to learn how to remove the pest and scotch its impact at the browser level.
Maftask virus manual removal for Mac
The steps listed below will walk you through the removal of this malicious application. Be sure to follow the instructions in the specified order.
Expand the Go menu in your Mac’s Finder bar and select Utilities as shown below.

Locate the Activity Monitor icon on the Utilities screen and double-click on it.

In the Activity Monitor app, look for maftask or another process that appears suspicious. To narrow down your search, focus on unfamiliar resource-intensive entries on the list. Keep in mind that its name isn’t necessarily related to the way the threat is manifesting itself, so you’ll need to trust your own judgement. If you pinpoint the culprit, select it and click on the Stop icon in the upper left-hand corner of the screen.

When a follow-up dialog pops up asking if you are sure you want to quit the troublemaking process, select the Force Quit option.

Click on the Go menu icon in the Finder again and select Go to Folder. You can as well use the Command-Shift-G keyboard shortcut.

Type /Library/LaunchAgents in the folder search dialog and click on the Go button.

Examine the contents of the LaunchAgents folder for dubious-looking items. Be advised that the names of files spawned by malware may give no clear clues that they are malicious, so you should look for recently added entities that appear to deviate from the norm.
As an illustration, here are several examples of LaunchAgents related to mainstream Mac infections: com.techyutil.maftask.plist, com.techyutil.mafuninstaller.plist, com.pcv.hlpramc.plist, com.updater.mcy.plist, com.avickUpd.plist, and com.msp.agent.plist. If you spot files that don’t belong on the list, go ahead and drag them to the Trash.

Use the Go to Folder lookup feature again to navigate to the folder named ~/Library/Application Support (note the tilde symbol prepended to the path).

When the Application Support directory is opened, identify recently generated suspicious folders in it and send them to the Trash. A quick tip is to look for items whose names have nothing to do with Apple products or apps you knowingly installed. A few examples of known-malicious folder names are Mac Auto Fixer, ProgressSite, and IdeaShared.

Enter ~/Library/LaunchAgents string (don’t forget to include the tilde character) in the Go to Folder search area.

The system will display LaunchAgents residing in the current user’s Home directory. Look for dodgy items related to maftask virus (see logic highlighted in subsections above) and drag the suspects to the Trash.

Type /Library/LaunchDaemons in the Go to Folder search field.

In the LaunchDaemons path, try to pinpoint the files the malware is using for persistence. Several examples of such items cropped by Mac infections are com.techyutil.maftask.plist, com.pplauncher.plist, com.startup.plist, and com.ExpertModuleSearchDaemon.plist. Delete the sketchy files immediately.

Click on the Go menu icon in your Mac’s Finder and select Applications on the list.

Find the entry for MacAutoFixer or another app that clearly doesn’t belong there and move it to the Trash. If this action requires your admin password for confirmation, go ahead and enter it.

Expand the Apple menu and select System Preferences.


Proceed to Users & Groups and click on the Login Items tab.


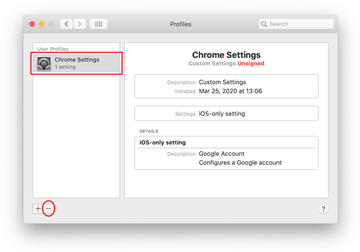
Now select Profiles under System Preferences. Look for a malicious item in the left-hand sidebar. Several examples of configuration profiles created by Mac adware include TechSignalSearch, MainSearchPlatform, AdminPrefs, and Chrome Settings. Select the offending entity and click on the minus sign at the bottom to eliminate it.

Get rid of Maftask virus in web browser on Mac
To begin with, the web browser settings taken over by the Maftask virus should be restored to their default values. Although this will clear most of your customizations, web surfing history, and all temporary data stored by websites, the malicious interference should be terminated likewise. The overview of the steps for completing this procedure is as follows:
- Remove Maftask virus from Safari
Open the browser and go to Safari menu. Select Preferences in the drop-down list.

Once the Preferences screen appears, click on the Advanced tab and enable the option saying “Show Develop menu in menu bar”.

Now that the Develop entry has been added to the Safari menu, expand it and click on Empty Caches.

Now select History in the Safari menu and click on Clear History in the drop-down list.

Safari will display a dialog asking you to specify the period of time this action will apply to. Select all history to ensure a maximum effect. Click on the Clear History button to confirm and exit.

Go back to the Safari Preferences and hit the Privacy tab at the top. Find the option that says Manage Website Data and click on it.

The browser will display a follow-up screen listing the websites that have stored data about your Internet activities. This dialog additionally includes a brief description of what the removal does: you may be logged out of some services and encounter other changes of website behavior after the procedure. If you’re okay with that, go ahead and click on the Remove All button.

Restart Safari
- Remove Maftask in Google Chrome
Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down

When on the Settings pane, select Advanced
Scroll down to the Reset settings section.

Confirm the Chrome reset on a dialog that will pop up. When the procedure is completed, relaunch the browser and check it for malware activity.

- Remove Maftask from Mozilla Firefox
Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).


When on the Troubleshooting Information screen, click on the Refresh Firefox button.

Confirm the intended changes and restart Firefox.
Use automatic tool to uninstall Maftask virus from your Mac
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove Maftask virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the Maftask issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove Maftask threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.
FAQ
How do you close a Maftask?
In most cases, you can close the Maftask process by going to the Activity Monitor from your Mac’s Utilities screen, selecting the unwanted entry and clicking the ‘Quit Process’ button. On a confirmation dialog, select the ‘Force Quit’ option to terminate the stubborn executable. Keep in mind, though, that Maftask will most likely reappear on your running processes list unless you apply the appropriate malware removal procedure.
To get rid of Maftask for good, you need to uninstall the underlying fake system utility called Mac Auto Fixer that relies on the offensive binary in question. Aside from closing the malicious process in the Activity Monitor, remove the core program from your Applications and Login Items as explained in the guide above. Consider emptying the Trash when done.
What is hlpradc?
Hlpradc is a malicious process used by a rogue application called Advanced Mac Cleaner or one of its variants. The affiliated scareware programs that are known to utilize this executable include Mac Ads Cleaner and Mac Adware Cleaner. Although the names differ, the behavior and objectives of these apps are nearly identical. They all report numerous security and performance issues on a Mac and try to dupe the victim into purchasing their license. Obviously, if you discover ‘hlpradc’ among the processes running on your Mac computer, be sure to terminate it immediately and proceed with removing the associated harmful app.
What is helperamc/helpermcp?
Helperamc/helpermcp is an entity mentioned on macOS security alerts stating that it will damage your computer and recommending you to move it to the Trash without delay. These notices are being mostly reported by people who have just installed macOS Catalina 10.15 released in October 2019. It appears that this build of the operating system has introduced a new approach to handling suspicious software previously installed on the Mac. If it cannot verify the app publisher, it will most likely trigger an alert like that.
It turns out that ‘helperamc(helpermcp)’ is a process launched by a phony system utility or adware program once it infiltrates a Mac. Unfortunately, the victims are unable to delete it by simply clicking the ‘Move to Trash’ button on the system popups mentioned above. Instead, those infected should leverage an antimalware tool to sort out the problem, or search for ‘hiprade’ on their hard drive and erase all the detected files manually. It’s recommended to empty the Trash afterward.
What is Spchlpr?
Spchlpr is an executable file of an aggressive pseudo optimizer called Similar Photo Cleaner. The telltale sign of this malware’s activity comes down to recurrent system scans and popup alerts that raise red flags on serious disk space issues due to large and unused images stored on the computer. However, the infection concocts all of these problems in order to pressure the victim into buying its full version, which will supposedly unlock the cleanup feature. Be advised that these notifications about memory improvement potential are a bluff.
Speaking of the ‘spchlpr’ process, it is merely one of the symptoms of the malware attack. To remove Similar Photo Cleaner junk from your Mac, you need to stop this executable first and then get down to eradicating the rest of the culprit’s components.
![How to remove Maftask virus process from Mac [Apr 2020]](/img/bBZnfSnhft-360-remove-maftask-malware-process.png)