This is a complete knowledgebase covering the features of Mac Auto Fixer virus and providing intuitive manual and automatic instructions to remove it from Mac.
Update:
| Threat Profile | |
|---|---|
| Name | Mac Auto Fixer |
| Category | Mac scareware, rogue system cleaner |
| Symptoms | Displays fake scan reports, triggers follow-up alerts pushing the licensed version, redirects browsers to junk services |
| Distribution Techniques | Freeware bundles, pirated apps, fake virus detection alerts online, booby-trapped software updates |
| Severity Level | Medium |
| Damage | Mac slowdown, browser takeover, personally identifiable data (PID) harvesting |
| Removal | Scan your Mac with Combo Cleaner to detect all files related to the Mac Auto Fixer. Use the tool to remove the infection if found. |
The threat actors who masterminded the Mac Auto Fixer malware campaign apparently have some strong cybercriminal background and decent coding skills. Here is what proves this unsettling assumption. The application itself appears to be competently designed and gives you the delusive impression that it’s worth a shot to keep a Mac running smooth. Meanwhile, it obviously inherits multiple hallmarks of a rogue optimization tools lineage also represented by such an oldie as Advanced Mac Cleaner and newer impostors like Mac Mechanic and Mac Tonic, the former having dominated the Mac scareware landscape for many months on end. Furthermore, the baddie under scrutiny is backed by a massive distribution wave that rookies wouldn’t conduct. So we are undoubtedly confronted with a serious adversary spreading a well-tailored toxic program.
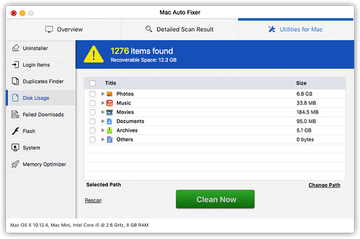
The despicable gist of Mac Auto Fixer comes down to inundating the host system with false positives in an attempt to pressure the victim into purchasing its license. This tactic is at least a decade old, but this particular rogueware implements it more persuasively than competitors. While imitating the detection of most issues it reports, the pest mixes them up with some actual minor system performance bugs to give you the big picture of an awfully unhealthy Mac that needs urgent repairing. To add insult to injury, the infection’s brainwashing logic isn’t restricted to deceptive scans running at random. It additionally displays frustrating popup errors reminding the victim that the more they linger with the fix the worse their machine’s stability status will get.
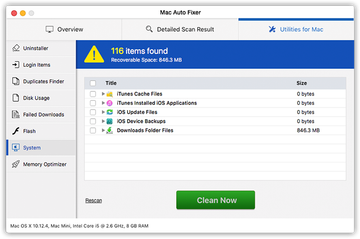
An extra intimidation technique that makes Mac Auto Fixer stand out from the crowd is that it also claims to deliver security features, not only performance-related ones. By falsely reporting a few Trojans or spyware entities, the counterfeit cleaner further increases the odds of duping the user into coughing up some money for the “fully-functional” edition. The preys who are obsessed with privacy might also get on the hook after seeing a report with a bunch tracking cookies and other privacy issues allegedly spotted on board the Mac. Overall, Mac Auto Fixer seems to have all sensitive areas covered in its manipulative routine, therefore sober thinking and rejecting its crafty recommendations are the tips of the day for those infected.
Mac Auto Fixer may re-infect your Mac multiple times unless you delete all of its fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.One more nuisance precipitated by the surreptitious installation of Mac Auto Fixer is that the web browsers slip out of the victim’s control. The scareware adds an extension that replaces the original preferences in Safari, Chrome, and Firefox with set-ups that make the user frown. The goal of this tampering is to make the person recurrently head to a web page crammed up with popup alerts or to a website designed for accepting payments for the app’s license. This adds a layer of pressure on top of the fake system scans and warning messages generated by the pseudo system utility itself.
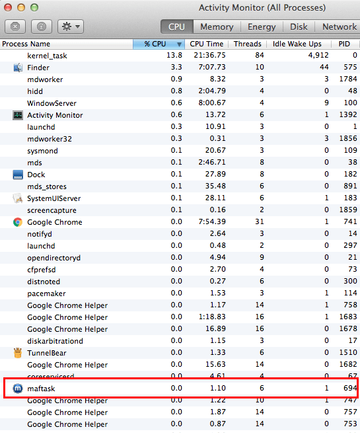
An extra symptom of this attack is that a process named maftask can be pinpointed in the infected Mac’s Activity Monitor. This is the underlying malicious executable that coerces the system to behave in a particular way. In many scenarios, the victims don’t even have to explore the running processes to discover this entity. Since macOS Catalina release, Macs have been giving users a heads up about installed suspicious applications through popup alerts. In the case of Mac Auto Fixer, these dialogs say, “maftask will damage your computer. You should move it to the Trash”. Although these warnings have a “Move to Bin” button, clicking on it doesn’t remove the virus because it’s more stubborn than the average Mac threat. Its persistence, in part, comes down to a shady device profile created without the user’s awareness and permission.
Mac Auto Fixer also poses a privacy risk that shouldn’t be underestimated. It quietly collects information that may allow its operators to profile the victim uniquely and haunt them with phishing hoaxes and targeted ads down the road. This data includes, among other things, the IP address, macOS version, hardware specifications, running apps, and web surfing history. When mishandled by a competent malicious third party, these details can have serious negative implications for the user.
Although this rogue program isn’t really progressive in terms of distribution methods and relies on the good-ol’ bundling trickery, it boasts well-orchestrated propagation that results in thousands of Mac users being infected daily. As unsuspecting users are installing some freeware via custom setup clients, Mac Auto Fixer tailgates inside their systems alongside the primary installs. So the next time you decide to get a free applet from a site with unknown or dubious reputation, be sure to check what’s under the hood of the setup wizard by opting out of the default installation option. Then, simply deselect whatever you deem redundant. Anyway, Mac Auto Fixer is malicious and should be removed from Mac immediately. The walkthroughs below will lend you a helping hand with the cleanup.
Mac Auto Fixer virus manual removal for Mac
The steps listed below will walk you through the removal of this malicious application. Be sure to follow the instructions in the specified order.
Expand the Go menu in your Mac’s Finder bar and select Utilities as shown below.

Locate the Activity Monitor icon on the Utilities screen and double-click on it.

In the Activity Monitor app, look for maftask or another process that appears suspicious. To narrow down your search, focus on unfamiliar resource-intensive entries on the list. Keep in mind that its name isn’t necessarily related to the way the threat is manifesting itself, so you’ll need to trust your own judgement. If you pinpoint the culprit, select it and click on the Stop icon in the upper left-hand corner of the screen.

When a follow-up dialog pops up asking if you are sure you want to quit the troublemaking process, select the Force Quit option.

Click on the Go menu icon in the Finder again and select Go to Folder. You can as well use the Command-Shift-G keyboard shortcut.

Type /Library/LaunchAgents in the folder search dialog and click on the Go button.

Examine the contents of the LaunchAgents folder for dubious-looking items. Be advised that the names of files spawned by malware may give no clear clues that they are malicious, so you should look for recently added entities that appear to deviate from the norm.
As an illustration, here are several examples of LaunchAgents related to mainstream Mac infections: com.techyutil.maftask.plist, com.techyutil.mafuninstaller.plist, com.pcv.hlpramc.plist, com.updater.mcy.plist, com.avickUpd.plist, and com.msp.agent.plist. If you spot files that don’t belong on the list, go ahead and drag them to the Trash.

Use the Go to Folder lookup feature again to navigate to the folder named ~/Library/Application Support (note the tilde symbol prepended to the path).

When the Application Support directory is opened, identify recently generated suspicious folders in it and send them to the Trash. A quick tip is to look for items whose names have nothing to do with Apple products or apps you knowingly installed. A few examples of known-malicious folder names are Mac Auto Fixer, ProgressSite, and IdeaShared.

Enter ~/Library/LaunchAgents string (don’t forget to include the tilde character) in the Go to Folder search area.

The system will display LaunchAgents residing in the current user’s Home directory. Look for dodgy items related to Mac Auto Fixer virus (see logic highlighted in subsections above) and drag the suspects to the Trash.

Type /Library/LaunchDaemons in the Go to Folder search field.

In the LaunchDaemons path, try to pinpoint the files the malware is using for persistence. Several examples of such items cropped by Mac infections are com.techyutil.maftask.plist, com.pplauncher.plist, com.startup.plist, and com.ExpertModuleSearchDaemon.plist. Delete the sketchy files immediately.

Click on the Go menu icon in your Mac’s Finder and select Applications on the list.

Find the entry for Mac Auto Fixer or another app that clearly doesn’t belong there and move it to the Trash. If this action requires your admin password for confirmation, go ahead and enter it.

Expand the Apple menu and select System Preferences.


Proceed to Users & Groups and click on the Login Items tab.


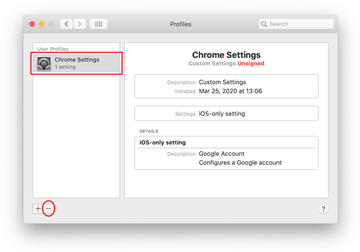
Now select Profiles under System Preferences. Look for a malicious item in the left-hand sidebar. Several examples of configuration profiles created by Mac adware include TechSignalSearch, MainSearchPlatform, AdminPrefs, and Chrome Settings. Select the offending entity and click on the minus sign at the bottom to eliminate it.

Get rid of Mac Auto Fixer virus in web browser on Mac
To begin with, the web browser settings taken over by the Mac Auto Fixer virus should be restored to their default values. Although this will clear most of your customizations, web surfing history, and all temporary data stored by websites, the malicious interference should be terminated likewise. The overview of the steps for completing this procedure is as follows:
- Remove Mac Auto Fixer virus from Safari
Open the browser and go to Safari menu. Select Preferences in the drop-down list.

Once the Preferences screen appears, click on the Advanced tab and enable the option saying “Show Develop menu in menu bar”.

Now that the Develop entry has been added to the Safari menu, expand it and click on Empty Caches.

Now select History in the Safari menu and click on Clear History in the drop-down list.

Safari will display a dialog asking you to specify the period of time this action will apply to. Select all history to ensure a maximum effect. Click on the Clear History button to confirm and exit.

Go back to the Safari Preferences and hit the Privacy tab at the top. Find the option that says Manage Website Data and click on it.

The browser will display a follow-up screen listing the websites that have stored data about your Internet activities. This dialog additionally includes a brief description of what the removal does: you may be logged out of some services and encounter other changes of website behavior after the procedure. If you’re okay with that, go ahead and click on the Remove All button.

Restart Safari
- Remove Mac Auto Fixer in Google Chrome
Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down

When on the Settings pane, select Advanced
Scroll down to the Reset settings section.

Confirm the Chrome reset on a dialog that will pop up. When the procedure is completed, relaunch the browser and check it for malware activity.

- Remove Mac Auto Fixer from Mozilla Firefox
Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).


When on the Troubleshooting Information screen, click on the Refresh Firefox button.

Confirm the intended changes and restart Firefox.
Use automatic tool to uninstall Mac Auto Fixer virus from your Mac
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove Mac Auto Fixer virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the Mac Auto Fixer issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove Mac Auto Fixer threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.
FAQ
Is Mac Auto Fixer safe to use?
The short answer is “No, it’s not”. It’s a fake Mac utility that concocts its scan reports to give users a false impression that their systems are chock-full of performance issues and viruses. Another fact proving that Mac Auto Fixer plays dirty is that it arrives with software bundles that deliberately omit its promotion under the umbrella of a harmless utility. It means that the installation is absolutely not a matter of an informed decision.
Furthermore, this scareware is notoriously persistent. Its grip relies on interference at the level of configuration profiles, a feature used to manage specific system preferences. One of the obnoxious instances of this impact is that the victim’s default web browser is fraudulently reconfigured to redirect the traffic to fake warning sites or to landing pages fleecing the user into purchasing the full version of the phony product.
Is Mac Mechanic an Apple product?
No, Mac Mechanic has nothing to do with Apple. It isn’t a regular performance enhancement tool either. Just like Mac Auto Fixer thoroughly analyzed in the above tutorial, it is an imitation maintenance tool that tries to dupe users into buying its licensed version. In fact, both applications hail from the same source and take a very similar unethical route in terms of the tactics.
Originally discovered in 2018, Mac Mechanic tailgates into computers alongside benign-looking or junk programs advertised on low-quality software download repositories. Once on board a system, it spoofs an unsatisfactory condition of the host by displaying counterfeit scan results that list dozens or hundreds of memory hogs, redundant cache files, unused language packages, and logs. Most of these items aren’t even there, so the high improvement potential signaled by these scan reports is a fake. Therefore, every user who discovers this Mac Mechanic would be better off uninstalling it without hesitation.
What is Nspchlpr?
Nspchlpr is the name of a malicious process associated with Similar Photo Cleaner, an application originating from the same scareware pool as Mac Auto Fixer, Mac Mechanic, and Mac Tonic. The program in question isn’t legit or trustworthy because it intentionally deluges a user’s computing experience with faux notifications about gigabytes of disk space that can be supposedly released by trashing duplicate images.
Some victims become alerted to the presence of Nspchlpr process on their Macs in a straightforward way. The recent tweaks in macOS mechanisms for flagging suspicious code result in periodic popups that go, “nspchlpr will damage your computer. You should move it to the Bin”. Whereas this is a real system warning, it quickly becomes intolerable because Similar Photo Cleaner cannot be removed via a classic uninstall technique and the dialogs continue to appear incessantly.
How do I remove Mac Auto Fixer from my MacBook?
If Mac Auto Fixer has cropped up on your Mac, you’ll have to think of the box to make it vanish. It is a stubborn threat by design and therefore the removal isn’t only a matter of going to Applications and dragging its icon to the Trash. In an attempt to thwart a victim’s uninstalling efforts, it creates multiple LaunchAgents, LaunchDaemons, and folders in the Application Support path. Additionally Mac Auto Fixer mishandles the login items feature and the device profiles functionality to run at boot time and maintain control of web browsing preferences on the machine.
To get rid of it for good, the related files and folders should be removed from all the affected system areas. Plus, it’s necessary to revert to the correct web browsing settings. Please follow the steps listed in the Mac Auto Fixer removal guide above to spot and delete every fragment of this malicious app and undo the unwanted changes it made.
