Search Marquis virus Mac is a new persona of the Bing redirect malady that hijacks a victim’s web browser and causes annoying redirects unless removed.
Update:
| Threat Profile | |
|---|---|
| Name | Search Marquis (searchmarquis.com) browser hijacker |
| Category | Mac adware, redirect virus, PUA |
| IP Address | 54.230.89.106 |
| Related Domains | searchmarquis.com, searchbaron.com, searchnewworld.com, mybrowser-search.com, api.lisumanagerine.club, search.surfharvest.xyz, search-location.com, searchsnow.com, searchitnow.info, r.a9g.io, nearbyme.io, search1.me, chillsearch.xyz, search-alpha.com |
| Symptoms | Redirects web browser to Bing via searchmarquis.com, adds sponsored content to search results, causes system slowdown, resists regular removal |
| Distribution Techniques | Fake Adobe Flash Player update popups, malware-riddled bundles, spam |
| Severity Level | Medium |
| Damage | Unwanted changes of browser preferences, privacy issues due to Internet activity tracking, search redirects, ads above the fold |
| Removal | Scan your Mac with Combo Cleaner to detect all files related to the browser hijacker. Use the tool to remove the infection if found. |
What is Search Marquis redirect virus?
There is a cybercriminal gang on the loose whose activity is shaping up to be a huge concern for the entire Mac community. Although these crooks don’t ruin systems or spread mayhem through greedy crypto-mining behind the victims’ backs, the malicious code they have been creating is hugely obnoxious and extraordinarily hard to remove from plagued Mac machines. The focus of all fishy campaigns under scrutiny is on the web surfing side of computer use. By depositing sneaky apps and plugins onto macOS systems without admins’ consent, the malefactors make browsers act up by rerouting the traffic to sites like searchmarquis.com. What is Search Marquis anyway? It is a manifestation of the virus that gives one’s Internet navigation set-up a malicious overhaul to promote its own landing page. From there, the users are forced to hit Bing.com, Search1.me, or Ask.com, with the browsing path traveling through a number of intermediate domains, such as Search Baron (searchbaron.com), before reaching the destination.
Search Marquis infection chain
The Search Marquis virus slithers its way into a Mac by dint of a tricky software packaging scheme referred to as bundling. This technique co-promotes several applications under the guise of one that’s benign and typically free of charge. While legit per se, the mechanism provides attackers with an opportunity to push their harmful programs without notifying the would-be victim. Unless the default setup mode is unchecked and the custom option is selected in the installation client, the malware will rush into the Mac alongside an item that the user is knowingly installing.
As a result, the pest gets all the privileges it needs, and the prey is clueless about ever granting these permissions. From that moment on, the Search Marquis infection starts dominating all things web browsing on the target computer without allowing the administrator to revert to their normal configuration in a commonplace way. To top it off, the app is code-signed and therefore bypasses Apple’s notarization controls. It means that it doesn’t raise a red flag when checked by the Gatekeeper feature built into macOS.
Search Marquis may re-infect your Mac multiple times unless you delete all of its fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.Web browsing is the hardest-hit macOS area
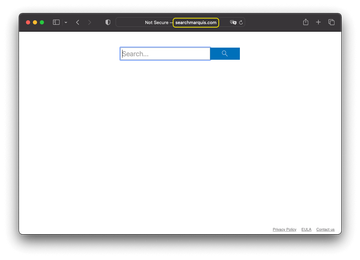
As previously stated, this virus zeroes in on web browsers it detects on the compromised Mac. It supports Safari, Chrome, and Firefox – given the prevalence of these solutions, the impact is going to make itself felt in nearly every attack scenario. The rogue helper object incorporated into the victim’s preferred browser instantly tweaks the homepage, search, and new tab page settings to its own advantage. It replaces these values with searchmarquis.com so that the plagued user visits the unwanted page over and over.
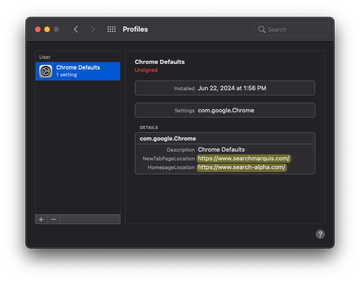
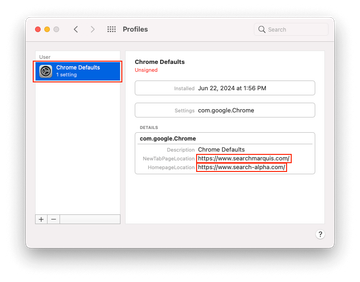
The offending entity tends to additionally tamper with the DNS server settings for extra persistence. This interference leads to the pseudo search engine being constantly resolved instead of the desired one. To tighten the grip further, the culprit stealthily abuses the Mac’s built-in command line, or Terminal utility, to create a random-named configuration profile under System Preferences that holds sway over the targeted browser settings.
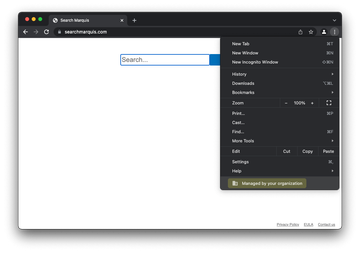
In Google Chrome, this foul play is the easiest to notice, as its main drop-down menu will include a notification saying “Managed by your organization”, as illustrated in the following image. In the case of infection, the message shows up even on a personal Mac that isn’t supervised by an administrator. Aside from generating hits to the fake search engine, this method of obtrusion reportedly has strange repercussions such as signing the victim out of their account in Chrome once in a while – which, obviously, adds insult to injury.
Search engine takeover leading to Bing
On the face of it, searchmarquis.com seems to be a primitive lookup instrument with a search box and a few links leading to the EULA, Privacy Policy, and the Contact Us page. No matter what keywords are entered in it, the sketchy service will return Bing.com. The route of the navigation, though, also includes a couple of URLs that the victim can only see for a fraction of a second. These transitional items denote advertisement networks where every such inconspicuous hit will count as a unique visit, thereby generating profit for the operators of this hoax. As this malicious campaign evolves, new in-between and destination pages are being added to the wicked mix. A couple of examples are:
- searchnewworld.com
- mybrowser-search.com
- api.lisumanagerine.club
- search.surfharvest.xyz
- search-location.com
- searchsnow.com
- searchitnow.info
- r.a9g.io
- nearbyme.io
- search1.me
- chillsearch.xyz
- search-alpha.com
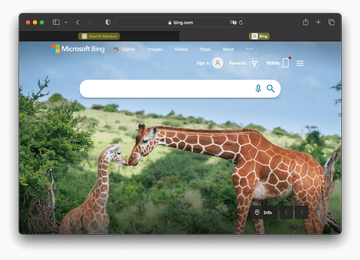
These sites return custom search results powered by a legitimate service, so the hoax keeps heading in basically the same direction, combining clearly harmful activity with benign elements. As of August 2023, the Search Marquis campaign underwent the biggest tweak in many months, accompanied by the addition of a new domain to the original stack. A good deal of the intercepted traffic has since been passing through the Search Alpha rogue service parked at search-alpha.com. Despite the URL switching, the shady logic is invariable: the adware hijacks a browser, reroutes it to a worthless provider with no proprietary search algorithms under its hood, and then the traffic reaches a Bing hosted search page.
Counterintuitively, the latter per se is an insignificant part of the attack equation, albeit an ostensible one. Its function is limited to furnishing the whole occurrence with deceptive hues of normality, while the submerged part of the iceberg holds murky URLs from the list above that fill the monetization void and thus matter the most from felons’ perspective.
Additional symptoms
Another likely symptom of the Search Marquis attack on a Mac is the surge of annoying alerts that say, “Your computer is low on memory”. These warnings usually pop up shortly after system startup and instruct the user to close a few applications to free up some memory. Meanwhile, the available RAM may be multiple times more than what’s required for all running programs to work flawlessly. This quirk, obviously, doesn’t appear to get along with the concept of a browser hijacker, and yet these predicaments bizarrely overlap in most cases. It turns out that such an alert may treacherously overlay a dialog that requests access to control Safari or another web browser. The “undercover” pop-up typically says some app or process whose name consists of multiple random numbers wants to perform actions within the web browser, including unwarranted ingress into the related documents and data. In other words, the faux low memory alert serves as malware’s curtain for privilege escalation on the Mac. The same is true for a more recent spoof warning variant that says, “Your hard drive is almost full”. This one urges a victim to release disk space when there is actually no need to do it. Again, it eclipses a permission request that shouldn’t be accepted.

Sometimes the takeover of web preferences co-occurs with a stealth installation of a scareware app onto the system. The faux cleaning utility could be the one to blame for duping the user into thinking that their machine is short of RAM. This way, the misleading software tries to bilk the unsuspecting victim of a registration fee that will supposedly unlock the imaginary optimization features. So much for the pranks of the Search Marquis virus.
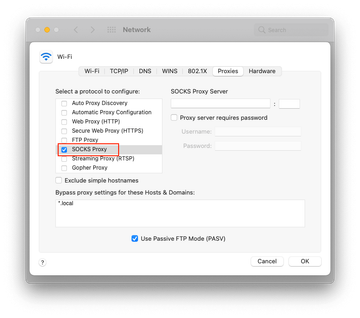
Mac adware is also increasingly leveraging tricks reminiscent of man-in-the-middle (MITM) attacks to misrepresent the appearance of web pages. For instance, it may embed advertisements or fake forms into both encrypted and unencrypted traffic. To this end, these culprits may quietly install a proxy tool that additionally enables them to snoop on victims’ online activities and grab details on the running software as well as hardware specifications. Search Marquis tends to take this route, thereby posing extra risks besides simply being a nuisance. What about the fix? The only way to address the issue is to spot and delete all elements of the perpetrating app. Read the follow-up sections to find out how it’s done.
Search Marquis virus manual removal for Mac
The steps listed below will walk you through the removal of this malicious application. Be sure to follow the instructions in the specified order.
Expand the Go menu in your Mac’s Finder bar and select Utilities as shown below.

Locate the Activity Monitor icon on the Utilities screen and double-click on it.

In the Activity Monitor app, look for a process that appears suspicious. To narrow down your search, focus on unfamiliar resource-intensive entries on the list. Keep in mind that its name isn’t necessarily related to the way the threat is manifesting itself, so you’ll need to trust your own judgement. If you pinpoint the culprit, select it and click on the Stop icon in the upper left-hand corner of the screen.

When a follow-up dialog pops up asking if you are sure you want to quit the troublemaking process, select the Force Quit option.

Click on the Go menu icon in the Finder again and select Go to Folder. You can as well use the Command-Shift-G keyboard shortcut.

Type /Library/LaunchAgents in the folder search dialog and click on the Go button.

Examine the contents of the LaunchAgents folder for dubious-looking items. Be advised that the names of files spawned by malware may give no clear clues that they are malicious, so you should look for recently added entities that appear to deviate from the norm.
As an illustration, here are several examples of LaunchAgents related to mainstream Mac infections: com.pcv.hlpramc.plist, com.updater.mcy.plist, com.avickUpd.plist, and com.msp.agent.plist. If you spot files that don’t belong on the list, go ahead and drag them to the Trash.

Use the Go to Folder lookup feature again to navigate to the folder named ~/Library/Application Support (note the tilde symbol prepended to the path).

When the Application Support directory is opened, identify recently generated suspicious folders in it and send them to the Trash. A quick tip is to look for items whose names have nothing to do with Apple products or apps you knowingly installed. A few examples of known-malicious folder names are UtilityParze, ProgressSite, and IdeaShared.

Enter ~/Library/LaunchAgents string (don’t forget to include the tilde character) in the Go to Folder search area.

The system will display LaunchAgents residing in the current user’s Home directory. Look for dodgy items related to Search Marquis redirect virus (see logic highlighted in subsections above) and drag the suspects to the Trash.

Type /Library/LaunchDaemons in the Go to Folder search field.

In the LaunchDaemons path, try to pinpoint the files the malware is using for persistence. Several examples of such items cropped by Mac infections are com.pplauncher.plist, com.startup.plist, and com.ExpertModuleSearchDaemon.plist. Delete the sketchy files immediately.

Click on the Go menu icon in your Mac’s Finder and select Applications on the list.

Find the entry for an app that clearly doesn’t belong there and move it to the Trash. If this action requires your admin password for confirmation, go ahead and enter it.

Expand the Apple menu and select System Preferences.


Proceed to Users & Groups and click on the Login Items tab.

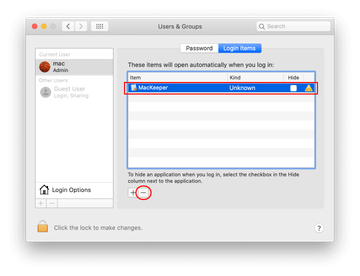
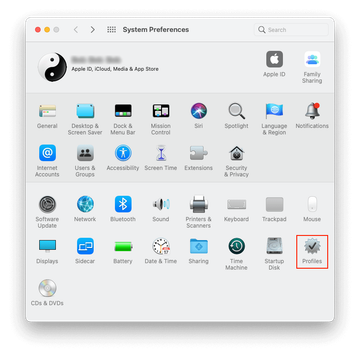
Now select Profiles under System Preferences. Look for a malicious item in the left-hand sidebar. Several examples of configuration profiles created by Mac adware include TechSignalSearch, MainSearchPlatform, AdminPrefs, and Chrome Settings. Select the offending entity and click on the minus sign at the bottom to eliminate it.
Get rid of Search Marquis virus in web browser on Mac
To begin with, the web browser settings taken over by the Search Marquis virus should be restored to their default values. Although this will clear most of your customizations, web surfing history, and all temporary data stored by websites, the malicious interference should be terminated likewise. The overview of the steps for completing this procedure is as follows:
- Remove Search Marquis virus from Safari
Open the browser and go to Safari menu. Select Preferences in the drop-down list.

Once the Preferences screen appears, click on the Advanced tab and enable the option saying “Show Develop menu in menu bar”.

Now that the Develop entry has been added to the Safari menu, expand it and click on Empty Caches.

Now select History in the Safari menu and click on Clear History in the drop-down list.

Safari will display a dialog asking you to specify the period of time this action will apply to. Select all history to ensure a maximum effect. Click on the Clear History button to confirm and exit.

Go back to the Safari Preferences and hit the Privacy tab at the top. Find the option that says Manage Website Data and click on it.

The browser will display a follow-up screen listing the websites that have stored data about your Internet activities. This dialog additionally includes a brief description of what the removal does: you may be logged out of some services and encounter other changes of website behavior after the procedure. If you’re okay with that, go ahead and click on the Remove All button.

Restart Safari
- Remove Search Marquis in Google Chrome
Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down

When on the Settings pane, select Advanced
Scroll down to the Reset settings section.

Confirm the Chrome reset on a dialog that will pop up. When the procedure is completed, relaunch the browser and check it for malware activity.

- Remove Search Marquis from Mozilla Firefox
Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).


When on the Troubleshooting Information screen, click on the Refresh Firefox button.

Confirm the intended changes and restart Firefox.
Get rid of Search Marquis virus using Combo Cleaner removal tool
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove Search Marquis virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the Search Marquis issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove Search Marquis threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.
FAQ
What is Search Marquis search engine?
Search Marquis is an element of a broad-sweeping adware fraud targeting Mac computers. Hosted as searchmarquis.com, it is disguised as a garden-variety web search provider but turns out to lack the essential feature that should be inherent to the type of service it tries to impersonate. Specifically, it doesn’t return search results of its own. Instead, the page responds to every request by redirecting the user to bing.com.
This is the behavior exhibited on a healthy computer, where none of the above takes place unless you deliberately visit the sketchy site and do some experimenting. However, things get more complicated if the so-called Bing redirect virus infects a Mac. In this case, Safari, Google Chrome, and Mozilla Firefox will be automatically forwarded to searchmarquis.com without any such intent on your end. This is because a malicious app that has previously slithered into the system and took over the web surfing preferences.
The purpose of this nefarious interference is to hijack and redistribute the victim’s Internet traffic. Although Bing plays a role of the final-stage landing page in this scheme, it has nothing to do with the cybercriminals’ shenanigans who chose as a means to outsource the missing search function of Search Marquis.
Why is Bing coming up instead of Google on Safari browser?
First things first, this won’t happen unless you configure Safari this way or your Mac is hit by a browser hijacker that imposes unwanted search preferences without permission. If the former scenario isn’t the case, then the whys and wherefores are entirely in the malware domain. The malicious code that sets this plot in motion is referred to as the Bing redirect virus.
Technically, it’s a potentially unwanted application (PUA) that kicked in behind the scenes by modifying the default settings on Safari. The pest usually makes the rounds via tricky software bundles such as spoofed Flash Player update packages peddled through popup ads on hacked websites. If the predicament is underway on a Mac, the only way to address is to identify and remove the underlying app. Fixing the browser settings comes next on your to-do list.
How do I get rid of Search Marquis?
Search Marquis removal is a two-pronged process. First, you need to uninstall the troublemaking application that has skewed the web browser settings and added a malicious configuration profile that maintains a system-wide impact to hamper all cleaning efforts. To pinpoint the infection, examine the Activity Monitor, Applications, LaunchAgents, LaunchDaemons, Login Items, and Profiles on your Mac. Look for entries that deviate from the norm and send them to the Trash. To get a better idea of how to perform this tidying, follow the steps listed in the tutorial above.
The next stage of the fix is to rid the affected web browsers of the intrusive adware influence. Start by analyzing the extensions currently running in Safari, Chrome, and Firefox. If a suspicious one shows up there, disable and uninstall it right away. The infection might not leave such conspicuous breadcrumbs behind, though. If so, the right move is to reset the browser to its default condition – note that in Safari the procedure is a bit more complicated than clicking on one “magic” button. Again, use the browser-related instructions above to take care of the issue.
There is one more noxious element of the Search Marquis infection aftermath hidden in plain sight. Even after removing the malicious application and its debris, users may run into difficulties going online on their Macs. In this scenario, Internet connectivity is hampered by a covert interference with network settings geared toward collecting web browsing information. To spy on a user, the harmful code sets up a connection of its own. Here is an easy way to fix things:
- Open the System Preferences screen;
- Select Network;
- Click the Advanced button at the bottom right;
- Hit the Proxies tab;
- Make sure there are no protocols enabled behind your back (e.g. SOCKS Proxy). If any entry is checked, remove the checkmark and click OK to save the change.
This should resume your normal Internet connection. If all the previous removal steps have been effective, you are now good to go.
Why does Search Marquis come up?
There are several strongholds of the Search Marquis browser hijack that underlie its incessant adverse effects while allowing it to survive commonplace cleaning procedures. First off, it uses a malicious device profile to manage the victim’s web browsing settings as if this were an IT admin-level implementation of an enterprise policy. This meddling alone gives the infection enough privileges to persevere on a Mac computer. It does much more to go stubborn, though.
To make matters worse, the adware enrolls itself in the Login Items list so that its executable runs automatically once macOS is loaded. By the way, many victims who peek in there additionally discover unwanted applications such as Mac Cleanup Pro and Similar Photo Cleaner. These are fake optimization tools that often accompany Search Marquis and generate fake system alerts such as “Your computer is low on memory” popup. Aside from that, several malicious LaunchAgents, LaunchDaemons, and directories in the Application Support folder contribute to the cumulative impact. Because this threat and its cousins are doing the rounds via covert bundling, none of these entities crop up on a Mac through the victim’s explicit consent.
How do you know if your Mac is infected with virus?
System performance impact is the most generic signal of virus presence. It occurs because malicious software tends to spawn multiple processes that use up more CPU and RAM resources than normal applications. Furthermore, some viruses are crudely coded and don’t fit the paradigm of proper interoperability between macOS components.
Given that the vast majority of today’s Mac threats are adware and browser hijackers, another common sign of danger is a disruption of your web surfing activities. Haphazard or systematic redirects to unwanted sites, redundant ads on search engines and other web pages, and pop-ups telling you to download or update something – these are symptoms encountered the most.
With fake Mac optimizers gearing up for a rise, you are also likely to be faced with a slew of system scans and follow-up alerts stating that numerous performance issues were found and instructing you to unlock the cleaning feature by purchasing a license. Another form of detrimental code called ransomware will encrypt your data and display a ransom note.
Some threats don’t manifest themselves as clearly, though. Info-stealing Trojans and rootkits are like that. While being stealthy by design, they do create new entries in the LaunchAgents, LaunchDaemons, and Application Support folders. Therefore, these paths are worth examining for dubious items if you suspect a virus attack.
What does Search Marquis mean?
It’s hard to say what reasoning underlies a specific cybercriminal group’s malware naming convention, so the answer can only be within the realms of speculation. Here’s the wiki side of the concept: the term “marquis” denotes a person of high social rank in Europe.
Zooming into the security area, one thing that’s known for a fact is that the gang behind Search Marquis virus had an impulse toward an aristocratic theme at some point. In the summer of 2019, they also released a browser hijacker called Search Baron (searchbaron.com) that has since been a part of the Search Marquis traffic redistribution scheme.
Perhaps this Mac malware family sticks to the “blue blood” denomination logic because it spans infections that form the backbone of these crooks’ activities. Search Marquis exhibits striking longevity and has hit thousands of Macs, so this is definitely a high-profile campaign that lives up to its name.
How do I get the search bar on my Mac?
Assuming that the question relates to a search bar and URL bar being displayed separately in Safari on Mac, the answer is simple: there is no way to do it. These browser components were merged into a single area with the release of Safari 6 back in 2012.
Therefore, entering keywords in the website address bar will return the results via the search engine specified in Safari settings. The same principle was implemented in Google Chrome, Firefox, and other popular web browsers years ago. It’s the industry standard nowadays.
If the question is about searching for files and apps stored on a Mac, then you need to bring up the Spotlight interface where you can type an item name and get quick results. To open Spotlight, click the icon with the magnifying glass pictogram in the menu bar (or press the Command-Space key combination) and enter what you are looking for.
