Read an overview of the A.akamaihd.net and GoPhoto.it adware issue on Mac and get step-by-step removal instructions to completely resolve this problem.
Update:
| Threat Profile | |
|---|---|
| Name | A.akamaihd.net browser hijacker |
| Category | Mac adware, browser hijacker, redirect virus, PUA |
| IP Address | 184.24.98.170, 104.91.166.56 |
| Related domains | Lkysearchds[random]-a.akamaihd.net, default[random]-a.akamaihd.net, search[random]-a.akamaihd.net, search.safefinder.com, search.anysearchmanager.com, searchmine.net, search.searchpulse.net |
| Symptoms | Redirects web browser to Yahoo via third-party websites, adds sponsored content to search results, causes system slowdown, resists regular removal |
| Distribution Techniques | Fake Adobe Flash Player update popups, malware-riddled app bundles, spam |
| Severity Level | Medium |
| Damage | Unwanted changes of custom browsing settings, privacy issues due to Internet activity tracking, search redirects, redundant ads |
| Removal | Scan your Mac with Combo Cleaner to detect all files related to the browser hijacker. Use the tool to remove the infection if found. |
There has been recently an extremely substantial rise of aggressive adware programs that act more like browser hijackers in that they trigger spoof software download recommendations and redirect one’s web traffic to ad-oriented pages without users’ consent. Rvzr-a.akamaihd.net is an example of the Internet fraudsters’ take on such unethical advertising. However, what makes this particular adware different is not only its capability to affect various browsers, but also the cross-platform contamination it’s fit to deploy.
This article will cover the effects of a.akamaihd.net attacking Mac machines and an efficient removal workflow applicable to this scenario. Indeed, a predominant majority of infection cases refer to Windows, but it appears the pest is no less persistent and perhaps even harder to eliminate from computers running macOS.
Let’s kick off with analyzing what this adware does to a Mac. No matter if you’re using Firefox, Google Chrome, Safari or other web browser customized for Mac, the virus reroutes your traffic to deceptive landing pages or pops up new browser windows with -a.akamaihd.net in the URL field. Note that the web address can be appended by different tails, meaning that the look of these pages may vary. In any case, victims get to see persistent recommendations of downloading some weird stuff such as a critical browser update, multimedia player, video downloader – the former one being prevalent among the reported ‘offers’. Those infected additionally find themselves in a loop of repeated browser redirects that lead to a fake web search service.
It’s worth pointing out that Akamaihd.net per se is not a malicious service. It is part of a large CDN (content delivery network) using multiple servers around the world and processing a great deal of Internet traffic. However, it appears that the operators of massive adware campaigns have been abusing this platform for quite some time. The foul play most likely relies on renting server capacities to rotate online scams rather than deliver benign content. These fraudulent activities fly under the radar of traditional web filtering mechanisms because the core service is legit and reputable, which explains why the malefactors keep adhering with this controversial cooperation. It is somewhat unclear, though, how such a powerful network could possibly become a pivot point of numerous Internet hoaxes circulating for years.
Malware triggering a.akamaihd.net may re-infect your Mac multiple times unless you delete all of its fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.From a technical perspective, when it comes to Macs, redirects to Rvzr-a.akamaihd.net are a symptom of the activity of a web browser extension installed by a potentially unwanted program called WindowMix or GoPhoto.it. The former is a known-malicious adware app that sneaks into systems without permission and displays popup ads while additionally redistributing users’ web traffic to faux search engines. The latter is a fairly popular add-on intended to facilitate viewing, editing and sharing images on the Internet. If this browser helper object gets installed, things are going to get frustrating because along with the actually handy image processing you run into the obnoxious popup problem. Basically, this means it’s not really Rvzr-a.akamaihd.net proper that you need to get rid of. The issue is caused by GoPhoto.it, and that’s your target if you’re experiencing the diverts. The issue is caused by WindowMix, GoPhoto.it or other adware, and that’s your target if you’re experiencing the diverts.
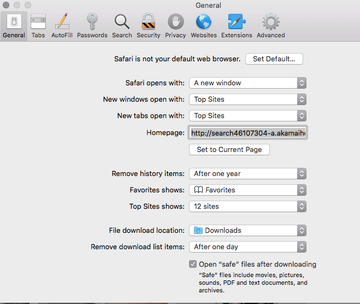
There is one more shady service constituting the Akamaihd.net fraud. It’s called Safe Finder. This is a notorious source of numerous browser hijack stratagems targeting Mac computers since the dawn of the epidemic. Here is how the scheme works: first, a malware-tainted web browser gets its default homepage replaced with a URL similar to search46107304-a.akamaihd.net, with a random-looking extension appended to it:
- am-a.akamaihd.net
- asrv-a.akamaihd.net
- assetsnffrgf-a.akamaihd.net
- cdncache-a.akamaihd.net
- default120617-a.akamaihd.net
- default21076355-a.akamaihd.net
- default26061326-a.akamaihd.net
- default29061341-a.akamaihd.net
- download-a.akamaihd.net
- fbcdn-dragon-a.akamaihd.net
- fbcdn-gtvideo-a.akamaihd.net
- fbcdn-external-a.akamaihd.net
- fbcdn-sphotos-a-a.akamaihd.net
- lumiere-a.akamaihd.net
- pxlclnmdecom-a.akamaihd.net
- search0184386-a.akamaihd.net
- search1173423-a.akamaihd.net
- search2385514-a.akamaihd.net
- search28374278-a.akamaihd.net
- search37085340-a.akamaihd.net
- search82298264-a.akamaihd.net
- search8952443-a.akamaihd.net
- search93117247-a.akamaihd.net
- searchinterneat-a.akamaihd.net
- soprod-a.akamaihd.net
- steam-cdn-a.akamaihd.net
- steamuserimages-a.akamaihd.net
- uctgprsbgl-a.akamaihd.net
- lkysearchds1086-a.akamaihd.net
- lkysearchds3643-a.akamaihd.net
- lkysearchds5012-a.akamaihd.net
- lkysearchds9437-a-akamaihd.net
- lkysearchex1488-a.akamaihd.net
- lkysearchds01269-a-akamaihd.net
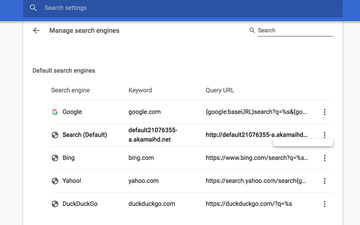
This encroachment on a victim’s online preferences entails iterative instances of traffic forwarding to the wrong domain. From there, the infected user is automatically rerouted to a pseudo search provider, such as search.searchpulse.net, search.anysearchmanager.com or search.safefinderformac.com. All keyword queries made with either one of these junk services lead to Yahoo search results combined with ads above the fold and a logo of the malicious service interwoven with this exploitation, such as Safe Finder. Incidentally, the URL of the landing page is appended with “yhs” characters, so it will start with search.yahoo.com/yhs. That’s most likely an abbreviation of “Yahoo Hosted Search”, a popular solution offering customizable search features. This way, the unscrupulous e-marketers are monetizing their dubious activities.
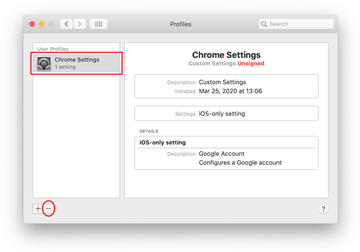
The contamination logic revolves around bundling, a method of promoting apps in a covert way so that the would-be victim is only aware of a benign element of the installer while having no idea that it’s got company. Fake Adobe Flash Player updates touted by intrusive popups on malicious websites are among the main entry points for the A.akamaihd.net threat. Once inside and running on a Mac, the harmful code instantly creates a new configuration profile that manages the victim’s browsing settings. This tactic makes it very problematic to revert to the correct search and homepage preferences in Safari, Chrome, and Firefox. That’s why the malware cleanup is only effective as long as the malware-riddle device profile is deleted. In order to do it, open the Finder menu, go to System Preferences, and select Profiles. Then, check the list in the left-hand section of the screen for items you don’t recognize. Any unfamiliar entry should be deleted without a second thought. All it takes is selecting it and clicking on the minus icon at the bottom. This should unlock the usual recovery techniques covered further down.
No matter which incarnation of the Akamaihd.net virus you are faced with, the only effective response is to get rid of the infection. The section below is tailored to assist those affected in removing the adware and hence ceasing the popup and redirect activity for good.
A.akamaihd.net manual removal for Mac
The steps listed below will walk you through the removal of this malicious application. Be sure to follow the instructions in the specified order.
Expand the Go menu in your Mac’s Finder bar and select Utilities as shown below.

Locate the Activity Monitor icon on the Utilities screen and double-click on it.

In the Activity Monitor app, look for a process that appears suspicious. To narrow down your search, focus on unfamiliar resource-intensive entries on the list. Keep in mind that its name isn’t necessarily related to the way the threat is manifesting itself, so you’ll need to trust your own judgement. If you pinpoint the culprit, select it and click on the Stop icon in the upper left-hand corner of the screen.

When a follow-up dialog pops up asking if you are sure you want to quit the troublemaking process, select the Force Quit option.

Click on the Go menu icon in the Finder again and select Go to Folder. You can as well use the Command-Shift-G keyboard shortcut.

Type /Library/LaunchAgents in the folder search dialog and click on the Go button.

Examine the contents of the LaunchAgents folder for dubious-looking items. Be advised that the names of files spawned by malware may give no clear clues that they are malicious, so you should look for recently added entities that appear to deviate from the norm.
As an illustration, here are several examples of LaunchAgents related to mainstream Mac infections: com.pcv.hlpramc.plist, com.updater.mcy.plist, com.avickUpd.plist, and com.msp.agent.plist. If you spot files that don’t belong on the list, go ahead and drag them to the Trash.

Use the Go to Folder lookup feature again to navigate to the folder named ~/Library/Application Support (note the tilde symbol prepended to the path).

When the Application Support directory is opened, identify recently generated suspicious folders in it and send them to the Trash. A quick tip is to look for items whose names have nothing to do with Apple products or apps you knowingly installed. A few examples of known-malicious folder names are SystemSpecial, ProgressSite, and IdeaShared.

Enter ~/Library/LaunchAgents string (don’t forget to include the tilde character) in the Go to Folder search area.

The system will display LaunchAgents residing in the current user’s Home directory. Look for dodgy items related to a.akamaihd.net redirect virus (see logic highlighted in subsections above) and drag the suspects to the Trash.

Type /Library/LaunchDaemons in the Go to Folder search field.

In the LaunchDaemons path, try to pinpoint the files the malware is using for persistence. Several examples of such items cropped by Mac infections are com.pplauncher.plist, com.startup.plist, and com.ExpertModuleSearchDaemon.plist. Delete the sketchy files immediately.

Click on the Go menu icon in your Mac’s Finder and select Applications on the list.

Find the entry for an app that clearly doesn’t belong there and move it to the Trash. If this action requires your admin password for confirmation, go ahead and enter it.

Expand the Apple menu and select System Preferences.


Proceed to Users & Groups and click on the Login Items tab.


Now select Profiles under System Preferences. Look for a malicious item in the left-hand sidebar. Several examples of configuration profiles created by Mac adware include TechSignalSearch, MainSearchPlatform, AdminPrefs, and Chrome Settings. Select the offending entity and click on the minus sign at the bottom to eliminate it.

Get rid of a.akamaihd.net virus in web browser on Mac
To begin with, the web browser settings taken over by the a.akamaihd.net virus should be restored to their default values. Although this will clear most of your customizations, web surfing history, and all temporary data stored by websites, the malicious interference should be terminated likewise. The overview of the steps for completing this procedure is as follows:
- Remove a.akamaihd.net virus from Safari
Open the browser and go to Safari menu. Select Preferences in the drop-down list.

Once the Preferences screen appears, click on the Advanced tab and enable the option saying “Show Develop menu in menu bar”.

Now that the Develop entry has been added to the Safari menu, expand it and click on Empty Caches.

Now select History in the Safari menu and click on Clear History in the drop-down list.

Safari will display a dialog asking you to specify the period of time this action will apply to. Select all history to ensure a maximum effect. Click on the Clear History button to confirm and exit.

Go back to the Safari Preferences and hit the Privacy tab at the top. Find the option that says Manage Website Data and click on it.

The browser will display a follow-up screen listing the websites that have stored data about your Internet activities. This dialog additionally includes a brief description of what the removal does: you may be logged out of some services and encounter other changes of website behavior after the procedure. If you’re okay with that, go ahead and click on the Remove All button.

Restart Safari
- Remove a.akamaihd.net in Google Chrome
Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down

When on the Settings pane, select Advanced
Scroll down to the Reset settings section.

Confirm the Chrome reset on a dialog that will pop up. When the procedure is completed, relaunch the browser and check it for malware activity.

- Remove a.akamaihd.net from Mozilla Firefox
Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).


When on the Troubleshooting Information screen, click on the Refresh Firefox button.

Confirm the intended changes and restart Firefox.
Use automatic tool to fix the a.akamaihd.net Mac issue
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove a.akamaihd.net virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the a.akamaihd.net issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove a.akamaihd.net threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.
FAQ
What is Akamaihd net used for?
Akamaihd is a content delivery network with a complex infrastructure of servers distributed around the world. Its services are used by major corporations and regular website owners alike. One of the key benefits of this cooperation comes down to boosting site loading speed due to optimization of online content delivery based on the visitor’s geographic location.
Akamaihd net is, undoubtedly, a legit platform leveraged and trusted by numerous businesses and webmasters. However, it also appears to be a part of large-scale adware and browser hijacking frauds perpetrated by cybercriminals. The fact that the service has a solid reputation allows these campaigns to stay up and running for years on end without being taken down. How exactly the crooks manage to manipulate the CDN’s checks and controls is still a question that has yet to be answered.
What is Pxlclnmdecom a Akamaihd?
Pxlclnmdecom a Akamaihd is the way users refer to a widespread browser redirect fraud currently making the rounds. In fact, the accurate URL the victims encounter in their address bar during the hijack is pxlclnmdecom-a.akamaihd.net. The string is followed by a tail denoting the identifiers of a particular shady sub-campaign. This domain is a transit spot forwarding the contaminated web browser further to fake software update pages, spammy ads, tech support scams, or rogue search providers.
Can Macs get hacked?
Any Internet-facing electronic system can get hacked, and so can Macs. In the case of Akamaihd.net virus, though, the attack isn’t really a hack in the traditional sense. Its operators are unable to control the plagued computers remotely or cause suchlike damage. Instead, once the infection is inside, it runs autonomously in compliance with a predefined set of instructions. It invokes a series of commands to change the victim’s browsing preferences and thus rearrange the normal web surfing routine without authorization. This interference doesn’t call forth severe effects, but it’s a nuisance preventing those contaminated from using their computers in a hassle-free way. All in all, classic hacking is probably a marginal thing in the macOS environment, but Mac malware is definitely real, and it’s here to stay.
What is Akamaihd net on iPhone?
As mentioned in the guide above, Akamaihd.net virus is both cross-browser and multi-platform. It means iPhones are just as susceptible to the attack as laptops and desktop computers, although the mobile infections issue isn’t as common. The logic of the incursion is the same: the pest typically slithers into an iPhone via booby-trapped installations promoted on uncertified app stores. Once on board, it tweaks the custom Internet settings to drive traffic to the affiliated junk sources. If you have discovered such an anomaly on your iOS device, the fix is usually a matter of clearing caches, history and data in the affected web browser.
What is default21076355-a.akamaihd.net?
It is one of the numerous knockoffs of the akamaihd.net scam haunting the macOS ecosystem. This string replaces the default search engine setting in Google Chrome, Safari, or Firefox on a computer raided by the underlying adware application. The purpose of this unauthorized change is to narrow down the victim’s Internet search activity to a service that works as a dispatcher sending the traffic further. Although the resulting site is the authentic Yahoo Search, the route towards it includes several midway spots that can hardly be discerned with the naked eye. These pages in transit are traffic aggregator networks that enable the actors behind a.akamaihd.net to rake in profits. Going back to the original question, default21076355-a.akamaihd.net is just a small, yet important, link in a complex chain of the browser hijack campaign.