Opera browser that has cropped up on a Mac without the user’s consent may signal a prior malware attack and the unwanted app should be uninstalled.
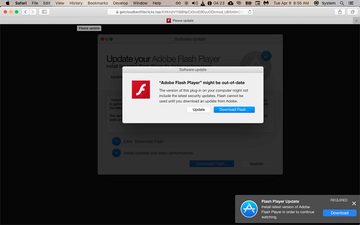
First things first, Opera is a trusted web browser listed in the top 10 solutions of its kind by the global market share criterion. There is no denying that it’s intuitive, flexible, secure, and privacy-aware. However, switching to a new web navigation tool no matter which one it is, or simply giving it a shot, should be an informed decision. With Opera, this obvious rule doesn’t always work seamlessly. Mac users have been increasingly reporting instances of this browser installing itself behind the scenes, with no clear-cut permission requests accompanying the process. Normally, this type of unauthorized emergence is a red flag indicating a social engineering scam. It turns out that the application is sometimes promoted by a notoriously prolific hoax relying on fake Adobe Flash Player updates. Here’s how it pans out: when on a regular website, a Mac user is suddenly redirected to another page that displays a number of popups insisting on an immediate update of the Flash Player. If the person falls for it, they run the risk of allowing adware to enter their computer. In some recent cases, though, the payload is Opera browser.
The original redirect that sets this attack chain in motion is usually triggered once the unsuspecting user clicks on a bait link. But, there are situations where the mishap takes place without any user action at all. The operators of this malvertising plot are adept at embedding malicious scripts into popular websites so that the visitors encounter predefined shady scenarios without clicking anything. One way or another, the spoofed Adobe Flash Player update popups underlie software bundles that install potentially unwanted applications (PUAs) onto Macs. The common threats that slip by users’ attention this way are browser hijackers or ad-injecting parasites such as Safe Finder and IdeaShared 1.0. It seems that Opera browser doesn’t fit the mold of a commonplace entity tailgating into systems via such an unethical mechanism. And yet, it has been in the cybercrooks’ portfolio for quite some time.
Opera PUA may re-infect your Mac multiple times unless you delete all of its fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.A likely motivation for cross-promoting the Opera browser is to earn a sort of affiliate revenue. It’s hard to say who the seasoned e-malefactors are in cahoots with, but this is the most plausible conclusion drawn from these distribution practices. As soon as Opera is on board a Mac, it may prompt the user to set it as the default browser. Chances are that this happens without properly manifested requests, which may further puzzle the victim over the ways to revert to their correct Internet surfing preferences. Additionally, the unwelcome software often maintains persistence by adding itself to the Login Items so that it’s executed during every sign-in. On top of that, the program might meddle with the Device Profiles feature on Mac to enforce certain system-wide tweaks and control the web browsing facet of computer use. Ultimately, the footprint of Opera in the target machine gets blown out of proportion, making the user want to get rid of it for good.
The above-mentioned symptoms are likely precipitated by extra infections that could have infiltrated the Mac through the same bundle. Therefore, the victim will probably experience one more attack tier that involves the installation of nefarious extensions on the other browsers, including Google Chrome, Safari, and Mozilla Firefox. Again, this is a surreptitious workflow that omits the user interaction stage. The add-on will invoke incessant redirects leading to pseudo search providers, plus it will cause sponsored materials to be displayed across benign websites being visited. This interference doesn’t get along with hassle-free computing and therefore the user will imminently look for a way to bring this frenzy to a halt.
Unlike the cases where Opera is knowingly installed from the official source and configured, the cybercrime-flavored propagation presupposes obstacles hampering uninstall attempts. The app may be too obstinate to yield to classic removal. It means that spotting its icon on the Applications screen and dragging it to the Trash is only half the battle because some traces such as LaunchAgents and LaunchDaemons will be left behind. It means that the browser may reappear down the road. If you didn’t mean to install Opera and it’s giving you a hard time, the following tips will make the removal efforts effective by shedding light on the ways to diminish its persistence and purge the threats that may have snuck into your Mac in the same wrapping.
Opera manual removal for Mac
The steps listed below will walk you through the removal of this malicious application. Be sure to follow the instructions in the specified order.
Expand the Go menu in your Mac’s Finder bar and select Utilities as shown below.

Locate the Activity Monitor icon on the Utilities screen and double-click on it.

In the Activity Monitor app, look for a process that appears suspicious. To narrow down your search, focus on unfamiliar resource-intensive entries on the list. Keep in mind that its name isn’t necessarily related to the way the threat is manifesting itself, so you’ll need to trust your own judgement. If you pinpoint the culprit, select it and click on the Stop icon in the upper left-hand corner of the screen.

When a follow-up dialog pops up asking if you are sure you want to quit the troublemaking process, select the Force Quit option.

Click on the Go menu icon in the Finder again and select Go to Folder. You can as well use the Command-Shift-G keyboard shortcut.

Type /Library/LaunchAgents in the folder search dialog and click on the Go button.

Examine the contents of the LaunchAgents folder for dubious-looking items. Be advised that the names of files spawned by malware may give no clear clues that they are malicious, so you should look for recently added entities that appear to deviate from the norm.
As an illustration, here are several examples of LaunchAgents related to mainstream Mac infections: com.pcv.hlpramc.plist, com.updater.mcy.plist, com.avickUpd.plist, and com.msp.agent.plist. If you spot files that don’t belong on the list, go ahead and drag them to the Trash.

Use the Go to Folder lookup feature again to navigate to the folder named ~/Library/Application Support (note the tilde symbol prepended to the path).

When the Application Support directory is opened, identify recently generated suspicious folders in it and send them to the Trash. A quick tip is to look for items whose names have nothing to do with Apple products or apps you knowingly installed. A few examples of known-malicious folder names are SystemSpecial, ProgressSite, and IdeaShared.

Enter ~/Library/LaunchAgents string (don’t forget to include the tilde character) in the Go to Folder search area.

The system will display LaunchAgents residing in the current user’s Home directory. Look for dodgy items related to Opera PUA (see logic highlighted in subsections above) and drag the suspects to the Trash.

Type /Library/LaunchDaemons in the Go to Folder search field.

In the LaunchDaemons path, try to pinpoint the files the malware is using for persistence. Several examples of such items cropped by Mac infections are com.pplauncher.plist, com.startup.plist, and com.ExpertModuleSearchDaemon.plist. Delete the sketchy files immediately.

Click on the Go menu icon in your Mac’s Finder and select Applications on the list.

Find the entry for an app that clearly doesn’t belong there and move it to the Trash. If this action requires your admin password for confirmation, go ahead and enter it.

Expand the Apple menu and select System Preferences.


Proceed to Users & Groups and click on the Login Items tab.


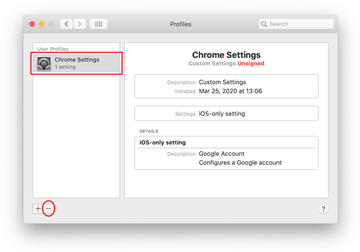
Now select Profiles under System Preferences. Look for a malicious item in the left-hand sidebar. Several examples of configuration profiles created by Mac adware include TechSignalSearch, MainSearchPlatform, AdminPrefs, and Chrome Settings. Select the offending entity and click on the minus sign at the bottom to eliminate it.

Get rid of Opera-related ads and redirect activity in web browser on Mac
To begin with, the web browser settings taken over by Opera-linked adware should be restored to their default values. Although this will clear most of your customizations, web surfing history, and all temporary data stored by websites, the malicious interference should be terminated likewise. The overview of the steps for completing this procedure is as follows:
- Remove Opera PUA components in Safari
- Open the browser and go to Safari menu. Select Preferences in the drop-down list

- Once the Preferences screen appears, click on the Advanced tab and enable the option saying “Show Develop menu in menu bar”.

- Now that the Develop entry has been added to the Safari menu, expand it and click on Empty Caches.

- Now select History in the Safari menu and click on Clear History in the drop-down list.

- Safari will display a dialog asking you to specify the period of time this action will apply to. Select all history to ensure a maximum effect. Click on the Clear History button to confirm and exit.

- Go back to the Safari Preferences and hit the Privacy tab at the top. Find the option that says Manage Website Data and click on it.

- The browser will display a follow-up screen listing the websites that have stored data about your Internet activities. This dialog additionally includes a brief description of what the removal does: you may be logged out of some services and encounter other changes of website behavior after the procedure. If you’re okay with that, go ahead and click on the Remove All button.

- Restart Safari
- Open the browser and go to Safari menu. Select Preferences in the drop-down list
- Get rid of redirects in Google Chrome caused by Opera-related PUA
- Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down

- When on the Settings pane, select Advanced
- Scroll down to the Reset settings section.

- Confirm the Chrome reset on a dialog that will pop up. When the procedure is completed, relaunch the browser and check it for malware activity.

- Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down
- Remove Opera-related extension in Mozilla Firefox
- Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).


- When on the Troubleshooting Information screen, click on the Refresh Firefox button.

- Confirm the intended changes and restart Firefox.
- Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).
Get rid of Opera potentially unwanted application using Combo Cleaner removal tool
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove Opera PUA virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the Opera PUA issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove Opera PUA threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.
