- Common variants of the spoofed update popups
- Other red flags to watch out for
- A website-borne scam
- The hoax is evolving
- Persistence schemes
- Fake Adobe Flash Player update virus manual removal for Mac
- Get rid of Fake Adobe Flash Player Update virus in web browser on Mac
- Get rid of Adobe Flash Player update virus using Combo Cleaner removal tool
- FAQ
Learn how to remove fake Adobe Flash Player update virus from Mac and thereby prevent the browser from being redirected to rogue software installation websites.
Update:
| Threat Profile | |
|---|---|
| Name | Fake Adobe Flash Player update virus |
| Category | Mac browser hijacker, redirect/popup virus, Mac adware |
| Detection | Avast: MacOS:AMC-DK [PUP], Avira: PUA/OSX.GT32SupportGeeks.hflsn, BitDefender: Adware.MAC.Generic.12496, ESET: A Variant Of OSX/GT32SupportGeeks.B, Kaspersky: Trojan-Downloader.OSX.Shlayer.a, Microsoft: PUA:MacOS/AMCleaner.B!MTB, Sophos: AdvancedMacCleaner (PUA), Symantec: OSX.Trojan.Gen.2 |
| Domains involved | deej.almeusciu.site, upgradecircle.findgreatsourceforupgrade.info, afew.zoyufo.pw, upgradebestmaintenancetheclicks.icu, s3.amazonaws.com, updatemostrenewedapplication.best |
| Symptoms | Interrupts web sessions with fake Flash Player update popups, redirects to deceptive sites, causes browser slowdown |
| Distribution Techniques | Freeware bundles, torrents, booby-trapped software updates, misleading popup ads |
| Severity Level | Medium |
| Damage | Interference with browsing settings, harmful downloads, privacy issues due to Internet activity tracking, search redirects, malicious ads |
| Removal | Scan your Mac with Combo Cleaner to detect all files related to the browser hijacker. Use the tool to remove the infection if found. |
The Adobe Flash Player update virus is one of the common ways cybercriminals try to deposit additional harmful code onto a Mac. It usually operates in tandem with such threats as bogus system utilities that report non-existent problems and thus attempt to manipulate users into activating the licensed copy of the scareware. This type of a ruse can be used to promote such unwanted apps as Mac Auto Fixer, Mac Cleanup Pro, Easy Mac Care or Advanced Mac Tuneup. These opportunistic infections will run phony scans of the host system and claim to detect hundreds of issues – ones that aren’t there for real. This hoax is also the pivot for distributing the nastiest Mac adware threats to date, including Search Pulse, Any Search Manager, TapuFind, Chill-Tab, and the a.akamaihd.net redirect virus that underlies most of these dubious services. The targeted Mac users therefore deal with a triple contamination scenario, where they first encounter recurrent and really annoying instances of browser rerouting and then suffer the consequences of counterfeit software activity combined with redirects leading to fake search engines and advertising networks. It’s the early stage of the brainwashing that is backed by the Adobe Flash Player update virus popups.
Common variants of the spoofed update popups
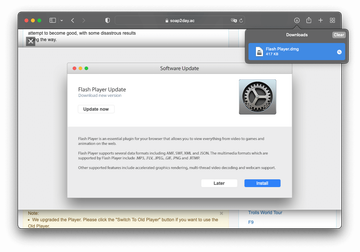
The reason why the architects of this trickery have added the Flash Player to the mix of their shenanigans is probably because it’s a commonly used program trusted by most users. The caveat is that a completely different piece of code is camouflaged as the explicitly stated software. This part of the incursion is usually isolated to the web browser, although there are rare cases where the misguiding popups appear when the browser is closed. The virus manifests itself through random redirects to a site that instantly displays a popup alert saying something like the following:
"Adobe Flash Player" is out of date
To continue using “Adobe Flash Player”, download an updated version.
The wording in the spoofed notifications may be different, though. A few other common examples are as follows: “Flash Player update is available for your computer”, “Your system is missing critical plugin updates”, “Install the latest Flash Player for better performance”, “Flash Player might be out-of-date. The version of this plug-in on your computer might not include the latest security updates”, and “Flash Player Update. Download new version”. Meanwhile, a prompt at the top of the page layout may wrongfully emphasize that “Latest version of Adobe Flash Player is required to encode and/or decode (Play) audio files in high quality”. Everybody likes quality multimedia content, so a lot of users end up falling for this trick.
Other red flags to watch out for
In all of these adverse situations, those who pay attention to detail will notice that there is something wrong with such a recommendation. First off, the URL of the website that generates these Adobe Flash Player update popups is a giveaway. Obviously, it has nothing to do with the genuine vendor, being clearly designed to mimic the legit update workflow. Furthermore, despite the fact that the alerts may provide a button to opt out, such as “Later” or “Cancel”, clicking it isn’t likely to close the dialogs for more than a few milliseconds. The pre-configured website script will relaunch the ads, so the victims may have to force quit Safari, Chrome, Firefox – or whatever browser is infected – to get the bogus notifications out of the way.
Fake Adobe Flash Player Update virus may re-infect your Mac multiple times unless you delete all of its fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.A website-borne scam
A few examples of the spoofed promo pages massively reported by victims are deej.almeusciu.site, upgradecircle.findgreatsourceforupgrade.info and afew.zoyufo.pw. The list of these malware serving domains is constantly expanding as old ones are being knocked offline in response to victims’ complaints or blacklisting on the browser end. Incidentally, the above-mentioned scam sites splashed onto the scene amidst a spike in the fake Flash Player update hoax in March 2020, which co-occurred with a very unsettling trend. Numerous Mac users claim to be redirected to these malware-riddled pages when on reputable resources with huge user audiences, including CNN and NY Times news outlets. One of the theories why this could be happening is that the criminals may have somehow injected malicious scripts into a number of popular websites so that the visitors end up being forwarded to unwanted landing pages.
The hoax is evolving
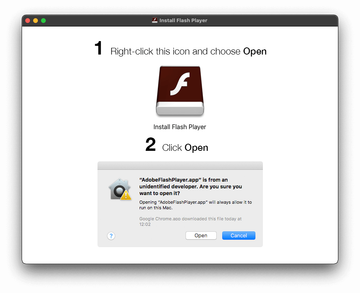
A whole new attack mechanism with the fake Adobe Flash Player update popups at its core is distributing an emerging Mac threat codenamed Tarmac. Also known as OSX/Tarmac, this infection relies on another type of harmful code called Trojan:OSX/Shlayer. The latter is a notorious Mac Trojan whose objective is to set large-scale malvertising schemes in motion. Its original entry point is a phony alert about an out-of-date version of the Flash Player. Once inside, it reaches out to the Command and Control server and downloads a copy of Tarmac onto the host. The second-stage malware is code signed and leverages RSA encryption to camouflage the fishy gist of its payload, which allows the pest to fly below the radar of quarantine-aware software running on the Mac. As soon as OSX/Tarmac is launched, it attempts to elevate its privileges on the machine by generating a dialog that says, “Play wants to make changes”.
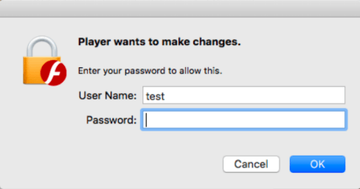
This popup asks for the administrator’s username and password, making it look like the request comes from Adobe Flash Player. Even if the victim is prudent enough to refrain from entering the credentials, Tarmac continues to run with fairly high permissions. Just like Shlayer, it can easily connect to its C&C server and download arbitrary code from it, such as rogue system utilities, adware, or even Mac ransomware. This recently discovered tandem of dangerous programs relying on counterfeit Flash Player update ads demonstrates that the campaign is evolving and assuming more unsettling characteristics.
In January 2020, security analysts unveiled some eyebrow-raising details about the scope of Shlayer wave that piggybacks on rogue Flash Player update popups. According to these findings, one of this Trojan’s iterations was the top Mac threat picked up by a popular antimalware solution last year. Aside from well-orchestrated social engineering trickery, its domination stems from the fact that the operators of this scam have been actively recruiting YouTube channel owners, Wikipedia writers, and bloggers with large subscriber audiences to post ads leading to the malware-riddled downloads.
There is also a hefty number of malicious sites created specifically to spread the plague. Some of these trojanized links posted on various legit web outlets lead to domains that expired recently, and it appears that the crooks have bought and repurposed them to serve up the infection. As a result, Mac users who are looking up some trending terms on search engines, such as a new TV show episode or a live stream of a sports event, run the risk of visiting the wrong page that hosts the shady installer.
Another oddity is that this stratagem is still going strong in early 2021 despite the fact that Adobe no longer officially supports its product. However, in some scenarios the black hats push a modified version of the fraud in line with this change. Mac users are being growingly targeted with phony Adobe Flash Player Uninstaller popups that claim to streamline the process of removing the now-obsolete software. More irrationally, the original plot continues to make itself felt in 2022. Plenty of people must still be getting on the hook, so the crooks don’t seem to care about the current status of the discontinued application they mimic.
Persistence schemes
This troublemaking scenario tends to be bolstered by a malicious browser plugin or extension. The fake helper object modifies Internet settings, such as the homepage or search defaults, and may even interfere with the DNS server preset. This is what causes the redirects in the first place. What happens if you click “OK” and actually download the pseudo Adobe Flash Player update is a whole new attack layer. The affiliated harmful program will establish persistence on the Mac by adding itself to Login Items and utilizing antivirus evasion mechanisms. Then, it will start launching scans of the macOS, purporting to find numerous memory issues and security problems each time. Again, this routine is aimed at pressuring the victim into making a hasty decision to pay for the cyber-impostor’s licensed version. So much for the tactic. Speaking of the fix for the Adobe Flash Player update virus activity, the only method is to spot the components of the pest on the Mac and remove them. See below to learn how it’s done.
Fake Adobe Flash Player update virus manual removal for Mac
The steps listed below will walk you through the removal of this malicious application. Be sure to follow the instructions in the specified order.
Expand the Go menu in your Mac’s Finder bar and select Utilities as shown below.

Locate the Activity Monitor icon on the Utilities screen and double-click on it.

In the Activity Monitor app, look for a process that appears suspicious. To narrow down your search, focus on unfamiliar resource-intensive entries on the list. Keep in mind that its name isn’t necessarily related to the way the threat is manifesting itself, so you’ll need to trust your own judgement. If you pinpoint the culprit, select it and click on the Stop icon in the upper left-hand corner of the screen.

When a follow-up dialog pops up asking if you are sure you want to quit the troublemaking process, select the Force Quit option.

Click on the Go menu icon in the Finder again and select Go to Folder. You can as well use the Command-Shift-G keyboard shortcut.

Type /Library/LaunchAgents in the folder search dialog and click on the Go button.

Examine the contents of the LaunchAgents folder for dubious-looking items. Be advised that the names of files spawned by malware may give no clear clues that they are malicious, so you should look for recently added entities that appear to deviate from the norm.
As an illustration, here are several examples of LaunchAgents related to mainstream Mac infections: com.pcv.hlpramc.plist, com.updater.mcy.plist, com.avickUpd.plist, and com.msp.agent.plist. If you spot files that don’t belong on the list, go ahead and drag them to the Trash.

Use the Go to Folder lookup feature again to navigate to the folder named ~/Library/Application Support (note the tilde symbol prepended to the path).

When the Application Support directory is opened, identify recently generated suspicious folders in it and send them to the Trash. A quick tip is to look for items whose names have nothing to do with Apple products or apps you knowingly installed. A few examples of known-malicious folder names are SystemSpecial, ProgressSite, and IdeaShared.

Enter ~/Library/LaunchAgents string (don’t forget to include the tilde character) in the Go to Folder search area.

The system will display LaunchAgents residing in the current user’s Home directory. Look for dodgy items related to fake Adobe Flash Player update virus (see logic highlighted in subsections above) and drag the suspects to the Trash.

Type /Library/LaunchDaemons in the Go to Folder search field.

In the LaunchDaemons path, try to pinpoint the files the malware is using for persistence. Several examples of such items cropped by Mac infections are com.pplauncher.plist, com.startup.plist, and com.ExpertModuleSearchDaemon.plist. Delete the sketchy files immediately.

Click on the Go menu icon in your Mac’s Finder and select Applications on the list.

Find the entry for an app that clearly doesn’t belong there and move it to the Trash. If this action requires your admin password for confirmation, go ahead and enter it.

Expand the Apple menu and select System Preferences.


Proceed to Users & Groups and click on the Login Items tab.


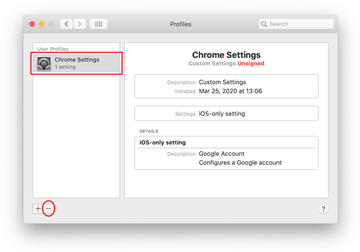
Now select Profiles under System Preferences. Look for a malicious item in the left-hand sidebar. Several examples of configuration profiles created by Mac adware include TechSignalSearch, MainSearchPlatform, AdminPrefs, and Chrome Settings. Select the offending entity and click on the minus sign at the bottom to eliminate it.

Get rid of Fake Adobe Flash Player Update virus in web browser on Mac
To begin with, the web browser settings taken over by the Fake Adobe Flash Player Update virus should be restored to their default values. Although this will clear most of your customizations, web surfing history, and all temporary data stored by websites, the malicious interference should be terminated likewise. The overview of the steps for completing this procedure is as follows:
- Remove Fake Adobe Flash Player Update virus from Safari
Open the browser and go to Safari menu. Select Preferences in the drop-down list.

Once the Preferences screen appears, click on the Advanced tab and enable the option saying “Show Develop menu in menu bar”.

Now that the Develop entry has been added to the Safari menu, expand it and click on Empty Caches.

Now select History in the Safari menu and click on Clear History in the drop-down list.

Safari will display a dialog asking you to specify the period of time this action will apply to. Select all history to ensure a maximum effect. Click on the Clear History button to confirm and exit.

Go back to the Safari Preferences and hit the Privacy tab at the top. Find the option that says Manage Website Data and click on it.

The browser will display a follow-up screen listing the websites that have stored data about your Internet activities. This dialog additionally includes a brief description of what the removal does: you may be logged out of some services and encounter other changes of website behavior after the procedure. If you’re okay with that, go ahead and click on the Remove All button.

Restart Safari
- Remove Fake Adobe Flash Player Update in Google Chrome
Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down

When on the Settings pane, select Advanced
Scroll down to the Reset settings section.

Confirm the Chrome reset on a dialog that will pop up. When the procedure is completed, relaunch the browser and check it for malware activity.

- Remove Fake Adobe Flash Player Update from Mozilla Firefox
Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).


When on the Troubleshooting Information screen, click on the Refresh Firefox button.

Confirm the intended changes and restart Firefox.
Get rid of Adobe Flash Player update virus using Combo Cleaner removal tool
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove Fake Adobe Flash Player Update virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the Fake Adobe Flash Player Update issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove Fake Adobe Flash Player Update threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.
FAQ
How to disable Adobe Flash in your browser?
Whereas Adobe Flash Player is useful software that enhances your online experience in plenty of ways, it can as well be a source of vulnerabilities exposing your Mac to cyber-attacks. Furthermore, many users simply don’t catch up with the frequent patches rolled out by the publisher, inadvertently turning their computers into low-hanging fruit.
It comes as no surprise that many users end up disabling the Flash plugin in their web browser at some point. This tool can be safely turned off at the browser level without the need to uninstall it from a Mac altogether. Here is how to disable it in popular browsers:
Safari:
- In Safari menu bar, select Preferences
- Select the Security tab, spot the Internet Plug-ins area, and click Plug-in Settings
- Remove the checkmark next to Adobe Flash Player in the subsequent screen
- Click Done
Google Chrome:
- Type chrome://settings/content in Chrome’s URL bar
- Scroll down and find the Flash entry on the page. Click it
- Spot the Allow sites to run Flash option and toggle it off using the adjacent slider
Mozilla Firefox:
- Type about:addons in the URL bar and hit Enter
- Select Plugins in the left-hand navigation bar
- Find the Flash Player plugin and expand the appropriate menu
- Choose between Ask to Activate and Never Activate options. The latter is preferable if you don’t want to see annoying popup dialogs during web surfing.
How to turn off Adobe Flash Player update notifications?
In case the regular Flash Player update popups are interrupting your activities, there is a way to get them out of sight. Be advised that by clicking the Remind Me Later button on these notifications you simply postpone the process, and the irritating message will reappear in an hour. Here’s how to prevent these messages from appearing on your Mac for good:
- Go to the Finder and select System Preferences
- Click the Flash Player icon
- When on the Flash Player screen, hit the Updates tab in its upper part
- You will see the following options to choose from: Allow Adobe to install updates, Notify me to install updates, and Never check for updates
- Enable a radio button next to the Never check for updates option. You can alternatively allow Adobe to install updates – in that case, Flash Player will be updated on its own without producing any popups
Does updating Mac remove viruses?
If a malicious app is already on board your system, then a macOS update isn’t likely to fix the problem. That being said, updating your Mac does address known security vulnerabilities so that you are protected against common exploits and mainstream viruses further on. Another benefit of applying the updates as soon as they are available is that your Mac will be optimized to ensure smooth performance. Keep in mind that human error might undermine the built-in Mac defenses no matter how top-notch they are.
Can you get a virus from Adobe Flash Player?
No, you can’t – as long as you diligently keep Flash Player up to date and all the new versions are installed from the official source. In a vast majority of incidents where this utility is exploited to deposit malware onto Macs, the victims neglect the update hygiene and use very old versions of the product with multiple unpatched security loopholes in them.
Flash updates pushed via popup alerts on rogue websites are a completely different story. The installation clients in this case include bundled malware. If you happen to opt for this kind of an offer, a contamination is pretty much inevitable. The article above highlights the common infection scenarios through fake Adobe Flash Player update notifications. Note that Mac users are typically redirected to these landing pages because their browsers have been hijacked. Therefore, removal of the underlying virus is a prerequisite of addressing the predicament.
