Articles
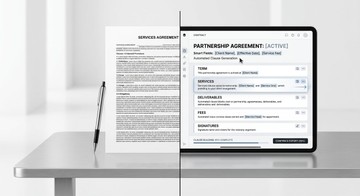
Contract generator vs contract template: What’s better for real work?
Compare contract templates vs. contract generators. Learn the key differences in speed, legal compliance, customization, and error risk to choose the right tool for your business needs.
Securing Apple devices at home: Why layered security and microlearning keep families safe
Learn how layered security and microlearning (short, focused lessons) keep households safe from phishing, weak habits, and human error.
Impact of AI-driven automation on the corporate attack surface
AI-driven automation expands the corporate attack surface through credential sprawl, prompt injection, third-party integrations, and shadow workflows that traditional security models often miss.
What is application modernization and how to approach it
A general-tech guide explaining application modernization, legacy system challenges, and practical strategies for modernizing enterprise software.
What happens to corporate data when employees work from their own Mac
Using personal Macs for work can expose corporate data through limited visibility, unmanaged apps, weak encryption, and inconsistent endpoint controls.
QR code phishing is quietly targeting Mac and iPhone users
QR code phishing is bypassing traditional security measures by exploiting the convenience and trust of iPhone and Mac users. Learn why these attacks are effective and how to protect yourself.