- “Service Records will damage your computer” pop-up alert
- “FileZilla.app will damage your computer” warning
- “Steuern2016 will damage your computer” pop-up
- “Sibelius6 will damage your computer” message
- “Cisco AnyConnect Secure Mobility Client will damage your computer” pop-up
- “Vpnagentd will damage your computer” alert
- “Ciscod will damage your computer” pop-up notification
- “Pulse Secure will damage your computer” warning
- “PDE.plugin will damage your computer” pop-up
- “Matterhorn.framework will damage your computer” warning
- “… will damage your computer” virus manual removal for Mac
- Get rid of “… will damage your computer” virus in web browser on Mac
- Use automatic tool to uninstall “… will damage your computer” virus from your Mac
Remove "Receiver Helper will damage your computer. You should move it to the Trash" virus from Mac to remedy the affected web browser and stop obnoxious pop-ups saying that this application will damage your computer.
Update:
Hassle-free computing is a misnomer if adware infiltrates a Mac. Whereas some digital threats, such as info-stealers, are covert by design and cause harm without telltale signs of infection, the above-mentioned culprits manifest themselves more than conspicuously. Often referred to as potentially unwanted applications (PUAs), they hit the web browsing side of the Mac by incessantly displaying ads and spoofed pop-up alerts. Browser redirects that lead to shady or worthless services add a few extra touches to the nasty big picture. All of these unwelcome after-effects of the attack hold true for Receiver Helper (aka ActivityInputd, CleanParameterd, DominantPartitiond, ElementaryTyped, ManagerAnalogd, ProtocolStatus, StandardBoostd, OperativeMachined, etc.), an adware strain that’s currently seeing a sizable spike in distribution. It tiptoes into a system as part of a multi-pronged installer that misleadingly appears to promote a harmless app with no strings attached. Having made it into the Mac, the e-pest shows its true colors by turning the user’s Internet defaults upside down.
"Receiver Helper will damage your computer" virus homes in on the user-defined preferences in Safari, Google Chrome, or Mozilla Firefox. It identifies which browser to target by profiling the victim at the early stage of the attack. This process involves, among other things, a reconnaissance aimed at amassing the details on the hardware set-up, macOS version, third-party software installed, IP address, system language, and geolocation. Obviously, it’s the default browser that undergoes the tweaking. This way, the adware operators make sure that they strike exactly where it hurts. The mechanics of this tampering are as follows: the infection replaces the preferred search engine, start page, and new tab page settings with a page involved in a traffic monetization scheme. It tends to be a search provider copycat that outsources all requests to a real information lookup service like Yahoo or Bing while plugging one or a few in-between domains into the rerouting logic. These transitional URLs are mostly advertising networks that treat all user leads as a tradeable commodity no matter if they originate from legit sources or from unethical browser hijacking techniques.
“…will damage your computer” alert virus may re-infect your Mac multiple times unless you delete all of its fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.There is more to a "ReceiverHelper will damage your computer" incursion than the defiant reorganization of the victim’s Internet traffic. It installs a malicious browser extension that meddles with the way web page content is rendered to the user. The misbehaving add-on does this by executing scripts which, in their turn, trigger advertisements based on the browsing history that was previously logged in a stealthy manner. The fact that ads by Receiver Helper are targeted and properly aligned with the infected user’s interests is a heads up in itself. It is a derivative of the privacy encroachment properties manifested by the PUA in question. Simply put, not only is the app a nuisance but it also poses a risk to sensitive data.
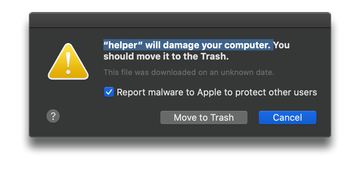
It comes as no surprise that macOS Big Sur 11.5, the latest iteration of the operating system (as of October 2021), flags it as a potential threat. It alerts the users by displaying pop-ups that say, “*will damage your computer”. The dialog also recommends that the suspicious program should be moved to the Trash. There is a hurdle, though: if the victim chooses this shortcut and clicks the embedded button to eradicate the culprit, nothing happens. In some cases, an additional pop-up will appear and notify the user that the application cannot be removed because it’s in use. Either way, there is zero effect. The system warnings will continue to splash up, making the attack yet more annoying. Under the circumstances, the only tactic that really works is to get rid of Receiver Helper using some of the best practices of Mac malware removal. This will stop unwanted ads, browser redirects, and system errors caused by the intrusive app.
As a matter of fact, many more Mac threats trigger the exact same macOS response. Gatekeeper, Apple’s security feature that verifies processes before they can be executed on computers, alerts users to potential danger by displaying the “[app name] will damage your computer” pop-ups every time such suspicious binaries are being run. In some cases, these warnings appear right after the system loads. This goes for situations where the dubious application added itself to the Login Items without permission.
![‘[app name] will damage your computer’ Mac alert ‘[app name] will damage your computer’ Mac alert](/img/Tn_ioIJWTn-360-warning-about-damage.png)
Here is a list of the processes commonly flagged this way by macOS Big Sur and Catalina as of October 2021:
- ActivityInputd (Mar 2021)
- AnalyzerWindowd (Feb 2021)
- Cisco AnyConnect (Aug 2021)
- Ciscod (Aug 2021)
- CleanParameterd (Feb 2021)
- ConfigTyped (Feb 2021)
- CUDA.framework (Jun 2022)
- DigitalDataSourceDaemon
- DominantPartitiond (Mar 2021)
- ElementaryTyped (Feb 2021)
- ExtendedSprintd (Feb 2021)
- Fax.Backend
- HerculesLookupDaemon
- Hmopt
- HPDeviceMonitoring.framework
- hpdm.framework
- hpPostProcessing.bundle (Apr 2021)
- hpPostScriptpde.plugin
- HP Scanner 3
- HP Utility / HP Utility 3
- InitialProgramd (Feb 2021)
- InitialSkilld (Feb 2021)
- inkjet1.driver (Apr 2021)
- Kanbanier
- LauncherSetup (Feb 2021)
- libecomlodr.dylib
- ManagerAnalogd (Feb 2021)
- Matterhorn.framework (Apr 2021)
- Nearwoodce
- Ocensmail
- OnlineResultsDaemon
- OperativeMachined (Mar 2021)
- OriginalModuled (Feb 2021)
- PDE.Plugin
- PenTabletSpringboard
- PlaybeatTrial
- ProtocolPort (Feb 2021)
- ProtocolStatus (Feb 2021)
- Pulse Secure (Aug 2021)
- Receiver Helper
- RecordMapperd (Feb 2021)
- Safe Surf FinderDaemon
- SearchConsoleDaemeon
- SearchSystemsDaemon
- ServiceRecords (Oct 2021)
- SkilledObjectd (Feb 2021)
- SorimbrsecDaemon
- SpiderOak
- StandardBoostd (Feb 2021)
- StandartProductd (Feb 2021)
- SymLicensing.framework
- TechFunctionSearchDaemon
- TituricsecDaemon
- TrustedAnalogd (Feb 2021)
- Unithandlerd (Feb 2021)
- Vpnagentd (Aug 2021)
Many of these are executables associated with Mac adware. Because they don’t pass the operating system’s checks in terms of code signing, they are deemed as a possible source of security and privacy issues. Some of these are obsolete versions of legitimate products that lack the latest security patches, in which case installing the newest build should stop the alerts from appearing.
“Service Records will damage your computer” pop-up alert
Both Service Records and Receiver Helper are processes used by Citrix Receiver, a workspace virtualization tool heavily used by numerous organizations. This solution was superseded by an app called Citrix Workspace in 2018. macOS is flagging Service Records as harmful because many companies and individuals are still using the legacy software. Therefore, addressing the problem is a matter of uninstalling the old instance of the Citrix tool and installing the latest version provided by the publisher. This is probably a prophylactic reaction of the system to known vulnerabilities in older iterations of the program. According to some reports, the company made a questionably reasonable choice of a Certificate Authority (CA) to get its code signed at some point. It leverages certificates issued by Symantec, which has a controversial track record in this area. This could be a strong reason for macOS to distrust Citrix products.
Zooming out of the “cert-gate” story, it’s noteworthy that many users who are heavily annoyed by “Service Records will damage your computer” alerts discover that the detected file resides inside a directory called libexec. That’s strange, because the wiki dimension of this object is absolutely within the realms of legitimacy – it is an important folder storing macOS service extensions. Its involvement in shadowy schemes could have two facets. One is that a strain of sneaky malware somehow gets around the read-only nature of the genuine “libexec” folder to inject its components into it. By blending with benign daemons and executables, the culprit tries to evade detection. The other theory is both more realistic and prosaic. A harmful code sample may create a “libexec” folder of its own and keep its binaries in it. In this case, macOS may interpret the presence of the copycat as a sign of danger, hence the influx of warning pop-ups.
“FileZilla.app will damage your computer” warning
The logic covered in the previous paragraph applies to the FileZilla.app reporting scenario, too. FileZilla is a hugely popular free FTP client that supports file transfers between a computer and a server. The alert about possible risks of executing this solution looks like a false positive. However, macOS 10.15 only treats out-of-date builds of FileZilla this way. The tip of the day for those affected is to trash the current version of the tool and then install the most recent one from the vendor’s site.

“Steuern2016 will damage your computer” pop-up
Although the above two examples may be deemed controversial due to somewhat exaggerated response of macOS, Steuern2016 is a clearly malicious process that doesn’t belong inside a computer. It is a core binary used by an adware application that makes a mess of one’s web browser preferences and redirects the traffic to fake search services. If such a warning is appearing non-stop, it’s strongly recommended to pinpoint and vanquish the infection.
“Sibelius6 will damage your computer” message
Sibelius6 is a process used by the Sibelius music notation tool allowing users to create, edit, and print music scores. Whilst it’s not malicious per se, its previous release could be riddled with loopholes for exploitation by malicious actors. Therefore, if the Gatekeeper module detects this app as potentially dangerous, the fix comes down to replacing the current build with the latest one, namely Sibelius 6.1. If the usual uninstall technique doesn’t work as intended, use Spotlight Search to locate all instances of Sibelius6 file on the Mac. Then, delete each one and empty the Trash. When done, install the fresh version from the publisher’s website.
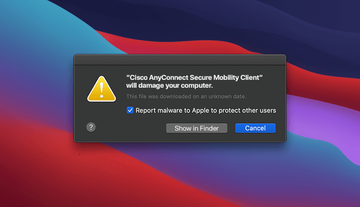
“Cisco AnyConnect Secure Mobility Client will damage your computer” pop-up
This issue is affecting both macOS Catalina and Big Sur users. The AnyConnect Secure Mobility Client is a piece of software heavily used in enterprise environments for protection against Internet-borne threats. One of its primary tasks, though, comes down to Virtual Private Network (VPN) services. In August 2021, Mac machines that run this product started alerting users to possible risk supposedly stemming from an unsafe copy of the Cisco client. This is most likely the system’s response to an out-of-date version of AnyConnect, and therefore the fix is to update it as soon as possible.
“Vpnagentd will damage your computer” alert
Vpnagentd is a component of the above-mentioned Cisco AnyConnect product. When a customer is using the VPN feature of this client, their Mac may trigger a pop-up warning that says this entity is dangerous. According to some reports, this is probably an old certificate issue that can be addressed by installing the latest version of the program. It’s within the realms of possibility, though, that malware is to blame. Either way, it makes sense to check the Mac for threats if this dialog is repeatedly appearing.
“Ciscod will damage your computer” pop-up notification
Yet another process associated with Cisco AnyConnect ended up in the spotlight of Apple’s security mechanisms. Ciscod is an executable that performs an auxiliary function in the operation of the popular toolkit. Due to a certificate issue, XProtect is detecting it as a threat and letting the users know in a fairly intrusive way. To address the predicament, network administrators should ascertain that the latest version of the software is running on endpoints. A malware scan is an extra precaution definitely worth making.
“Pulse Secure will damage your computer” warning
This is another instance of a VPN-related notification giving Mac users a hard time. As of August 2021, Apple has begun flagging some versions of the Pulse Secure app as malicious. One of the possible reasons is that vulnerabilities were found in the utility, and it can become an entry point for cybercriminals. Again, the top remedy is to update the VPN service without delay. Ensuring that this isn’t a virus issue is a good idea, too.
“PDE.plugin will damage your computer” pop-up
This alert fits the context of a certificate revocation snafu that hit a handful of Hewlett Packard applications, including drivers and plugins, shortly after last year’s release of macOS Big Sur. PDE.plugin is a helper component of the famous company’s printing logic. It kicks in as soon as a Mac user starts a new print job. Unfortunately, it is better known for being a false positives catalyst than for facilitating HP-related processes.
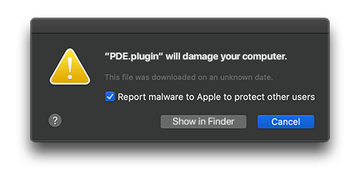
When faced with the invalid digital certificate scenario, Mac owners can use several effective workarounds. One of them is to leverage AirPrint, which works wirelessly and doesn’t require any HP drivers at all. Another easy fix is to remove the HP device along with its drivers from “Printers & Scanners” under System Preferences, reconnect the printer, and then let the operating system pull in and install the latest version of the necessary software automatically.
Sometimes, the “PDE.plugin will damage your computer” alert is a symptom of malware infection. A strain of harmful code may mimic a legitimate application to fool Apple’s XProtect feature and run without any hindrance. Since the malware signatures database of this macOS component is refreshed on a regular basis, another such update may cause the native system defenses to identify the impostor app as a threat. This will be accompanied by security notifications appearing repeatedly. In this situation, the only effective way to stop the popup activity is to address the root cause, that is, to get rid of the malware in disguise.
“Matterhorn.framework will damage your computer” warning
This is yet another nuisance alert that fits the context of the HP certificates revocation story. Protection features on Macs have been flagging different components of older printing suite versions, including Matterhorn.framework, as potential malware for many months due to their untrustworthy digital signatures. If stars align in such an unfavorable way, the emergence of this popup will co-occur with every attempt to print. The silver bullet in this case is to update the associated software or reinstall drivers for the Hewlett Packard device in use.

As is the case with some other alerts on the list, this one may be a more serious wake-up call. If a sample of Mac malware masquerades itself as the legitimate HP process in question, macOS will likely identify the inconsistency in its signatures and behavior. As a result, these notifications will be constantly interrupting the user’s routine. The distinguishing thing in this scenario is that the popup activity doesn’t overlap with printing. This quandary can be addressed by detecting and removing the quasi-legitimate application. The following steps will shed light on this procedure.
“… will damage your computer” virus manual removal for Mac
The steps listed below will walk you through the removal of this malicious application. Be sure to follow the instructions in the specified order.
Expand the Go menu in your Mac’s Finder bar and select Utilities as shown below.

Locate the Activity Monitor icon on the Utilities screen and double-click on it.

In the Activity Monitor app, look for the app name mentioned in “… will damage your computer” alert, or another process that appears suspicious. To narrow down your search, focus on unfamiliar resource-intensive entries on the list. Keep in mind that its name isn’t necessarily related to the way the threat is manifesting itself, so you’ll need to trust your own judgement. If you pinpoint the culprit, select it and click on the Stop icon in the upper left-hand corner of the screen.

When a follow-up dialog pops up asking if you are sure you want to quit the troublemaking process, select the Force Quit option.

Click on the Go menu icon in the Finder again and select Go to Folder. You can as well use the Command-Shift-G keyboard shortcut.

Type /Library/LaunchAgents in the folder search dialog and click on the Go button.

Examine the contents of the LaunchAgents folder for dubious-looking items. Be advised that the names of files spawned by malware may give no clear clues that they are malicious, so you should look for recently added entities that appear to deviate from the norm.
As an illustration, here are several examples of LaunchAgents related to mainstream Mac infections: com.pcv.hlpramc.plist, com.updater.mcy.plist, com.avickUpd.plist, and com.msp.agent.plist. If you spot files that don’t belong on the list, go ahead and drag them to the Trash.

Use the Go to Folder lookup feature again to navigate to the folder named ~/Library/Application Support (note the tilde symbol prepended to the path).

When the Application Support directory is opened, identify recently generated suspicious folders in it and send them to the Trash. A quick tip is to look for items whose names have nothing to do with Apple products or apps you knowingly installed. A few examples of known-malicious folder names are Mac Cleanup Pro, IdeaShared, and ProgressMatch.

Enter ~/Library/LaunchAgents string (don’t forget to include the tilde character) in the Go to Folder search area.

The system will display LaunchAgents residing in the current user’s Home directory. Look for dodgy items related to “… will damage your computer” virus (see logic highlighted in subsections above) and drag the suspects to the Trash.

Type /Library/LaunchDaemons in the Go to Folder search field.

In the LaunchDaemons path, try to pinpoint the files the malware is using for persistence. Several examples of such items cropped by Mac infections are com.pplauncher.plist, com.startup.plist, and com.ExpertModuleSearchDaemon.plist. Delete the sketchy files immediately.

Click on the Go menu icon in your Mac’s Finder and select Applications on the list.

Find the app specified in “… will damage your computer” pop-ups and move it to the Trash. If this action requires your admin password for confirmation, go ahead and enter it.

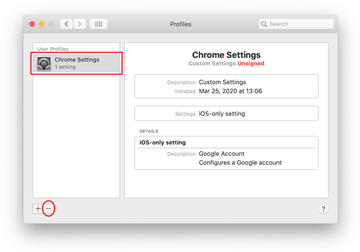
Expand the Apple menu and select System Preferences.


Proceed to Users & Groups and click on the Login Items tab.


Now select Profiles under System Preferences. Look for a malicious item in the left-hand sidebar. Several examples of configuration profiles created by Mac adware include TechSignalSearch, MainSearchPlatform, AdminPrefs, and Chrome Settings. Select the offending entity and click on the minus sign at the bottom to eliminate it.

Get rid of “… will damage your computer” virus in web browser on Mac
To begin with, the web browser settings taken over by “… will damage your computer” threat should be restored to their default values. Although this will clear most of your customizations, web surfing history, and all temporary data stored by websites, the malicious interference should be terminated likewise. The overview of the steps for completing this procedure is as follows:
- Remove “… will damage your computer” virus from Safari
- Open the browser and go to Safari menu. Select Preferences in the drop-down list

- Once the Preferences screen appears, click on the Advanced tab and enable the option saying “Show Develop menu in menu bar”.

- Now that the Develop entry has been added to the Safari menu, expand it and click on Empty Caches.

- Now select History in the Safari menu and click on Clear History in the drop-down list.

- Safari will display a dialog asking you to specify the period of time this action will apply to. Select all history to ensure a maximum effect. Click on the Clear History button to confirm and exit.

- Go back to the Safari Preferences and hit the Privacy tab at the top. Find the option that says Manage Website Data and click on it.

- The browser will display a follow-up screen listing the websites that have stored data about your Internet activities. This dialog additionally includes a brief description of what the removal does: you may be logged out of some services and encounter other changes of website behavior after the procedure. If you’re okay with that, go ahead and click on the Remove All button.

- Restart Safari
- Open the browser and go to Safari menu. Select Preferences in the drop-down list
- Remove “… will damage your computer” virus in Google Chrome
- Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down

- When on the Settings pane, select Advanced
- Scroll down to the Reset settings section.

- Confirm the Chrome reset on a dialog that will pop up. When the procedure is completed, relaunch the browser and check it for malware activity.

- Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down
- Remove “… will damage your computer” alert from Mozilla Firefox
- Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).


- When on the Troubleshooting Information screen, click on the Refresh Firefox button.

- Confirm the intended changes and restart Firefox.
- Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).
Use automatic tool to uninstall “… will damage your computer” virus from your Mac
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove “… will damage your computer” virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the “… will damage your computer” issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove “… will damage your computer” threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.
