Learn how to remove SearchMine malware from Mac and thereby prevent Safari, Chrome and Firefox from being redirected to searchmine.net rogue site.
Update:
| Threat Profile | |
|---|---|
| Name | SearchMine (SearchMine.net) browser hijacker |
| Category | Mac browser hijacker, redirect virus, Mac adware |
| Related Domains | searchmine.net, opti-page.com, webcrawler.com, trovi.com, prudensearch.com |
| Detection | Avast: MacOS:Agent-EN [Drp], BitDefender: Adware.MAC.Bundlore.DMM, Emsisoft: Adware.MAC.Bundlore.DMM (B), F-Secure: Adware.ADWARE/OSX.Bnodlero, McAfee: RDN/Generic.osx, Sophos AV: Bundlore (PUA) |
| Symptoms | Redirects web browser to SearchMine.net, adds sponsored content to search results, causes system slowdown, resists regular removal, adds a rogue enterprise policy in Google Chrome |
| Distribution Techniques | Fake Adobe Flash Player update popups, freeware bundles, spam, rogue Chrome extensions for Google Workspace users |
| Severity Level | Medium |
| Damage | Unwanted changes of custom browsing settings, privacy issues due to Internet activity tracking, search redirects, redundant ads |
| Removal | Scan your Mac with Combo Cleaner to detect all files related to the browser hijacker. Use the tool to remove the infection if found. |
What is SearchMine “Smart Search”?
When it comes to one’s online experience, it’s hard to think of a greater nuisance than a browser hijack that gives the web preferences an overhaul without the victim’s consent. The issue is big regardless of the operating system and it has been that way for years, but the macOS territory is currently a rapidly expanding battlefield in this regard. What does it mean to be hit by a piece of browser-twisting malware such as SearchMine? The most conspicuous impact is all about redirects. The culprit keeps on forwarding an ambushed Mac user’s Internet traffic to its landing page at searchmine.net. This activity isn’t haphazard, though, as it follows a fairly strict pattern. The victim’s default browser – be it Safari, Google Chrome, or Mozilla Firefox – undergoes unauthorized manipulation resulting in the custom settings being replaced with a new value.
SearchMine may re-infect your Mac multiple times unless you delete all of its fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.Persistence techniques used by SearchMine
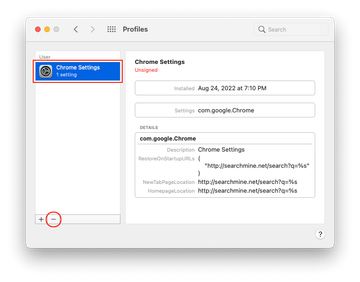
This attack has one more revolting facet that makes the pest a moving target. Let’s say Chrome on a Mac is being redirected to searchmine.net. In addition to tweaking the browser preferences, the malware sets a Chrome enterprise policy that overrides the admin’s settings and disallows changes that the victim may attempt to make in a regular way. Each try will be accompanied by a message saying that the browser is “Managed by your organization”, when it’s actually not.
Incidentally, group policies are an indispensable instrument in the toolkit of enterprise network administrators. They allow an organization to specify browser settings and restrictions so that employees don’t download potentially harmful files or visit sites they aren’t supposed to. This adjustment of system behavior isn’t only the prerogative of admins, but it’s also doable by third-party software. Obviously, SearchMine operators have found a way to repurpose enterprise policies for persistence of their malicious application.
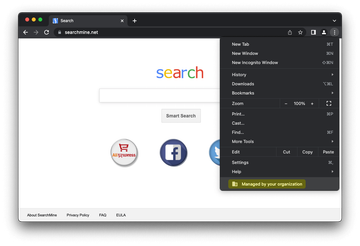
In the upshot, the browser forwarding loop is there to stay until the sketchy policy is removed. A telltale symptom of this tampering is that the homepage, new tab, and default search provider settings may become unresponsive and grayed out to keep the infected person from remediating them by hand. To add insult to injury, the pest may add a rogue device profile to enforce one more layer of persistence. The examples of these configuration profiles include:
- AdminPrefs;
- Safari Settings;
- Chrome Settings.
The enterprise policy trick and interference at the level of system preferences make SearchMine a really stubborn malware that requires the victims to think outside the box.
Affiliated rogue sites
The landing page, searchmine.net, might appear to fit the mold of a garden-variety search provider. It contains a keyword entry bar and a few links underneath it that lead to popular services, namely Facebook, Twitter, YouTube, and AliExpress. However, this ostensible mundanity turns out to conceal a serious pitfall. If you input an arbitrary query, the site will return trovi.com, opti-page.com or webcrawler.com which, in turn, displays questionably accurate results that may forward you to other malicious web pages with virus downloads lurking on them.
In many cases, the landing pages are valid Bing or Yahoo Search results but the route towards this ostensibly safe destination is riddled with dubious URLs and controversial advertising networks. For instance, the rogue web resources frequently observed in the browser’s status bar during the redirect are different knockoffs of the a-akamaihd.net domain, which is part of a cloud and content delivery service heavily mishandled by Mac adware makers.
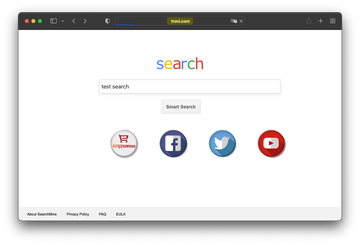
Since August 2020, SearchMine operators have been increasingly forwarding victims’ web traffic to Bing. These redirects are backed by auxiliary services such as searchmarquis.com or searchbaron.com, which can be noticed in an affected browser’s status bar for a split second before the landing page is hit. As of 2022, the scheme has been enhanced by two more dubious in-between services, prudensearch.com and trovi.com. The former is a relatively new searchmine.net clone, and the latter represents one of the heavyweight Mac adware families active for at least eight years now.
SearchMine virus distribution
As far as the distribution of the SearchMine Mac virus goes, everything fits the mold of a commonplace adware campaign. The ne’er-do-wells chose to stick with the old school bundling mechanism to deposit the nasty payload onto systems. The installer for this malicious item constitutes fishy setup clients that are allegedly intended to make the process of installing some nifty software seamless. The worst part is that the hoax hides in plain sight, being part of the “express” setup option that most people never deselect. This covertness, paired with numerous Mac users’ affinity with freebies, such as apps available on unofficial sources, explains why the malware under scrutiny is increasingly prolific.
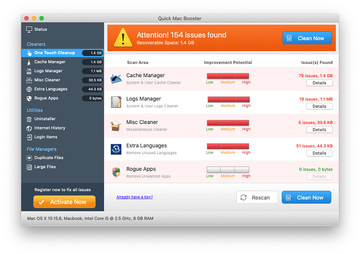
Yet another infection vector engages what’s called “malvertising”. This stratagem involves misleading popup ads shown online that say Adobe Flash Player is out of date. If the unsuspecting user decides to apply the purported update, though, the SearchMine malware will be installed instead. To top it off, there might be a potentially unwanted follow-up application in this package, such as a Mac Cleanup Pro or Quick Mac Booster fake system utility that leverages a scare tactic to hoodwink people into buying its license. Another commonly reported pest that may accompany this browser hijacker is Media Downloader, a known adware program that claims to allow users to download streaming videos but ends up inundating web pages with annoying ads.
As if these cross-promoted entities weren’t enough to diminish the user experience, the virus-riddled Flash Player bundle often also includes MyCouponsmart adware. This dubious app injects redundant ads into the visited websites while pretending to be a tool that delivers a better e-shopping experience. A new spreading scheme unearthed in August 2022 explains another significant surge in infections. SearchMine makers have been heavily exploiting the immensely popular Google Workspace theme to deliver payloads on Macs. The pest can arrive with a handful of booby-trapped extensions that mimic Chrome management tools for Workspace accounts. In this case, the browser in question becomes an entry point for the further deployment of the malicious code within a host. A recap of this shady distribution is as follows: SearchMine virus hardly ever arrives at Macs on its own. If it’s in, then it makes sense looking for and deleting more threats that probably infiltrated the system as well.
Privacy risks
Here’s one more thing to consider: the victims are so baffled by the conspicuous aftermath of this attack that they fail to notice a more subtle, yet unnerving, side effect. Both the adware in question and the accompanying threats get their privileges on a Mac computer escalated to such an extent that there is no obstacle for them to collect sensitive online data. The private information at risk includes browsing history, web searches, and even keystrokes made to sign into personal accounts.
According to malware analysts’ findings unearthed in April 2020, SearchMine also amasses such details as the macOS and browser version, the list of installed applications, the current build of Apple’s proprietary Malware Removal Tool (MRT), as well as a summary of LaunchAgents and LaunchDaemons on a Mac. The infection then exfiltrates this information to a remote server so that it can be mishandled for identity theft and future malware attacks. Although eclipsed by the super-annoying browser redirects, this activity can entail serious privacy encroachment issues down the road.
How to avoid SearchMine virus?
One of the key lessons to learn from the distribution practices employed by SearchMine virus authors is that application bundles are a potential source of malware infections, especially if they look too good to be true or if their promotion is laced with an element of pressure and urgency. Avoiding security issues in such scenarios is a matter of taking a deeper dive into the installer’s structure beyond the default mode so that the extra apps are revealed and can be unchecked. Additionally, Mac users should finally start ignoring popups that tout those fake Flash Player updates on dubious websites. No matter how exactly the redirect virus in question has made its way into a Mac, it is undoubtedly subject to removal otherwise the web browsing routine will continue to be a mess. The part below is a one-stop walkthrough to get rid of SearchMine malware.
SearchMine redirect virus manual removal for Mac
The steps listed below will walk you through the removal of this malicious application. Be sure to follow the instructions in the specified order.
Expand the Go menu in your Mac’s Finder bar and select Utilities as shown below.

Locate the Activity Monitor icon on the Utilities screen and double-click on it.

In the Activity Monitor app, look for SearchMine (Search Mine) or another process that appears suspicious. To narrow down your search, focus on unfamiliar resource-intensive entries on the list. Keep in mind that its name isn’t necessarily related to the way the threat is manifesting itself, so you’ll need to trust your own judgement. If you pinpoint the culprit, select it and click on the Stop icon in the upper left-hand corner of the screen.

When a follow-up dialog pops up asking if you are sure you want to quit the troublemaking process, select the Force Quit option.

Click on the Go menu icon in the Finder again and select Go to Folder. You can as well use the Command-Shift-G keyboard shortcut.

Type /Library/LaunchAgents in the folder search dialog and click on the Go button.

Examine the contents of the LaunchAgents folder for dubious-looking items. Be advised that the names of files spawned by malware may give no clear clues that they are malicious, so you should look for recently added entities that appear to deviate from the norm.
As an illustration, here are several examples of LaunchAgents related to mainstream Mac infections: com.pcv.hlpramc.plist, com.updater.mcy.plist, com.avickUpd.plist, and com.msp.agent.plist. If you spot files that don’t belong on the list, go ahead and drag them to the Trash.

Use the Go to Folder lookup feature again to navigate to the folder named ~/Library/Application Support (note the tilde symbol prepended to the path).

When the Application Support directory is opened, identify recently generated suspicious folders in it and send them to the Trash. A quick tip is to look for items whose names have nothing to do with Apple products or apps you knowingly installed. A few examples of known-malicious folder names are Quick Mac Booster, IdeaShared, and ProgressMatch.

Enter ~/Library/LaunchAgents string (don’t forget to include the tilde character) in the Go to Folder search area.

The system will display LaunchAgents residing in the current user’s Home directory. Look for dodgy items related to SearchMine virus (see logic highlighted in subsections above) and drag the suspects to the Trash.

Type /Library/LaunchDaemons in the Go to Folder search field.

In the LaunchDaemons path, try to pinpoint the files the malware is using for persistence. Several examples of such items cropped by Mac infections are com.pplauncher.plist, com.startup.plist, and com.ExpertModuleSearchDaemon.plist. Delete the sketchy files immediately.

Click on the Go menu icon in your Mac’s Finder and select Applications on the list.

Find the entry for an app that clearly doesn’t belong there and move it to the Trash. If this action requires your admin password for confirmation, go ahead and enter it.

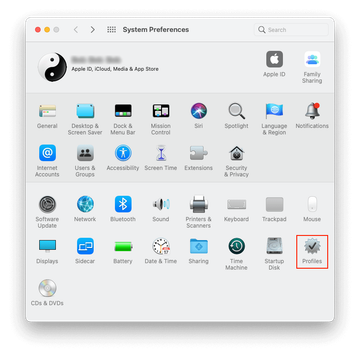
Expand the Apple menu and select System Preferences.


Proceed to Users & Groups and click on the Login Items tab.


Now select Profiles under System Preferences. Look for a malicious item in the left-hand sidebar. Several examples of configuration profiles created by Mac adware include TechSignalSearch, MainSearchPlatform, AdminPrefs, and Chrome Settings. Select the offending entity and click on the minus sign at the bottom to eliminate it.
Get rid of SearchMine virus in web browser on Mac
To begin with, the web browser settings taken over by the SearchMine virus should be restored to their default values. Although this will clear most of your customizations, web surfing history, and all temporary data stored by websites, the malicious interference should be terminated likewise. The overview of the steps for completing this procedure is as follows:
- Remove SearchMine virus from Safari
Open the browser and go to Safari menu. Select Preferences in the drop-down list.

Once the Preferences screen appears, click on the Advanced tab and enable the option saying “Show Develop menu in menu bar”.

Now that the Develop entry has been added to the Safari menu, expand it and click on Empty Caches.

Now select History in the Safari menu and click on Clear History in the drop-down list.

Safari will display a dialog asking you to specify the period of time this action will apply to. Select all history to ensure a maximum effect. Click on the Clear History button to confirm and exit.

Go back to the Safari Preferences and hit the Privacy tab at the top. Find the option that says Manage Website Data and click on it.

The browser will display a follow-up screen listing the websites that have stored data about your Internet activities. This dialog additionally includes a brief description of what the removal does: you may be logged out of some services and encounter other changes of website behavior after the procedure. If you’re okay with that, go ahead and click on the Remove All button.

Restart Safari
- Remove SearchMine in Google Chrome
Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down

When on the Settings pane, select Advanced
Scroll down to the Reset settings section.

Confirm the Chrome reset on a dialog that will pop up. When the procedure is completed, relaunch the browser and check it for malware activity.

- Remove SearchMine from Mozilla Firefox
Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).


When on the Troubleshooting Information screen, click on the Refresh Firefox button.

Confirm the intended changes and restart Firefox.
Get rid of SearchMine malware using Combo Cleaner removal tool
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove SearchMine virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the SearchMine issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove SearchMine threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.
FAQ
What is SearchMine search engine?
SearchMine is a dodgy web service camouflaged as a typical search engine. It is considered to be a browser hijacker for a number of reasons. First off, it changes a victim’s browsing preferences without their consent and adds an enterprise policy in Google Chrome to complicate the process of reverting to the correct settings. Another vector of establishing persistence on a Mac revolves around a new device profile being created under System Preferences.
Furthermore, the SearchMine app is installed beyond the victim’s awareness, constituting toxic bundles cloaked by freeware installers. One of these techniques involves phony Adobe Flash Player updates pushed on hacked or malicious websites. On top of that, the infection is usually promoted alongside adware programs and pseudo optimizers, such as Mac Cleanup Pro.
Regarding the search engine resemblance of searchmine.net, it is an illusion because the site will simply redirect all searches to another shady provider, opti-page.com. On the whole, the service in question is neither useful nor safe, therefore you should definitely steer clear of it.
How do I remove Google Chrome as my default browser on Mac?
As mentioned in the article above, the SearchMine virus affects Chrome to a somewhat bigger extent than the other popular web browsers. It tends to set a new Chrome enterprise policy that disables the option of uninstalling the malicious extension by regular means. In this scenario, you may repeatedly get notifications saying that Chrome is “managed by your organization”. This is a hurdle you must get around before applying any fixes. In addition to that, the harmful application may set Chrome as your default browser without asking.
Under the circumstances, you may want to switch to another web browser unaffected by the hijacker or allowing for easier troubleshooting. Fortunately, this isn’t complicated. Here’s what you need to do:
- Click the ‘Apple’ icon in the upper left-hand part of the screen
- Select ‘Preferences’ in the drop-down menu
- Click the ‘General’ tab
- Find the ‘Default web browser’ setting and click it to expand the list
- Select Safari or other browser you prefer to use
- Exit the ‘Preferences’ screen.
That’s it – your default web browser has been changed.
How do I get rid of Searchmine.net?
Simply re-entering the correct Internet preferences is not enough to prevent a browser from being redirected to Searchmine.net. The reason is prosaic: you are dealing with a virus rather than a misconfiguration glitch. Obviously, to get rid of Searchmine.net for good you need to address the security issue first.
Start with a virus hunt. In other words, you should scrutinize your installed apps, Login Items, and browser extensions for an object that got there behind your back. Make sure you delete all suspicious entries you manage to find. This part of the repair can be done manually or through the use of an automatic removal tool, the latter option being more effective and preferable if you aren’t very tech-savvy.
It’s not until the infection has been completely eliminated that you can customize your web browser so that it returns the right sites when you perform web search. In some cases, it may be necessary to reset the browser to its original state and then define the appropriate defaults.
How dangerous is SearchMine?
As is the case with the average adware application, SearchMine isn’t particularly harmful. It’s an awful nuisance, though. A victim cannot adjust the web browsing settings and visits searchmine.net non-stop. As part of the attack, the PUA adds a rogue enterprise policy in Google Chrome. By the way, this browser seems to be the most severely affected – perhaps due to its popularity among Mac fans. The policy trick, combined with a device profile that the infection creates on a Mac as well, allows the bad code to manage Internet preferences that are normally up to the user. This persistence adds up to the annoyance effect.
The only significant risk stemming from the SearchMine incursion boils down to privacy encroachment. The adware is known to track down various facets of its victim’s online behavior. This includes information about the visited sites, search terms, and merchants the user purchases from. These details are covertly sent to the browser hijacker’s operators who may sell them to third parties or mishandle them on their own by chasing the person with targeted ads on searchmine.net homepage and unrelated web resources.