Find out how to tell if your Mac has a virus, what to do in case of infection, and how to prevent different forms of malware from contaminating a Mac.
There is no operating system immune to viruses, and a magic vaccine to fend them all off has yet to be invented. Macs aren’t in the risky red area in this context, but nevertheless, malware outbreaks are constantly occurring in this ecosystem. Some people might think Macintosh computers are only susceptible to security issues over out-of-the-common things like the deleterious Meltdown and Spectre microprocessor flaws, but that’s a big misconception.
A slew of garden-variety PUAs (potentially unwanted apps), adware, browser redirect viruses, rogue system utilities, ransomware, and cryptojackers are out there targeting Mac machines on a massive scale. The strains that show up the most on the Mac virus heat map are ad-injecting culprits and scareware programs. The former display sponsored content on most web pages the victim is visiting, and the latter trigger fake problem reports to try and fool the users into purchasing their licenses.
Importantly, a Mac that’s acting up isn’t necessarily a virus-stricken one. For instance, a slowdown can be caused by low available memory or heaps of junk files inundating the system. Browser crashes can stem from Flash Player being out of date. Non-malware predicaments of that sort do happen, although they are generally marginal when it comes to Mac OS X and the newer macOS editions. A virus may call forth similar symptoms, but there are telltale signs of malicious activity that allow users to distinguish it from a regular performance quirk. Here is a roundup of the most common symptoms giving you clues that your Mac has a virus.
1. You’re seeing recurrent popups and scan reports that appear at random
If your Mac experience is being interrupted by popup alerts from an application you didn’t install – or so you think – then you have likely fallen victim to scareware. This category of malicious code spans fake optimization utilities and phony malware cleaners that infiltrate computers without permission and deliberately report inexistent problems to trick the victims into registering the licensed version.
There’s a series of widespread rogue programs zeroing in on Macs in 2019. One of them is a pest called Mac Cleanup Pro, which is a clone of the infamous Advanced Mac Cleaner malware. As you can tell from the screenshot below, its GUI looks quite competently tailored and the numerous system issues purportedly found during the scan yield high improvement potential. This, however, is part of the intense brainwashing fired at the user.

The cybercriminals behind such scareware campaigns have gotten proficient in mimicking genuine Mac cleaning features over time, so it may be hard to separate the wheat from the chaff. The biggest giveaway in this case is that the victims are sure they never installed the app, but that’s not quite so. These counterfeit programs arrive as part of freeware bundles, where the user opts for one app but ends up getting a few. This technique isn’t malicious per se but it can be foul play if the extra items aren’t mentioned anywhere on the default setup screens.
2. Your browser is being redirected to unwanted sites
This is a red flag indicating that your Mac has been infected with a browser hijacker. Harmful code of this type bypasses authorization when getting privileges sufficient to modify system settings and tweak the way your default web browser is functioning. Most of the time, a hijacker is an aggressive plugin that replaces the custom Internet surfing configuration with rogue values without the admin’s approval. In the aftermath of these changes, the preferred browser – be it Safari, Chrome or Firefox – starts forwarding the traffic to junk sites haphazardly or every time you launch it, open a new tab or perform Internet search. Such perpetrating entities currently doing the rounds on a large scale include TapuFind, Chill Tab, and the Bing redirect virus.
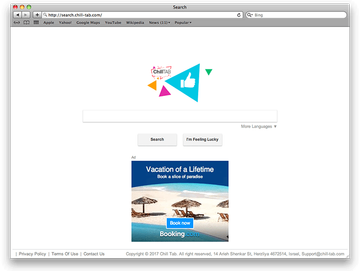
The vast majority of the landing pages are copycats of regular search engines that don’t have a built-in information lookup feature and instead return results hosted at a third-party provider. The goal of most browser hijacking viruses is to intercept one’s traffic and take advantage of it to show advertisements on the resulting pages. Essentially, this a monetization tactic done in a malign way. Sometimes you may end up on fake warning pages that say your Mac is infected with viruses – this is another way to promote scareware. Redirect viruses tend to propagate through bundling as well, where the user is unaware of additional items being installed alongside what appears to be some nifty free application.
3. You’re seeing redundant ads while surfing the web
The influx of ads on all websites you visit is attributed to the activity of Mac adware. This cluster of infections outstrips many other forms of malware in terms of their prevalence. As is the case with hijackers, adware apps do their dirty job by skewing browser settings so that a virtual layer is displayed on top of regular web page content. Again, it’s harmful browser extensions or plugins to blame for this misdemeanor. In the upshot, the plagued user’s Internet navigation experience is going to be crammed up with a host of advertisements that otherwise wouldn’t be there.

The annoying advertisements can be manifested as in-text links, banners with coupons and freebies, comparison shopping boxes, and interstitial ads that open in a separate browser tab or window. They may be labeled “Ads by Lyrics”, “Brought to you by MacShop” or similar. The fundamental difference between malware-borne ads and ones routinely displayed on sites with the webmasters’ consent is that the former are isolated to Macs infested with adware and won’t show up on the exact same web page if it’s visited from a healthy computer. The entry points for this surreptitious code include the “good old” software bundling stratagem and drive-by downloads.
Viruses may re-infect your Mac multiple times unless you delete all of their fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.4. Your personal files have been encrypted and cannot be accessed
Contrary to Windows, this isn’t a widespread case for Macintosh machines, and yet the ransomware threat shouldn’t be underestimated. There have been a few outbreaks of file-encrypting viruses that specifically target Macs. The newsmaking examples include MacRansom and KeRanger campaigns. Both are fully-fledged ransom Trojans that encode a victim’s personal data and drop ransom notes with decryption terms. These infections may additionally append an extra extension to hostage files, such as the .encrypted string which is a clear sign of the attack.
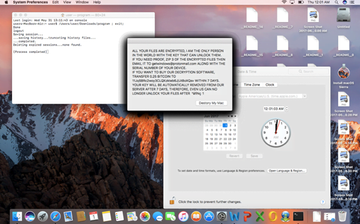
Browser lockers are a peculiar category of Mac ransomware, with the adverse influence being much milder. Unlike their crypto counterparts, they only affect Safari and make it display a ransom alert pretending to be from the FBI or other law enforcement agency. The lock screen usually says some prohibited material has been found on the computer and demands that the victim pay a fine so that the case doesn’t go to court. Fortunately, the fix is easy – all it takes is clearing browser cache.
5. Your Mac is slower than usual
There are Mac viruses that turn a contaminated host into a part of a botnet. In other words, the compromised machine will be receiving random commands from a remote C2 server, such as to participate in a DDoS attack or mine cryptocurrency for the criminals. Either way, the consequences involve continuous network communication and high CPU or GPU usage, hence a considerable slowdown of the plagued computer.
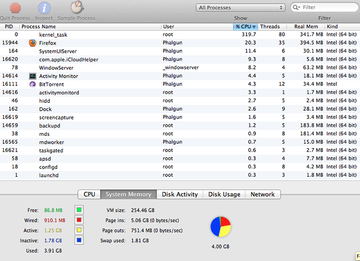
In response to interference like that, macOS will typically utilize a special service called kernel_task to cool down the processing unit by limiting CPU consumption for resource-heavy processes. The flip side of this routine is that the built-in mechanism may fail to reallocate the available memory right, eating up most or all of it by itself. At the end of the day, this predicament turns into a loop that won’t break until the malware is wiped from the system.
Avoiding Mac infections is a matter of proper online hygiene for the most part. Here are a few best practice tips to stay safe:
- Be sure to download apps from the official sources only.
- Check all installation clients for bundled items by opting out of the default setup option and selecting custom mode instead.
- Keep your operating system and installed software up to date.
- Treat email attachments with caution.
- Keep the firewall enabled.
- Don’t ignore Gatekeeper’s alerts.
- Maintain backups of important data.
- Use a security solution you trust.
If you have noticed any of the above symptoms, focus on the countermeasures right away. First, identify the type of the infection based on the descriptions provided in this article. Then, move on to the cleanup that’s relevant to the specific virus. Finally, remediate system changes made by the culprit if necessary. This brings us to the applicable walkthroughs to handle a Mac malware quandary.
Mac virus manual removal
The steps listed below will walk you through the removal of the unwanted application that hit your Mac. Be sure to follow the instructions in the order specified.
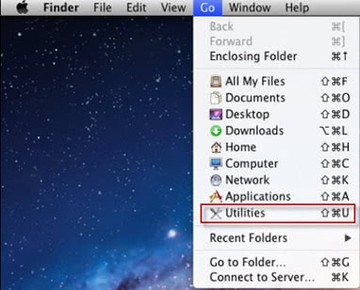
- Open up the Utilities folder as shown below
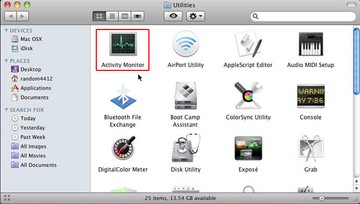
- Locate the Activity Monitor icon on the screen and double-click on it
- Under Activity Monitor, find the entry for the harmful program, select it and click Quit Process
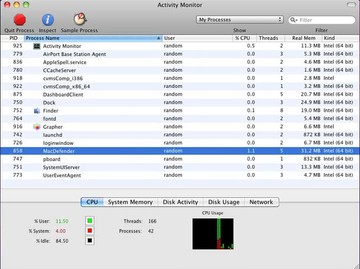
- A dialog should pop up, asking if you are sure you would like to quit the malicious executable. Select the Force Quit option
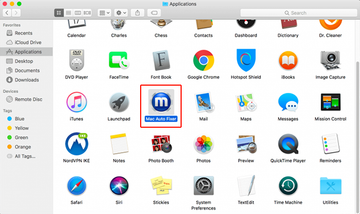
- Expand the Go menu in Apple Finder and select Applications on the list. Find the entry for the virus you have identified, right-click on it and select Move to Trash. If user password is required, go ahead and enter it
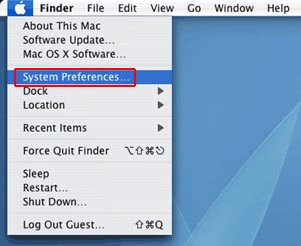
- Now go to Apple Menu and pick the System Preferences option
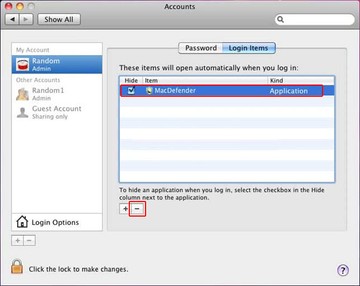
- Select Accounts and click the Login Items button. The system will come up with the list of the items that launch when the box is started up. Locate the unwanted entry there and click on the "-" button
Get rid of malicious browser add-ons on Mac
To begin with, settings for the web browser that got hit by a hijacker or adware should be restored to their default values. The overview of steps for this procedure is as follows:
- Reset Safari
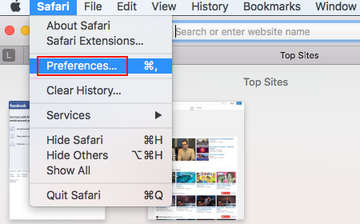
- Open the browser and go to Safari menu. Select Preferences in the drop-down list
- Once the Preferences screen appears, hit the Privacy tab at the top. Find the option that says Remove All Website Data and click on it
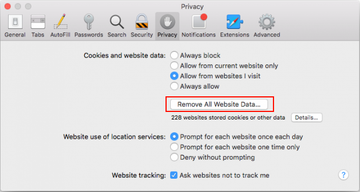
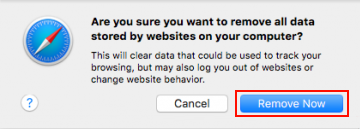
- The system will display a confirmation dialog that also includes a brief description of what the reset does. Specifically, you may be logged out of some services and encounter other changes of website behavior after the procedure. If you’re okay with that, go ahead and click the Remove Now button
- In order to selectively clear data generated by certain websites only, not all of them, hit the Details button under the Privacy section of Safari Preferences

- This feature will list all websites that have stored potentially sensitive data, including cache and cookies. Select the one, or ones, that might be causing trouble and click the appropriate button at the bottom (Remove or Remove All). Click the Done button to exit.
- Open the browser and go to Safari menu. Select Preferences in the drop-down list
- Reset Google Chrome
- Open Chrome, click the More (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down
- When on the Settings pane, select Advanced
- Scroll down to the Reset settings section. Under the Restore settings to their original defaults option, click the Reset settings button
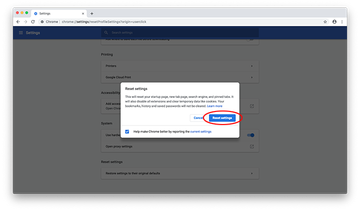
- Confirm the Chrome reset on a dialog that will pop up. When the procedure is completed, relaunch the browser and check it for malware activity.
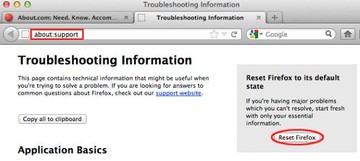
- Reset Mozilla Firefox
- Open Firefox and select Help – Troubleshooting Information
- On the page that opened, click the Reset Firefox button