The subject matter of this article is TapuFind, a Mac virus that displays irritating popups, redirects browsers, and hence should be removed without more ado.
Update:
| Threat Profile | |
|---|---|
| Name | TapuFind (MacAppExtensions) browser hijacker |
| Category | Mac adware, PUA, browser hijacker, redirect virus |
| IP Address | 13.66.51.37 |
| Related domains | Search.tapufind.com, tab.tapufind.com |
| Symptoms | Redirects web browser to Yahoo via third-party websites, adds sponsored content to search results, causes system slowdown, resists regular removal |
| Distribution Techniques | Fake Adobe Flash Player update popups, malware-riddled app bundles, spam |
| Severity Level | Medium |
| Damage | Unwanted changes of custom browsing settings, privacy issues due to Internet activity tracking, search redirects, redundant ads |
| Removal | Scan your Mac with Combo Cleaner to detect all files related to the browser hijacker. Use the tool to remove the infection if found. |
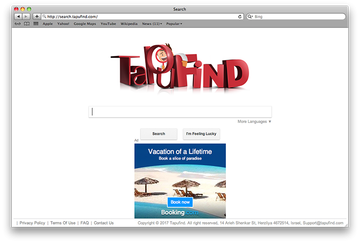
The TapuFind Mac virus is yet another unwelcome echo from the Download Valley, the ill-famed syndicate of Israeli firms that have been coining adware threats for years. These companies can only be considered legit by the slimmest of margins, given their shady software distribution practices and the aggressive way their digital products behave. And yet, this adverse phenomenon appears to be here to stay and continues to thrive at the expense of regular users’ peace of mind. The applet in question, TapuFind, is a combo of adware and browser hijacker as it displays misleading alerts in the victim’s web browser and forwards the traffic to its landing pages. These include search.tapufind.com and tab.tapufind.com – the former replacing the infected Mac user’s default search provider, and the latter being imposed as the new tab page. Both are designed to look like a regular web search service but they return Yahoo Search custom results instead of their own. Importantly, this perpetrating app is doing the rounds by means of bundling, so it’s always worthwhile to scrutinize setup clients when you are about to install new programs. If any extra items are there, deselect them at once.
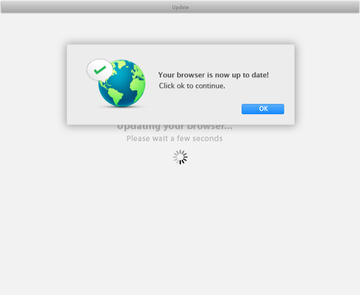
From a functional perspective, this malicious code bears a close resemblance to the ChillTab virus. It spreads in a similar fashion and causes pretty much the same side effects on contaminated Macs. Moreover, the vendor’s address, which is indicated in the landing page footers of both of these malicious services, is an exact match. The attack proper is a multilayered process. Aside from the redirect activity, one of the abominable impacts has to do with fake popup alerts that appear in the affected browser. These splash screens say, “Your browser is now up to date” and thus pretend to notify the victim of a successful installation of new features in Safari, Google Chrome, or Mozilla Firefox. The trick is that the user is prompted to click the OK button on the manipulative ad, which is likely to fire up another download of random harmful software onto the Mac.
One more flagrant element of the onslaught is the traffic interception activity. The TapuFind virus runs with admin privileges, because it’s coded that way. Meanwhile, the targeted Mac user is never asked for permission to grant these elevated rights on the machine, which is per se a clear sign of malware behavior. Such a tactic allows the infection to make changes to the victim’s web surfing presets while bypassing their consent altogether. This is how it succeeds in replacing the preferred search engine, new tab page and homepage with search.tapufind.com or tab.tapufind.com. As a result, the web navigation routine will be nearly isolated to visiting the unwanted site over and over. When processing a random request the victim enters in the search bar, the browsing session is forwarded to a Yahoo Hosted Search (YHS) page featuring Safe Finder, a known-malicious service involved in large-scale traffic reorganization foul play targeting Macs. To add insult to injury, the rogue browser update popups described above will be further diminishing the user’s online experience. Ultimately, TapuFind ends up dominating the whole Internet navigation on the plagued Mac and prevents the victim from reverting to the correct configuration via the regular mechanisms.
TapuFind redirect virus may re-infect your Mac multiple times unless you delete all of its fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.TapuFind virus removal, though, is manageable as long as you leverage a tandem of several cleaning vectors. Be sure to follow the tips below to get rid of the nasty browser hijacker and keep it from reinstalling itself. Before you proceed, bear in mind that in some cases the culprit may not be listed in the Applications pane, unlike benign Mac software. Instead, most of its core components might reside in the /Users/Shared directory. These entities are manifested as multiple folders named according to the following pattern: App_[random string]. Interestingly, the gibberish long character sequences in the names of these items make them easy to identify, so that’s kind of good news in terms of the fix. Each one of these folders contains an entry called MacAppExtensions.app. This is a critical file accompanying the TapuFind hijack. It executes the nasty browser poisoning routine and additionally plays a role in the persistence of this threat by meddling with the startup items on the host Mac. Therefore, don’t fail to find and delete this object as part of the cleaning procedure.
TapuFind redirect virus manual removal for Mac
The steps listed below will walk you through the removal of this malicious application. Be sure to follow the instructions in the specified order.
Expand the Go menu in your Mac’s Finder bar and select Utilities as shown below.

Locate the Activity Monitor icon on the Utilities screen and double-click on it.

In the Activity Monitor app, look for TapuFind, MacAppExtensions.app, or another process that appears suspicious. To narrow down your search, focus on unfamiliar resource-intensive entries on the list. Keep in mind that its name isn’t necessarily related to the way the threat is manifesting itself, so you’ll need to trust your own judgement. If you pinpoint the culprit, select it and click on the Stop icon in the upper left-hand corner of the screen.

When a follow-up dialog pops up asking if you are sure you want to quit the troublemaking process, select the Force Quit option.

Click on the Go menu icon in the Finder again and select Go to Folder. You can as well use the Command-Shift-G keyboard shortcut.

Type /Library/LaunchAgents in the folder search dialog and click on the Go button.

Examine the contents of the LaunchAgents folder for dubious-looking items. The objects known to be associated with TapuFind virus are as follows: com.tapufind.plist and com.SoftwareUpdater.agent.plist.
Be advised that the names of files spawned by malware may give no clear clues that they are malicious, so you should look for recently added entities that appear to deviate from the norm. As an illustration, here are several examples of LaunchAgents related to mainstream Mac infections: com.pcv.hlpramc.plist, com.updater.mcy.plist, com.avickUpd.plist, and com.msp.agent.plist. If you spot files that don’t belong on the list, go ahead and drag them to the Trash.

Use the Go to Folder lookup feature again to navigate to the folder named ~/Library/Application Support (note the tilde symbol prepended to the path).

When the Application Support directory is opened, identify recently generated suspicious folders in it and send them to the Trash. A quick tip is to look for items whose names have nothing to do with Apple products or apps you knowingly installed. A few examples of known-malicious folder names are tab.chill-tab.com, SoftwareUpdater, and IdeaShared.

Enter ~/Library/LaunchAgents string (don’t forget to include the tilde character) in the Go to Folder search area.

The system will display LaunchAgents residing in the current user’s Home directory. Look for dodgy items related to TapuFind virus (see logic highlighted in subsections above) and drag the suspects to the Trash.

Type /Library/LaunchDaemons in the Go to Folder search field.

In the LaunchDaemons path, try to pinpoint the files the malware is using for persistence. Several examples of such items cropped by Mac infections are com.pplauncher.plist, com.startup.plist, and com.ExpertModuleSearchDaemon.plist. Delete the sketchy files immediately.

Click on the Go menu icon in your Mac’s Finder and select Applications on the list.

Find the entry for TapuFind, MacAppExtensions, or another app that clearly doesn’t belong there and move it to the Trash. If this action requires your admin password for confirmation, go ahead and enter it.

Expand the Apple menu and select System Preferences.


Proceed to Users & Groups and click on the Login Items tab.


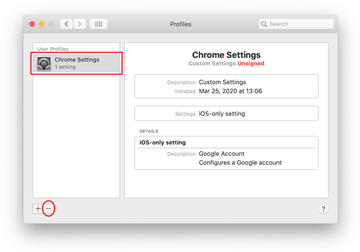
Now select Profiles under System Preferences. Look for a malicious item in the left-hand sidebar. Several examples of configuration profiles created by Mac adware include TechSignalSearch, MainSearchPlatform, AdminPrefs, and Chrome Settings. Select the offending entity and click on the minus sign at the bottom to eliminate it.

Get rid of TapuFind redirect virus in web browser on Mac
To begin with, the web browser settings taken over by the TapuFind redirect virus should be restored to their default values. Although this will clear most of your customizations, web surfing history, and all temporary data stored by websites, the malicious interference should be terminated likewise. The overview of the steps for completing this procedure is as follows:
- Remove TapuFind redirect virus from Safari
Open the browser and go to Safari menu. Select Preferences in the drop-down list.

Once the Preferences screen appears, click on the Advanced tab and enable the option saying “Show Develop menu in menu bar”.

Now that the Develop entry has been added to the Safari menu, expand it and click on Empty Caches.

Now select History in the Safari menu and click on Clear History in the drop-down list.

Safari will display a dialog asking you to specify the period of time this action will apply to. Select all history to ensure a maximum effect. Click on the Clear History button to confirm and exit.

Go back to the Safari Preferences and hit the Privacy tab at the top. Find the option that says Manage Website Data and click on it.

The browser will display a follow-up screen listing the websites that have stored data about your Internet activities. This dialog additionally includes a brief description of what the removal does: you may be logged out of some services and encounter other changes of website behavior after the procedure. If you’re okay with that, go ahead and click on the Remove All button.

Restart Safari
- Remove TapuFind redirect in Google Chrome
Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down

When on the Settings pane, select Advanced
Scroll down to the Reset settings section.

Confirm the Chrome reset on a dialog that will pop up. When the procedure is completed, relaunch the browser and check it for malware activity.

- Remove TapuFind redirect from Mozilla Firefox
Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).


When on the Troubleshooting Information screen, click on the Refresh Firefox button.

Confirm the intended changes and restart Firefox.
Get rid of TapuFind redirect virus Mac using Combo Cleaner removal tool
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove TapuFind redirect virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the TapuFind redirect issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove TapuFind redirect threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.
FAQ
What is TapuFind?
TapuFind is a highly persistent Mac infection whose primary goal is browser takeover. This activity fully contradicts the ‘official’ facet of the app, which is marketed as a powerful web search enhancement service. In fact, most victims don’t even have a chance to examine its purported features because it infiltrates computers without their knowledge and approval.
Whereas installation behind the scenes is a giveaway big enough to categorize TapuFind as a virus, adware, or PUA (potentially unwanted application), there are plenty of other characteristics that leave no room for doubt regarding its malicious gist. The application replaces a victim’s preferred search engine and new tab page with search.tapufind.com and tab.tapufind.com, respectively. Although these landing pages aren’t identical, they both resemble a garden-variety search provider. However, whatever keyword you enter, the results will be returned via Yahoo Search. The operators of this fraud, evidently, generate some kind of affiliate revenue this way.
The infection undermines the victim’s experience in one more way. It promotes other PUAs by means of rogue popup alerts about a browser update. This way, the user is duped into opting for the fake update, which is another malicious program in disguise. Yet another serious concern is that TapuFind is problematic to delete as long as the user goes the well-trodden standard uninstall route. It drops a component called “MacAppExtensions.app” that adds an extra layer of obstinacy to the browser hijacker. All of these hideous features, combined with the fact that TapuFind harvests details about one’s web surfing habits, make it an app that should be removed without a second thought.
How do I remove TapuFind extension from Safari?
If you think you can dodge this browser hijack by simply removing the respective browser extension, TapuFind will prove you wrong. It causes a more overarching impact, leaving a footprint in macOS operation overall. Therefore, to prevent Safari from being redirected to search.tapufind.com and tab.tapufind.com, the fix should start beyond the browser itself.
First, go into the Activity Monitor, Applications, and Login Items and look for the entries related to the virus. Furthermore, navigate to Library/LaunchAgents and ~Library/LaunchAgents folders and check them for items that may be associated with TapuFind (see tutorial above for detailed steps). Whatever you find should be dragged to the Trash. Make sure you also go to the /Users/Shared folder and look for directories containing an entity called “MacAppExtensions” or “MacAppExtensions.app”. Delete these ones without hesitation.
Now that the underlying infection has been eliminated, you can finally implement the troubleshooting in Safari. Start by going to the browser’s Extensions pane. Locate TapuFind or other suspicious item with a random-looking name. Disable and remove the perpetrating extension. Restart Safari and see if the issue has been fixed.
If there are no more redirects, you are good to go. In case Safari keeps acting up, though, you should additionally empty caches and clear history to remove all website data. This procedure will log you out of personal accounts and wipe other personalized settings, and yet it is an effective way of stopping malicious activity in the browser.
How do I stop the virus from popping up on my Mac?
Preventing virus-borne popups on a Mac is a complex process consisting of two major stages. First, you need to identify the malicious application and obliterate all of its files, including obfuscated ones that will reinstall the infection unless deleted. Secondly, the fix requires some tidying at the browser level so that the unwanted program won’t meddle with the Internet preferences and stops executing shady scripts on regular web pages.
Virus removal may resemble a hide-and-seek quest because Mac threats are designed to be persistent and hide their traces from the victim. Most users are knowledgeable about the traditional method that boils down to sending the dodgy item from the Applications folder to the Trash, deleting its icon from the Dock, and emptying the Trash when done. Unfortunately, this technique alone doesn’t work with the likes of TapuFind.
You’ll additionally have to examine the LaunchAgents (both at the root level and in the user’s home directory), LaunchDaemons, Application Support folder contents, Device Profiles list, and Login Items. Whatever looks out of place should be removed. In many cases, deleting these artifacts is impossible unless you force quit the culprit’s core process in the Activity Monitor beforehand.
To rid a web browser of the virus influence, uninstalling a malicious extension and redefining the correct preferences should do the trick as long as the add-on is listed in the settings. This isn’t always the case, though, and therefore resetting the browser to its original state may be the only effective way to take care of the issue. Keep in mind that Safari doesn’t have a dedicated reset feature, so you’ll need to empty its caches and clear the history along with cookies and all website data. The summary of these techniques is provided in the tutorial above.
How do I get rid of MacAppExtensions?
To begin with, MacAppExtensions is a malicious component underlying the TapuFind browser hijack. Its presence on a Mac is eclipsed by unauthorized overhaul of the browsing settings, which entails incessant redirects to search.tapufind.com or tab.tapufind.com. However, the overall system footprint of this entity is just as impactful as the browser mess it causes, and the fix is only effective if MacAppExtensions is removed.
To get rid of this evasive entity, you should open the Finder and head to the Macintosh HD/Users/Shared directory. You will see multiple random-named folders spawned by the infection. MacAppExtensions.app is going to be inside these folders. Its icon will typically have the TapuFind logo next to it. When found, delete all copies of the baddie right away and then empty the Trash. Also, look for traces of this object among the installed browser extensions and remove it if spotted.
