Remove KeRanger, the first known ransomware crafted for Mac OS X, learn how to avoid this assault and restore the files encrypted by this infection.
The worst nightmare of the Mac user community has come true as the first Mac ransomware campaign commenced last weekend. In fact, a few months ago a JavaScript based crypto plague called Ransom32 emerged, which caused serious concerns in the expert circles because it could potentially run on platforms other than Windows. It turned out these predictions weren’t too far off the actual state of things. The recently discovered infection called KeRanger is reportedly propagating over a mutilated downloader of the Transmission BitTorrent Client. The success of malicious payload serving is backed by the popularity of the latter application with Mac customers. The version of Transmission that’s unsafe is 2.90. At this point, the developer has put up a warning on their website with a recommendation to urgently upgrade to 2.92, which is a malware-free edition.
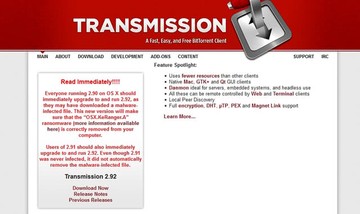
Obviously, the aforementioned vendor’s site had suffered a hack incident therefore the perpetrators were able to covertly substitute the original DMG file installer with an altered one carrying the harmful drive-by. The reason why the Gatekeeper solution failed to block these downloads is because the app featured a valid developer certificate, so the defenses simply didn’t identify the hazard on the initial stage. Thankfully, the cert has now been blacklisted, so Gatekeeper is flagging the corrupt setups.
Once the KeRanger ransomware ends up inside a Mac, it adds an executable disguised as ‘General.rtf’ file. When this object is automatically launched, it harvests machine-specific details and transmits these identifiers to the Command and Control server via Tor. Then, the virus scans the hard drive and encrypts files with widespread extensions, including documents, images, audio, video, certificates, emails, archives, and source code entities. Every ciphered item is appended with the .encrypted string at the end of the filename, so a ‘flower.jpg’ file will look like this – ‘flower.jpg.encrypted’. This part of the attack being completed, the victim will see data recovery instructions in a file named README_FOR_DECRYPT.txt.
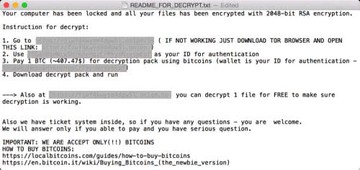
According to the ransom notes, the infected Mac user needs to submit 1 BTC (about $400) in order to be able to download the decrypt pack. The document also contains the .onion address and the person’s unique ID for authentication with the malign service. The Tor website enables the victim to decrypt 1 file for free and provides the option to pay the ransom, send a ticket and read some FAQs. If the user chooses not to redeem their personal data with the deadline of 72 hours, the amount for buyout will most likely increase.
KeRanger leverages the RSA-2048 cryptographic algorithm to encode files. This is an asymmetric cipher, where the public key is used for encryption and the private key – for decryption. The latter high-entropy chunk of information stays on the extortionists’ remote server throughout the onslaught, so it’s not feasible to restore anything by brute-forcing or similar techniques. Doing the buyout, on the other hand, is a terrible idea. So what should the contaminated Mac users do? First and foremost, uninstall the KeRanger ransomware and try to use a couple of tips and tricks to reinstate the locked files.
KeRanger ransomware manual removal for Mac
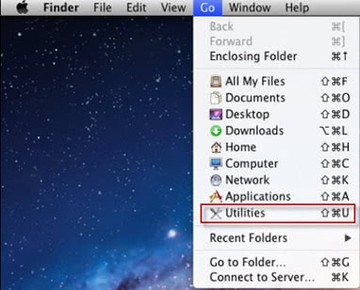
The steps listed below will walk you through the removal of this application. Be sure to follow the instructions in the order specified.
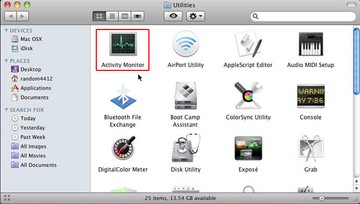
• Open up the Utilities folder as shown below
• Locate the Activity Monitor icon on the screen and double-click on it
• Under Activity Monitor,find suspicious entries General.rtf, kernelservice, kernelpid, kerneltime, kernelcomplete, Search Marquis or Search Baron), select them and click Quit Process for each.
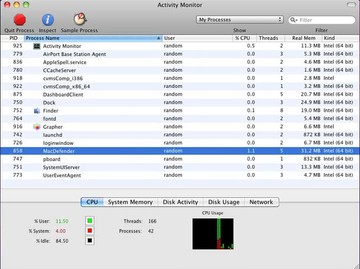
• A dialog should pop up, asking if you are sure you would like to quit the executable. Select the Force Quit option
• Click the Go button again, but this time select Applications on the list. Find the Transmission entry on the interface, right-click on it and select Move to Trash. If user password is required, enter it. After the cleanup is performed all the way, you can reinstall the safe version of the app, that is, 2.92 and onward
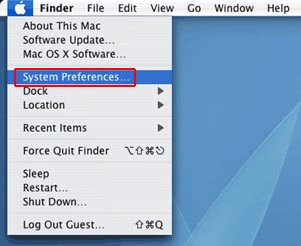
• Now go to Apple Menu and pick the System Preferences option
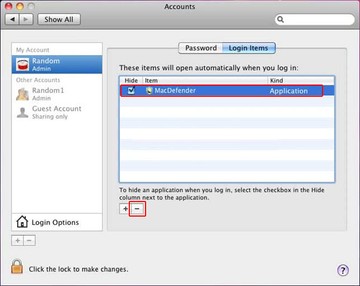
• Select Accounts and click the Login Items button. Mac OS will come up with the list of the items that launch when the box is started up. Locate suspicious entries there and click on the "-" button for those
OSX.KeRanger virus automatic removal for Mac
Unless you are a power user, you run the risk of failing to find and delete some components of this infection on your own. Overlooking dodgy LaunchAgents, LaunchDaemons, and malicious configuration profiles means that the threat will continue to cause problems. A more efficient alternative to manual cleanup is to use MacBooster 8, an application that will scan your Mac for issues and fix them automatically.
The app comes with a competitive toolkit that includes Virus & Malware Scan as well as a decent range of optimization features. Therefore, not only does it identify and vanquish mainstream Mac viruses but it also releases disk space and memory so that your computer gets a performance tune-up. Here’s how to go the route of KeRanger ransomware - Transmission 2.9 malware removal with MacBooster:
Download and install MacBooster 8.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Pro version of MacBooster.
Open the app. When on the System Status screen, click the Scan button to check your Mac for viruses, junk files, and memory hogs.

Once the scan is completed, inspect the report to see what security threats and performance issues have been found. To get rid of the detected items, click the Fix button at the bottom.

As an extra step, you might want to make sure that the KeRanger ransomware - Transmission 2.9 malware infection leftovers are no longer riddling your web browser. This can be the case in an adware scenario. Proceed to the Privacy Protection feature in the left-hand sidebar, select the default browser in the list, and click the Clean button.

In case your web browser is still acting up, follow the steps provided in the previous section of this guide to get rid of the adverse web surfing interference for good.