- What is a browser redirect Mac virus?
- Types of Mac browser redirect viruses
- Persistence techniques in the repertoire of a Mac redirect virus
- Browser redirect virus manual removal for Mac
- Get rid of browser redirect virus in web browser on Mac
- Get rid of a browser redirect virus using Combo Cleaner removal tool
Macs are on the receiving end of attacks in which browser settings are skewed by redirect viruses that promote fake search engines and other sketchy services.
What is a browser redirect Mac virus?
With the threat landscape for macOS being increasingly diverse, there are thankfully still few strains of highly severe malicious code hitting this environment with real-world incursions. It has seen several ransomware outbreaks, but with limited reach that keeps this disgusting phenomenon from becoming a game-changer so far. Rootkits and spyware that provide an attacker with backdoor access and pull off privilege escalation are in the proof-of-concept (PoC) area rather than being a ubiquitous peril. This is largely due to the commendable protections on Apple’s end. Nonetheless, these computers are massively raided with less harmful, yet incredibly annoying infections called browser redirect viruses. As the name suggests, they reroute Internet traffic over to unwanted websites without asking for consent. To set such an attack in motion, a piece of toxic software replaces the web surfing customizations with something unrelated behind the victim’s back.
As a result, the affected browser turns into a generator of hits for advertising networks or for sites whose authors are okay with boosting their SEO (and hence search engine presence) via shadowy schemes. Aside from that, the destinations may include tech support scams, credential phishing pages, and cesspools of dangerous applications spreading through drive-by download trickery. None of this would take place if users exerted due caution with the software they install. Most browser redirect viruses, or browser hijackers as they are often referred to, spread under the cover of freeware bundles that push several programs in one go. This isn’t a malicious mechanism per se, but cybercriminals have weaponized it to disguise toxic stuff. In that scenario, the user accepts all terms of the multi-component installation client, only to let the infection in alongside a straightforwardly promoted benign app. When dealing with bundles, it is strongly recommended to select the custom mode instead of the default one and then uncheck whatever appears to be suspicious. In addition to this attack vector, crooks often fake popular extensions and upload them to official browser marketplaces if they succeed in bypassing the verification controls that are in place.
Browser redirect virus may re-infect your Mac multiple times unless you delete all of its fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.Types of Mac browser redirect viruses
The above-mentioned distribution techniques (bundling and extension forgery) are shared by all browser hijackers that target Mac machines. Another common denominator is the redirect principle that boils down to changing all or some of the main Internet preferences, such as the default search engine, homepage, and new tab page. What makes each sample stand out from the rest, though, is the path of the rerouting process as well as the landing page. Oddly enough, this arena is currently dominated by culprits that redirect to legitimate search providers. One species is the Bing redirect virus. This long-running campaign harbors a handful of hijackers that drive web traffic to Bing.com via a network of affiliated services. Several notorious examples of “accomplice” sites are SearchBaron.com, SearchMarquis.com, Search1.me, and Nearbyme.io.
An equally prolific campaign relies on the Yahoo redirect virus. By taking over victims’ browsers, it forces hits to pseudo search engines that lead to Yahoo Hosted Search (YHS) results. The nastiest spin-offs are Safe Finder, Any Search, TapuFind, Chill Tab, SearchMine, Search Pulse, and TabSearch. It seems utterly bizarre that malicious actors have made some of the world’s most popular services of their kind the landing pages in their stratagems. The most plausible theory is that Bing and Yahoo are abused to smokescreen the hideous stuff happening en route. With the malware on board, the browser is configured to send nearly inconspicuous queries to dodgy URLs, many of which are linked with the APIs of fraudulent ad networks. An additional layer of monetization may relate to legitimate affiliate platforms run by the above tech giants, but it’s hard to believe that malefactors could be gaming their rigid controls for years.
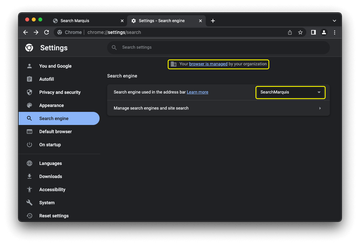
Some Mac browser hijackers don’t go with the flow, making victims visit pages that display fake virus alerts, limiting the redirect activity to worthless “proprietary” search services, or displaying bogus human verification pop-ups that cloak permissions to control the browser. However, most of these samples are short-lived and fairly marginal. Regardless of the type, cross-browser nature is a hallmark of all these nasties. Whether you prefer Safari, Google Chrome, Mozilla Firefox, or Opera, the virus you may come across is almost certainly capable of affecting it, with subtle differences. For instance, a message that says “Your browser is managed by your organization” (as illustrated in the screenshot above) is a very common attack symptom in Chrome.
Persistence techniques in the repertoire of a Mac redirect virus
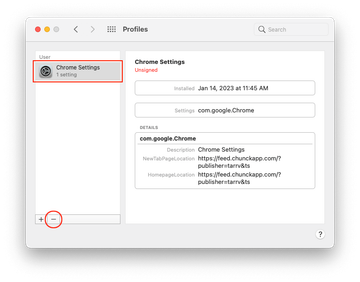
This form of malware sticks to a style of attack where the ability to resist regular disinfection is paramount. To that end, redirect viruses go beyond sprinkling their files across system folders such as Application Support, LaunchAgents, and LaunchDaemons. A classic trick is to mishandle configuration profiles, a feature mostly used by network admins to enforce corporate policies within organizations. The power of this functionality lies in specifying restrictions and patterns for different macOS components or third-party software, including web browsers. For instance, it can narrow down the user’s Internet activities to certain websites. The image below shows a fraudulent profile that defines a malware-backed resource as the default homepage and new tab page in Google Chrome.
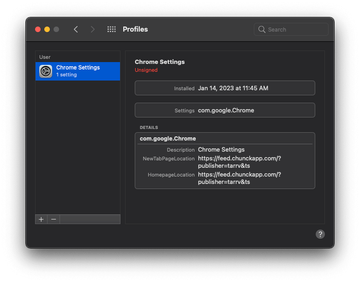
The same tweak can be done for Safari and other browsers detected in the target system. This method prevents the victim from redefining their preferences manually, as the wrong settings are sort of hard-coded and cannot be modified unless the profile vanishes. The infection may further enhance its foothold in a Mac by setting up a policy called ExtensionInstallForcelist, which gives attackers the green light to install add-ons in Chrome without the user’s permission. Combining browser policies and device profiles is an effective way for the virus to survive regular removal and extend the attack surface through inconspicuous downloads of other malware.
To gain extra privileges at the level of a web browser, some strains employ a pop-up overlay mechanism in which an eye-catching alert appears on top of another. The idea is to make the user accept a tricky request unknowingly. Notifications that say “Your computer is low on memory” and “Your hard drive is almost full” exemplify such manipulation and accompany attacks by the above-mentioned Search Baron and Search Marquis baddies. Each one obscures a dialog where a malicious app asks for permission to control the browser – this includes access to documents and data as well as the ability to perform actions within the app.
All in all, the prevalence of this exploitation means that a browser is juicy prey for bad actors. Aside from providing significant traffic monetization opportunities, it retains personal information that can also be in the crosshairs. Therefore, proper software installation hygiene is in your best interest, since it helps you steer clear of booby-trapped bundles with a high chance of redirect viruses lurking inside. If a malicious program like that is already in, here are some tips to get rid of it and redefine the browser settings.
Browser redirect virus manual removal for Mac
The steps listed below will walk you through the removal of this malicious application. Be sure to follow the instructions in the specified order.
Expand the Go menu in your Mac’s Finder bar and select Utilities as shown below.

Locate the Activity Monitor icon on the Utilities screen and double-click on it.

In the Activity Monitor app, look for a process that appears suspicious. To narrow down your search, focus on unfamiliar resource-intensive entries on the list. Keep in mind that its name isn’t necessarily related to the way the threat is manifesting itself, so you’ll need to trust your own judgement. If you pinpoint the culprit, select it and click on the Stop icon in the upper left-hand corner of the screen.

When a follow-up dialog pops up asking if you are sure you want to quit the troublemaking process, select the Force Quit option.

Click on the Go menu icon in the Finder again and select Go to Folder. You can as well use the Command-Shift-G keyboard shortcut.

Type /Library/LaunchAgents in the folder search dialog and click on the Go button.

Examine the contents of the LaunchAgents folder for dubious-looking items. Be advised that the names of files spawned by malware may give no clear clues that they are malicious, so you should look for recently added entities that appear to deviate from the norm.
As an illustration, here are several examples of LaunchAgents related to mainstream Mac infections: com.updater.mcy.plist, com.avickUpd.plist, and com.msp.agent.plist. If you spot files that don’t belong on the list, go ahead and drag them to the Trash.

Use the Go to Folder lookup feature again to navigate to the folder named ~/Library/Application Support (note the tilde symbol prepended to the path).

When the Application Support directory is opened, identify recently generated suspicious folders in it and send them to the Trash. A quick tip is to look for items whose names have nothing to do with Apple products or apps you knowingly installed. A few examples of known-malicious folder names are com.AuraSearchDaemon, ProgressSite, and IdeaShared.

Enter ~/Library/LaunchAgents string (don’t forget to include the tilde character) in the Go to Folder search area.

The system will display LaunchAgents residing in the current user’s Home directory. Look for dodgy items related to the browser redirect virus (see logic highlighted in subsections above) and drag the suspects to the Trash.

Type /Library/LaunchDaemons in the Go to Folder search field.

In the LaunchDaemons path, try to pinpoint the files the malware is using for persistence. Several examples of such items cropped by Mac infections are com.ConnectionCache.system.plist, com.mulkeyd.plist, and com.pplauncher.plist. Delete the sketchy files immediately.

Click on the Go menu icon in your Mac’s Finder and select Applications on the list.

Find the app that clearly doesn’t belong there and move it to the Trash. If this action requires your admin password for confirmation, go ahead and enter it.

Expand the Apple menu and select System Preferences.


Proceed to Users & Groups and click on the Login Items tab.

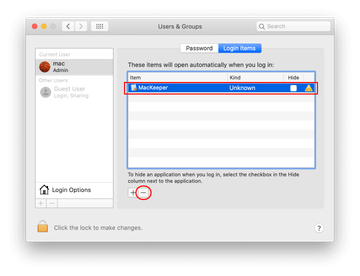
Now select Profiles under System Preferences. Look for a malicious item in the left-hand sidebar. Several examples of configuration profiles created by Mac adware include AdminPrefs, TechSignalSearch, MainSearchPlatform, and Safari Settings. Select the offending entity and click on the minus sign at the bottom to eliminate it.

Get rid of browser redirect virus in web browser on Mac
To begin with, the web browser settings taken over by the browser redirect virus should be restored to their default values. Although this will clear most of your customizations, web surfing history, and all temporary data stored by websites, the malicious interference should be terminated likewise. The overview of the steps for completing this procedure is as follows:
- Remove browser redirect virus from Safari
Open the browser and go to Safari menu. Select Preferences in the drop-down list.

Once the Preferences screen appears, click on the Advanced tab and enable the option saying “Show Develop menu in menu bar”.

Now that the Develop entry has been added to the Safari menu, expand it and click on Empty Caches.

Now select History in the Safari menu and click on Clear History in the drop-down list.

Safari will display a dialog asking you to specify the period of time this action will apply to. Select all history to ensure a maximum effect. Click on the Clear History button to confirm and exit.

Go back to the Safari Preferences and hit the Privacy tab at the top. Find the option that says Manage Website Data and click on it.

The browser will display a follow-up screen listing the websites that have stored data about your Internet activities. This dialog additionally includes a brief description of what the removal does: you may be logged out of some services and encounter other changes of website behavior after the procedure. If you’re okay with that, go ahead and click on the Remove All button.

Restart Safari
- Remove browser redirect in Google Chrome
Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down

When on the Settings pane, select Advanced
Scroll down to the Reset settings section.

Confirm the Chrome reset on a dialog that will pop up. When the procedure is completed, relaunch the browser and check it for malware activity.

- Remove browser redirect from Mozilla Firefox
Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).


When on the Troubleshooting Information screen, click on the Refresh Firefox button.

Confirm the intended changes and restart Firefox.
Get rid of a browser redirect virus using Combo Cleaner removal tool
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove browser redirect virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the browser redirect issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove browser redirect threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.
