With the Chrome redirect Mac virus being a mainstream and an escalating threat, this write-up will help remove it and overthrow the unwanted browser settings.
Update:
| Threat Profile | |
|---|---|
| Name | Chrome redirect virus Mac |
| Category | Mac browser hijacker, Mac adware, PUA |
| Related Domains | search.safefinder.com, search.tapufind.com, search.anysearch.net, search.chill-tab.com, search.searchpulse.net, search.landslidesearch.com, searchmine.net, searchlee.com, searchmarquis.com, searchbaron.com, searchsnow.com, searchitnow.info, mybrowser-search.com, nearbyme.io, r.a9g.io |
| Symptoms | Redirects Chrome to Bing, Yahoo or fake search engines via ad network APIs, makes a Mac run slower than usual |
| Distribution Techniques | Freeware bundles, fake software updates, misleading pop-ups |
| Severity Level | Medium |
| Damage | Privacy issues due to Internet activity tracking, search redirects, unauthorized modification of browsing preferences, redundant ads |
| Removal | Scan your Mac with Combo Cleaner to detect all files related to the browser hijacker. Use the tool to remove the infection if found. |
What is Chrome redirect virus?
Google Chrome is the undisputed champion in the global league of web browsers for a good reason. It is fast, intuitive, secure, and well-maintained. Unsurprisingly, cybercriminals think of its heavyweight status as an opportunity to extend their reach. There are a plethora of malicious apps, plugins, and extensions in the wild that subordinate Chrome’s behavior and take over the key preferences specified by the user. This overwhelming focus goes for Mac machines in particular. The following paragraphs will shine the light on the most widespread threats collectively referred to as the Chrome redirect virus Mac.
Bing redirect schemes in Chrome
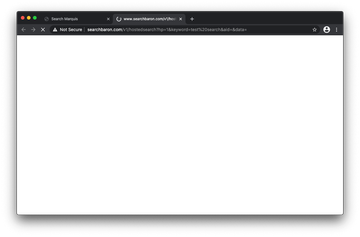
Forcibly reorganizing a Mac user’s web surfing activities to land the traffic at Bing.com is arguably the dominating plot in the Chrome environment at this point. The trend started gaining traction in the summer of 2019 with the debut of the Search Marquis and Search Baron infections. The evil duet of interstitial URLs is still making itself felt in late 2020, which is a record-breaking interval for harmful code overall.
Chrome redirect virus may re-infect your Mac multiple times unless you delete all of its fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.In this scenario, the Chrome redirect process is triggered by malicious software that sneaks into a Mac through a bundle consisting of multiple apps. The redirect process involves the following interim domains being visited momentarily before the browser displays Bing.com:
- Searchmarquis.com
- Searchbaron.com
- Searchitnow.info
- Searchsnow.com
- Mybrowser-search.com
- Nearbyme.io
- R.a9g.io
The essence of this stratagem is to unnoticeably drive traffic to advertising networks, with the legitimate Bing search results simply serving as a distraction maneuver. The rogue Chrome settings imposed by the infection cannot be modified using the standard manual configuration practices. As a result, the victim is stuck with a search engine they never agreed to use as their default one.
Yahoo as the landing page in a Chrome takeover frenzy
The Yahoo redirect campaign is another impactful Chrome hijacking wave that has a significant footprint in the macOS area. Its logic is the same as described previously: bringing a user to real search engine results pages (SERPs) while quietly gliding through a handful of in-between URLs. These auxiliary domains are associated with web application programming interfaces (APIs) that ensure traffic monetization. The problem is that Yahoo overrides the victim’s Chrome preferences although no such permission is expressly granted.
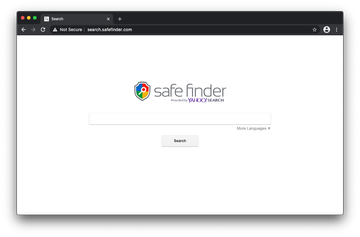
This plot is more complex than it may appear at first sight. It employs a network of search engine copycats that lead to Yahoo Hosted Search (YHS) pages. The most frequently encountered knock-offs are as follows:
- Search.safefinder.com
- Search.chill-tab.com
- Searchmine.net
- Search.searchpulse.net
- Search.anysearch.net
- Search.tapufind.com
- Search.landslidesearch.com
- Searchlee.com
The nifty look and feel of these dubious sites is meant to instill trust in victims and make the browser hijack look like some sort of a glitch that has resulted in tweaking the online preferences. This impression is ruined once the user tries to revert to valid setups – doing so is a no-go because the core malware uses a number of techniques to prevent the easy fix.
Persistence tricks used by Chrome redirect virus Mac
Most Mac users who have fallen victim to the Chrome redirect virus encounter an oddball symptom. When opening the settings pull-down menu in the browser, they’ll notice an inscription saying “Managed by your organization” as illustrated in the screen capture below. Normally, this message signals the presence of an enterprise policy in a corporate computer network. But if it’s a personal rather than a company-issued Mac, the notification is a red flag.
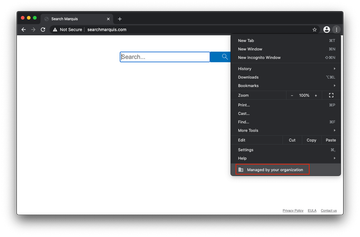
To make their evil code survive regular troubleshooting, the operators of the Chrome redirect Mac virus came up with a mechanism that mishandles the browser policy feature. When the victim takes a deeper dive into the settings, they’ll discover another giveaway. The Management pane includes a phrase that goes, “Your browser is managed”. It means that someone can modify the browser setup remotely.
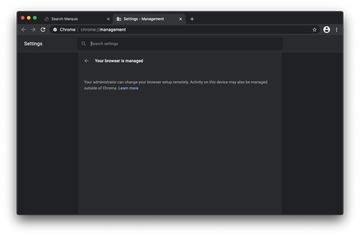
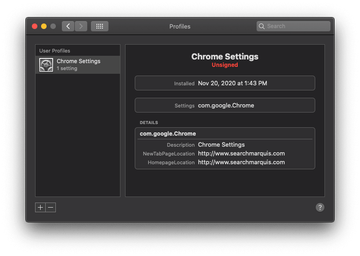
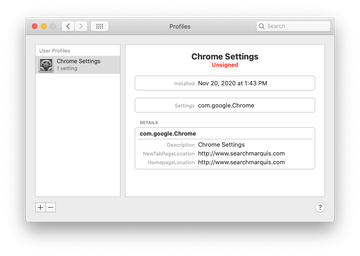
The Chrome enterprise policy hoax revolves around a Mac configuration profile added by the virus once it infiltrates the system. This change occurs at the level of commands executed in the Terminal app behind the user’s back. The device profile imposes limitations on the web surfing routine in the browser and may define the default settings such as the search engine, homepage, and new tab page location.
At the end of the day, the Chrome redirect virus will continue to mess things up until this offensive profile is vanquished. This is the stronghold of the pest’s stubborn activity. The cleanup steps below address this quirk and provide a complete walkthrough to get rid of the infection. The browser remediation section of this tutorial additionally includes instructions for Safari and Mozilla Firefox browsers that are usually affected by the redirect nasty as well.
As far as the prevention goes, the game-changing tip is to exercise caution with freeware installations. This is by far the most common way the browser hijacker sneaks into Macs. At the very least, opt out of the ‘recommended’ mode in such installers and examine what else is being promoted alongside the harmless-looking main app.
Chrome redirect virus manual removal for Mac
The steps listed below will walk you through the removal of this malicious application. Be sure to follow the instructions in the specified order.
Expand the Go menu in your Mac’s Finder bar and select Utilities as shown below.

Locate the Activity Monitor icon on the Utilities screen and double-click on it.

In the Activity Monitor app, look for a process that appears suspicious. To narrow down your search, focus on unfamiliar resource-intensive entries on the list. Keep in mind that its name isn’t necessarily related to the way the threat is manifesting itself, so you’ll need to trust your own judgement. If you pinpoint the culprit, select it and click on the Stop icon in the upper left-hand corner of the screen.

When a follow-up dialog pops up asking if you are sure you want to quit the troublemaking process, select the Force Quit option.

Click on the Go menu icon in the Finder again and select Go to Folder. You can as well use the Command-Shift-G keyboard shortcut.

Type /Library/LaunchAgents in the folder search dialog and click on the Go button.

Examine the contents of the LaunchAgents folder for dubious-looking items. Be advised that the names of files spawned by malware may give no clear clues that they are malicious, so you should look for recently added entities that appear to deviate from the norm.
As an illustration, here are several examples of LaunchAgents related to mainstream Mac infections: com.pcv.hlpramc.plist, com.updater.mcy.plist, com.avickUpd.plist, and com.msp.agent.plist. If you spot files that don’t belong on the list, go ahead and drag them to the Trash.

Use the Go to Folder lookup feature again to navigate to the folder named ~/Library/Application Support (note the tilde symbol prepended to the path).

When the Application Support directory is opened, identify recently generated suspicious folders in it and send them to the Trash. A quick tip is to look for items whose names have nothing to do with Apple products or apps you knowingly installed. A few examples of known-malicious folder names are Quick Mac Booster, IdeaShared, and ProgressMatch.

Enter ~/Library/LaunchAgents string (don’t forget to include the tilde character) in the Go to Folder search area.

The system will display LaunchAgents residing in the current user’s Home directory. Look for dodgy items related to the Chrome redirect virus (see logic highlighted in subsections above) and drag the suspects to the Trash.

Type /Library/LaunchDaemons in the Go to Folder search field.

In the LaunchDaemons path, try to pinpoint the files the malware is using for persistence. Several examples of such items cropped by Mac infections are com.pplauncher.plist, com.startup.plist, and com.ExpertModuleSearchDaemon.plist. Delete the sketchy files immediately.

Click on the Go menu icon in your Mac’s Finder and select Applications on the list.

Find the entry for an app that clearly doesn’t belong there and move it to the Trash. If this action requires your admin password for confirmation, go ahead and enter it.

Expand the Apple menu and select System Preferences.


Proceed to Users & Groups and click on the Login Items tab.


Now select Profiles under System Preferences. Look for a malicious item in the left-hand sidebar. Several examples of configuration profiles created by Mac adware include Chrome Settings, TechSignalSearch, MainSearchPlatform, and AdminPrefs. Select the offending entity and click on the minus sign at the bottom to eliminate it.

Get rid of redirect virus in Chrome and other browsers on Mac
To begin with, the web browser settings taken over by the Chrome redirect virus should be restored to their default values. Although this will clear most of your customizations, web surfing history, and all temporary data stored by websites, the malicious interference should be terminated likewise. The overview of the steps for completing this procedure is as follows:
- Remove redirect virus from Google Chrome
- Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down

- When on the Settings pane, select Advanced
- Scroll down to the Reset settings section.

- Confirm the Chrome reset on a dialog that will pop up. When the procedure is completed, relaunch the browser and check it for malware activity.

- Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down
- Remove redirect virus in Safari
- Open the browser and go to Safari menu. Select Preferences in the drop-down list

- Once the Preferences screen appears, click on the Advanced tab and enable the option saying “Show Develop menu in menu bar”.

- Now that the Develop entry has been added to the Safari menu, expand it and click on Empty Caches.

- Now select History in the Safari menu and click on Clear History in the drop-down list.

- Safari will display a dialog asking you to specify the period of time this action will apply to. Select all history to ensure a maximum effect. Click on the Clear History button to confirm and exit.

- Go back to the Safari Preferences and hit the Privacy tab at the top. Find the option that says Manage Website Data and click on it.

- The browser will display a follow-up screen listing the websites that have stored data about your Internet activities. This dialog additionally includes a brief description of what the removal does: you may be logged out of some services and encounter other changes of website behavior after the procedure. If you’re okay with that, go ahead and click on the Remove All button.

- Restart Safari
- Open the browser and go to Safari menu. Select Preferences in the drop-down list
- Remove redirect virus from Mozilla Firefox
- Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).


- When on the Troubleshooting Information screen, click on the Refresh Firefox button.

- Confirm the intended changes and restart Firefox.
- Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).
Get rid of Chrome redirect Mac virus using Combo Cleaner removal tool
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove Chrome redirect Mac virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the Chrome redirect Mac issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove Chrome redirect Mac threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.
FAQ
How do I get rid of browser redirect virus on Mac?
There is quite a bit of system-wide virus activity behind the facade of a browser hijack. Although the redirects of web traffic to unwanted sites is the most conspicuous symptom, the fix is a bigger challenge than simply reverting to correct settings in Chrome, Safari, or Firefox. You’ll have to dig through multiple folders and system features in search of bad files and processes that should be deleted.
The full procedure is covered in the article above, so let’s go over browser redirect virus removal 101 here. Start with an examination of executables in the Activity Monitor to spot the one, or ones, that’s used by malware. Terminate it once found. Next, go check the following directories for unwanted items: /Library/LaunchAgents (with and without the tilde sign before the path), /Library/LaunchDaemons, and ~/Library/Application Support. Whatever suspicious is in there should go to the Trash.
Then, remove the potentially unwanted app from the Applications folder. Sort your apps by date to identify the recent ones that were installed behind your back. Proceed by opening Users & Groups under System Preferences – click the tab named Login Items and use the “minus” button to delete the startup programs that don’t belong there. If the Profiles feature is displayed on the System Preferences screen, open it and remove the dubious configuration details. You may be asked to enter your admin password to complete the process.
Having uninstalled the malicious program itself, clean up your web browser by deleting the extensions you don’t recognize. If this doesn’t help, you may have to reset the browser to its original settings. If all goes smoothly, these steps should rid you of the redirect virus on your Mac.
Can Google Chrome get a virus on Mac?
Not really. It can get a rogue extension, though. The obscure categorization of a computer virus, which is often used as an all-embracing term that denotes virtually all types of malicious software, spawns ambiguity and misconceptions. Let’s call a spade a spade: there are no viruses targeting Chrome specifically.
That said, intrusive extensions account for the vast majority of security issues with this browser. Ironically, it’s the users who install these applets, misled by shiny wrappings that don’t match the actual stuffing. To top it off, some Mac adware makers are clever enough to bypass the anti-fraud controls of the Chrome Web Store and upload their baddies to the browser’s official extension marketplace. Although this foul play is usually short-lived, it can increase the threat actors’ reach considerably.
Cross-browser adware is another source of problems in this area. It zeroes in on Macs in general rather than specific web browsers. However, since Chrome is one of a kind in terms of popularity, it never stays unaffected in the aftermath of such attacks.
How do I remove the Google Redirect Virus from Chrome?
The Google Redirect Virus is one of the top species of browser-centric Mac threats. It manifests itself in the following way: whenever a victim looks up information via the address bar (which is also the search bar in modern browsers), they are forwarded to a junk service instead of Google, given that this is their default search engine specified in the settings.
By the way, this is a fairly generic trick pulled by Mac browser hijackers, and it’s not necessarily restricted to Google. If you prefer using Yahoo, Bing, DuckDuckGo, or another service, the redirect logic is the same. However, with so many people opting for the world’s dominant search provider, the Google Redirect Virus is a common way to dub sketchy code of that sort.
To remove this nuisance entity from Chrome on your Mac, check your extensions list first. If you notice any items you don’t remember installing, vanquish it without a second thought. In the event that it’s too hard to identify the culprit, try disabling extensions one by one and do some test web searches each time.
If your trial and error tactic reveals that the predicament is unrelated to Chrome extensions, you’ll need to spot and remove Mac malware that may be holding sway over the browser through the configuration profiles feature. Please refer to the article above for details.
