The authors of notorious Mac adware found a workaround to fool Apple’s app notarization mechanism into allowing their code to run on Macs.
The strain known as Shlayer can easily slip below the radar by making the system think it’s safe, while it’s not. In early 2020, Apple brought extra protection to the Mac by extensively checking third-party applications for dodgy characteristics such as code-signing inconsistencies. This approach (called notarization) is aimed at preventing malicious software from being executed on machines with macOS Catalina and later on board. Anything downloaded from outside of the official App Store is now subject to preliminary inspection, which kicks in once a vendor submits their software to Apple.
If all the checks are passed, the Mac’s built-in Gatekeeper module will welcome the application without further ado. Otherwise, the system will block the potentially unsafe product and trigger an alert stating that the app will damage the computer and should be moved to the Trash. It turns out, though, that this technique isn’t as effective as it appears.
Adware notarized by Apple
According to security researcher Patrick Wardle, Shlayer adware makers somehow succeeded in manipulating Apple’s automatic notarization controls. These unwanted payloads can be executed on macOS 10.15 Catalina and the latest beta versions of macOS 11 Big Sur. The white hat elaborated on an observation made by a Twitter user Peter Dantini last week, who spotted a fake Adobe Flash Player update campaign being deployed on a Homebrew app download portal copycat. On a side note, the legitimate site’s URL is brew.sh, while the knockoff variant was hosted at homebrew.sh – a difference that the average user may overlook.
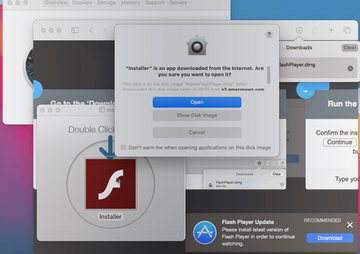
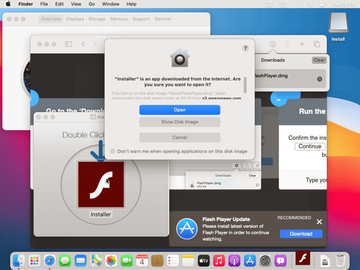
Instead of serving a real Flash Player sample, the faux installer promotes the Bundlore infection wrapping Shlayer spinoff whitelisted by Apple. The installation process involves a disk image (*.dmg) file that shows a custom screen with point-by-point instructions to complete the setup. The Gatekeeper feature stays quiet throughout this workflow, allowing the threat to run just like normal software.
Wardle reported these findings to Apple on August 28, and the company promptly revoked the wrongfully granted certificates. Nevertheless, new notarized iterations of Shlayer were spotted in the wild the same day. This suggests that the criminals followed a well-trodden path and pulled off the same trick successfully. The loophole must still be there, and the fact that Apple pulled the plug on a specific adware build is just a temporary relief.
Shlayer campaign in a nutshell
What kind of a threat is Shlayer? It made its debut in February 2018, and according to antivirus vendors’ telemetry systems, its victim count reportedly reached a whopping one-tenth of all Mac machines in two years’ time. It arrives with booby-trapped versions of the Adobe Flash Player, and once inside, surreptitiously installs a proxy tool to analyze and alter the victim’s web traffic, including encrypted communications. The attack entails ad injection into visited sites, the harvesting of web surfing history, and malicious browser redirects.