A security enthusiast has published details on a Safari vulnerability Apple was planning to fix only a year after acknowledging the reported bug.
The vulnerability was originally discovered by Pawel Wylecial who works for Poland-based cybersecurity services firm REDTEAM.PL. Technically, it is a bug in Web Share API, an interface allowing users to share browser content, such as text, links, and files, via third-party apps. According to the researcher’s findings, a serious pitfall is that the implementation of this mechanism in Safari supports exchanging files that are stored locally on a computer. The source for the problem is that the macOS and iOS versions of Apple’s proprietary browser allow for the so-called “file://” scheme, which can be abused to specify and fetch an arbitrary file residing on the hard disk.
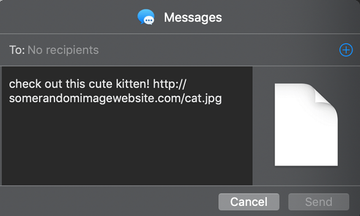
A real-world scenario of exploiting this security loophole involves a specially crafted malicious URL that an attacker sends to a target user. The link leads to a web page hosting an eye-catching image (a cute kitten in the researcher’s proof of concept) and recommending the visitor to share it with friends by clicking an embedded button. Next, the user is instructed to select the way of sharing this content – the Mail, Messages, and Gmail apps are a few common options. If the bug kicks in, a specified local file is sent out alongside the intended link.
The object that’s being sneakily exfiltrated from the macOS or iOS device is attached to the message. In the case of the Messages app, the filename isn’t displayed at all (as illustrated on the ethical hacker’s screenshot above). In the Mail app, the attachment can only be noticed if the victim scrolls down to the very bottom of the message. The Gmail app shows the embedded file but obfuscates its real name. In a PoC attack, Pawel Wylecial was able to obtain a hypothetical user’s browsing history log (History.db) in Safari.
Apple turns a blind eye to the bug
The white hat spotted this vulnerability and reported it to Apple in mid-April 2020. During the next four months, the company’s engineers were replying that the issue was being investigated every time the researcher requested a status update. On August 14, Apple asked Wylecial not to spread the word about the flaw as they were supposedly planning to patch it in the spring of 2021.
Since the conventional industry standard for non-disclosure of security vulnerabilities is 90 days and it was well overdue already, the researcher thought that a year’s time was too much for the tech giant to fix the bug he had found. As a result, he decided to publish his findings on August 24 rather than sit around waiting.
By the way, Apple’s track record of addressing vulnerabilities leaves a lot to be desired. Although the Cupertino company officially made its bug bounty program accessible for all researchers (not only select ones) in December 2019, some white hat hackers are frustrated about the way it works.
Perhaps the most-reported concern is that the program’s rules boil down to keeping researchers quiet about their discoveries for as long as possible. Furthermore, Apple engineers appear to take their time when it comes to prepping and rolling out some security patches, as is the case with the Safari Web Share API flaw in question.
