GSearch Extension 1.0 is a malicious Mac app that turns a victim’s web browsing upside down without permission and stymies conventional removal.
The timeline of Mac adware threats passed a game-changing milestone in last year’s fall. That was a period that gave rise to a whole new family of potentially unwanted applications (PUAs) that have since come to dominate this landscape in terms of both quantity and quality. GSearch Extension is the latest knockoff of this ever-growing strain. Also manifested as GSearch Extension 1.0, it takes over an infected Mac user’s default browser to inject superfluous ads and skew the search preferences beyond regular approval. The pest also stays abreast of the victim’s personal web navigation patterns in order to profile them in an unethical advertising context. The bonding of outright adverse effects and covert privacy encroachment activity has become a hallmark sign of this lineage. What are the other red flags to watch out for? There are a few.
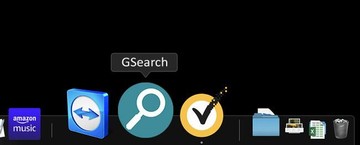
The GSearch Mac virus uses a uniform app extension shared by its near-clone “cousins”, including LinkBranch and UtilityParse. It depicts a magnifying glass symbol slightly tilted towards the right or left side. This graphical quirk is visible in the Dock, in the Applications screen, and the extensions interface of the affected web browser. Another symptom is that the version number may be displayed in some locations across the plagued system, so the sketchy program usually shows up as GSearch 1.0 or GSearch Extension 1.0. The adware exhibits cross-browser properties, littering around Safari, Google Chrome, and Mozilla Firefox in a pretty much identical way. The malicious add-on reconfigures the Internet preferences to default to a fake search service such as Safe Finder. The rogue destination page, in turn, reroutes the traffic to Yahoo via intermediate URLs that appear in the browser’s status bar for a split second.
GSearch Extension may re-infect your Mac multiple times unless you delete all of its fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.Reorganizing the victim’s custom web surfing settings is a major vector of GSearch virus activity, and yet it’s not the only one to worry about. The nasty additionally floods the visited web pages with annoying ads that come in the form of popups, static banners with coupons and freebies, as well as in-text links sprinkled all over the content. Not only is his influx of sponsored materials hugely irritating, but it’s also a memory hog that causes the browser to slow down to a crawl and even crash now and again. An extra concern about it is that the adverts accurately fit the range of the victim’s interests. This means that GSearch Extension displays them based on its prior shady reconnaissance. It captures fingerprintable details such as the user’s Internet history, web searches, accounts being signed into, and most unnervingly, login credentials. The danger stemming from this facet of the PUA’s activity shouldn’t be underestimated.
GSearch 1.0 virus is a bundle-borne threat. No one downloads it as an online search enhancement tool. Instead, Mac users get hit when downloading and installing an unrelated piece of software such as a free media converter, a pirated copy of a popular application, or a dubious Flash Player update pushing unwanted extras under its umbrella. The installation client is tailor-made specifically to hide the bad component in plain sight, with its express (recommended) option promoting a package of entities under the guise of a single program. This explains why the emergence of GSearch Extension inside a computer running macOS is always an unexpected encounter.
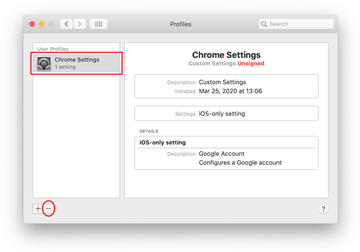
The fix is typically hampered by this threat’s persistence that mostly revolves around a configuration profile it adds during the attack. This trick enforces a browser preferences overhaul that resists the user’s attempts to specify the normal settings. Therefore, the footwork to take care of this issue should involve the removal of the evil profile in addition to malware cleanup best practices. The steps below cover these techniques in-depth and provide tips to rid the browser of the unwanted tampering.
GSearch Extension virus manual removal for Mac
The steps listed below will walk you through the removal of this malicious application. Be sure to follow the instructions in the specified order.
Expand the Go menu in your Mac’s Finder bar and select Utilities as shown below.

Locate the Activity Monitor icon on the Utilities screen and double-click on it.

In the Activity Monitor app, look for GSearch, GSearch Extension or another process that appears suspicious. To narrow down your search, focus on unfamiliar resource-intensive entries on the list. Keep in mind that its name isn’t necessarily related to the way the threat is manifesting itself, so you’ll need to trust your own judgement. If you pinpoint the culprit, select it and click on the Stop icon in the upper left-hand corner of the screen.

When a follow-up dialog pops up asking if you are sure you want to quit the troublemaking process, select the Force Quit option.

Click on the Go menu icon in the Finder again and select Go to Folder. You can as well use the Command-Shift-G keyboard shortcut.

Type /Library/LaunchAgents in the folder search dialog and click on the Go button.

Examine the contents of the LaunchAgents folder for dubious-looking items. Be advised that the names of files spawned by malware may give no clear clues that they are malicious, so you should look for recently added entities that appear to deviate from the norm.
As an illustration, here are several examples of LaunchAgents related to mainstream Mac infections: com.pcv.hlpramc.plist, com.updater.mcy.plist, com.avickUpd.plist, and com.msp.agent.plist. If you spot files that don’t belong on the list, go ahead and drag them to the Trash.

Use the Go to Folder lookup feature again to navigate to the folder named ~/Library/Application Support (note the tilde symbol prepended to the path).

When the Application Support directory is opened, identify recently generated suspicious folders in it and send them to the Trash. A quick tip is to look for items whose names have nothing to do with Apple products or apps you knowingly installed. A few examples of known-malicious folder names are GSearch, ProgressMatch, SystemSpecial, and IdeaShared.

Enter ~/Library/LaunchAgents string (don’t forget to include the tilde character) in the Go to Folder search area.

The system will display LaunchAgents residing in the current user’s Home directory. Look for dodgy items related to GSearch Extension virus (see logic highlighted in subsections above) and drag the suspects to the Trash.

Type /Library/LaunchDaemons in the Go to Folder search field.

In the LaunchDaemons path, try to pinpoint the files the malware is using for persistence. Several examples of such items cropped by Mac infections are com.pplauncher.plist, com.startup.plist, and com.ExpertModuleSearchDaemon.plist. Delete the sketchy files immediately.

Click on the Go menu icon in your Mac’s Finder and select Applications on the list.

Find the entry for GSearch Extension 1.0 or another app that clearly doesn’t belong there and move it to the Trash. If this action requires your admin password for confirmation, go ahead and enter it.

Expand the Apple menu and select System Preferences.


Proceed to Users & Groups and click on the Login Items tab.


Now select Profiles under System Preferences. Look for a malicious item in the left-hand sidebar. Several examples of configuration profiles created by Mac adware include TechSignalSearch, MainSearchPlatform, AdminPrefs, and Chrome Settings. Select the offending entity and click on the minus sign at the bottom to eliminate it.

Get rid of GSearch Extension ads and redirect activity in web browser on Mac
To begin with, the web browser settings taken over by GSearch should be restored to their default values. Although this will clear most of your customizations, web surfing history, and all temporary data stored by websites, the malicious interference should be terminated likewise. The overview of the steps for completing this procedure is as follows:
- Remove GSearch Extension 1.0 virus in Safari
- Open the browser and go to Safari menu. Select Preferences in the drop-down list

- Once the Preferences screen appears, click on the Advanced tab and enable the option saying “Show Develop menu in menu bar”.

- Now that the Develop entry has been added to the Safari menu, expand it and click on Empty Caches.

- Now select History in the Safari menu and click on Clear History in the drop-down list.

- Safari will display a dialog asking you to specify the period of time this action will apply to. Select all history to ensure a maximum effect. Click on the Clear History button to confirm and exit.

- Go back to the Safari Preferences and hit the Privacy tab at the top. Find the option that says Manage Website Data and click on it.

- The browser will display a follow-up screen listing the websites that have stored data about your Internet activities. This dialog additionally includes a brief description of what the removal does: you may be logged out of some services and encounter other changes of website behavior after the procedure. If you’re okay with that, go ahead and click on the Remove All button.

- Restart Safari
- Open the browser and go to Safari menu. Select Preferences in the drop-down list
- Get rid of GSearch Extension 1.0 virus in Google Chrome
- Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down

- When on the Settings pane, select Advanced
- Scroll down to the Reset settings section.

- Confirm the Chrome reset on a dialog that will pop up. When the procedure is completed, relaunch the browser and check it for malware activity.

- Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down
- Remove GSearch Extension 1.0 from Mozilla Firefox
- Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).


- When on the Troubleshooting Information screen, click on the Refresh Firefox button.

- Confirm the intended changes and restart Firefox.
- Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).
Get rid of GSearch virus using Combo Cleaner removal tool
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove GSearch Extension virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the GSearch Extension issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove GSearch Extension threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.