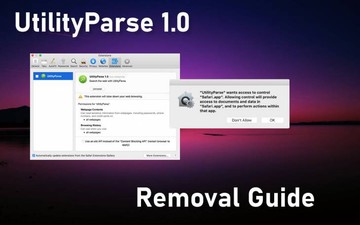
Misconceptions about Macs run the gamut from bulletproof native defenses to rejecting the existence of viable malware that targets these machines altogether. However, the very moment the application called UtilityParze crops up on a Mac, even the most skeptical user will rethink their beliefs. Also known as UtilityParse, this piece of software fits the mold of adware that skews one’s web browsing preferences in a snap. The goal is twofold: to display numerous irksome ads on sites and to redirect the Internet traffic to malicious or just plain out worthless pages, mostly search engine copycats with sponsored content here and there. Having completed the installation behind a victim’s back, this culprit manifests itself by trying to pull off a permissions escalation trick. This quirk involves a popup request that says, “UtilityParze will damage your computer” or “UtilityParse wants access to control Safari.app”. The dialog goes on to say that “allowing control will provide access to documents and data in Safari.app, and to perform actions within that app”. A part in this message varies depending on which web browser is the user’s default one, so it can be Google Chrome.app or Mozilla Firefox.app instead.
This symptom sheds light on the true objective of UtilityParse / UtilityParze virus. It seeks to take over the victim’s preferred web browser and thereby to execute a broad-sweeping dubious advertising and traffic redistribution attack. The privilege requests will be incessantly shown until the victim either opts in or vanquishes the potentially unwanted app (PUA). Whereas the latter is the only reasonable route to take, Mac users may choose to go with the flow and allow the shady program to do its thing. This will unleash the incursion into its full swing. Safari, Chrome, or Firefox will suddenly become deluged with obnoxious advertisements showing up where they don’t belong. These items range from popup ads and in-text links to price comparison charts and interstitial pages being opened in the background one after another. Not only is this a nuisance, but it’s also a serious memory hog making the browser slow down or crash at times. Furthermore, it doesn’t get along with user-friendly web surfing because useful materials on sites are eclipsed by third-party entities the webmasters never allowed to be there.
UtilityParze may re-infect your Mac multiple times unless you delete all of its fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.A whole additional vector of UtilityParze adware’s foul play is to replace the victim’s default browser settings with something absolutely different. The list of targeted preferences includes the search engine, homepage, and new tab page. The sketchy browser extension installed by this offending app will typically enforce the use of a fake search-related service instead of the original URLs the user has previously specified. This e-hoax results in incessant forwarding of the web traffic to a series of sites recurrently triggering extra redirects until the bewildered user arrives at a pseudo-legitimate info lookup resource. In some scenarios, the landing page resolved at the end of the day is Bing or Yahoo Search results laced with ads above the fold.
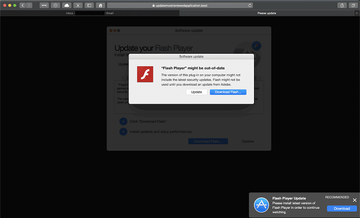
To make the rounds, UtilityParze app rides Mac adware authors’ favorite hype train. It’s all about bogus Flash Player updates pushed through untrustworthy sites that have nothing to do with Adobe. Users run into this stratagem out of the blue when visiting regular websites or in case their systems have already been infiltrated by a browser hijacker. In other words, the deceptive update recommendations may pop up because a furtively embedded script in a popular site triggers them. They can as well stem from a browser redirect plot backed by another piece of malware. One way or another, the resulting page says the Adobe Flash Player version currently running on the Mac might be obsolete, and an update should address this issue and streamline the online multimedia viewing options. Although these installers may look real, they cloak one or several bundled applications underneath their default mode. A great habit to stay away from cybercriminals’ hooks like that is to always deselect the express setup option and ascertain that there are no supplementary programs hiding under the same umbrella.
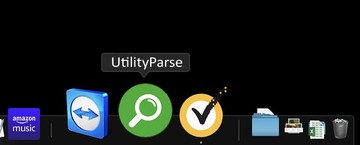
Few Mac users are as proactive as that, though. This explains why UtilityParze (UtilityParse) infections are on the rise. If it is wreaking havoc with web browsers, there is a good deal of cleaning to do. Be advised that simply sending it to the Trash from the Applications screen and then removing it from Dock won’t help. Familiarize yourself with the steps below to completely eliminate this pest and undo the abominable changes it has caused.
UtilityParze virus manual removal for Mac
The steps listed below will walk you through the removal of this malicious application. Be sure to follow the instructions in the specified order.
Expand the Go menu in your Mac’s Finder bar and select Utilities as shown below.

Locate the Activity Monitor icon on the Utilities screen and double-click on it.

In the Activity Monitor app, look for a process that appears suspicious. To narrow down your search, focus on unfamiliar resource-intensive entries on the list. Keep in mind that its name isn’t necessarily related to the way the threat is manifesting itself, so you’ll need to trust your own judgement. If you pinpoint the culprit, select it and click on the Stop icon in the upper left-hand corner of the screen.

When a follow-up dialog pops up asking if you are sure you want to quit the troublemaking process, select the Force Quit option.

Click on the Go menu icon in the Finder again and select Go to Folder. You can as well use the Command-Shift-G keyboard shortcut.

Type /Library/LaunchAgents in the folder search dialog and click on the Go button.

Examine the contents of the LaunchAgents folder for dubious-looking items. Be advised that the names of files spawned by malware may give no clear clues that they are malicious, so you should look for recently added entities that appear to deviate from the norm.
As an illustration, here are several examples of LaunchAgents related to mainstream Mac infections: com.pcv.hlpramc.plist, com.updater.mcy.plist, com.avickUpd.plist, and com.msp.agent.plist. If you spot files that don’t belong on the list, go ahead and drag them to the Trash.

Use the Go to Folder lookup feature again to navigate to the folder named ~/Library/Application Support (note the tilde symbol prepended to the path).

When the Application Support directory is opened, identify recently generated suspicious folders in it and send them to the Trash. A quick tip is to look for items whose names have nothing to do with Apple products or apps you knowingly installed. A few examples of known-malicious folder names are ProgressMatch, SystemSpecial, and IdeaShared.

Enter ~/Library/LaunchAgents string (don’t forget to include the tilde character) in the Go to Folder search area.

The system will display LaunchAgents residing in the current user’s Home directory. Look for dodgy items related to UtilityParze virus (see logic highlighted in subsections above) and drag the suspects to the Trash.

Type /Library/LaunchDaemons in the Go to Folder search field.

In the LaunchDaemons path, try to pinpoint the files the malware is using for persistence. Several examples of such items cropped by Mac infections are com.pplauncher.plist, com.startup.plist, and com.ExpertModuleSearchDaemon.plist. Delete the sketchy files immediately.

Click on the Go menu icon in your Mac’s Finder and select Applications on the list.

Find the entry for UtilityParze (UtilityParse) or another app that clearly doesn’t belong there and move it to the Trash. If this action requires your admin password for confirmation, go ahead and enter it.

Expand the Apple menu and select System Preferences.


Proceed to Users & Groups and click on the Login Items tab.


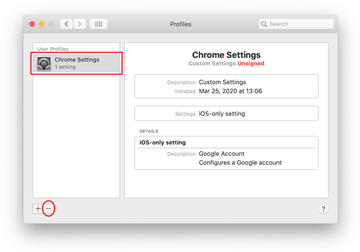
Now select Profiles under System Preferences. Look for a malicious item in the left-hand sidebar. Several examples of configuration profiles created by Mac adware include TechSignalSearch, MainSearchPlatform, AdminPrefs, and Chrome Settings. Select the offending entity and click on the minus sign at the bottom to eliminate it.

Get rid of UtilityParze virus in web browser on Mac
To begin with, the web browser settings taken over by the UtilityParze virus should be restored to their default values. Although this will clear most of your customizations, web surfing history, and all temporary data stored by websites, the malicious interference should be terminated likewise. The overview of the steps for completing this procedure is as follows:
- Remove UtilityParze virus from Safari
Open the browser and go to Safari menu. Select Preferences in the drop-down list.

Once the Preferences screen appears, click on the Advanced tab and enable the option saying “Show Develop menu in menu bar”.

Now that the Develop entry has been added to the Safari menu, expand it and click on Empty Caches.

Now select History in the Safari menu and click on Clear History in the drop-down list.

Safari will display a dialog asking you to specify the period of time this action will apply to. Select all history to ensure a maximum effect. Click on the Clear History button to confirm and exit.

Go back to the Safari Preferences and hit the Privacy tab at the top. Find the option that says Manage Website Data and click on it.

The browser will display a follow-up screen listing the websites that have stored data about your Internet activities. This dialog additionally includes a brief description of what the removal does: you may be logged out of some services and encounter other changes of website behavior after the procedure. If you’re okay with that, go ahead and click on the Remove All button.

Restart Safari
- Remove UtilityParze in Google Chrome
Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down

When on the Settings pane, select Advanced
Scroll down to the Reset settings section.

Confirm the Chrome reset on a dialog that will pop up. When the procedure is completed, relaunch the browser and check it for malware activity.

- Remove UtilityParze from Mozilla Firefox
Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).


When on the Troubleshooting Information screen, click on the Refresh Firefox button.

Confirm the intended changes and restart Firefox.
Get rid of UtilityParze ads and redirect activity in web browser on Mac
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove UtilityParze virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the UtilityParze issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove UtilityParze threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.