Review this guide to learn what the Trovi adware is, how it compromises computers, and how to completely remove it from an infected Mac machine.
Update:
| Threat Profile | |
|---|---|
| Name | Trovi redirect virus |
| Category | Mac browser hijacker, adware, PUA |
| IP Address | 3.130.94.1 |
| Related Domains | trovi.com, trovigo.com, weknow.ac |
| Symptoms | Redirects web searches to Bing via trovi.com, trovigo.com or weknow.ac, displays unwanted ads, slows down the system |
| Distribution Techniques | Freeware bundles, torrents, pirated apps, fake software updates |
| Severity Level | Low |
| Damage | Search redirects, browser history tracking, unwanted ads |
| Removal | Scan your Mac with Combo Cleaner to detect all files related to the browser hijacker. Use the tool to remove the infection if found. |
Malware-free macOS is unfortunately turning into a delusion at a steady pace. The good news is it’s not as susceptible to viruses as Windows, but potentially unsafe applications such as adware have been capable of compromising Mac machines for quite a while now. The infection which is the subject of this article is called Trovi, and it’s an extreme nuisance and a big time web surfing experience spoiler. This potentially unwanted code is commonly flagged by antivirus utilities as adware, that is, a program taking advantage of hijacked Internet traffic in order to monetize it and promote certain services. It has been in circulation since 2014 and hasn’t undergone any filtering or blacklisting countermeasures up till the present moment. Seven years after discovery, the malware continues to make new victims who are at their wit’s end trying to get rid of the irritating redirects and bring serenity back into their digital lives.
Mac users are ensnared via classic trickery
The Trovi threat is known to be closely affiliated with Conduit, or Conduit Search – one of the prevalent homepage hijackers in the wild. So if you’ve got one on your machine, the other is probably there as well. Just like its Conduit satellite, Trovi is distributed as part of freeware whose spreading pattern in no way presupposes declaring that any sort of bundle is coming along. Scrutinizing the Terms of Service for random free multimedia utilities or browser helper objects might help avoid the contamination but, first off, not necessarily, and secondly, there aren’t a whole lot of users doing that as a rule.
Trojanized Adobe Flash Player updaters dominate the Trovi virus distribution campaign. This hoax is backed by popups that appear on hacked or malicious websites stating that the update is mandatory for proper processing of multimedia content in the browser. Predictably enough, the spoofed installer is a bundle comprising Trovi payload in addition to the harmless core application that supposedly needs fine-tuning. Now that Adobe is dropping support of its long-standing product (the EOL move is due December 31, 2020), cybercrooks are switching to the use of spoofed “Adobe Flash Player Uninstaller” pop-ups to promote the likes of Trovi.
How exactly does Trovi affect a Mac?
This adware changes the web browsing preferences on the infected workstation, namely the values for the homepage and default search engine. The Mac versions of Chrome, Firefox, as well as Safari therefore start to act up, constantly returning www.trovi.com or trovigo.com instead of the URLs for the above settings previously configured by the user. There is no actual danger stemming from the landing web page for this adware except for the annoyance aspect. Trovi.com bears a tangible value to its creators, though, because it displays ads to the victims. Whether you click on those banners and sponsored links or not, it’s profitable to Trovi authors. Also, while having no real search functionality in itself, this service redirects all searches to Bing.
Trovi may re-infect your Mac multiple times unless you delete all of its fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.When the hijack is underway, Trovi.com can be resolved in the affected browser briefly and isn’t necessarily the actual landing page the victim arrives at. Moreover, it is often one of several “en route” domains the traffic slips through. In many cases, the fraudulently imposed web navigation path additionally encompasses such URLs as go.next-search.net and weknow.ac. Regardless of the specific series of sites being observed in transit, the Mac user will be hitting Bing.com in the long run. The role of this reputable search provider is to spice the adware attack with a false sense of legitimacy.

Browser hijacking isn’t the only pitfall
On top of the conspicuous browser redirect activity, the Trovi malware deploys a sort of reconnaissance on the plagued Mac. In particular, it drops tracking cookies and gathers the victim’s sensitive data, such as the browsing history, email address, and details of account logon instances. The architects of this campaign then take advantage of the harvested information themselves or sell it to third parties that may conduct targeted phishing attacks and generate spam. The longer the infection remains on board a computer and active, the higher the likelihood of identity theft.
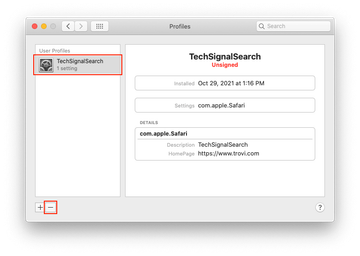
It’s worth pointing out separately that although you only see the impact of Trovi in the way your web browsers behave, it spreads its cyber tentacles much further than that and drops malicious components into multiple paths in the host Mac. For example, it adds a configuration profile via the command line as part of the attack. The goal of this multi-level compromise tactic is to establish persistence and prevent easy cleanup. That’s why the removal of this adware should be performed in several stages that include resetting the affected web browsers and eliminating the malicious app proper. Below are detailed instructions on what needs to be done.
Trovi manual removal for Mac
The steps listed below will walk you through the removal of this malicious application. Be sure to follow the instructions in the specified order.
Expand the Go menu in your Mac’s Finder bar and select Utilities as shown below.

Locate the Activity Monitor icon on the Utilities screen and double-click on it.

In the Activity Monitor app, look for a process that appears suspicious. To narrow down your search, focus on unfamiliar resource-intensive entries on the list. Keep in mind that its name isn’t necessarily related to the way the threat is manifesting itself, so you’ll need to trust your own judgement. If you pinpoint the culprit, select it and click on the Stop icon in the upper left-hand corner of the screen.

When a follow-up dialog pops up asking if you are sure you want to quit the troublemaking process, select the Force Quit option.

Click on the Go menu icon in the Finder again and select Go to Folder. You can as well use the Command-Shift-G keyboard shortcut.

Type /Library/LaunchAgents in the folder search dialog and click on the Go button.

Examine the contents of the LaunchAgents folder for dubious-looking items. Be advised that the names of files spawned by malware may give no clear clues that they are malicious, so you should look for recently added entities that appear to deviate from the norm.
As an illustration, here are several examples of LaunchAgents related to mainstream Mac infections: com.pcv.hlpramc.plist, com.updater.mcy.plist, com.avickUpd.plist, and com.msp.agent.plist. If you spot files that don’t belong on the list, go ahead and drag them to the Trash.

Use the Go to Folder lookup feature again to navigate to the folder named ~/Library/Application Support (note the tilde symbol prepended to the path).

When the Application Support directory is opened, identify recently generated suspicious folders in it and send them to the Trash. A quick tip is to look for items whose names have nothing to do with Apple products or apps you knowingly installed. A few examples of known-malicious folder names are Trovi, IdeaShared, and ProgressMatch.

Enter ~/Library/LaunchAgents string (don’t forget to include the tilde character) in the Go to Folder search area.

The system will display LaunchAgents residing in the current user’s Home directory. Look for dodgy items related to Trovi virus (see logic highlighted in subsections above) and drag the suspects to the Trash.

Type /Library/LaunchDaemons in the Go to Folder search field.

In the LaunchDaemons path, try to pinpoint the files the malware is using for persistence. Several examples of such items cropped by Mac infections are com.pplauncher.plist, com.startup.plist, and com.ExpertModuleSearchDaemon.plist. Delete the sketchy files immediately.

Click on the Go menu icon in your Mac’s Finder and select Applications on the list.

Find Trovi or another app that clearly doesn’t belong there and move it to the Trash. If this action requires your admin password for confirmation, go ahead and enter it.

Expand the Apple menu and select System Preferences.


Proceed to Users & Groups and click on the Login Items tab.


Now select Profiles under System Preferences. Look for a malicious item in the left-hand sidebar. Several examples of configuration profiles created by Mac adware include TechSignalSearch, MainSearchPlatform, AdminPrefs, and Chrome Settings. Select the offending entity and click on the minus sign at the bottom to eliminate it.

Get rid of Trovi virus in web browser on Mac
To begin with, the web browser settings taken over by the Trovi virus should be restored to their default values. Although this will clear most of your customizations, web surfing history, and all temporary data stored by websites, the malicious interference should be terminated likewise. The overview of the steps for completing this procedure is as follows:
- Remove Trovi virus from Safari
Open the browser and go to Safari menu. Select Preferences in the drop-down list.

Once the Preferences screen appears, click on the Advanced tab and enable the option saying “Show Develop menu in menu bar”.

Now that the Develop entry has been added to the Safari menu, expand it and click on Empty Caches.

Now select History in the Safari menu and click on Clear History in the drop-down list.

Safari will display a dialog asking you to specify the period of time this action will apply to. Select all history to ensure a maximum effect. Click on the Clear History button to confirm and exit.

Go back to the Safari Preferences and hit the Privacy tab at the top. Find the option that says Manage Website Data and click on it.

The browser will display a follow-up screen listing the websites that have stored data about your Internet activities. This dialog additionally includes a brief description of what the removal does: you may be logged out of some services and encounter other changes of website behavior after the procedure. If you’re okay with that, go ahead and click on the Remove All button.

Restart Safari
- Remove Trovi in Google Chrome
Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down

When on the Settings pane, select Advanced
Scroll down to the Reset settings section.

Confirm the Chrome reset on a dialog that will pop up. When the procedure is completed, relaunch the browser and check it for malware activity.

- Remove Trovi from Mozilla Firefox
Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).


When on the Troubleshooting Information screen, click on the Refresh Firefox button.

Confirm the intended changes and restart Firefox.
Get rid of Trovi virus using Combo Cleaner automatic removal tool
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove Trovi virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the Trovi issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove Trovi threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.
FAQ
Is Trovi com a virus?
Most security experts argue that calling any malicious Mac application a virus would be a misnomer. Apple has invested a lot of effort and resources to build monolithic barriers around its operating systems over the years. Viruses – in the traditional sense – have no chance to get around these defenses at this point. Furthermore, there are no known examples of dangerous code that replicates itself inside macOS, which is a hallmark that sets a computer virus aside from other unwanted programs.
Trovi.com is rather a nuisance entity with characteristics inherent to adware. This web page functions as a midway point in a prolific Internet traffic redistribution scheme backed by a strain that fits the mold of a potentially unwanted application (PUA). The facade of this redirect campaign is Bing, the legitimate search engine visited in the aftermath of Trovi.com activity. All these traits are examples of classic Mac adware artifice. Back to the original question, no, Trovi.com is not a virus. But, it is a fairly complex and persistent threat.
How did Trovi get on my Mac?
As preposterous as it may sound, you most likely let Trovi in yourself. It wasn’t an informed decision, though. Here’s the thing: this adware is distributed through bundles that consist of several different applications. One of them looks harmless and raises no red flags at all.
It often poses as an Adobe Flash Player update pushed through a pop-up on a hacked or malicious website. Although this is now a deprecated product, cybercriminals are still piggybacking on its past fame to cloak bad intentions. The conspicuous element of the package could also be any other freeware from a popular category, such as a video downloader, a torrent client, or a file format converter.
Once you agree to the default installation terms, the quasi-legitimate program pulls Trovi inside with hardly any giveaways. A sure-shot method to avoid this hoax is to select the advanced setup option in the installer, as it reveals the real composition of the bundle and allows you to untick all suspicious extras.
How do I remove unwanted search engine from my Mac?
In a situation not aggravated by adware interference, swapping an unwanted search engine for the right one is easy. You should do it at the level of the specific web browser whose settings you would like to modify. In Safari, this is as simple as heading to its preferences, clicking the “Search” tab, and selecting the desired provider in a drop-down list.
In Google Chrome, the process is similar: go to “Search engine” under preferences and pick another service in a readily available list. Unlike Safari, though, Chrome allows you to add a custom search engine by clicking the “Manage search engines” button. Just follow on-screen instructions to complete the action.
To remove a dubious search provider from Firefox, go to the browser’s settings, select “Search” in the sidebar, and choose the preferred service in the “Default Search Engine” area. Everything is fairly smooth and intuitive no matter what browser’s configurations you want to re-adjust. Again, that’s how to do it on a healthy Mac without malicious code putting a spanner in the works.
If a Mac threat such as Trovi is on board, the procedure is much more complicated. It must be performed at two levels: the entire system and the affected web browser. Adware removal is a multi-pronged workflow that spans deleting a malicious configuration profile, the shady application itself, evil login items, and more. In some cases, you have to terminate the offending executable via the Activity Monitor first.
To rectify browser settings skewed by malicious code, look for an extension that could be associated with the pest. It could be a random-named item you don’t remember adding to Safari, Chrome, or Firefox. If this object won’t disappear after regular uninstall attempts and keeps preventing you from re-specifying your search preferences, you may need to clear the browser’s cache, cookies, history, and other website data.
How do I get rid of a phishing virus on my Mac?
Most Mac threats make the rounds through social engineering rather than software or hardware flaws. Phishing is one of the most common types of such chicanery. In a broad sense, this technique aims to manipulate a user into making a mistake and downloading something they shouldn’t or clicking a link that leads to malware.
If you happen to get on a phisher’s hook and fall victim to a harmful application, there is no alternative to removal. You’ll need to spot and delete all bits and pieces of the culprit from your Mac, including harmful launch agents, launch daemons, and items in the Application Support folder that don’t belong there. If your web browser is acting up, which is a likely upshot of a phishing scam, purge it of malware traces as well. Please refer to the article above for more information.