- Safari virus warning scams are booming across the iPhone ecosystem
- The Mac facet of the Safari virus warning
- Safari virus warning manual removal for iPhone and iPad
- Safari virus warning manual removal for Mac
- Get rid of Safari virus warning in the browser on Mac
- Get rid of Safari virus warning using Combo Cleaner removal tool
Here is a hands-on summary of the Safari virus warning, a multi-pronged pivot of numerous online scams targeting Mac and iPhone users for years.
Threat actors who boil their schemes down to ensnaring users of Apple products couldn’t possibly pass by Safari, the browser pre-installed on millions of hugely popular devices. Until recently, gadgets running iOS and iPadOS hadn’t even allowed for switching to another default browser. The latest Safari version for the Mac is more visually attractive than the predecessors and delivers awesome privacy extras. While these bells and whistles are good news for the average user, they are a call to action from a seasoned attacker’s twisted perspective. Amid all the exploitation opportunities in the present-day crooks’ handbook, the Safari virus warning stands out due to its prevalence and wicked efficiency. It underlies a series of online scams whose goals run the gamut from injecting malware to stealing Apple IDs and other sensitive credentials.
Safari virus warning scams are booming across the iPhone ecosystem
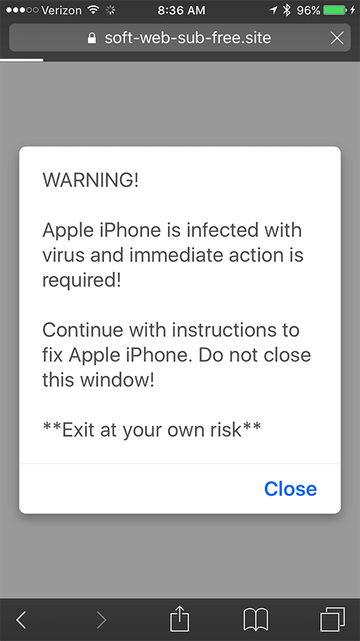
An example of the attack chain on an iPhone is a Safari warning that says the device is infected with a virus and the user needs to take immediate action to take care of the alleged predicament. It is manifested as a pop-up that appears on a dubious website the user visits out of curiosity or in the aftermath of clicking a fishy link. In some scenarios, a script stealthily injected into a legitimate site is to blame for redirecting the browser to a faux alert page. When the victim taps Close, the alert may vanish for a while and then reappear, or Safari will further forward the Internet traffic to a dodgy resource that provides fraudulent cleaning recommendations. The page may promote a security app that’s spyware in disguise. It could as well instruct the user to enter their Apple ID and password in a fake form that mimics the authentic sign-in page.
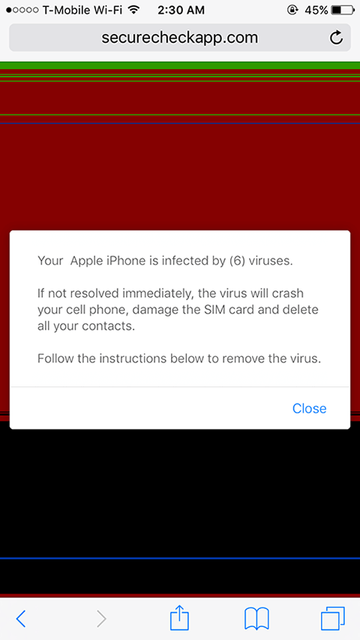
One more widespread type of this hoax in the mobile context is a Safari alert stating that the iPhone is infected with 6 viruses. To pressure the user, the warning goes on to say that the infection may brick the device, damage the SIM, and wipe all contacts unless removed. As is the case with the above-mentioned attack vector, the follow-up steps will try to dupe the victim into slipping up by providing personal information or installing a rogue app that will open a backdoor into the system so that the malefactor can access it at a later point. A particularly adverse situation occurs if the scammer obtains access to the Find My service to remotely lock the device. If this trick pans out, the attacker may mishandle the custom lock screen feature to display a ransom note and extort the user.
A spoofed warning that says, “Your iPhone Has Been Hacked” is yet another common type of the fraudulent Safari alert. It relies on a similar logic, attempting to hoodwink the would-be victim into disclosing account credentials or dialing a phone number to contact a pseudo-technician who will try to wheedle out personally identifiable information.
The Mac facet of the Safari virus warning
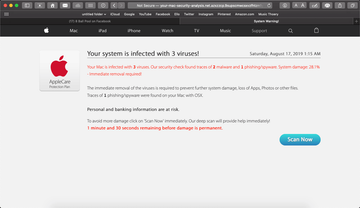
There are plenty of such scams with a Mac flavor, too. In a long-running tech support fraud campaign, malicious actors use landing pages that say, “Your system is infected with 3 viruses”. Unlike the previously mentioned iPhone hoaxes, the purpose of this one is restricted to contaminating a computer with a scareware application. The alert contains a “Scan Now” button that, when clicked, triggers a page mimicking a security audit of the target system and recommending a fake cleaner to address the purported infestation with malware like Tapsnake, CronDNS, or Dubfishicv. The warning page includes a logo of the AppleCare Protection Plan to give victims a false sense of legitimacy. Another prolific Mac scam saying, “Zeus Virus Detected” bears a resemblance to this one, except that it mainly tries to coerce victims into contacting impostor support agents over the phone.
Safari virus warning scam may re-infect your Mac multiple times unless you delete all of its fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.Macs are also being shelled with a variant of the Safari virus warning that promotes a booby-trapped version of the Adobe Flash Player. Although the software in question is obsolete now in 2021 and is no longer supported by the publisher, cybercriminals continue to piggyback on its past fame to spread adware and phony Mac maintenance tools. The counterfeit Flash Player update alerts pop up for one of the following reasons: if a corresponding script is triggered on a malicious or compromised website the user visits; or if a browser hijacker has previously cropped up in the system and is causing incessant redirects to untrustworthy pages that display the sketchy update recommendation.
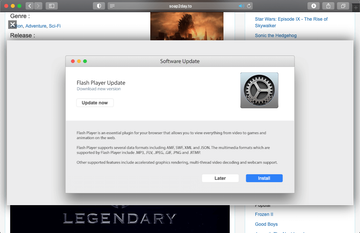
If a Mac user falls for this trivial stratagem, they unknowingly permit a strain of malware to infiltrate the system. The resulting payload will install a pest such as a Safari redirect virus or an app that pretends to detect numerous performance issues and security threats. In the latter case, the user runs the risk of wasting money on a cleaning service they don’t actually need. When it comes to this hoax, a rule of thumb is to distrust software update prompts generated by a web page.
Regardless of the specific spin-off of the Safari virus warning fraud, the right response is two-fold. Ignoring what these browser-borne alerts say is half the battle. In other words, do not follow the steps listed in these dialogs or engage in any form of interaction other than closing them. Secondly, if the pop-ups or browser redirects keep occurring, this is a telltale sign of malware already running in the system. This situation won’t sort itself out unless the harmful code is purged. Depending on the affected device, the steps below should pull the plug on the unwanted browser activity.
Safari virus warning manual removal for iPhone and iPad
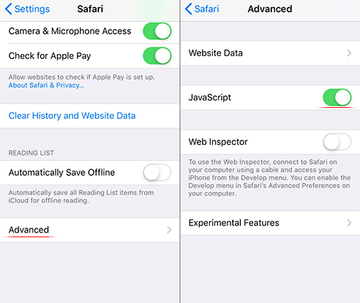
As per the anatomy of this hijack, settings of the web browser hit by the virus should be restored to their default values. The steps for performing this procedure are as follows:
Safari troubleshooting on iPhone / iPad
- Go to Settings and select Safari on the menu
- Tap the Clear History and Website Data option
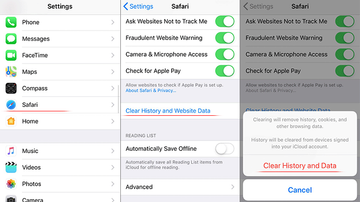
- Confirm by tapping Clear History and Data. Check if the problem with Safari has been fixed. In the event the iPhone / iPad virus popups are still there, proceed to next step.
- When on the Safari Settings screen, tap Advanced. Find the JavaScript entry there and toggle it off. This should solve the problem
Safari virus warning manual removal for Mac
The steps listed below will walk you through the removal of this malicious application. Be sure to follow the instructions in the specified order.
Expand the Go menu in your Mac’s Finder bar and select Utilities as shown below.

Locate the Activity Monitor icon on the Utilities screen and double-click on it.

In the Activity Monitor app, look for a process that appears suspicious. To narrow down your search, focus on unfamiliar resource-intensive entries on the list. Keep in mind that its name isn’t necessarily related to the way the threat is manifesting itself, so you’ll need to trust your own judgement. If you pinpoint the culprit, select it and click on the Stop icon in the upper left-hand corner of the screen.

When a follow-up dialog pops up asking if you are sure you want to quit the troublemaking process, select the Force Quit option.

Click on the Go menu icon in the Finder again and select Go to Folder. You can as well use the Command-Shift-G keyboard shortcut.

Type /Library/LaunchAgents in the folder search dialog and click on the Go button.

Examine the contents of the LaunchAgents folder for dubious-looking items. Be advised that the names of files spawned by malware may give no clear clues that they are malicious, so you should look for recently added entities that appear to deviate from the norm.
As an illustration, here are several examples of LaunchAgents related to mainstream Mac infections: com.pcv.hlpramc.plist, com.updater.mcy.plist, com.avickUpd.plist, and com.msp.agent.plist. If you spot files that don’t belong on the list, go ahead and drag them to the Trash.

Use the Go to Folder lookup feature again to navigate to the folder named ~/Library/Application Support (note the tilde symbol prepended to the path).

When the Application Support directory is opened, identify recently generated suspicious folders in it and send them to the Trash. A quick tip is to look for items whose names have nothing to do with Apple products or apps you knowingly installed. A few examples of known-malicious folder names are Quick Mac Booster, IdeaShared, and ProgressMatch.

Enter ~/Library/LaunchAgents string (don’t forget to include the tilde character) in the Go to Folder search area.

The system will display LaunchAgents residing in the current user’s Home directory. Look for dodgy items related to Safari virus warning (see logic highlighted in subsections above) and drag the suspects to the Trash.

Type /Library/LaunchDaemons in the Go to Folder search field.

In the LaunchDaemons path, try to pinpoint the files the malware is using for persistence. Several examples of such items cropped by Mac infections are com.pplauncher.plist, com.startup.plist, and com.ExpertModuleSearchDaemon.plist. Delete the sketchy files immediately.

Click on the Go menu icon in your Mac’s Finder and select Applications on the list.

Find the app that clearly doesn’t belong there and move it to the Trash. If this action requires your admin password for confirmation, go ahead and enter it.

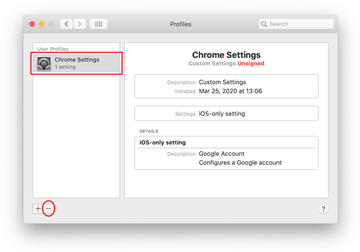
Expand the Apple menu and select System Preferences.


Proceed to Users & Groups and click on the Login Items tab.


Now select Profiles under System Preferences. Look for a malicious item in the left-hand sidebar. Several examples of configuration profiles created by Mac adware include TechSignalSearch, MainSearchPlatform, AdminPrefs, and Chrome Settings. Select the offending entity and click on the minus sign at the bottom to eliminate it.

Get rid of Safari virus warning in the browser on Mac
To begin with, the web browser settings taken over by the Safari virus warning scam should be restored to their default values. Although this will clear most of your customizations, web surfing history, and all temporary data stored by websites, the malicious interference should be terminated likewise. The overview of the steps for completing this procedure is as follows:
Remove Safari virus warning (Mac)
- Open the browser and go to Safari menu. Select Preferences in the drop-down list.

- Once the Preferences screen appears, click on the Advanced tab and enable the option saying “Show Develop menu in menu bar”.

- Now that the Develop entry has been added to the Safari menu, expand it and click on Empty Caches.

- Now select History in the Safari menu and click on Clear History in the drop-down list.

- Safari will display a dialog asking you to specify the period of time this action will apply to. Select all history to ensure a maximum effect. Click on the Clear History button to confirm and exit.

- Go back to the Safari Preferences and hit the Privacy tab at the top. Find the option that says Manage Website Data and click on it.

- The browser will display a follow-up screen listing the websites that have stored data about your Internet activities. This dialog additionally includes a brief description of what the removal does: you may be logged out of some services and encounter other changes of website behavior after the procedure. If you’re okay with that, go ahead and click on the Remove All button.

- Restart Safari
Get rid of Safari virus warning using Combo Cleaner removal tool
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove Safari virus warning virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the Safari virus warning issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove Safari virus warning threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.