The latest security updates for macOS Big Sur, Catalina, and Mojave address dozens of loopholes in multiple services, including Safari, Kernel, and WebKit.
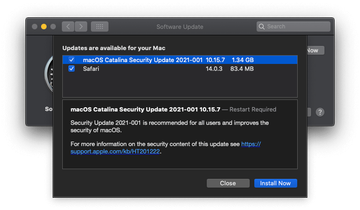
The updates rolled out on February 1, 2021 brought a whopping number of bug fixes to macOS Catalina 10.15.7 and macOS Mojave 10.14.6. This move co-occurred with the release of macOS Big Sur 11.2, which also arrived with multiple patches. In addition to tackling system-wide issues, Apple stepped up users’ web surfing security by introducing Safari 14.0.3 with several improvements onboard. Whereas updates like this happen regularly and are nothing out of the ordinary, this series stands out from the rest. It addresses a total of 66 security flaws across the macOS Big Sur, Catalina, and Mojave ecosystems, plus it sorts out three imperfections in Safari.
Some of these bugs may have been exploited in the wild
In a roundup of security implications behind these issues, Apple listed specific vulnerabilities in macOS areas such as Analytics, APFS, CFNetwork Cache, CoreGraphics, Crash Reporter, Directory Utility, Font Parser, ImageIO, Login Window, Messages, Model I/O, Screen Sharing, and more. Many of these flaws allow an adversary to run malicious code behind a user’s back or cause an adverse condition like heap corruption or a denial of service.
According to Apple, three loopholes could have been actively parasitized in real-world attacks. One of them is a Kernel vulnerability (tracked as CVE-2021-1782) that may allow a malicious app to elevate its privileges. The remaining two (CVE-2021-1870 and CVE-2021-1871) are bugs in the WebKit that may underlie arbitrary code execution in macOS Big Sur 10.0.1. It’s noteworthy that the exact same security gaps were previously patched in iOS 14.4 and iPadOS 14.4 releases that went live in late January 2021. This fact indicates that the flaws are cross-platform. To stay safe, users who are on macOS Big Sur, Catalina, and Mojave should head to Software Update under System Preferences and apply the latest fixes.
