- What is XprotectService on your Mac?
- What can go wrong with XprotectService?
- A crudely designed app or malware could be the culprit
- XprotectService high CPU virus manual removal from Mac
- Get rid of XprotectService related malware in web browser on Mac
- Fix XprotectService Mac issue using Combo Cleaner removal tool
When a macOS process named XprotectService siphons off too much CPU, this could be either the system’s normal anti-malware activity or an anomaly.
What is XprotectService on your Mac?
To answer this question, let’s shed light on what signature-based detection is. This has been the gold standard of malware defenses on computers for decades. It works by comparing a process that runs on a system against a frequently updated database of hallmarks intrinsic to known harmful programs. This principle works at the level of a third-party AV tool and at the level of the operating system. When it comes to macOS, the component responsible for this nontrivial task is called XProtect. Operating in concert with Apple’s prevention-centric security technologies such as Gatekeeper and Notarization, XProtect takes care of dangerous code that has somehow slithered its way into a Mac and has been executed. To do its thing, this crucial element in the system’s native protection chain can run a series of processes visible in the Activity Monitor, including XprotectService, XprotectPluginService, and more.
The XprotectService high CPU and memory virus may re-infect your Mac multiple times unless you delete all of its fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.What can go wrong with XprotectService?
Normally, this workflow runs silently behind the scenes without causing any inconveniences. That’s the way it’s supposed to scan active processes for suspicious signals in an ideal world. But the reality can be different as many users’ feedback illustrates that things aren’t always smooth. Most of those concerns relate to awfully high CPU consumption triggered by this entity periodically or incessantly. A particularly weird symptom is that the CPU usage can skyrocket well beyond a commonsensical 100%. People have reported spikes up to about 700%. This oddity is actually quite easy to explain, though: it manifests itself when more than one core or stream of the processing unit is engaged in a task.
Figuring out these technicalities is certainly worthwhile, but the main question persists. What causes XprotectService to take the route of overkill in regards to the Mac’s processing resources? There is no simple explanation as it all depends on a specific case. This object takes off when you launch an app for the first time, when an already-installed app has been modified, or when the malware signatures database is being updated. It also gets busier than usual when you log into a specific user account after a long hiatus – in that situation, it takes a lot of time and capacity to traverse all programs in search of potential red flags.
A crudely designed app or malware could be the culprit
While the average user can tolerate temporary upswings in processor usage, no one is okay with constant CPU surges. A scenario where the computer’s “brain” is maxing out all the time is a catalyst for system slowdown, kernel panics, freezes, random reboots, and high fan speeds that can still barely reduce the heat. This combo of consequences is at odds with normal user experience, so it should be interpreted as a call to action in terms of the fix.
The service in question might get stuck in a loop when it’s trying to inspect an unresponsive third-party process. As the procedure fails over and over, the CPU takes the brunt of such attempts. This brings us to a theory that fits the mold of malware infection. Corrupted executables, or ones that prevent the system from analyzing them, are often associated with Mac threats such as adware, rogue system optimization tools, info-stealing trojans, or cryptocurrency miners. Another clever trick in cybercriminals’ genre, albeit not a very common one, is to mimic legitimate processes like XprotectService to evade detection.
Restarting a Mac is always a good idea when such predicaments kick in, but in the case of XprotectService that’s a temporary fix. If the built-in system security solutions can’t scan the application and address the risk, it makes sense to try alternative remediation methods. The following sections provide steps to check your machine for signs of contamination, and if such evidence is found, to sort out the malware problem that makes XprotectService gobble up the CPU resources.
XprotectService high CPU virus manual removal from Mac
The steps listed below will walk you through the removal of this malicious application. Be sure to follow the instructions in the specified order.
Expand the Go menu in your Mac’s Finder bar and select Utilities as shown below.

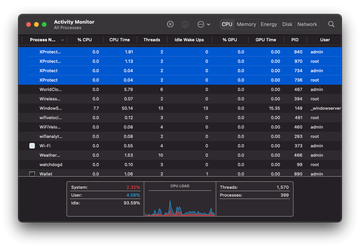
Locate the Activity Monitor icon on the Utilities screen and double-click on it.

In the Activity Monitor app, look for XprotectService or another process that appears suspicious. To narrow down your search, focus on unfamiliar resource-intensive entries on the list. Keep in mind that its name isn’t necessarily related to the way the threat is manifesting itself, so you’ll need to trust your own judgement. If you pinpoint the culprit, select it and click on the Stop icon in the upper left-hand corner of the screen.

When a follow-up dialog pops up asking if you are sure you want to quit the troublemaking process, select the Force Quit option.

Click on the Go menu icon in the Finder again and select Go to Folder. You can as well use the Command-Shift-G keyboard shortcut.

Type /Library/LaunchAgents in the folder search dialog and click on the Go button.

Examine the contents of the LaunchAgents folder for dubious-looking items. Be advised that the names of files spawned by malware may give no clear clues that they are malicious, so you should look for recently added entities that appear to deviate from the norm.
As an illustration, here are several examples of LaunchAgents related to mainstream Mac infections: com.updater.mcy.plist, com.avickUpd.plist, and com.msp.agent.plist. If you spot files that don’t belong on the list, go ahead and drag them to the Trash.

Use the Go to Folder lookup feature again to navigate to the folder named ~/Library/Application Support (note the tilde symbol prepended to the path).

When the Application Support directory is opened, identify recently generated suspicious folders in it and send them to the Trash. A quick tip is to look for items whose names have nothing to do with Apple products or apps you knowingly installed. A few examples of known-malicious folder names are ProgressSite and IdeaShared.

Enter ~/Library/LaunchAgents string (don’t forget to include the tilde character) in the Go to Folder search area.

The system will display LaunchAgents residing in the current user’s Home directory. Look for dodgy items related to rogue XprotectService process (see logic highlighted in subsections above) and drag the suspects to the Trash.

Type /Library/LaunchDaemons in the Go to Folder search field.

In the LaunchDaemons path, try to pinpoint the files the malware is using for persistence. Several examples of such items cropped by Mac infections are com.apple.sysmond.plist, com.startup.plist, and com.ExpertModuleSearchDaemon.plist. Delete the sketchy files immediately.

Click on the Go menu icon in your Mac’s Finder and select Applications on the list.

Find the entry for an app that clearly doesn’t belong there and move it to the Trash. If this action requires your admin password for confirmation, go ahead and enter it.

Expand the Apple menu and select System Preferences.


Proceed to Users & Groups and click on the Login Items tab.

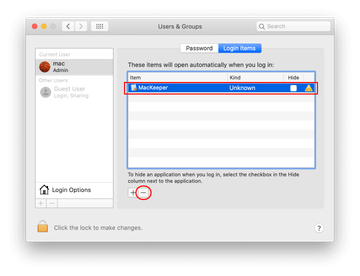
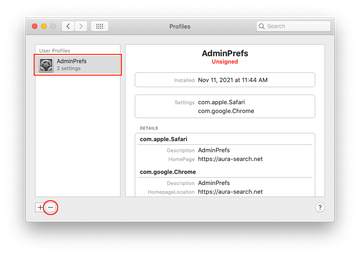
Now select Profiles under System Preferences. Look for a malicious item in the left-hand sidebar. Several examples of configuration profiles created by Mac adware include TechSignalSearch, MainSearchPlatform, AdminPrefs, and Safari Settings. Select the offending entity and click on the minus sign at the bottom to eliminate it.

Get rid of XprotectService related malware in web browser on Mac
To begin with, the web browser settings taken over by the XprotectService copycat malware should be restored to their default values. Although this will clear most of your customizations, web surfing history, and all temporary data stored by websites, the malicious interference should be terminated likewise. The overview of the steps for completing this procedure is as follows:
- Remove XprotectService virus from Safari
- Open the browser and go to Safari menu. Select Preferences in the drop-down list.

- Once the Preferences screen appears, click on the Advanced tab and enable the option saying “Show Develop menu in menu bar”.

- Now that the Develop entry has been added to the Safari menu, expand it and click on Empty Caches.

- Now select History in the Safari menu and click on Clear History in the drop-down list.

- Safari will display a dialog asking you to specify the period of time this action will apply to. Select all history to ensure a maximum effect. Click on the Clear History button to confirm and exit.

- Go back to the Safari Preferences and hit the Privacy tab at the top. Find the option that says Manage Website Data and click on it.

- The browser will display a follow-up screen listing the websites that have stored data about your Internet activities. This dialog additionally includes a brief description of what the removal does: you may be logged out of some services and encounter other changes of website behavior after the procedure. If you’re okay with that, go ahead and click on the Remove All button.

- Restart Safari
- Open the browser and go to Safari menu. Select Preferences in the drop-down list.
- Remove XprotectService virus in Google Chrome
- Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down

- When on the Settings pane, select Advanced
- Scroll down to the Reset settings section.

- Confirm the Chrome reset on a dialog that will pop up. When the procedure is completed, relaunch the browser and check it for malware activity.

- Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down
- Fix XprotectService problem on Mozilla Firefox
- Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).


- When on the Troubleshooting Information screen, click on the Refresh Firefox button.

- Confirm the intended changes and restart Firefox.
- Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).
Fix XprotectService Mac issue using Combo Cleaner removal tool
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove XprotectService high CPU virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the XprotectService high CPU issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove XprotectService high CPU threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.
