With many users wondering if an email can infect a computer with a virus when opened, let’s go over the risk scenarios and figure out the right precautions.
Common sources of infection through email
The average cybersecurity advisory you’ll find online is half-baked if it doesn’t emphasize the importance of being wary of suspicious emails. There is a strong reason why it doesn’t hurt to be a little paranoid about messages that end up in one’s inbox, especially those received from strangers. However, most of these threats relate to instances where recipients interact with specific contents of an email. In other words, a user should be on the safe side as long as they refrain from clicking a link or downloading an attachment. Links can lead to drive-by malware downloads, tech support scams, and credential phishing pages. Attachments may harbor hidden executables that start running in the background once you open those embedded files without a second thought. To top it off, virus authors use social engineering “best practices” to dupe people into slipping up and engaging with such potentially unsafe objects.
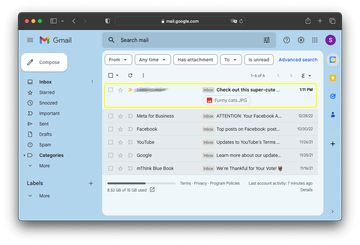
Sketchy attachments often come in the form of images or text files that have a double extension. This trick allows criminals to conceal the actual format of the file and thereby make the would-be victim think they are dealing with something harmless. An example is “Funny cats.JPG.DMG” that appears to be an image based on the first appended extension, but turns out to be a disk image item that can run arbitrary code and install potentially unwanted software. Compressed ZIP files in emails are notorious carriers of dangerous content, too. There are plenty of other tricks that malefactors use to manipulate people and circumvent traditional filtering services, such as secure email gateways (SEGs), so that their malicious messages get through. While it’s clear that attachments and links are potential sources of danger, can you get a virus by simply opening an email? The odds of this are close to zero, but with a caveat.
A virus may re-infect your Mac multiple times unless you delete all of its fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.Can an email be harmful with a minimum of interaction?
Luckily, this is a marginal situation that hardly ever occurs in the wild. In theory, the peril may stem from scripts that launch quietly whether or not you click anything inside a message. These scripts typically run in an HTML environment, which is a protocol used by most (if not all) email clients and web-based email services. HTML is what makes messaging more user-friendly and graphically neat, but since it can be a catalyst for contamination due to the vast scripting possibilities, it may be a good idea to disable it if the email service you are using supports such an option. This way, the information will be in plaintext and the likelihood of security problems is close to zero. The good news is that most people don’t have to bother going the extra mile, because tailoring a virus-riddled message like that is easier said than done. It requires the use of zero-day exploits that are mainly the prerogative of high-profile cybercriminals. By and large, unless you are a three-letter agency official or hold a similarly important position, there is no need to worry.
Tips to avoid email-borne threats
Although a trivial instance of opening a message in the inbox isn’t likely to get you in trouble, email is one of the top channels for distributing malware and viruses. Therefore, this is an area where proper security hygiene makes a lot of sense. The following recommendations will help you steer clear of viruses that arrive with emails:
- Avoid clicking on links in emails. If you know the sender, consider first contacting that person to ask where the link leads and other details.
- Don’t open attachments sent by someone you don’t know. If your curiosity takes over, right-click the file and select the option to scan it for viruses with a reliable security app if you are using one. Even better, use a people search free tool to verify the sender's details before interacting with the email.
- Disable HTML in your email client or web-based email service if you are okay with messages in plaintext.
- Configure your email client or service to maximize its filtering activity so that messages whose structure fits known-malicious phishing or malware spreading templates don’t get a chance to reach your inbox.
- Read the contents of an email carefully. If it claims to be from a reputable company or trusted individual but the text contains errors and typos, this could be an impostor.
- Keep your most important data backed up to protect it from being stolen by viruses or encrypted by ransomware.
To recap, just opening an email is unlikely to trigger virus infection on your Mac. The threat escalates if you click or open something inside a booby-trapped message. With the right combination of vigilance and automated defenses with an antivirus and email filtering features, you should be good to go. If you suspect malicious code has infiltrated your computer through an email, follow the steps below to err on the side of caution.
Remove a virus that came in an email
The steps listed below will walk you through the removal of this malicious application. Be sure to follow the instructions in the specified order.
Expand the Go menu in your Mac’s Finder bar and select Utilities as shown below.

Locate the Activity Monitor icon on the Utilities screen and double-click on it.

In the Activity Monitor app, look for a process that appears suspicious. To narrow down your search, focus on unfamiliar resource-intensive entries on the list. Keep in mind that its name isn’t necessarily related to the way the threat is manifesting itself, so you’ll need to trust your own judgement. If you pinpoint the culprit, select it and click on the Stop icon in the upper left-hand corner of the screen.

When a follow-up dialog pops up asking if you are sure you want to quit the troublemaking process, select the Force Quit option.

Click on the Go menu icon in the Finder again and select Go to Folder. You can as well use the Command-Shift-G keyboard shortcut.

Type /Library/LaunchAgents in the folder search dialog and click on the Go button.

Examine the contents of the LaunchAgents folder for dubious-looking items. Be advised that the names of files spawned by malware may give no clear clues that they are malicious, so you should look for recently added entities that appear to deviate from the norm.
As an illustration, here are several examples of LaunchAgents related to mainstream Mac infections: com.updater.mcy.plist, com.avickUpd.plist, and com.msp.agent.plist. If you spot files that don’t belong on the list, go ahead and drag them to the Trash.

Use the Go to Folder lookup feature again to navigate to the folder named ~/Library/Application Support (note the tilde symbol prepended to the path).

When the Application Support directory is opened, identify recently generated suspicious folders in it and send them to the Trash. A quick tip is to look for items whose names have nothing to do with Apple products or apps you knowingly installed. A few examples of known-malicious folder names are com.AuraSearchDaemon, ProgressSite, and IdeaShared.

Enter ~/Library/LaunchAgents string (don’t forget to include the tilde character) in the Go to Folder search area.

The system will display LaunchAgents residing in the current user’s Home directory. Follow the above logic to find dodgy items related to the email virus. Drag these files to the Trash.

Type /Library/LaunchDaemons in the Go to Folder search field.

In the LaunchDaemons path, try to pinpoint the files the virus is using for persistence. Several examples of items cropped by Mac infections are com.pplauncher.plist, com.startup.plist, and com.mulkeyd.plist. Delete the sketchy files immediately.

Click on the Go menu icon in your Mac’s Finder and select Applications on the list.

Find the app that clearly doesn’t belong there and move it to the Trash. If this action requires your admin password for confirmation, go ahead and enter it.

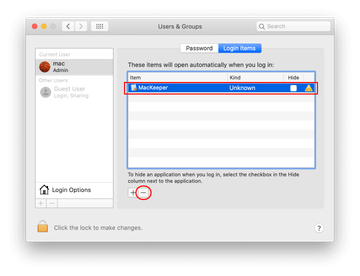
Expand the Apple menu and select System Preferences.


Proceed to Users & Groups and click on the Login Items tab.

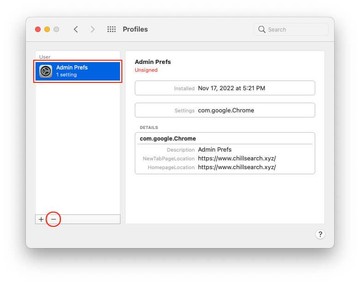
Now select Profiles under System Preferences. Look for a malicious item in the left-hand sidebar. Several examples of configuration profiles created by Mac adware include AdminPrefs, TechSignalSearch, MainSearchPlatform and Safari Preferences. Select the offending entity and click on the minus sign at the bottom to eliminate it.

Get rid of a virus in a web browser on Mac
To begin with, the web browser settings taken over by the email virus should be restored to their default values. Although this will clear most of your customizations, web surfing history, and all temporary data stored by websites, the malicious interference should be terminated likewise. The overview of the steps for completing this procedure is as follows:
- Remove a virus in Safari
- Open the browser and go to Safari menu. Select Preferences in the drop-down list.

- Once the Preferences screen appears, click on the Advanced tab and enable the option saying “Show Develop menu in menu bar”.

- Now that the Develop entry has been added to the Safari menu, expand it and click on Empty Caches.

- Now select History in the Safari menu and click on Clear History in the drop-down list.

- Safari will display a dialog asking you to specify the period of time this action will apply to. Select all history to ensure a maximum effect. Click on the Clear History button to confirm and exit.

- Go back to the Safari Preferences and hit the Privacy tab at the top. Find the option that says Manage Website Data and click on it.

- The browser will display a follow-up screen listing the websites that have stored data about your Internet activities. This dialog additionally includes a brief description of what the removal does: you may be logged out of some services and encounter other changes of website behavior after the procedure. If you’re okay with that, go ahead and click on the Remove All button.

- Restart Safari
- Open the browser and go to Safari menu. Select Preferences in the drop-down list.
- Remove a virus in Google Chrome
- Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down

- When on the Settings pane, select Advanced
- Scroll down to the Reset settings section.

- Confirm the Chrome reset on a dialog that will pop up. When the procedure is completed, relaunch the browser and check it for malware activity.

- Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down
- Remove a virus in Mozilla Firefox
- Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).


- When on the Troubleshooting Information screen, click on the Refresh Firefox button.

- Confirm the intended changes and restart Firefox.
- Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).
Get rid of an email virus using Combo Cleaner removal tool
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove email virus virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the email virus issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove email virus threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.
