Security researchers at Trend Micro shared details about a new privilege escalation flaw affecting CVMServer on macOS Big Sur, iOS, and iPadOS.
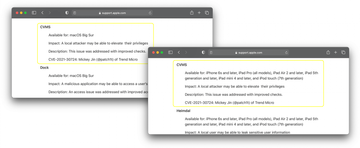
In late May 2021, Apple released updates for all platforms under its umbrella. While digging through the official documentation that covered the security content of these improvements, most reviewers would pay attention to issues that may have been exploited in the wild, such as the TCC loophole misused by XCSSET malware. Amid eye-catching stuff, it’s easy to miss bugs that could have an equally serious real-world impact. The one discovered by Trend Micro fits the mold of such an “underdog” vulnerability. Tracked as CVE-2021-30724, it affects the CVMServer system daemon in operating system versions older than macOS Big Sur 11.4, iOS 14.6, and iPadOS 14.6. The imperfection is patched in the latest releases.
CVE-2021-30724 vulnerability details
The risks are high because the loophole undermines the security of macOS and iOS/iPadOS at the level of XPC, a low-level (libSystem) mechanism responsible for interoperability between different system processes. The affected Core Virtual Machine Server (CVMServer) is part of the XPC framework that manages the execution of generic tasks. According to Trend Micro, the flaw is in the way the XPC application programming interface (API) handles request messages from client processes before sending them to the server.
To exploit the vulnerability, a malicious actor can modify the code of the CVMServer logic by specifying a larger integer for the request length value and thereby circumvent the normal checks. This, in turn, will trigger an out-of-bounds memory access condition, which is a common launch pad for privilege escalation in the target system.
How to stay safe
As previously stated, Apple has addressed this bug by fine-tuning the checks to prevent integer overflow when XPC request messages are processed. However, a device stays susceptible to compromise unless it’s running the latest macOS Big Sur 11.4, iOS 14.6, or iPadOS 14.6. To make sure you are in the clear, head to system preferences and check the current version of the operating system. If an update is available, apply it immediately.
