Malware authors broke new ground by creating a strain that runs on the latest Mac models with innovative ARM-based M1 processors on board.
Whereas malware has been running amok around the Apple landscape for years and the myth about virus-proof Macs sank into oblivion a long time ago, the ARM-M1 hardware architecture looked like a promising step forward in terms of security. Geared toward departing from the long-standing Intel x86 domination, this breakthrough has also allowed the Cupertino company to incorporate more robust defenses at the processor level. However, expectations from the big shift may have been blown out of proportion, with the recent cybercrime developments giving rise to a malware sample that runs natively on machines with these chips under the hood.
M1-compatible malware makes its debut
It looks like regular app developers aren’t the only ones who have had a ton of work to do for a smooth transition to the Apple Silicon framework since it was launched in November last year. Cybercrooks appear to have been busy making their shadowy code fit the M1 context as well. The emergence of an “ARM-aware” threat called GoSearch22 became the wake-up call. This is a spinoff of Pirrit, one of today’s dominating Mac adware lineages.
According to the findings of well-known security researcher Patrick Wardle, somebody uploaded this sample to the VirusTotal service for the first time in late December, that is to say, in fairly quick succession after the M1 system on a chip (SoC) technology was deployed. Flagged by antivirus engines as a variant of Pirrit, this pest pretends to be a garden-variety Safari extension. When installed, though, it snoops on the victim’s online activities, steals data relating to system specifications, triggers dubious pop-up ads, and may forward the web traffic to knock-off search engines.
Detection pitfalls
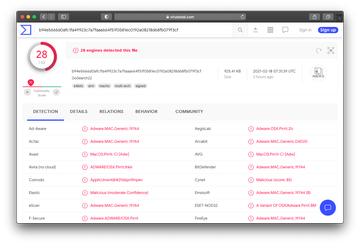
Furthermore, the malicious app was signed with a valid digital certificate at the time of discovery. Apple revoked it shortly after being notified of the foul play. Aside from this antivirus evasion trick, the researcher also found that the M1 version of GoSearch22 adware was detected by 15% fewer AV engines across the spectrum than its x86 counterpart. The difference stems from the fact that classic security tools often use signature-based analysis to identify Mac threats, and this void has yet to be filled for the ARM paradigm.
Although the new Pirrit adware variant that works seamlessly on Apple Silicon machines isn’t particularly harmful, it demonstrates the viability of such threats and will most likely pave the way for successors. Under the circumstances, security vendors need to focus on aligning their products with the new challenges.
