- An insanely easy exploitation trick
- Social engineering trickery takes the attack to the next level
- Bad actors’ goals
- iPhone Calendar virus removal
- How to prevent malicious iPhone Calendar events from reappearing
- Remove misleading Calendar events virus from Mac
- Get rid of Spammy Calendar events virus in web browser on Mac
- Get rid of rogue Calendar events virus using Combo Cleaner removal tool
- FAQ
This article provides detailed walkthroughs to get rid of misleading events that recurrently poison the Calendar app on an iOS device or Mac computer.
Update:
Accidentally tapping or clicking something on the Internet entails a fair degree of potential risk these days. Whether it’s an innocuous-looking popup ad, an in-text link, or an “Allow Notifications” dialog from a web page, the outcome can range from a trivial one-time browser redirect – all the way to a malware download hidden in plain sight. In some cases, though, the entrapment comes down to a plethora of spam links being served through a third-party application or one pre-installed on the victim’s device as part of the feature set that comes with the operating system.
A growingly prolific malvertising wave of that sort is underway hitting iPhone and Mac users. It relies on a combo of social engineering and malicious code to litter around one’s Calendar app. The affected users get numerous spammy events and invitations added to their built-in Calendar. As if the influx of these entries weren’t enough to ruin the experience of a self-organized user, they are riddled with hyperlinks leading to shady sites.
An insanely easy exploitation trick
Often blamed on what’s called the iPhone Calendar virus, this ambush might have a less technically complex nature than the tedious process of developing and distributing malicious software or website scripts. Believe it or not, a malefactor may be able to send deceptive invitations by simply knowing the email address enrolled in the would-be victim’s Calendar account. The reason is that the application is configured to keep its doors wide open for anybody in terms of such appointments by default.
This indiscriminate tactic is at the heart of the service in question because it eliminates all barriers for members of the Apple user community to interact with each other. At the same time, it’s a major weak link of the Calendar app when it comes to abuse. Simply put, a malicious actor may obtain user credentials, possibly dumped on the Dark Web in the aftermath of a data breach incurred by an email provider, and from there orchestrate a spam campaign featuring custom event descriptions with phishing links in them.
Spammy Calendar events virus may re-infect your Mac multiple times unless you delete all of its fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.Social engineering trickery takes the attack to the next level
Whereas the offensive logic described above is one of the plausible scenarios, there is a more vicious facet of the issue that adds virus activity to the mix. It’s about an instance of tapping on an advertisement online that sets a well-trodden contamination routine in motion. Most users do it unintentionally or in an attempt to close an ad they find intrusive.
Furthermore, most of these dialogs are designed to evoke curiosity and a false sense of security. This explains why an iPhone or Mac user is likely to click through to explore in depth what’s being advertised, only to trigger a furtive website script that delivers a piece of malware to the device. Next thing the victim knows, the Calendar widget starts getting deluged with deceptive events, invitations, and appointments. These items come in huge quantities, ending up on the app’s list once or several times an hour. An additional nuisance is that they may be combined with audio alerts going off almost non-stop.
In some scenarios, the emergence of spammy Calendar events on a Mac overlaps with an adware attack. This is an upshot of installing a software bundle that promotes several potentially unwanted applications (PUAs) in one go. A common symptom of extra infection is a browser hijack accompanied by misleading popups that say, “Your computer is low on memory”. What sets this alert apart from a genuine macOS counterpart is that it occurs even if the machine has more than enough free RAM. The objective is to dupe the user into clicking a wrong button that may quietly trigger a dubious drive-by download.
Bad actors’ goals
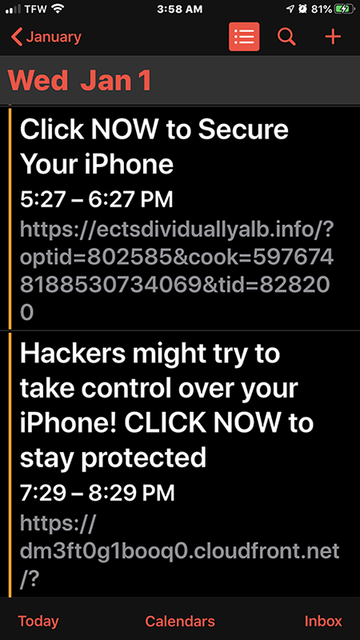
The themes of these fake Calendar events are typically related to some security issue with the Apple device, a recommendation to claim a gift that’s too good to be true, a photo sharing session with a stranger, or something similar that captures one’s attention. The bogus virus or compromise report, which is among the most common subjects, is aimed at giving the victim a heads-up via phrases like “Hackers might try to take control over your iPhone” or “Click now to secure your iPhone”.
One way or another, all of these spoofed messages share one characteristic – they are laced with clickable links that are spammy or clearly malicious. By clicking them, the user runs the risk of visiting a fake login form and other types of phishing pages. Sometimes the links lead to info-stealing malware or adware. The only good news is, the Calendar virus problem is usually quite easy to deal with no matter if it’s encountered on an iPhone, iPad, or a Mac computer. The instructions below will do the trick, so go ahead and follow them to regain a peace of mind and make sure only real and worthwhile events show up in the Calendar app.
iPhone Calendar virus removal
If spammy events are constantly showing up in the iPhone Calendar app, there are several steps that will sort out the issue. For a start, it’s recommended to delete the sketchy calendar that was added to the device by a third-party service without proper authorization. Note that the following three steps apply to iOS 14, the latest version of Apple’s mobile operating system.
- Go to Settings and select Calendar.
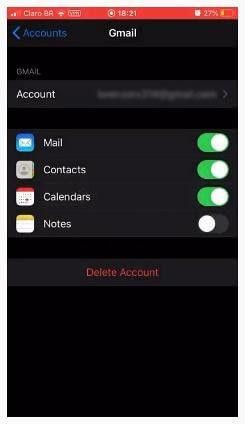
- Tap Accounts and try to spot the malicious entry. Examining account details such as the email address should give you some important clues about which one is the culprit.
- If you find the rogue item, go ahead and delete it using on-screen prompts.
If your device is running iOS 13 or earlier, then the process of eliminating the dodgy calendar is as follows:
- Tap Settings in the Home screen and select Passwords & Accounts.
- Under the subsection called Accounts, find an unfamiliar account whose access permissions include, among other things, the “Calendars” feature. Its name may be “Subscribed Calendars”, “Other Calendars”, or similar.

- Select the unwanted account and tap the “Delete Account” button at the bottom.
Now that the underlying issue has been addressed, it’s recommended to make doubly sure that the same trick won’t reoccur down the road.
How to prevent malicious iPhone Calendar events from reappearing
In order to ascertain that the same hoax won’t play out again, you need to configure your personal Calendar preferences accordingly. Here’s the walkthrough to do it.
- Sign into your iCloud account and select Calendar.
- Click the gear symbol in the bottom left-hand corner of the app screen and select Preferences.
- Hit the Advanced tab.
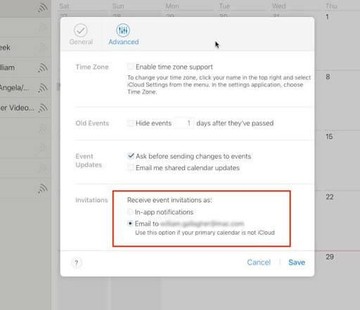
- In the subsection called Invitations, click the radio button next to the “Email to [your email address]” option to make this setting your default one instead of “In-app notifications”.
Remove misleading Calendar events virus from Mac
The steps listed below will walk you through the removal of this malicious application. Be sure to follow the instructions in the specified order.
Expand the Go menu in your Mac’s Finder bar and select Utilities as shown below.

Locate the Activity Monitor icon on the Utilities screen and double-click on it.

In the Activity Monitor app, look for a process that appears suspicious. To narrow down your search, focus on unfamiliar resource-intensive entries on the list. Keep in mind that its name isn’t necessarily related to the way the threat is manifesting itself, so you’ll need to trust your own judgement. If you pinpoint the culprit, select it and click on the Stop icon in the upper left-hand corner of the screen.

When a follow-up dialog pops up asking if you are sure you want to quit the troublemaking process, select the Force Quit option.

Click on the Go menu icon in the Finder again and select Go to Folder. You can as well use the Command-Shift-G keyboard shortcut.

Type /Library/LaunchAgents in the folder search dialog and click on the Go button.

Examine the contents of the LaunchAgents folder for dubious-looking items. Be advised that the names of files spawned by malware may give no clear clues that they are malicious, so you should look for recently added entities that appear to deviate from the norm.
As an illustration, here are several examples of LaunchAgents related to mainstream Mac infections: com.pcv.hlpramc.plist, com.updater.mcy.plist, com.avickUpd.plist, and com.msp.agent.plist. If you spot files that don’t belong on the list, go ahead and drag them to the Trash.

Use the Go to Folder lookup feature again to navigate to the folder named ~/Library/Application Support (note the tilde symbol prepended to the path).

When the Application Support directory is opened, identify recently generated suspicious folders in it and send them to the Trash. A quick tip is to look for items whose names have nothing to do with Apple products or apps you knowingly installed. A few examples of known-malicious folder names are Mac Cleanup Pro, IdeaShared, and ProgressMatch.

Enter ~/Library/LaunchAgents string (don’t forget to include the tilde character) in the Go to Folder search area.

The system will display LaunchAgents residing in the current user’s Home directory. Look for dodgy items related to the Calendar spam virus (see logic highlighted in subsections above) and drag the suspects to the Trash.

Type /Library/LaunchDaemons in the Go to Folder search field.

In the LaunchDaemons path, try to pinpoint the files the malware is using for persistence. Several examples of such items cropped by Mac infections are com.pplauncher.plist, com.startup.plist, and com.ExpertModuleSearchDaemon.plist. Delete the sketchy files immediately.

Click on the Go menu icon in your Mac’s Finder and select Applications on the list.

Find an app that clearly doesn’t belong there and move it to the Trash. If this action requires your admin password for confirmation, go ahead and enter it.

Expand the Apple menu and select System Preferences.


Proceed to Users & Groups and click on the Login Items tab.


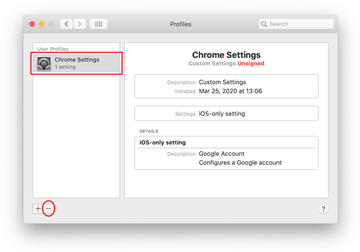
Now select Profiles under System Preferences. Look for a malicious item in the left-hand sidebar. Several examples of configuration profiles created by Mac adware include TechSignalSearch, MainSearchPlatform, AdminPrefs, and Chrome Settings. Select the offending entity and click on the minus sign at the bottom to eliminate it.

Get rid of Spammy Calendar events virus in web browser on Mac
To begin with, the web browser settings taken over by the Spammy Calendar events virus should be restored to their default values. Although this will clear most of your customizations, web surfing history, and all temporary data stored by websites, the malicious interference should be terminated likewise. The overview of the steps for completing this procedure is as follows:
- Remove Spammy Calendar events virus from Safari
Open the browser and go to Safari menu. Select Preferences in the drop-down list.

Once the Preferences screen appears, click on the Advanced tab and enable the option saying “Show Develop menu in menu bar”.

Now that the Develop entry has been added to the Safari menu, expand it and click on Empty Caches.

Now select History in the Safari menu and click on Clear History in the drop-down list.

Safari will display a dialog asking you to specify the period of time this action will apply to. Select all history to ensure a maximum effect. Click on the Clear History button to confirm and exit.

Go back to the Safari Preferences and hit the Privacy tab at the top. Find the option that says Manage Website Data and click on it.

The browser will display a follow-up screen listing the websites that have stored data about your Internet activities. This dialog additionally includes a brief description of what the removal does: you may be logged out of some services and encounter other changes of website behavior after the procedure. If you’re okay with that, go ahead and click on the Remove All button.

Restart Safari
- Remove Spammy Calendar events in Google Chrome
Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down

When on the Settings pane, select Advanced
Scroll down to the Reset settings section.

Confirm the Chrome reset on a dialog that will pop up. When the procedure is completed, relaunch the browser and check it for malware activity.

- Remove Spammy Calendar events from Mozilla Firefox
Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).


When on the Troubleshooting Information screen, click on the Refresh Firefox button.

Confirm the intended changes and restart Firefox.
Get rid of rogue Calendar events virus using Combo Cleaner removal tool
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove Spammy Calendar events virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the Spammy Calendar events issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove Spammy Calendar events threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.
FAQ
How do I remove spam from my iPhone Calendar?
The easiest way to purge a specific unwanted notification from the Calendar app on your iPhone is to tap it and select the Decline or Delete Event option. However, this is just about as effective as addressing a symptom without curing a disease, because more spammy items will be showing up down the line.
To apply a fix that lasts, you’ll need to identify and get rid of the root cause for the onset of these obnoxious events. This tends to be a dodgy subscription you may have unwittingly opted for at some point. Be advised that the method depends on your iOS version.
If your device is running the latest release (iOS 14), head to Settings > Calendar > Accounts, and look for suspicious items in there. If you pinpoint a shadowy account, delete it without a second thought.
For iOS 13 and earlier, go to Settings > Passwords & Accounts > Accounts, and remove the entry and doesn’t belong there.
How do I remove a virus from my Calendar iOS 14?
As described in the previous answer, you’ll need to open Settings, select Calendar, and tap Accounts. Try to spot the rogue account you don’t remember adding. Once that entry is found, go ahead and remove it. A quick tip is to look for a calendar whose icon shares the color and design elements with the spammy events that keep inundating your iPhone’s Calendar app. In most cases, the rogue entity stands out from the rest in terms of its visual manifestation and is therefore easy to identify. Keep in mind that it is linked with an account that uses an unfamiliar email address.
How do I remove a subscribed calendar virus?
It depends on the device that’s on the receiving end of the Calendar spam. If it’s a Mac, you’ll have to go the extra mile checking a series of system paths for unwanted files or folders. These include Applications, Application Support, LaunchAgents, and LaunchDaemons. Additionally, peek into System Preferences > Users & Groups > Login Items and remove an app that looks out of place. System Preferences > Profiles is another place to examine. If a suspicious configuration profile is listed there, click the minus icon to get rid of it.
One more thing to consider is that Calendar spam virus attack may co-occur with sneaky infiltration of other malware. If so, your default web browser may be redirected to junk sites or fake search engines. In this case, an extra troubleshooting layer is to delete caches, history, and other data spawned by malicious sites. The tutorial above explains each step in detail.
If a dodgy subscribed calendar crops up on your iPhone, then you should go to Settings > Calendar > Accounts, and eliminate an entry you don’t recognize. For iOS 13 and older versions of the operating system, the path is as follows: Settings > Passwords & Accounts > Accounts.
