A developer has found a vulnerability that allows an attacker to bypass privacy protections in macOS Mojave and later versions of the operating system.
The exploit was discovered by a macOS developer named Jeff Johnson in September 2019 but hadn’t been disclosed to the public until late June 2020. The reason for this gap is that the enthusiast reported his findings to the Apple Security Bounty Program the day it was launched (December 19, 2019) in an attempt to get a reward. This was followed by a merry-go-round of status update requests from the researcher and statements from the company’s engineers that they were investigating the issue. When the white hat realized that the progress of addressing the bug was stuck amid empty assurances from the Product Security team and he wasn’t going to get paid, he published his analysis of the loophole. According to it, the exploit circumvents Apple’s Transparency, Consent, and Control (TCC) framework. The proof-of-concept attack can be executed on macOS 10.14 Mojave, macOS 10.15 Catalina, and even in the first beta version of macOS 11 Big Sur.
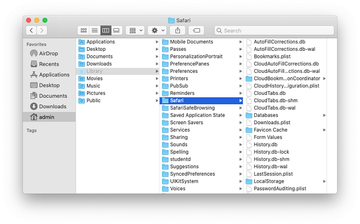
To demonstrate the logic of the TCC bypass, the researcher created a malicious clone of the Safari app. The catch is that the copycat is created in a path on disk that’s different from the location of the original program. Although the evil counterpart of the app comes with altered resources, it uses the exact same file access privileges as the benign prototype. In addition to accessing the contents of the ~/Library/Safari folder on the Mac, the malware in disguise can send the surreptitiously retrieved data to a remote server.
There are two security vulnerabilities that enable a hypothetical adversary to set this incursion in motion. First off, the macOS permission exceptions revolve around a bundle identifier while ignoring the file path from which a program is run. Secondly, application code signature checks aren’t performed rigorously enough. Based on these inconsistencies, Johnson calls the privacy tools built into the system a “security theater” as they create roadblocks to legitimate developers while at the same time allowing malicious apps to get around them easily through plenty of imperfections.
After letting Apple’s Product Security know about this exploitation vector in December last year, the analyst was told that the flaw would be patched in spring 2020. As time went by, none of this happened. In June 2020, the macOS 11 Big Sur beta became available to developers. According to the researcher who tested his exploit on the all-new platform, this build is also susceptible to the bug. Having waited for more than six months after the vulnerability report, which exceeds the 90-day “reasonable disclosure” period, he decided to spread the word about these findings. In his blog post, Johnson also calls the Apple Security Bounty a “disappointment” and says he doesn’t plan on participating again in the future. At this point, the only effective way to mitigate this vulnerability is to avoid installing apps from outside of the official App Store.
