Find out how the new EvilQuest ransomware infects Macs, what damage it causes aside from the classic data encryption, and how to recover from the attack.
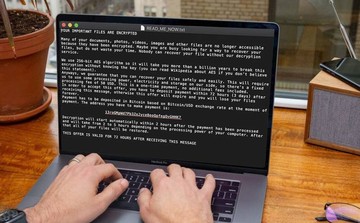
Sometimes cybercriminals use specific properties of malicious code to smokescreen a different vector of their activity. For instance, what looks like a typical ransom Trojan can be a data wiper or an info-stealing virus in disguise. Whereas this isn’t a mainstream tactic, the all-new Mac ransomware dubbed EvilQuest fits the mold of such a hybrid threat. Discovered in late June 2020, it scrambles a victim’s files by means of a strong cryptographic algorithm, creates a ransom note named READ_ME_NOW.txt, and demands $50 worth of Bitcoin for the decryption. This is an unusually low ransom compared to the average amount the counterparts ask for. A little bit of deeper insight into this attack, though, might explain this inconsistency. Unlike the notorious predecessors, including KeRanger, Patcher, and FileCoder, this one doesn’t really focus on bilking Mac users for money. Instead, it appears to employ the extortion routine as a red herring. What is EvilQuest’s real goal, then?
It turns out that the ransomware under scrutiny additionally comes with keylogging and data theft modules. This way, it harvests the Mac user’s images, different types of text files, databases, spreadsheets, presentations, backups, cryptocurrency wallets, and sensitive credentials. Once EvilQuest scans the host for this information and finds the entirety of items that match its data formats criteria, it establishes a stealth connection with its Command and Control server by opening a reverse shell. The infection harnesses it as a backdoor to download arbitrary files onto the Mac and exfiltrate the amassed data behind the scenes. Whilst this is an inconspicuous part of the attack, there are plenty of noticeable symptoms. The perpetrating program isn’t very discriminate in terms of the information it encrypts. Because it locks down some system files along the way, the machine may start acting up. A few reported examples of the resulting bugs are as follows: the Finder may become unresponsive, and the Dock might assume its default look and feel all of a sudden.
EvilQuest ransomware may re-infect your Mac multiple times unless you delete all of its fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
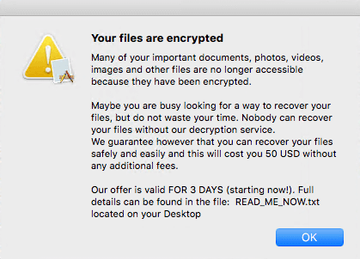
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.With that said, the most prominent part of EvilQuest ransomware’s incursion is the extortion, although its implementation is kind of broken, perhaps on purpose. Having applied a cipher to make data inaccessible, it displays an alert that says, “Your files are encrypted” in its header. It also drops a rescue note. As previously mentioned, it’s named READ_ME_NOW.txt. The contents of this object echo the info outlined in the popup warning, plus there are additional details such as cryptographic nuances and the Bitcoin wallet address for payments. The overlapping text fragments in both of these victim interaction elements say: “Many of your documents, photos, videos, images and other files are no longer accessible because they have been encrypted. Maybe you are busy looking for a way to recover your files, but do not waste your time. Nobody can recover your file without our decryption service.”
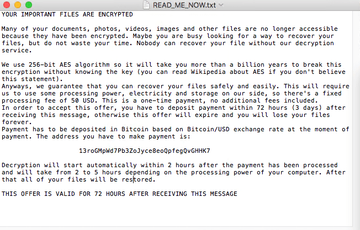
The how-to document also specifies a 72-hour deadline for submitting a ransom of $50 in Bitcoin. After this period expires, the data will be supposedly erased for good. The interesting thing is that according to the note, the decryption will commence on its own within two hours after the crooks receive the payment. The caveat is that even the most sophisticated, long-running ransomware species out there don’t use an automatic recovery logic, most likely because its implementation is too complex from a technical perspective. This claim made by EvilQuest is one of the clues suggesting that its operators are bluffing. An even more obvious giveaway proving this theory is that it uses a static Bitcoin address. In other words, all the victims are coerced to send funds to the exact same destination, and therefore the criminals are unable to associate payments with specific users who made them. The apparent conclusion is that EvilQuest attackers won’t provide a data recovery service down the road.
Although this isn’t clearly a hallmark of a data wiper, the lack of an effective decryption mechanism means that the attackers aren’t pursuing an extortion objective. Their primary mission is to steal data instead. One way or another, the files affected by this non-typical ransomware cannot be reinstated unless the victim has an up-to-date backup. If there is a recent copy of all the data stored externally, the use of the macOS Migration Assistant tool should help restore it – the relevant instructions are provided further down. An important thing to keep in mind, though, is that EvilQuest ransomware removal should come first; otherwise the pest will do its job and probably encrypt the files again.
Speaking of the prevention, the pro tip is to avoid pirated software installers. This particular strain is spreading through booby-trapped versions of popular applications, including the Little Snitch firewall solution and the audio processing tool called Ableton. So, following safe app installation practices is the key prerequisite for avoiding the EvilQuest nasty.
EvilQuest ransomware manual removal for Mac
The steps listed below will walk you through the removal of this malicious application. Be sure to follow the instructions in the specified order.
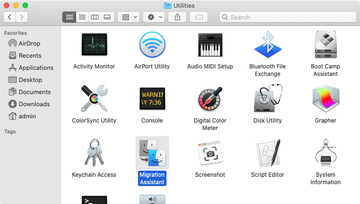
Expand the Go menu in your Mac’s Finder bar and select Utilities as shown below.

Locate the Activity Monitor icon on the Utilities screen and double-click on it.

In the Activity Monitor app, look for questd or another process that appears suspicious. To narrow down your search, focus on unfamiliar resource-intensive entries on the list. Keep in mind that its name isn’t necessarily related to the way the threat is manifesting itself, so you’ll need to trust your own judgement. If you pinpoint the culprit, select it and click on the Stop icon in the upper left-hand corner of the screen.

When a follow-up dialog pops up asking if you are sure you want to quit the troublemaking process, select the Force Quit option.

Click on the Go menu icon in the Finder again and select Go to Folder. You can as well use the Command-Shift-G keyboard shortcut.

Type /Library/LaunchAgents in the folder search dialog and click on the Go button.

Examine the contents of the LaunchAgents folder for dubious-looking items. Be advised that the names of files spawned by malware may give no clear clues that they are malicious, so you should look for recently added entities that appear to deviate from the norm.
As an illustration, here are several examples of LaunchAgents related to mainstream Mac infections: com.apple.questd.plist, com.pcv.hlpramc.plist, com.updater.mcy.plist, com.avickUpd.plist, and com.msp.agent.plist. If you spot files that don’t belong on the list, go ahead and drag them to the Trash.

Use the Go to Folder lookup feature again to navigate to the folder named ~/Library/Application Support (note the tilde symbol prepended to the path).

When the Application Support directory is opened, identify recently generated suspicious folders in it and send them to the Trash. A quick tip is to look for items whose names have nothing to do with Apple products or apps you knowingly installed. A few examples of known-malicious folder names are AppQuest, LinkBranch, SystemSpecial, and IdeaShared.

Enter ~/Library/LaunchAgents string (don’t forget to include the tilde character) in the Go to Folder search area.

The system will display LaunchAgents residing in the current user’s Home directory. Look for com.apple.questd.plist or other dodgy items related to EvilQuest ransomware (see logic highlighted in subsections above) and drag the suspects to the Trash.

Type /Library/LaunchDaemons in the Go to Folder search field.

In the LaunchDaemons path, try to pinpoint the files the malware is using for persistence. Several examples of such items cropped by Mac infections are com.apple.questd.plist, com.startup.plist, and com.ExpertModuleSearchDaemon.plist. Delete the sketchy files immediately.

Click on the Go menu icon in your Mac’s Finder and select Applications on the list.

Find the entry for AppQuest or another app that clearly doesn’t belong there and move it to the Trash. If this action requires your admin password for confirmation, go ahead and enter it.

Expand the Apple menu and select System Preferences.


Proceed to Users & Groups and click on the Login Items tab.


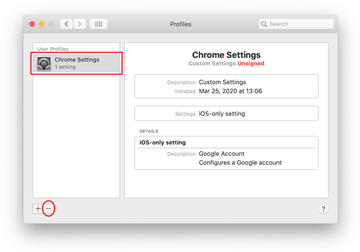
Now select Profiles under System Preferences. Look for a malicious item in the left-hand sidebar. Several examples of configuration profiles created by Mac adware include TechSignalSearch, MainSearchPlatform, AdminPrefs, and Chrome Settings. Select the offending entity and click on the minus sign at the bottom to eliminate it.

Restore files encrypted by EvilQuest Mac ransomware
The only way to get your data back is to restore it from a previously made backup. Since EvilQuest acts as a wiper rather than a classic Mac ransom Trojan, paying the ransom isn’t going to get you anywhere with your recovery efforts. Therefore, if you have been prudent enough to maintain backups of your important files, the following steps will help you out in this regard:
- Expand the Go pull-down menu in your Finder and select Utilities.
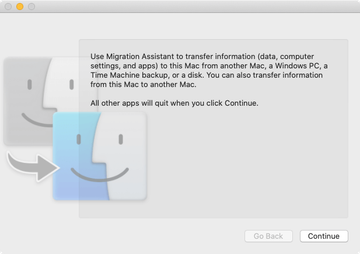
- Find Migration Assistant and double-click on it.
- Click Continue.
- A follow-up screen will ask how you’d like to transfer your information. Select the option that says “From a Mac, Time Machine backup, or startup disk” and click Continue.
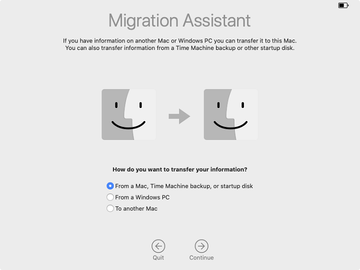
- Select the appropriate Time Machine backup you previously made and click Continue once again.

- Specify what information you want to transfer and hit Continue to start the process. Be advised it may take hours, depending on the amount of data being restored. So, be patient and take your time – the result is worth it. You will regain access to your valuable files.
It’s important to keep in mind that you should only get down to file recovery after the EvilQuest ransomware has been completely eradicated from your Mac. Otherwise, the malicious application will re-encrypt your data. In case the above manual removal steps weren’t effective enough, proceed to the following section to purge the threat for good.
Get rid of EvilQuest ransomware using Combo Cleaner removal tool
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove EvilQuest virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the EvilQuest issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run the update of malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove EvilQuest threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, data recovery is still on your to-do list. Resort to the previous section of this tutorial to get your files back – as long as you have been making backups with Time Machine.