With the MetroPremium Mac adware wave gearing up for a rise, it’s important to know how the unwanted app affects computers and how to remove it for good.
A new highly prolific adware family is shaping up to be a serious player on the Mac cybercrime arena. The ambitious operators of this campaign have been releasing several PUAs (potentially unwanted applications) at a time since mid-October 2019. More disconcertingly, there is a clear upward trend in the wicked developers’ productivity. Obviously, there has to be a motivation behind such a boom. What is it? To get the big picture, let’s take a close look at the app called MetroPremium (also referred to as MetroPremium.app or Metro Premium), one of the recent spinoffs of this growing lineage. Putting the unique name aside, it is a clone of a series of Mac adware samples discovered in the past couple of weeks, including DefaultProducts and IdeaShared. The evident common denominator across these app instances is that they all have a version number of 1.0 indicated next to their names in the infected Mac’s Applications folder. Another shared feature is the round green icon featuring an image of a magnifying glass inside.
In terms of the claimed functionality, MetroPremium 1.0 takes after all of its replicas as well. The respective browser extension is supposedly intended to improve the way the user looks up information on the Internet by reducing search times and delivering refined results via proprietary algorithms. This feature set turns out to be a dummy, though. Instead of introducing online experience enhancements, the adware imposes changes of personalized settings in Safari, Chrome, and Firefox on the plagued Mac. The worst part of this tampering is that the modifications are made without the victim’s approval or even awareness. This way, MetroPremium redirects a major portion of the web traffic to junk search engines, with the process of this hijack involving intermediary ad networks that aren’t discernibly resolved in the browser but, technically, still receive hits from the contaminated computers.
Metro Premium virus may re-infect your Mac multiple times unless you delete all of its fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.Unsolicited forwarding of one’s web browser to worthless search engines with ads above the fold isn’t the most disturbing symptom of MetroPremium 1.0 virus activity. A much more obnoxious effect is that the victim will be occasionally rerouted to sites hosting aggressive popup alerts. These landing pages can be anything from tech support scams to pesky hoaxes that push rogue system utilities under the guise of “must-have” cleaners. The scare theme is usually fueled by fake Mac virus detection reports or messages about critical privacy risks. Essentially, this is an extra layer of attack monetization aiming to cross-promote affiliated malicious software. Furthermore, these warning notifications are problematic to get out of the way by simply closing the browser tabs. In many cases, the only way to get rid of them is to force quit and restart the browser, which makes the predicament yet more annoying.
Ads by MetroPremium are additional elements of this nasty campaign. They come in the form of in-text links, comparison shopping areas, banners showcasing coupons and freebies, as well as interstitial adverts popping up beyond the current browser window. Not only do these items slow down the affected web browser to a crawl when a certain amount of them is reached, but they also keep the users from enjoying their favorite sites as large parts of the page layout end up being overcast by redundant ecommerce content.
On a side note, there are several adware programs hailing from the exact same source and making the rounds concurrently with MetroPremium 1.0. Again, these dodgy apps are strikingly similar on the outside and act in basically the same way. They may even replace each other on an already-infected Mac, displaying a popup that says “Installation Complete” every time this happens. The simultaneous circulation of multiple PUAs representing the same genealogy is a hallmark sign of this particular Mac malware wave. Here is a quick overview of the MetroPremium app look-alikes in question:
LookupShare
LookupShare, also manifesting itself as LookupShare.app, is a piece of adware that installs itself onto a Mac without the user’s permission and alters custom settings in Safari, Chrome, or Firefox. It causes a number of adverse effects that diminish the user experience and impact the performance of the default web browser. In particular, LookupShare substitutes the user’s preferred search engine setting with Bing, Yahoo, or fake search service backed by low-quality advertising networks. The infection tends to additionally display unwanted ads on regular websites that include no sponsored materials if visited from a healthy computer.
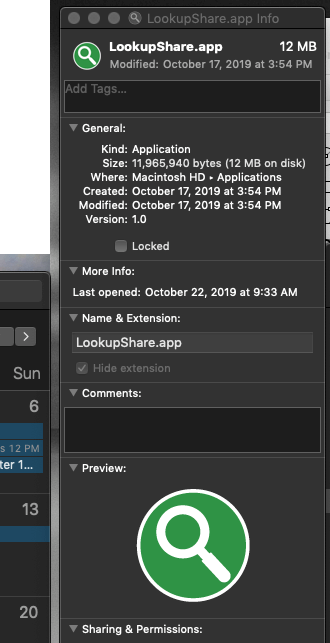
In order to serve targeted ads, LookupShare collects PII (personally identifiable information) as the victim is surfing the web. These details include browsing history, bookmarked sites, and quite possibly, even usernames and passwords for online accounts. The privacy issues caused by this adware, combined with a defiant interference with normal Internet navigation, are the reasons substantial enough to get rid of the threat without delay.
MetroPremium app manual removal for Mac
The steps listed below will walk you through the removal of this malicious application. Be sure to follow the instructions in the order specified.
1. Open up the Utilities folder as shown below
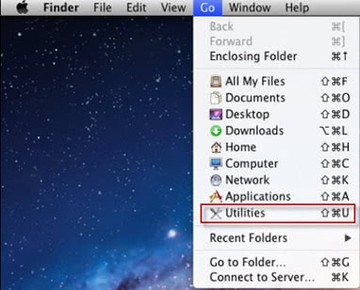
2. Locate the Activity Monitor icon on the screen and double-click on it
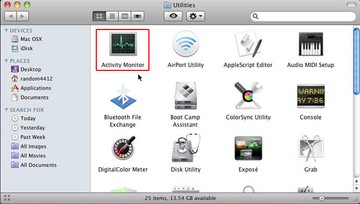
3. Under Activity Monitor, find a process named MetroPremium, IdeaShared, ForwardOpen or another one that appears to be suspicious, select it and click Quit Process
4. A dialog should pop up, asking if you are sure you would like to quit the troublemaking process. Select the Force Quit option
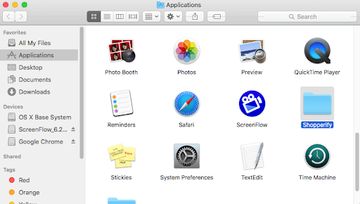
5. Click the Go button again, but this time select Applications on the list. Locate Metro Premium (MetroPremium 1.0) entry on the interface, right-click on it and select Move to Trash. If user password is required, go ahead and enter it
6. Now go to Apple Menu and pick the System Preferences option
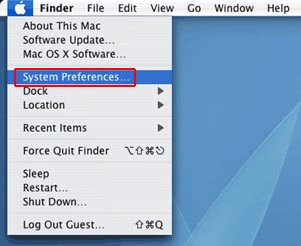
7. Select Accounts and click the Login Items button. The system will come up with the list of the items that launch when the box is started up. Find IdeaShared, ForwardOpen, SafeFinder or other potentially unwanted app there and click on the “-“ button
Get rid of MetroPremium redirects in web browser on Mac
To begin with, settings for the web browser that got hit by this virus should be restored to their default values. The overview of steps for this procedure is as follows:
- Reset Safari
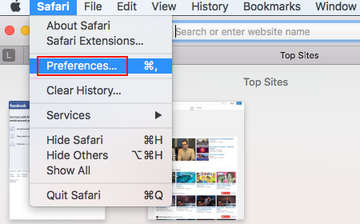
- Open the browser and go to Safari menu. Select Preferences in the drop-down list
- Once the Preferences screen appears, hit the Privacy tab at the top. Find the option that says Remove All Website Data and click on it
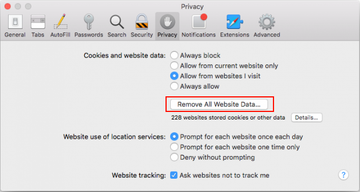
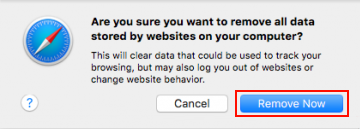
- The system will display a confirmation dialog that also includes a brief description of what the reset does. Specifically, you may be logged out of some services and encounter other changes of website behavior after the procedure. If you’re okay with that, go ahead and click the Remove Now button
- In order to selectively clear data generated by certain websites only, not all of them, hit the Details button under the Privacy section of Safari Preferences

- This feature will list all websites that have stored potentially sensitive data, including cache and cookies. Select the one, or ones, that might be causing trouble and click the appropriate button at the bottom (Remove or Remove All). Click the Done button to exit.
- Open the browser and go to Safari menu. Select Preferences in the drop-down list
- Reset Google Chrome
- Open Chrome, click the More (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down
- When on the Settings pane, select Advanced
- Scroll down to the Reset settings section. Under the Restore settings to their original defaults option, click the Reset settings button
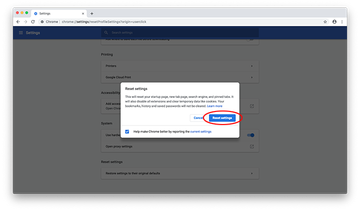
- Confirm the Chrome reset on a dialog that will pop up. When the procedure is completed, relaunch the browser and check it for malware activity.
- Reset Mozilla Firefox
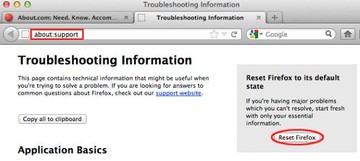
- Open Firefox and select Help – Troubleshooting Information
- On the page that opened, click the Reset Firefox button
Get rid of IdeaShared virus using Combo Cleaner automatic removal tool
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove Metro Premium virus virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the Metro Premium virus issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove Metro Premium virus threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.
