The Chromium virus on Mac is a benign thing turned upside down, where cybercriminals equip the open-source web browser with intrusive adware plugins.
Update:
Skewing the way regular software acts is on most malware authors’ wish list. This way, they can successfully peddle booby-trapped apps while passing them off as something legitimate, which certainly increases the odds of users installing the troublemaking entities. The distribution of the Chromium browser injected with aggressive helper objects has been the talk of the town lately. This issue stands out from the Mac malware crowd as it involves a harmless piece of software weaponized by crooks. For those uninitiated, Chromium is an open-source project that gave birth to Google Chrome and currently allows anybody to create their web browser build with specific preferences hard-coded in it. The attackers have perpetrated a campaign where they spread a Mac variant of Chromium equipped with add-ons that exhibit adverse functionality.
The rogue editions of Chromium may look identical to its better-known reputable Chrome counterpart, so the average Mac user is unlikely to notice anything suspicious about it from the start. The tip of the iceberg is a smooth-performing and intuitive Internet navigation instrument. It’s not until the victim gives the browser a shot for a while that they will realize the crucial difference on the inside. The Chromium virus keeps forwarding the web traffic to some predefined site, such as Yahoo! search. Furthermore, the meddlesome app is set as the default browser on the host Mac without proper permission. The irritating redirects will be invoked every time the user launches the browser or tries to look up random information online. To top it all off, the invasive plugin will be added to Safari, Firefox and the genuine Chrome so that the rerouting activity affects them as well.
As a brief recap on the above, the telltale signals of the Chromium virus presence on a Mac include the rogue browser being set as the default one, and the constant Internet traffic redirects to a web page the victim never opted for, most likely Yahoo! or a more exotic pseudo search provider like TapuFind. But how does the unannounced code install itself on a Mac. Those infected can’t recall agreeing to any changes in their web surfing routine prior to the predicament. The trespass is more subtle than that, which explains the unawareness.
The Chromium virus may re-infect your Mac multiple times unless you delete all of its fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
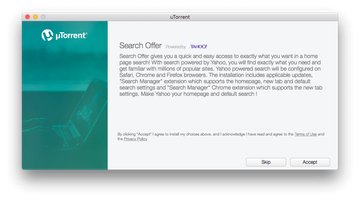
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.The Chromium malware is doing the rounds through bundling. This is a popular software installation mechanism that results in extra items landing onto a computer rather than one that’s clearly indicated. The typical workflow engages multi-element setup wizards for freeware, such as uTorrent clients, media players, streaming video downloaders and the like. The advanced install option mentions that the “Chromium browser powered by Yahoo!” will be installed, and said search engine will become the priority one on other browsers. It’s too bad that people hardly ever opt out of the quick setup, which doesn’t provide any such details. Note that the persistent extension pushed along the way is called “Search Manager” or simply “Management”.
The overhaul of one’s browsing preferences is the “main act”, but there is also a wicked “side show” hidden in plain sight. All the different spinoffs of the Chromium virus zero in on their victims’ private data. The scope of this reconnaissance extends further than search keywords, visited web pages, and the IP address, although these are the only details harvested by the majority of mainstream adware samples. The harmful extension under scrutiny can additionally retrieve the plagued Mac user’s geolocation data, furtively make screenshots, misrepresent website content, and manage downloads. In terms of the adverse outcome, this is potentially a more serious problem than redirects occurring in a web browser. With such an amount of confidential info and control at their disposal, the malware operators are able to orchestrate highly effective spear-phishing attacks, cause harmful downloads behind a victim’s back, steal personal secrets, and inject booby-trapped links or intrusive ads amidst the original materials shown visited sites.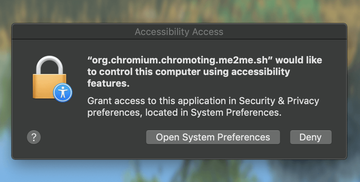
Note that newer versions of this infection make recurrent attempts to get their privileges escalated in a host system via a very unusual trick. Every time a victim logs onto their Mac, they see an Accessibility Access popup alert that says, “org.chromium.chromoting.me2me.sh would like to control this computer using accessibility features.” If the ‘Deny’ button is clicked on this dialog, the same annoying message will show up during the next logon. The troubling thing is that org.chromium.chromoting.me2me.sh is a shell script constituting the Chrome Remote Desktop tool by Google. In other words, the Chromium virus has evolved to the point where its distributors try to hoodwink the infected Mac users into granting remote access to their computers. If you are experiencing a combo of these issues on Mac, it’s about time you performed a thorough cleanup to get rid of the Chromium virus and undo the browser tweaking it caused along with sneaky data harvesting.
Chromium virus manual removal for Mac
The steps listed below will walk you through the removal of this potentially unwanted application. Be sure to follow the instructions in the order specified.
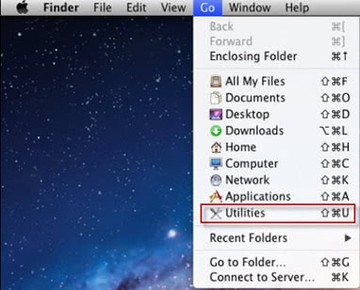
- Open up the Utilities folder as shown below
- Locate the Activity Monitor icon on the screen and double-click on it
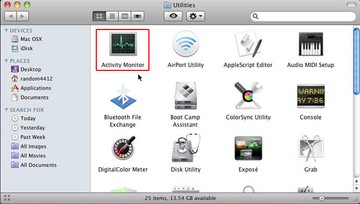
- Under Activity Monitor, find the entries for Chromium and Chromium Helper, select them one by one and click Quit Process each time
- A dialog should pop up, asking if you are sure you would like to quit the Chromium and Chromium Helper executables. Select the Force Quit option
- Expand the Go menu in Apple Finder and select Go to Folder
- Type or paste the following string in the folder search dialog: /Library/LaunchAgents
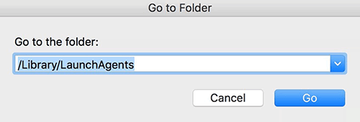
- Once the LaunchAgents directory directory opens up, find the following entry in it and move it to the Trash:
- org.chromium.Chromium.plist
- org.chromium.chromoting.plist
- Use the Go to Folder lookup feature again to navigate to the folder named ~/Library/LaunchAgents. When this path opens, look for the same entry (see above) and send it to the Trash
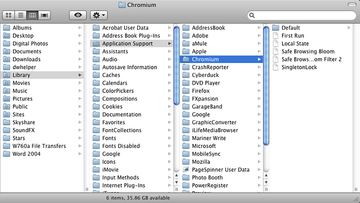
- Similarly, go to the ~Library/Application Support folder. Locate and move the following entry to the Trash:
- Chromium
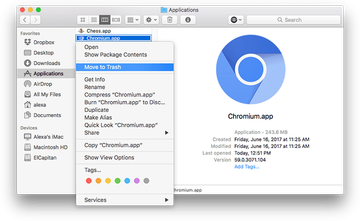
- Click the Go button again, but this time select Applications on the list. Find the entry for Chromium.app on the interface, right-click on it and select Move to Trash. If user password is required, go ahead and enter it
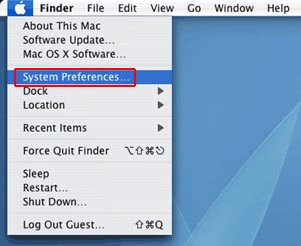
- Now go to Apple Menu and pick the System Preferences option
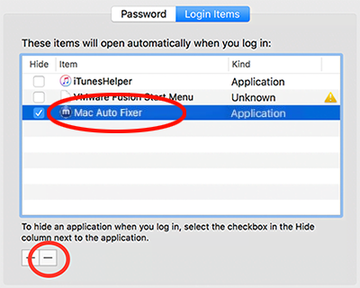
- Select Accounts and click the Login Items button. The system will come up with the list of the items that launch when the box is started up. Locate Chromium, runChmm, or org.chromium.chromoting.me2me.sh there and click on the “-“ button
Get rid of Chromium virus in web browser on Mac
To begin with, the web browser settings taken over by the Chromium virus should be restored to their default values. Although this will clear most of your customizations, web surfing history, and all temporary data stored by websites, the malicious interference should be terminated likewise. The overview of the steps for completing this procedure is as follows:
- Remove Chromium virus from Safari
Open the browser and go to Safari menu. Select Preferences in the drop-down list.

Once the Preferences screen appears, click on the Advanced tab and enable the option saying “Show Develop menu in menu bar”.

Now that the Develop entry has been added to the Safari menu, expand it and click on Empty Caches.

Now select History in the Safari menu and click on Clear History in the drop-down list.

Safari will display a dialog asking you to specify the period of time this action will apply to. Select all history to ensure a maximum effect. Click on the Clear History button to confirm and exit.

Go back to the Safari Preferences and hit the Privacy tab at the top. Find the option that says Manage Website Data and click on it.

The browser will display a follow-up screen listing the websites that have stored data about your Internet activities. This dialog additionally includes a brief description of what the removal does: you may be logged out of some services and encounter other changes of website behavior after the procedure. If you’re okay with that, go ahead and click on the Remove All button.

Restart Safari
- Remove Chromium in Google Chrome
Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down

When on the Settings pane, select Advanced
Scroll down to the Reset settings section.

Confirm the Chrome reset on a dialog that will pop up. When the procedure is completed, relaunch the browser and check it for malware activity.

- Remove Chromium from Mozilla Firefox
Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).


When on the Troubleshooting Information screen, click on the Refresh Firefox button.

Confirm the intended changes and restart Firefox.
Get rid of Chromium virus Mac using Combo Cleaner removal tool
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove Chromium virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the Chromium issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove Chromium threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.
FAQ
What is Chromium and why is it on my Mac?
Chromium is an open-source browser that became the basis for Google Chrome, the world’s leading web surfing solution. It is absolutely benign and boasts plenty of successful use cases. The extensive customization potential makes Chromium similar to a construction kit allowing developers to create custom browsing tools. Some of these may come with hard-coded features and pre-installed extensions under the hood. This explains why there are numerous knockoffs in the wild that exhibit malicious characteristics.
Chromium in its pure form isn’t likely to ever end up on your computer unless you wittingly choose to install it for whatever reason, such as to give its minimalist interface a shot or to try your hand at coding. These are marginal scenarios, though. In most cases, users encounter virus-tainted builds of Chromium that infiltrate their Macs without clear authorization and modify Internet navigation settings in other browsers, including Safari, Firefox, and the authentic Chrome. As a result, the victim will be constantly redirected to Yahoo or unwanted web pages stuffed up with ads.
If one of such culprits is running in your system, you probably installed it as part of a bundled setup client for uTorrent, some multimedia utility, or phony Flash Player update. There are instances where users ‘catch’ the infection while thinking that they are installing the genuine Chrome browser – indeed, malware-riddled variants can look very much like the famous progenitor. One way or another, the only right move is to uninstall the Chromium virus and revert to normal web browsing settings.
How do I get rid of Chromium on my MacBook?
If you are dealing with the legit Chromium browser, uninstalling it is as simple as going to the Applications, finding its entry, and sending it to the Trash. Things are much more complicated in case you are faced with a trojanized version of the software. If so, you need to terminate its process (e.g. Chromium Helper, runChmm) in the Activity Monitor first so that it doesn’t tamper with the cleaning workflow.
Then, go to the /Library/LaunchAgents, ~/Library/LaunchAgents, and ~/Library/Application Support folders, find the malicious entries (org.chromium.Chromium.plist, org.chromium.chromoting.plist, Chromium), and delete them. Next, remove Chromium.app, or similar item, from the Applications path as well as the Login Items under System Preferences. And finally, disable the malicious extension called “Search Manager” or “Management” in web browsers on your MacBook and define the correct search engine and homepage preferences.
