Get a comprehensive report on MacDownloader, a Mac OS X virus designed to steal U.S. defense organizations’ secrets via an intricate social engineering tactic.
A group of threat actors, presumably from Iran, have recently launched a cybercrime campaign that zeroes in on individuals representing some of the largest defense organizations based in the United States. A sample of perpetrating code referred to as MacDownloader has been predominantly infecting Mac machines within these institutions. Security analysts investigating these sorts of felonies are accustomed to dealing with high-profile attacks reminiscent of the notorious Stuxnet worm incident back in 2010. In this case, though, things are a bit different, to put it mildly. The breach workflow appears somewhat primitive, which suggests that the adversary is either not professional enough or simply sloppy.
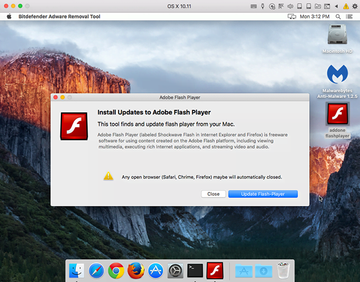
The MacDownloader attack commences with a would-be victim visiting a phishing web page masqueraded as a training course for interns working in the target organizations. The social engineering part revolves around an old-school technique where the user is unable to watch a video on the site. According to a deceptive alert that pops up, the problem has to do with out-of-date Adobe Flash Player. Then, another dialog appears, instructing the user to update the software immediately. At this point, simply clicking the Close button on the box will terminate the MacDownloader compromise. Otherwise, the rogue update will result in further brainwashing.

A new popup triggered if the user hits the Update Flash Player button is a notification that says, “Warning! Please Attention… An adware application found on your Mac OS (iWorm v0.681). This file will be clean in a few seconds.” Note that spelling errors and typos are literally everywhere on the malware’s dialogs. All in all, the detection of a worm that’s claimed to be adware is a huge giveaway. Indeed, why on earth would the genuine Adobe Flash Player report Mac infections? The most likely explanation of this apparent discrepancy is that MacDownloader must have been built as a rogue AV product, but the authors had to adapt its activity to absolutely new objectives and failed to do it properly.
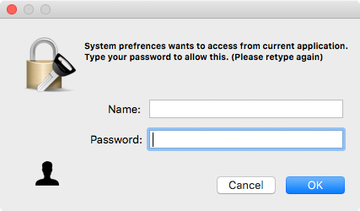
If the OK button is clicked on the spoof adware detection window, the victim will be presented with a new screen that requests their username and password. This is the phishing part in its most explicit form. In the event the user ends up providing their administrative credentials, the MacDownloader virus will be able to access the system’s keychain data and harvest all passwords. It doesn’t take a rocket scientist to predict the ultimate upshot of such activity – the offending program will attempt to transmit the collected information to its Command and Control server. To add insult to injury, it is also capable of downloading arbitrary payloads from the C2 and executing them inside the host Mac OS X machine without authorization. It’s clear that MacDownloader removal should be on a victim’s agenda. The tips below will shed light on the malware cleanup process.
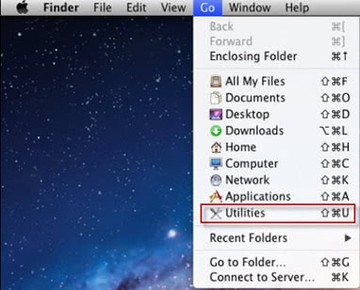
MacDownloader manual removal for Mac
The steps listed below will walk you through the removal of this application. Be sure to follow the instructions in the order specified.
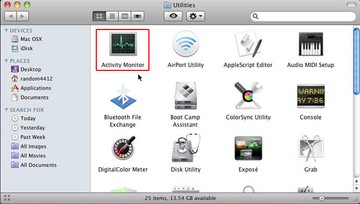
• Open up the Utilities folder as shown below
• Locate the Activity Monitor icon on the screen and double-click on it
• Under Activity Monitor, find the entry for MacDownloader, select it and click Quit Process
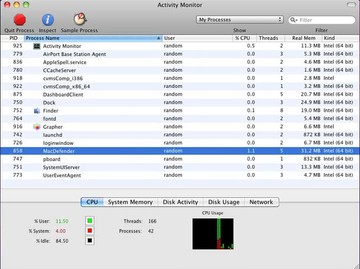
• A dialog should pop up, asking if you are sure you would like to quit the MacDownloader executable. Select the Force Quit option
• Click the Go button again, but this time select Applications on the list. Find the entry for MacDownloader on the interface, right-click on it and select Move to Trash. If user password is required, enter it
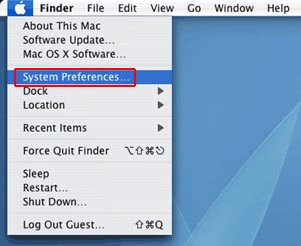
• Now go to Apple Menu and pick the System Preferences option
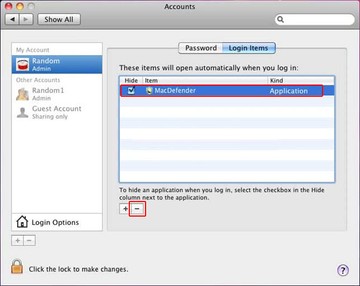
• Select Accounts and click the Login Items button. Mac OS will come up with the list of the items that launch when the box is started up. Locate MacDownloader there and click on the “-“ button
Get rid of MacDownloader using Combo Cleaner automatic removal tool
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove MacDownloader virus virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the MacDownloader virus issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove MacDownloader virus threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.