Find out what kind of issues the iWorm virus causes to an infected Mac and get an effective up-to-date walkthrough to get rid of this infection for good.
First and foremost, iWorm is a type of Mac malware that transforms the infected machines into bots. Figuratively speaking, a contaminated Mac becomes a dumb soldier in a big army of suchlike cyber creatures. The botnet operators can engage these “troops” in large-scale distributed denial of service attacks as well as assaults aimed at brute-forcing other users’ passwords. Of course nobody is willing to become criminals’ accomplice, but the iWorm trojan doesn’t ask for consent when deploying its despicable operations. This pest’s common entry point involves a legit-looking product, such as Adobe Photoshop, Java, or Microsoft Office. Some Mac application repositories online, including The PirateBay, contain virus-tainted installers for these generally trustworthy suites. The setup process in such scenarios promotes extra artifacts that are surreptitiously bundled with the kernel apps. This explains how a great many users fall victim to the baddie in question with no red flags being raised.

After the modified installer has dropped iWorm onto the Mac, the victim will see a dialog box that requests their admin password so that the setup can be completed. As soon as the password is typed in, things start getting out of hand. The trojan drops the com.JavaW.plist file, which configures the host system to run a malicious executable at startup time. Said process then establishes connection with one of the malware’s Command and Control servers. This way, the threat actors can remotely trigger arbitrary commands on the target Mac box. The users may not be aware of this happening. Somewhat higher CPU consumption than usual might be the only giveaway, but people tend to overlook this effect and move on with their day.
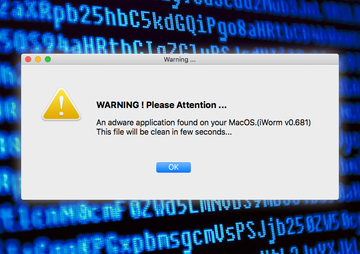
The context of iWorm’s activity has evolved over time. A recent cybercrime model using this infection has to do with another sample of Mac malware called MacDownloader. Analysts are convinced that the latter is run by Iranian hackers. The cybercrime ring behind it has been trying to compromise defense contractors based in the United States. The workflow of the MacDownloader attack involves a spear-phishing page camouflaged as a resource for personnel training. A video on that site appears to be broken and can only be viewed after the visitor updates their Adobe Flash Player to the latest version. The updater, however, installs the malware instead of doing what it’s supposed to.
Then, the MacDownloader virus displays a fake warning that reports an adware application found on the Mac. The name of this rogue threat is iWorm v0.681, where the version number may vary. To get rid of the purported infection, the user is instructed to hand over their admin password. The ultimate goal of the attack is to collect confidential data from plagued Mac workstations. So it turns out that the malefactors may also exploit the notoriety of iWorm to scare people into providing their sensitive credentials. No matter whether you are dealing with the genuine virus or a rogue security app that wrongfully reports it, it’s strongly recommended to get rid of the troublemaking code immediately.
iWorm virus manual removal for Mac
The steps listed below will walk you through the removal of this application. Be sure to follow the instructions in the order specified.
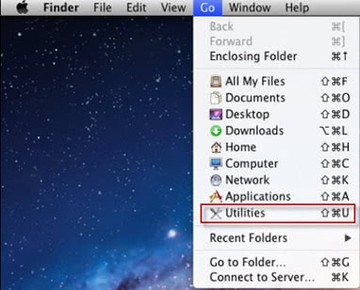
• Open up the Utilities folder as shown below
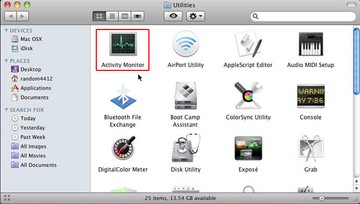
• Locate the Activity Monitor icon on the screen and double-click on it
• Under Activity Monitor, find the entry for JavaW or MacDownloader, select it and click Quit Process
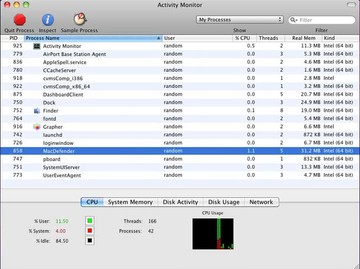
• A dialog should pop up, asking if you are sure you would like to quit the executable. Select the Force Quit option
• Click the Go button again, but this time select Applications on the list. Find the entry for JavaW or MacDownloader on the interface, right-click on it and select Move to Trash. If user password is required, enter it
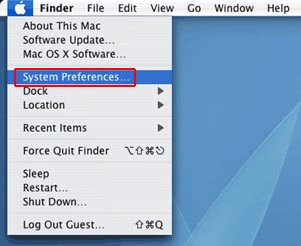
• Now go to Apple Menu and pick the System Preferences option
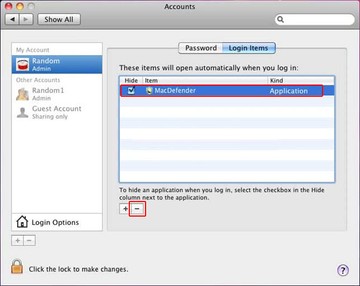
• Select Accounts and click the Login Items button. Mac OS will come up with the list of the items that launch when the box is started up. Locate JavaW or MacDownloader there and click on the “-“ button
Get rid of iWorm using Combo Cleaner automatic removal tool
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove iWorm trojan virus virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the iWorm trojan virus issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove iWorm trojan virus threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.