The rigid control of software and hardware in Apple devices is both an obstacle to exploitation and a way for high-profile threat actors to persevere inside.
The famous walled garden paradigm so nurtured by Apple is a tremendously effective way to keep attackers at bay. It is an isolated and firmly managed environment that prevents unverified apps from being executed on devices, primarily those with iOS on board but increasingly on Macs as well. Allowing only tried-and-tested code to run is an effective tactic, but unfortunately, it could do users a disservice. While fending off mainstream malware, it gives skilled adversaries the advantage of being unimpeded after gaining a foothold in a device.
Why is the walled garden a mixed blessing?
In a recent interview with MIT Technology Review, senior researcher at Citizen Lab Bill Marczak shared his well-founded concerns on this matter. His narrative comes down to the fact that while iPhones are incredibly hard for most crooks to hack, a minuscule number of top cybercriminal gangs will succeed. The paradox is that the walled garden ecosystem will give these attackers an extra layer of protection by keeping white hats from discovering the breach.
Last December, Marczak co-authored a report unveiling an eavesdropping campaign that targeted Al Jazeera journalists via a zero-tap iMessage exploit allegedly created by Israeli private intelligence company NSO Group. This plot was pinpointed not because clear evidence signaled the compromise, but because one of the victims suspected being surveilled and the researchers had to go the extra mile checking web traffic patterns on the iPhone. The breadcrumbs led to NSO Group’s servers.
The M1 chip built into the latest Mac models is largely geared toward the same approach of only allowing pre-approved code to run. But, although a more locked-down territory is a step forward in terms of security, a few Apple Silicon-compatible malware samples have already been spotted in the wild. One is an adware strain called GoSearch22, and the other is a fusion of a backdoor and a malware downloader dubbed Silver Sparrow.
The fundamental dilemma
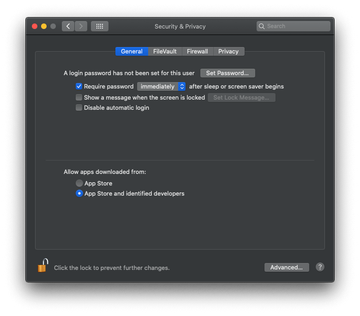
Apple’s tightly regulated digital environment has its downsides. A major one is that it hampers security analysts’ efforts by blocking their tools from scrutinizing sensitive system areas that are often parasitized by harmful programs. With some competently tailored malicious apps taking a file-less infection route, the only way to detect them is to analyze memory. At that point, though, all security endeavors stop.
Some experts argue that one of the ways of solving this puzzle is to give users the prerogative of deciding whether a trusted security professional can check their device for signs of compromise. But again, there is a roadblock. Cybercriminals are adept at social engineering, and there is a risk of duping users into making wrong choices.
By and large, compared to the security flaws of an open platform, the shortcomings of the walled garden framework are probably the lesser of two evils. But going forward, there are lots of improvements to make.
