Gatekeeper, the technology that’s meant to protect Macs against malware, could expose users’ personal data due to a questionably safe data transfer mechanism.
Apple’s terrific track record of keeping macOS safe from malicious apps is a double-edged sword. Recent findings of security enthusiasts about a Gatekeeper quirk demonstrate that the trade-off between security and privacy is a nontrivial one. Before elaborating on this issue further, let’s recall what this feature is intended to do in the first place. When a user tries to run an app, it checks the code against a database of known-harmful software. If a match is found, the security module disallows the execution of the dubious entity and triggers an appropriate alert. Whereas this method effectively turns macOS into a territory with a low chance of malware compromise, it has a flip side. The core of the problem is that Gatekeeper transmits app verification-related data over a crudely secured channel.
No encryption, no privacy
To send app samples to Apple’s servers, Gatekeeper leverages a communication channel called the Online Certificate Status Protocol (OCSP). In a global context, this workflow is constantly generating massive amounts of data traveling back and forth. As previously mentioned, the fundamental slip-up is that these interactions aren’t backed by safe encryption practices. Such a loophole could be a source for scenarios in which security and privacy don’t get along.
It’s noteworthy that the data in transit doesn’t include highly sensitive details such as the user’s name, biometric info, or credit card numbers. Nevertheless, the traffic does allow a potential third party to profile the person based on their app usage patterns over time. This is particularly unsettling for individuals who strongly hinge on privacy in their day-to-day activities. For instance, social media influencers, politicians, and investigative journalists could encounter serious issues if surveilled this way.
In the United States, the government has the authority to request and obtain user data from tech companies like Apple. However, with Gatekeeper communications lacking encryption, three-letter agencies or the military may be able to get a good deal of this information without having to send official requests. The existing traffic monitoring programs can pinpoint such data as it flows through the infrastructures of ISPs.
Gatekeeper to become more secure. And optional
Apple has replied to these concerns with a few soothing claims. First off, it has stated that there was no overlapping of Gatekeeper-borne app verification data with information about users or specific devices. Secondly, the company is planning to implement a new encrypted protocol to safeguard this traffic.
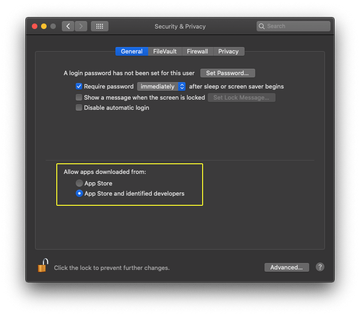
Perhaps the biggest game-changing future move is to allow users to disable the defenses if they so desire – at their own risk, obviously. Essentially, this change will make Mac computers more susceptible to malware attacks while adding an extra layer of privacy and freedom to one’s activities. When the shift takes place, prioritizing one thing over another will be up to the user.
That said, even in its current shape Gatekeeper doesn’t guarantee ultimate security. In October, we covered a Mac malware campaign that successfully tricked this protection module’s notarization checks. As a result, a handful of adware apps representing the OSX/MacOffers family got a seal of approval to run on Macs.
