The latest iOS 14 and iPadOS 14 have arrived with fixes of multiple security vulnerabilities, one of which is categorized as a severe privilege escalation bug.
As expected, Apple released the latest versions of its mobile operating systems, iOS 14.0 and iPadOS 14.0, on September 16, 2020. The big event has brought a series of previously announced perks to the iPhone, iPad, and iPod. These include, among other things, UI improvements, Siri enhancements, and privacy tweaks that limit the use of the microphone, camera, and geolocation by apps.
In addition to a conspicuous facelift of the general user experience, the new operating systems come with important security fixes under the hood. Judging by Apple’s official highlights of the security content in iOS 14 and iPadOS 14, the update includes patches of 11 vulnerabilities. These bugs could be a source for device exploitation scenarios that run the gamut from screen lock failure and kernel memory access, to cross-site scripting (XSS) and arbitrary code execution attacks.

An example of a now-addressed moderately dangerous flaw is a Siri loophole tracked as CVE-2020-9959. It allows anyone who has physical access to an iPhone to read notifications right from the lock screen. Another imperfection documented as CVE-2020-9976 affects the Keyboard feature and could pave a malicious app’s way toward leaking confidential user data. A sandbox issue catalogued as CVE-2020-9968 might allow a rogue app to access restricted files. One more bug on the list, CVE-2020-9946, prevents the screen lock from taking effect after a user-specified period of inactivity.
A vulnerability that stands out from the rest
Out of all the bugs addressed via the recent patches, one imperfection appears to be potentially the most impactful. Flagged as CVE-2020-9992, it is a privilege escalation loophole affecting iPhone 6s and newer models. It is also exploitable on iPad Air 2, iPad mini 4, the seventh-generation iPod Touch, and all later releases of these devices.
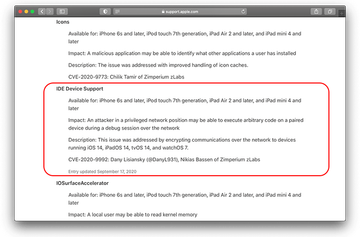
Technically, this flaw stems from a crude implementation of IDE Device Support, a component of Apple’s Xcode development toolkit. According to the patch log mentioned above, an adversary needs to be in a “privileged network position” to piggyback on this weakness. Another prerequisite for executing the attack comes down to social engineering: the threat actor has to convince a victim to open a specially crafted file. One of the ways to do it is by sending a booby-trapped message that either contains the malicious object as an attachment or lures the recipient into tapping a link that leads to the download page.
If these dodgy requirements are met, the hacker could give the vulnerability a go and run arbitrary code on a target mobile device during a debug session. Combined with privilege escalation, which is another byproduct of the bug under scrutiny, this attack vector can fuel exploitation ranging from sensitive information theft to the distribution of iOS malware. Given the stealth of this infection method and the possible consequences, iOS and iPadOS owners should update their devices to the latest version of the operating system.
