This article provides the details of the increasingly widespread iforgot.apple.com phishing scam, dissects its goals, and advises on ways to handle the hoax.
Strong security has always been on the plus side of Macs, and it’s getting increasingly hard for cybercrooks to deposit their harmful payloads onto these computers. The black hats, in their turn, have always been resourceful. If you put two and two together, one of the most effective attack scenarios has to do with manipulating humans rather than machines. This trend is spawning numerous social engineering campaigns, including phishing waves and other forms of email frauds. For instance, the recent iforgot.apple.com scam is currently gearing up for a rise in a defiant attempt to wheedle out Mac users’ sensitive information. The mechanism of deploying this scenario relies on a mass spam activity, where the felons send out thousands of deceptive emails that might resemble a shot in the dark at first sight.
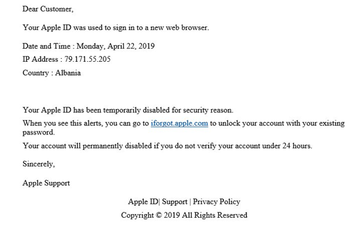
The gist of the fraudulent message is to make the recipient think that their Apple ID has been blocked because it was entered in a new web browser. Moreover, this suspicious event is claimed to have raised an extra red flag because it allegedly took place in a different country, Albania or Russia being most commonly mentioned in the message. For a greater persuasiveness, there is an indication of the purported hacker’s IP address, as well as the date and time of the sign-in. The biggest catch here is that the would-be victim is instructed to follow a link and unlock their credentials; furthermore, their account is stated to be subject to permanent suspension unless this is done within 24 hours. Here’s the full text of the email body:
“Dear Customer,
Your Apple ID was used to sign in to a new web browser.
Date and Time:
IP Address:
Country:
Your Apple ID has been temporarily disabled for security reason.
When you see this alerts, you can go to iforgot.apple.com to unlock your account with your existing password.
Your account will permanently disabled if you do not verify your account under 24 hours.
Sincerely,
Apple Support”
The fundamental tricky element of the hoax is that the embedded link leads to a rogue not legit Apple ID site. On the outside, it looks just like its genuine counterpart and many Mac users probably won’t tell the difference. It’s the URL that’s the main giveaway – it always differs from Apple’s real one. The phony page contains an imitation of authentication fields where the user is supposed to enter their credentials to log in. Once this is done, the victim gets redirected to another page that asks for additional personal details, including their first and last name, date of birth, and address. Obviously, all of this information will end up in the crooks’ hands if filled out.

There are several telltale signs suggesting that this is nothing but a scam. Firstly, Apple would address users by their name rather than with a phrase “Dear Customer”. Secondly, a deadline to do something otherwise the account will be disabled doesn’t align with the company’s practices. Furthermore, there is a grammar error in the wording, namely the part that says, “Your account will permanently disabled”. Apple wouldn’t send any messages written so carelessly. And again, yet another giveaway is the URL of the linked-to web page – it’s not really iforgot.apple.com, although the anchor text is correct.
The iforgot.apple.com scam may re-infect your Mac multiple times unless you delete all of its fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.There is one more facet of the iforgot.apple.com scam that’s quite disconcerting. It’s about the way the ill-minded operators of the campaign might have obtained one’s email address. It’s within the realms of possibility that the black hats are taking advantage of information from a massive dump of Mac users’ contact details. Therefore, a recipient might have fallen victim to credentials theft in the past, and this could be a malware predicament. There are Trojans that infect computers and perform reconnaissance on it, gathering different types of the plagued users’ information. These culprits are furtive enough to stay inside the system for months or even years without exhibiting any conspicuous symptoms, so it definitely makes sense to ascertain that there is no identity stealing malware on board. The steps below will help check your Mac for such threats. Another important point is to refrain from clicking any links in the iforgot.apple.com scam emails. Stay safe and exercise caution with dubious messages in your inbox.
Get rid of iforgot.apple.com scam virus using Combo Cleaner removal tool
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove The iforgot.apple.com scam virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the The iforgot.apple.com scam issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove The iforgot.apple.com scam threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.