QSearch virus removal from Mac is a must-do because it takes over web browsers to redirect the traffic to a social search service the victims didn’t ask for.
Update:
What is QSearch virus?
Even the users who think they are security-minded might have some hard time differentiating benign applications from malicious ones these days. That’s because cybercrime has become hybrid over time, and the borderline between the digital black and white is really blurred. As a result, people are facing a slew of apps from the “gray area” that don’t cause much, if any, damage but make the user experience go down the drain. QSearch is an example of such a controversy. It is a web solution that claims to bridge the gap in Facebook Timeline search, something that the social media giant in question has yet to provide. As is the case with many sketchy services out there, the idea is interesting but the implementation leaves plenty of questions unanswered.
Intrusive promotion practices
The caveat regarding QSearch is that Mac users may be recurrently redirected to its site. This forwarding of Internet traffic takes place beyond the permission of whoever is infected, which is a red flag indicating a security concern. The causality for this unfortunate turn of events involves a browser extension that supports Safari, Chrome, and Firefox. Once embedded in the victim’s preferred Internet surfing tool, the add-on twists the custom settings and may trigger a JavaScript-powered routine that leads to a reorientation of the browsing patterns. The hijacked homepage, default search engine and new tab page therefore resolve the wrong site, such as qsearch.cc or analytics.qsearch.cc, whenever the user opens the browser, tries to look up some arbitrary information, and loads a new page within the current window. To top it off, the redirect activity may also occur at random or accompany innocuous mouse clicks anywhere on any websites. It’s likely that annoying ads will be displayed as part of this complex electronic intrusion as well.
QSearch may re-infect your Mac multiple times unless you delete all of its fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.The landing page itself does not pose any significant risk to the victim, which is some good news. It simply advertises the core service and encourages the users to sign up and start their free trial to check out how the Timeline scouring works. One additional catch is that QSearch purportedly allows singling out trending topics on social media and goes equipped with a dashboard visualizing this data, which might be of interest to businesses. However, this whole toolkit in the app’s portfolio is overshadowed by the questionably ethical marketing tactics behind it.
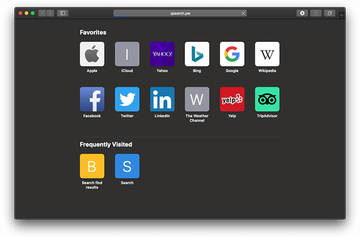
Browser redirects via qsearch.pw
Aside from the above relatively mild impact staying on a slim margin between legitimacy and outright fraud, this infection bares its fangs in a much more frustrating way. It can redirect the victim’s web browser to qsearch.pw website which, in turn, opens Bing or Yahoo after flinging the web traffic through a series of intermediate domains. These transitional pages are run by advertising platforms that buy and sell unique user hits without paying heed to the way these leads are provided. Although the resulting site in this particular redirect scenario is a popular search engine whose reputation isn’t tainted by dubious promotion, the operators of QSearch virus use it as a cover for unethical monetization of their foothold in the infected Mac. In some cases, qsearch.pw web page leads to services that are undoubtedly malicious, such as SearchMine. This cocktail of adverse properties turns the threat into a driving force of different notorious malvertising campaigns.
Qsearch.com spinoff displaying fake virus alerts
Another variant of this virus uses qsearch.com landing page instead. This one impersonates an official Apple support resource and focuses on hoodwinking Mac users into downloading and installing a piece of scareware. It says, “Your system is infected with 3 viruses” and triggers an extra popup saying that a Trojan called e.tre456_worm_osx has been detected on the computer. The pseudo-repair process presupposes that the victim opts for an online scan for threats. The scan report will list several more imaginary viruses, emphasizing that the only cleanup method is to use the “recommended” tool, which is a fake security app in disguise.
QSearch distribution schemes
The most probable way that the QSearch virus ends up on a Mac computer is through bundles. In plain words, this is a technique that co-promotes shady items along with regular software. The odds of falling victim to the scheme increase in free application installation scenarios. While believing they are getting one harmless program that doesn’t require any subscription fees, the users may click on and on until they unwittingly allow the culprit to get inside. Therefore, it’s always recommended to choose custom install over the express option – this will disclose the presence of the bundled objects in the package.
When it comes to the top driving force of QSearch malware distribution, it borrows a page from the playbook of the nastiest adware threats targeting Mac computers. Its operators cash in on fake Adobe Flash Player update popups. This long-standing hoax involves misleading alerts shown on a plethora of hacked and malicious web pages. These spoofed notifications try to get users on the hook by stating that the Flash Player version installed on their machines is obsolete and needs a refresh otherwise the online multimedia experience will be incomplete. In the meanwhile, the booby-trapped installer executes the bundled sketchy payload behind the scenes. Anyways, if the QSearch virus is on board your Mac and redirects the browser to unwanted sites, stick with the tips below to get rid of it.
QSearch redirect virus manual removal for Mac
The steps listed below will walk you through the removal of this malicious application. Be sure to follow the instructions in the specified order.
Expand the Go menu in your Mac’s Finder bar and select Utilities as shown below.

Locate the Activity Monitor icon on the Utilities screen and double-click on it.

In the Activity Monitor app, look for QSearch or another process that appears suspicious. To narrow down your search, focus on unfamiliar resource-intensive entries on the list. Keep in mind that its name isn’t necessarily related to the way the threat is manifesting itself, so you’ll need to trust your own judgement. If you pinpoint the culprit, select it and click on the Stop icon in the upper left-hand corner of the screen.

When a follow-up dialog pops up asking if you are sure you want to quit the troublemaking process, select the Force Quit option.

Click on the Go menu icon in the Finder again and select Go to Folder. You can as well use the Command-Shift-G keyboard shortcut.

Type /Library/LaunchAgents in the folder search dialog and click on the Go button.

Examine the contents of the LaunchAgents folder for dubious-looking items. Be advised that the names of files spawned by malware may give no clear clues that they are malicious, so you should look for recently added entities that appear to deviate from the norm.
As an illustration, here are several examples of LaunchAgents related to mainstream Mac infections: com.pcv.hlpramc.plist, com.updater.mcy.plist, com.avickUpd.plist, and com.msp.agent.plist. If you spot files that don’t belong on the list, go ahead and drag them to the Trash.

Use the Go to Folder lookup feature again to navigate to the folder named ~/Library/Application Support (note the tilde symbol prepended to the path).

When the Application Support directory is opened, identify recently generated suspicious folders in it and send them to the Trash. A quick tip is to look for items whose names have nothing to do with Apple products or apps you knowingly installed. A few examples of known-malicious folder names are Quick Mac Booster, IdeaShared, and ProgressMatch.

Enter ~/Library/LaunchAgents string (don’t forget to include the tilde character) in the Go to Folder search area.

The system will display LaunchAgents residing in the current user’s Home directory. Look for dodgy items related to QSearch virus (see logic highlighted in subsections above) and drag the suspects to the Trash.

Type /Library/LaunchDaemons in the Go to Folder search field.

In the LaunchDaemons path, try to pinpoint the files the malware is using for persistence. Several examples of such items cropped by Mac infections are com.pplauncher.plist, com.startup.plist, and com.ExpertModuleSearchDaemon.plist. Delete the sketchy files immediately.

Click on the Go menu icon in your Mac’s Finder and select Applications on the list.

Find QSearch or another app that clearly doesn’t belong there and move it to the Trash. If this action requires your admin password for confirmation, go ahead and enter it.

Expand the Apple menu and select System Preferences.


Proceed to Users & Groups and click on the Login Items tab.


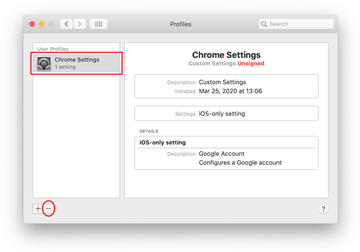
Now select Profiles under System Preferences. Look for a malicious item in the left-hand sidebar. Several examples of configuration profiles created by Mac adware include TechSignalSearch, MainSearchPlatform, AdminPrefs, and Chrome Settings. Select the offending entity and click on the minus sign at the bottom to eliminate it.

Get rid of QSearch virus in web browser on Mac
To begin with, the web browser settings taken over by the QSearch virus should be restored to their default values. Although this will clear most of your customizations, web surfing history, and all temporary data stored by websites, the malicious interference should be terminated likewise. The overview of the steps for completing this procedure is as follows:
- Remove QSearch virus from Safari
Open the browser and go to Safari menu. Select Preferences in the drop-down list.

Once the Preferences screen appears, click on the Advanced tab and enable the option saying “Show Develop menu in menu bar”.

Now that the Develop entry has been added to the Safari menu, expand it and click on Empty Caches.

Now select History in the Safari menu and click on Clear History in the drop-down list.

Safari will display a dialog asking you to specify the period of time this action will apply to. Select all history to ensure a maximum effect. Click on the Clear History button to confirm and exit.

Go back to the Safari Preferences and hit the Privacy tab at the top. Find the option that says Manage Website Data and click on it.

The browser will display a follow-up screen listing the websites that have stored data about your Internet activities. This dialog additionally includes a brief description of what the removal does: you may be logged out of some services and encounter other changes of website behavior after the procedure. If you’re okay with that, go ahead and click on the Remove All button.

Restart Safari
- Remove QSearch in Google Chrome
Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down

When on the Settings pane, select Advanced
Scroll down to the Reset settings section.

Confirm the Chrome reset on a dialog that will pop up. When the procedure is completed, relaunch the browser and check it for malware activity.

- Remove QSearch from Mozilla Firefox
Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).


When on the Troubleshooting Information screen, click on the Refresh Firefox button.

Confirm the intended changes and restart Firefox.
Get rid of QSearch redirect virus Mac using Combo Cleaner removal tool
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove QSearch virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the QSearch issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove QSearch threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.
FAQ
How do I disable QSearch?
QSearch fits the mold of garden-variety Mac adware, which means that disabling it equals completely removing the associated app, browser extension, and files. There is an extra layer of the system tidying, though. To maintain persistence, this threat enrolls a new login item and creates a configuration profile that manages browser behavior. Furthermore, QSearch tends to add an enterprise policy in Google Chrome so that the victim’s web surfing activity follows a rogue pattern specified by the infection. All of these must be removed as well.
To get started on repair, though, you should stop the process used by this malicious app; otherwise it may re-download its components, thereby making your effort futile. Open the Activity Monitor, pinpoint the executable named QSearch or another one you don’t recognize, and force quit it. Then, check the LaunchAgents, LaunchDaemons, and ApplicationSupport directories for suspicious items and send them to the Trash once found. To overcome the persistence tricks mentioned above, head to Users & Groups and Profiles under System Preferences and delete unwanted entries spawned by the pest.
Finally, open the affected web browser and disable the QSearch extension. If it’s not listed there, go ahead and reset the browser’s settings to their original defaults. At this point, all that’s left to do is customize the homepage, search engine, and new tab page so that the browser loads the right services when you need them.
