Learn how to remove Search It Now Mac virus and stop browser redirects to searchitnow.info via goto-searchitnow.global.ssl.fastly.net transit domain.
Update:
Search It Now, also known as SearchItNow, is a malware sample that affects Mac computers and redirects a victim’s web browser to searchitnow.info. This unwanted activity is primarily aimed at endorsing ecommerce services with poor reputation. A few of these opportunistic resources are Alpha Shoppers at alphashoppers.co, mybrowser-search.com, and the searchnewworld.com site – all are replicas of popular search providers. The redistribution of illicitly seized Internet traffic is performed with involvement of an intermediary online spot, the goto-searchitnow.global.ssl.fastly.net domain. Although the infected users can see the latter appear in their URL bar for only about a second when the rerouting process is underway, said auxiliary domain is a critical component of the malware authors’ tactic as it dispatches the pilfered web traffic and may lead to outright harmful sites.
Search It Now may re-infect your Mac multiple times unless you delete all of its fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.Most Mac users experiencing the Search It Now virus issue don’t remember ever installing an extension of that kind and, furthermore, find it really strange that the culprit has enough privileges to make such tangible changes to the browser settings. The trick is, the criminals employ a mechanism referred to as bundling to make sure their junk app proliferates. The catch is as follows: you find a free version of some must-have software online and proceed to the installation. On a side note, the setup wizard is usually hosted at uncertified application repositories that are neither controlled nor approved by Apple. Once the install routine begins, you are prompted to click through the options, with the express (recommended) method being the default one. Unless you dig deeper and go for the custom installation instead, baddies like SearchItNow will get inside.
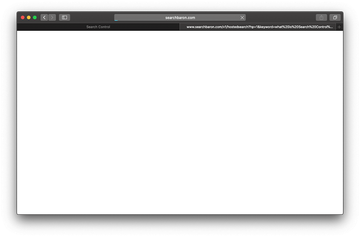
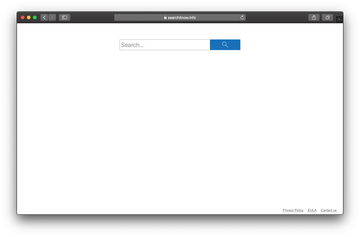
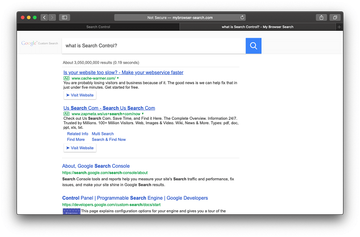
The beauty of this distribution method for the malefactors is that their malicious applet is inadvertently granted high permissions as part of the general terms acceptance for the bundle. This allows it to twist the settings of Safari, Firefox and Chrome and thereby adjust the browsers on infected Mac to its intended misdemeanor. As a result, when opening the browser or trying to look something up on a search engine of choice, you will be forwarded to searchitnow.info. This web page, titled Search Control, has a primitive design with hardly anything in it except the search bar. Any query you enter in there will first reroute the traffic to the above-mentioned goto-searchitnow.global.ssl.fastly.net domain, this URL being appended with a long campaign ID string. The mediator site then invokes another sequence of redirects whose final destination is one of the affiliated pseudo search providers, including Alpha Shoppers (alphashoppers.co).
As of July 2020, the goto-searchitnow.global.ssl.fastly.net dispatching URL has been superseded by searchbaron.com. This tweak gives the whole Searchitnow.info redirect algorithm an overhaul, with a series of extra domains having been added to the mix. These include:
- api.lisumanagerine.club;
- hut.brdtxhea.xyz;
- mybrowser-search.com;
- searchsnow.com;
- search.surfharvest.xyz.
In many cases, Bing is the landing page promoted by the malicious Search Control extension. Although this nuisance is backed by a visible change of the browsing preferences, reverting to correct settings is easier said than done. That’s because the infection manages browser behavior by means of the corresponding Mac configuration profile. A technique to overcome this obstacle will be described further down.
That’s a spiral of traffic forwarding activity that doesn’t seem to end, so the victim is forced to keep closing the wrong web pages off and on. The only effective fix is to find all components of the Search It Now Mac virus, delete them, and revert to normal browser settings. The following steps have been tailored to streamline this malware cleanup workflow.
Search It Now virus manual removal for Mac
The steps listed below will walk you through the removal of this malicious application. Be sure to follow the instructions in the specified order.
Expand the Go menu in your Mac’s Finder bar and select Utilities as shown below.

Locate the Activity Monitor icon on the Utilities screen and double-click on it.

In the Activity Monitor app, look for Search It Now (SearchItNow) or another process that appears suspicious. To narrow down your search, focus on unfamiliar resource-intensive entries on the list. Keep in mind that its name isn’t necessarily related to the way the threat is manifesting itself, so you’ll need to trust your own judgement. If you pinpoint the culprit, select it and click on the Stop icon in the upper left-hand corner of the screen.

When a follow-up dialog pops up asking if you are sure you want to quit the troublemaking process, select the Force Quit option.

Click on the Go menu icon in the Finder again and select Go to Folder. You can as well use the Command-Shift-G keyboard shortcut.

Type /Library/LaunchAgents in the folder search dialog and click on the Go button.

Examine the contents of the LaunchAgents folder for dubious-looking items. Be advised that the names of files spawned by malware may give no clear clues that they are malicious, so you should look for recently added entities that appear to deviate from the norm.
As an illustration, here are several examples of LaunchAgents related to mainstream Mac infections: com.pcv.hlpramc.plist, com.updater.mcy.plist, com.avickUpd.plist, and com.msp.agent.plist. If you spot files that don’t belong on the list, go ahead and drag them to the Trash.

Use the Go to Folder lookup feature again to navigate to the folder named ~/Library/Application Support (note the tilde symbol prepended to the path).

When the Application Support directory is opened, identify recently generated suspicious folders in it and send them to the Trash. A quick tip is to look for items whose names have nothing to do with Apple products or apps you knowingly installed. A few examples of known-malicious folder names are LinkBranch, ProgressMatch, SystemSpecial, and IdeaShared..

Enter ~/Library/LaunchAgents string (don’t forget to include the tilde character) in the Go to Folder search area.

The system will display LaunchAgents residing in the current user’s Home directory. Look for dodgy items related to SearchItNow virus (see logic highlighted in subsections above) and drag the suspects to the Trash.

Type /Library/LaunchDaemons in the Go to Folder search field.

In the LaunchDaemons path, try to pinpoint the files the malware is using for persistence. Several examples of such items cropped by Mac infections are com.pplauncher.plist, com.startup.plist, and com.ExpertModuleSearchDaemon.plist. Delete the sketchy files immediately.

Click on the Go menu icon in your Mac’s Finder and select Applications on the list.

Find the entry for an app that clearly doesn’t belong there and move it to the Trash. If this action requires your admin password for confirmation, go ahead and enter it.

Expand the Apple menu and select System Preferences.


Proceed to Users & Groups and click on the Login Items tab.


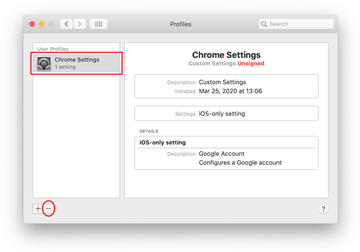
Now select Profiles under System Preferences. Look for a malicious item in the left-hand sidebar. Several examples of configuration profiles created by Mac adware include TechSignalSearch, MainSearchPlatform, AdminPrefs, and Chrome Settings. Select the offending entity and click on the minus sign at the bottom to eliminate it.

Get rid of searchitnow.info redirects in web browser
To begin with, the web browser settings taken over by searchitnow.info virus should be restored to their default values. Although this will clear most of your customizations, web surfing history, and all temporary data stored by websites, the malicious interference should be terminated likewise. The overview of the steps for completing this procedure is as follows:
- Remove searchitnow.info virus from Safari
- Open the browser and go to Safari menu. Select Preferences in the drop-down list

- Once the Preferences screen appears, click on the Advanced tab and enable the option saying “Show Develop menu in menu bar”.

- Now that the Develop entry has been added to the Safari menu, expand it and click on Empty Caches.

- Now select History in the Safari menu and click on Clear History in the drop-down list.

- Safari will display a dialog asking you to specify the period of time this action will apply to. Select all history to ensure a maximum effect. Click on the Clear History button to confirm and exit.

- Go back to the Safari Preferences and hit the Privacy tab at the top. Find the option that says Manage Website Data and click on it.

- The browser will display a follow-up screen listing the websites that have stored data about your Internet activities. This dialog additionally includes a brief description of what the removal does: you may be logged out of some services and encounter other changes of website behavior after the procedure. If you’re okay with that, go ahead and click on the Remove All button.

- Restart Safari
- Open the browser and go to Safari menu. Select Preferences in the drop-down list
- Remove searchitnow.info in Google Chrome
- Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down

- When on the Settings pane, select Advanced
- Scroll down to the Reset settings section.

- Confirm the Chrome reset on a dialog that will pop up. When the procedure is completed, relaunch the browser and check it for malware activity.

- Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down
- Remove SearchItNow from Mozilla Firefox
- Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).


- When on the Troubleshooting Information screen, click on the Refresh Firefox button.

- Confirm the intended changes and restart Firefox.
- Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).
Get rid of Search It Now malware using Combo Cleaner removal tool
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove “Search It Now” Mac virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the “Search It Now” Mac issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove “Search It Now” Mac threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.
FAQ
What is Searchitnow.info Mac?
Also known as “Search Control”, Searchitnow.info is a malicious service involved in a large-scale web hoax that hinges upon traffic reorganization to generate fraudulent revenue. It affects Safari, Google Chrome, and Mozilla Firefox on computers running macOS. The underlying unwanted extension modifies the user-specified preferences so that the browser returns Searchitnow.info instead of the correct defaults. Because the fake engine takes over the most important Internet navigation settings, the victim cannot perform web searches using their provider of choice. The loop of redirects is backed by the infamous searchbaron.com domain, which in turn routes the traffic towards Bing or the dodgy mybrowser-search.com site.
How do I check my MacBook for viruses?
If you notice unwanted changes in the behavior of your Mac and suspect a virus, there are several places to examine for malicious items. For a start, open the list of installed applications (select “Applications” in the “Go” pull-down menu) and check the list for recently added entries you don’t recognize. Another clue of virus activity is a new object showing up on the Login Items list (head to System Preferences and select “Users & Groups” to see it). Some Mac threats additionally create a device profile, which is also accessible from the System Preferences interface (“Profiles” icon). A more advanced way to fulfill the reconnaissance of your own is to inspect the following paths for dubious entities: /Library/LaunchAgents, ~/Library/Launch Agents, ~/Library/LaunchDaemons, and ~/Library/Application Support. This exercise could be a shot in the dark, though, because it’s hard to know for sure whether a specific item is clearly harmful. To ramp up your efforts, consider using an automatic cleaner that will accurately pinpoint every malicious file to make the further removal hassle-free and easy.
What it GOTO search it now?
GOTO search it now (goto-searchitnow.global.ssl.fastly.net, to be precise) is a malicious site that redirects Mac users to Searchitnow.com as part of a browser takeover attack. Its role in this scheme is to redistribute the hijacked web traffic so that it passes through a predefined network of sketchy URLs. It’s worth mentioning that this domain has been recently eclipsed by searchbaron.com, an analogue that forces hits to Bing.com or mybrowser-search.com via api.lisumanagerine.club, search.surfharvest.xyz, or hut.brdtxhea.xyz. All of these pages are auxiliary and only appear in a browser’s status bar for a split second. However, they set one of today’s most massive Mac-specific redirect stratagems in motion.
