Learn how the MacWizz ads virus infiltrates Mac computers and get an effective walkthrough on removing this threat and rectifying mutilated browsing settings.
The predicament where web browsers on Mac are acting up and displaying intrusive advertisements tends to be generally associated with adware. Despite the fact that this type of malicious code isn’t severe and doesn’t cause serious damage, it does not belong on a smoothly functioning system for sure. MacWizz represents this cluster of malicious software. Its activity is restricted to Mac OS X, with the attack surface covering web browsers, including Safari, Chrome and Firefox. The symptoms are easy to tell: whenever the infected user navigates to an arbitrary web page, they stumble upon annoying sponsored elements. These items include popup boxes with various deals in them and large banners hovering over sites’ content. To add insult to injury, the offending applet also affixes underlined clickable hyperlinks to keywords, which point to third-party services.

Yet another instance of impact by the MacWizz virus is interstitial advertising. This is the display of separate browser windows being fired when the victim clicks anywhere within the website they are currently on. It may be difficult to notice this happening, because the transitional ads stay in the background. The process underlying these occurrences has to do with an invisible virtual layer that the adware creates. A distinctive feature of these unwanted browser artifacts is the signature. They may be signed “Ads by MacWizz”, “Powered by MacWizz”, “Brought to you by MacWizz”, or “X by MacWizz”. Therefore, determining the adware name is a no-brainer.
As opposed to regular browser extensions, MacWizz is hardly ever added by Mac users manually. The infected people don’t remember to have ever installed it. But how does it get inside then? The anatomy of this attack boils down to a social engineering technique called bundling. It denotes a mechanism where users unknowingly approve the installation of arbitrary apps, including malicious ones, when installing something absolutely different and harmless. Such compound setup clients typically suggest that users select their preferred installation option, but most people don’t customize this process. Meanwhile, the default setup routine already has a potentially unwanted program or programs under the hood. That’s why safe online practices presuppose that users should choose custom setup instead and untick the extras they don’t trust.
If this infection has ended up inside a Mac through the trickery described above, the victim should realize that ads by MacWizz will keep popping up unless they do something about it. The troublemaking cross-browser add-on must be disabled and sent to trash. The section below explains what exactly should be done and in what sequence.
MacWizz adware manual removal for Mac
To begin with, settings for the web browser that got hit by the MacWizz virus should be restored to their default values. The overview of steps for this procedure is as follows:
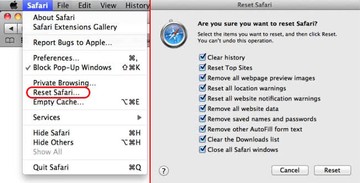
1. Reset Safari
• Open the browser and go to Safari menu. Select Reset Safari in the drop-down list
• Make sure all the boxes are ticked on the interface and hit Reset
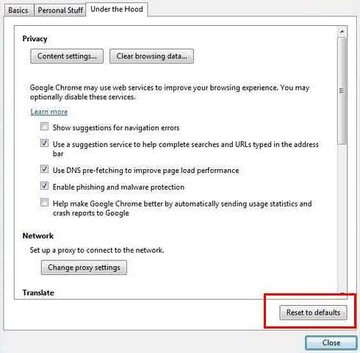
2. Reset Google Chrome
• Open Chrome and click the Customize and Control Google Chrome menu icon
• Select Options for a new window to appear
• Select Under the Hood tab, then click Reset to defaults button
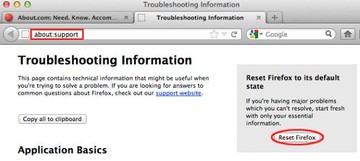
3. Reset Mozilla Firefox
• Open Firefox and select Help – Troubleshooting Information
• On the page that opened, click the Reset Firefox button
Get rid of MacWizz virus using Combo Cleaner automatic removal tool
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove MacWizz ads virus virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the MacWizz ads virus issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove MacWizz ads virus threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.
