Learn how to prevent attackers from hacking your iPhone or MacBook over iMessage and remove the virus if the breach has already taken place.
There has been a great deal of fuss around a new iOS and OS X infection vector over the past few months. In a nutshell, any iPhone, iPad or Apple Watch device running iOS version earlier than 9.3.3 is exposed to behind-the-scenes hacking via iMessage. The same applies to MacBooks with OS X build earlier than El Capitan 10.11.6. So the attack surface is potentially huge. The perpetrators exploit a security flaw in Apple’s Image I/O API to deploy the compromise in the background. This vulnerability catalogued as CVE-2016-4631 enables the malefactors to use a contagious TIFF (Tagged Image File Format) file in order to cause a buffer overflow. This, in its turn, makes it possible to circumvent Apple’s defenses and execute their code on the device in a stealthy fashion.

So, what type of activity should you look out for? The medium for these breaches is an incoming message with a .tif image file in it. By the way, it’s not only iMessage that relies on the vulnerable Image I/O API to render graphics. This characteristic also applies to MMS, Mail and Safari. The iMessage contamination route, though, poses a particularly harmful scenario because it may not necessarily require a would-be victim to actually open the rogue message – instead, the exploitation might well take place without any direct action on the user’s end. That’s the way this app is configured by default. Yet another social engineering trick to perform this attack involves phishing links sent over email, where the user is duped into downloading a malicious payload on the linked-to landing page.
One way or another, a remote hacker can obtain control of the device. These privileges suffice for stealing login and password data and accessing the victim’s personal files such as images, videos and contacts. Furthermore, by getting hold of user’s Apple ID the adversary can log into their iCloud account and leverage the “Find My iPhone” feature to lock the device and then demand a ransom to unlock it, as in the notorious helpappledevice@gmail.com hack. Ultimately, this compromise can cause serious issues, so anyone infected shouldn’t linger with troubleshooting. For a start, it’s recommended to upgrade iOS or OS X to the latest version, where the API vulnerability is patched. Also, be sure to follow safe online practices to avoid the iMessage virus. See the sections below for more information.
Use security software to prevent iPhone hacking via iMessage
Infections like the iMessage virus can obtain your sensitive credentials through unprotected connections. Logging into public Wi-Fi networks and visiting compromised sites can get the gadget exposed to malware and man-in-the-middle attacks. It’s therefore strongly recommended to use automatic protection during web surfing.
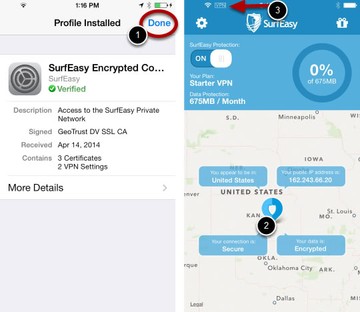
1. Download and install SurfEasy VPN (read review). This app accommodates Wi-Fi security as well as privacy and identity protection features
2. Make sure SurfEasy Protection is turned on throughout Internet browsing sessions. The application will encrypt all traffic, prevent ad tracking, anonymize online activities and secure the iOS device when it’s connected to Wi-Fi hotspots.
Get rid of iMessage virus using Combo Cleaner automatic removal tool
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove iMessage virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the iMessage issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove iMessage threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.
