Remove Tapsnake popup virus from macOS and prevent malicious scripts from running on random websites in Safari, Chrome and Firefox.
Update:
| Threat Profile | |
|---|---|
| Name | Tapsnake popup virus |
| Category | Fake alert, tech support scam, adware |
| Symptoms | Displays fake popup warnings, reports threats that aren’t there, redirects web browser to phony alert pages, affects system performance |
| Distribution Techniques | Fake Adobe Flash Player update popups, malware-riddled application bundles |
| Severity Level | Medium |
| Damage | Unwanted changes of browser preferences, financial losses, privacy issues due to Internet activity tracking, search redirects, ads above the fold |
| Removal | Scan your Mac with Combo Cleaner to detect all files related to the popup virus. Use the tool to remove the infection if found. |
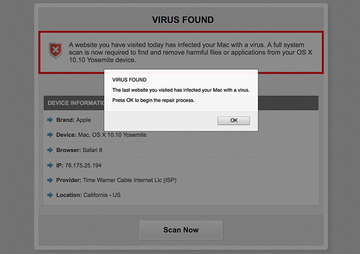
The use of one piece of malware to distribute another is not uncommon in the computer threatscape. The Tapsnake issue exemplifies a tandem like that. Problems begin with an adware sample infiltrating a Mac. It is a low-severity infection that doesn’t pursue any particularly destructive goals, but its role in distributing opportunistic software is crucial. This pest affects the web browsing environment on the system in the following way: it randomly displays popups that say “Download Required” when the victim is visiting regular sites. The alerts insist that the user “download the Mackeeper application to remove Tapsnake” from their Mac. Some of the virus information indicated there includes the risk level (high) as well as the infected file (/os/apps/snake.icv).
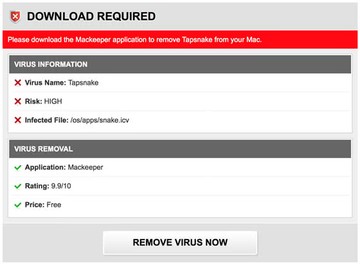
It’s noteworthy that this malvertising campaign underwent a tweak over time to enhance the scare element of the hoax. The new variant of the deceptive alert reports 3 viruses, rather than Tapsnake alone, that allegedly pose risk to the Mac. The list of pseudo threats now includes Tapsnake, CronDNS, and Dubfishicv. In order to pressure the victim further, the following line has been added to the fake warning: “Your Mac is heavily damaged! (33.2%)”. In this scenario, the entry covering the purported location of the infected files looks more detailed, saying: “/os/apps/hidden/os-component/X/snake.icv; /os/local/conf/keyboard/retype.icv”. A slightly modified replica of the alert lists different locations, namely: “/mac/apps/hidden/finder/X/snake.dmg; /mac/local/conf/keyboard/retype.dmg; /mac/remote/conf/services/CronDNS.dmg”.
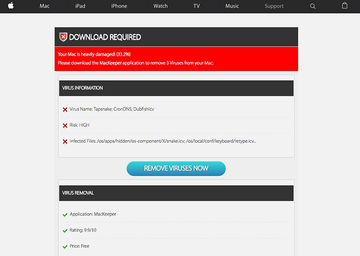
The download recommended in this shady fashion is not a genuine security tool for Mac OS X or newer macOS versions. It’s MacKeeper, a phony Mac system utility that has gained notoriety for its unparalleled vitality and large-scale distribution via multiple concurrent campaigns going on for years. The bogus alerts about the detection of Tapsnake, CronDNS, and Dubfishicv label this controversial app’s rating as 9.9/10 – this should be with the minus sign to align with the actual state of things. All in all, it makes sense breaking this issue down into components. The troublemaker that shows on the early stage of the breach is an adware, whose mission is to hijack the default web browser in order to redirect the traffic and generate misleading popup warnings. Fortunately, this problem is isolated to the browser for the most part, which makes it clear where to start with the fix.
Tapsnake may re-infect your Mac multiple times unless you delete all of its fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.In another twist of this malvertising campaign, the fake Tapsnake virus alerts have started pushing scareware other than MacKeeper. For instance, a redirect hoax forwarding victims to apple.com-guard-device.live and securingchecknow.casa landing pages has been promoting phony utilities called Cleanup My Mac and Mac Heal Pro, respectively. Both are spinoffs of the nasty Advanced Mac Cleaner pseudo optimizer. Just like their progenitor, the sketchy apps report imaginary issues with the system to convince the victim into registering their licensed edition. Overall, this recent wave follows the exact same logic as it used to, except that the harmful programs being distributed may vary.
By clicking the “Remove Virus Now” or “Remove Viruses Now” button on those spoof notifications, the user runs the risk of installing another type of malware. In the better case scenario, a worthless pseudo-antimalware app will end up on the Mac and flood the system with yet more rogue warnings. In summary, these virus alerts do not actually report any real Mac threats – instead, those are ads triggered by a corrupt browser plugin when users go to normal web pages. Consequently, Tapsnake, CronDNS, and Dubfishicv are not the bugs to get rid of. What needs to be removed is the adware that attempts to cause the brainwashing effect.
Tapsnake;CronDNS;Dubfishicv popup virus manual removal for Mac
The steps listed below will walk you through the removal of this malicious application. Be sure to follow the instructions in the specified order.
Expand the Go menu in your Mac’s Finder bar and select Utilities as shown below.

Locate the Activity Monitor icon on the Utilities screen and double-click on it.

In the Activity Monitor app, look for a process that appears suspicious. To narrow down your search, focus on unfamiliar resource-intensive entries on the list such as MacKeeper, Cleanup My Mac, or Mac Heal Pro. Keep in mind that its name isn’t necessarily related to the way the threat is manifesting itself, so you’ll need to trust your own judgement. If you pinpoint the culprit, select it and click on the Stop icon in the upper left-hand corner of the screen.

When a follow-up dialog pops up asking if you are sure you want to quit the troublemaking process, select the Force Quit option.

Click on the Go menu icon in the Finder again and select Go to Folder. You can as well use the Command-Shift-G keyboard shortcut.

Type /Library/LaunchAgents in the folder search dialog and click on the Go button.

Examine the contents of the LaunchAgents folder for dubious-looking items. Be advised that the names of files spawned by malware may give no clear clues that they are malicious, so you should look for recently added entities that appear to deviate from the norm.
As an illustration, here are several examples of LaunchAgents related to mainstream Mac infections: com.mackeeper.MacKeeper.Helper.plist, com.CleanupMyMac.agent.plist, com.CMM.agent.plist, com.CleanupMyMac.cmmhlpr, com.CMM.cmmhlpr, com.MacHealPro.agent.plist, com.MHP.agent.plist, com.MacHealPro.mcphlpr, com.MHP.mcphlpr. If you spot files that don’t belong on the list, go ahead and drag them to the Trash.

Use the Go to Folder lookup feature again to navigate to the folder named ~/Library/Application Support (note the tilde symbol prepended to the path).

When the Application Support directory is opened, identify recently generated suspicious folders in it and send them to the Trash. A quick tip is to look for items whose names have nothing to do with Apple products or apps you knowingly installed. A few examples of known-malicious folder names are MacKeeper, Cleanup My Mac, and Mac Heal Pro.

Enter ~/Library/LaunchAgents string (don’t forget to include the tilde character) in the Go to Folder search area.

The system will display LaunchAgents residing in the current user’s Home directory. Look for dodgy items related to Tapsnake popup virus (see logic highlighted in subsections above) and drag the suspects to the Trash.

Type /Library/LaunchDaemons in the Go to Folder search field.

In the LaunchDaemons path, try to pinpoint the files the malware is using for persistence. Several examples of such items cropped by Mac infections are com.pplauncher.plist, com.startup.plist, and com.ExpertModuleSearchDaemon.plist. Delete the sketchy files immediately.

Click on the Go menu icon in your Mac’s Finder and select Applications on the list.

Find the entry for MacKeeper, Cleanup My Mac, Mac Heal Pro, or another app that clearly doesn’t belong there and move it to the Trash. If this action requires your admin password for confirmation, go ahead and enter it.

Expand the Apple menu and select System Preferences.


Proceed to Users & Groups and click on the Login Items tab.


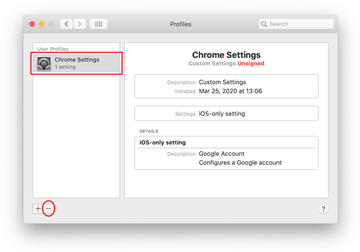
Now select Profiles under System Preferences. Look for a malicious item in the left-hand sidebar. Several examples of configuration profiles created by Mac adware include TechSignalSearch, MainSearchPlatform, AdminPrefs, and Chrome Settings. Select the offending entity and click on the minus sign at the bottom to eliminate it.

Get rid of Tapsnake virus in web browser on Mac
To begin with, the web browser settings taken over by the Tapsnake virus should be restored to their default values. Although this will clear most of your customizations, web surfing history, and all temporary data stored by websites, the malicious interference should be terminated likewise. The overview of the steps for completing this procedure is as follows:
- Remove Tapsnake virus from Safari
Open the browser and go to Safari menu. Select Preferences in the drop-down list.

Once the Preferences screen appears, click on the Advanced tab and enable the option saying “Show Develop menu in menu bar”.

Now that the Develop entry has been added to the Safari menu, expand it and click on Empty Caches.

Now select History in the Safari menu and click on Clear History in the drop-down list.

Safari will display a dialog asking you to specify the period of time this action will apply to. Select all history to ensure a maximum effect. Click on the Clear History button to confirm and exit.

Go back to the Safari Preferences and hit the Privacy tab at the top. Find the option that says Manage Website Data and click on it.

The browser will display a follow-up screen listing the websites that have stored data about your Internet activities. This dialog additionally includes a brief description of what the removal does: you may be logged out of some services and encounter other changes of website behavior after the procedure. If you’re okay with that, go ahead and click on the Remove All button.

Restart Safari
- Remove Tapsnake in Google Chrome
Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down

When on the Settings pane, select Advanced
Scroll down to the Reset settings section.

Confirm the Chrome reset on a dialog that will pop up. When the procedure is completed, relaunch the browser and check it for malware activity.

- Remove Tapsnake from Mozilla Firefox
Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).


When on the Troubleshooting Information screen, click on the Refresh Firefox button.

Confirm the intended changes and restart Firefox.
Get rid of Tapsnake, CronDNS, Dubfishicv virus alerts using Combo Cleaner automatic removal tool
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove Tapsnake virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the Tapsnake issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove Tapsnake threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.
FAQ
Is Tapsnake a real virus on Mac?
Originally, Tapsnake was a primitive strain of spyware targeting mobile devices. It was a booby-trapped version of a once popular game called Snake. When installed, the infection – disguised as a legit fun app – would furtively transmit the victim’s GPS location details to a remote server at predefined intervals. Note that the actual perpetrating program was in the wild almost a decade ago and is no longer in rotation.
The pest’s codename “Tapsnake” was revived by a cybercrime group perpetrating massive malvertising campaigns from around 2015 onwards. Years after the real outbreak, it turned into a scare element of rogue software distribution stratagems. The operators of these hoaxes have been using its name, along with CronDNS and Dubfishicv imaginary threats, to fool Mac users into installing and buying paid versions of scareware applications such as Advanced Mac Cleaner, Mac Keeper, Cleanup My Mac, Mac Heal Pro, and more.
Therefore, the term Tapsnake has got a new incarnation as a pseudo infection listed on deceptive JavaScript-backed popup alerts appearing on hacked or malicious sites. It isn’t a real Mac virus anymore.
What is Tapsnake CronDNS Dubfishicv?
This trio is part of a large-scale malvertising wave aimed at coercing Mac users into installing and purchasing bogus system maintenance and antivirus software. The manipulation is a multi-stage process commencing with a “Download Required” popup warning shown on a malicious or compromised web page. This alert states that a high-risk virus called Tapsnake has been detected on the Mac and tells the user to run a scan and thus get the big picture. The phony Mac scan routine reports additional viruses, namely CronDNS and Dubfishicv, and recommends the victim to install and activate a “cleaner’ that’s scareware in disguise.
Do you need virus protection on a Mac?
There continues to be a great deal of controversy regarding this question, even after the myth about virus-proof Mac has been debunked. Let’s face it: Macs do get infected with quite a few forms of malicious code ranging from low-impact adware to ransomware. Although the system boasts strong defenses overall, the risk of the user unwittingly authorizing some fishy installation always exists and shouldn’t be underestimated. That’s the way a vast majority of Mac infections infiltrate systems these days. A benign-looking freeware bundle plus a lack of vigilance on the user’s end – equals a contamination in many cases.
Given that Mac viruses are here to stay and the cybercriminals’ distribution toolkit is being constantly fine-tuned, virus protection on computers running macOS is an obvious necessity. By using an antivirus tool, you get an extra layer of protection enhancing the built-in security features.
Is the MacKeeper legit?
No, it’s not – that’s the answer that makes the most sense. Although MacKeeper may actually be able to detect some performance, privacy and security issues on a Mac, the unethical spreading tactics and totally exaggerated scan reports are on the minus side of the app making it a fake utility you should avoid.
In regards to the distribution, MacKeeper is backed by a gigantic network of malicious sites that display counterfeit virus detection alerts. It often sneaks into Macs by means of bundling, where the unwanted installer is deliberately kept out of sight. In either scenario, the installation isn’t an outcome of an informed decision.
To top it off, MacKeeper “finds” problems that aren’t there and flags innocuous items as severe ones to pressure the user into coughing up a fee for the “cleanup”. Numerous follow-up notifications in case of nonpayment are a nuisance, too. Regular apps don’t act like this. To recap, this software is too predatory to be considered legit.
Does Apple send virus warnings on Mac?
Apple’s macOS incorporates several security layers that prevent malicious code from running or help eliminate viruses that have already cropped up in a computer. A feature called Gatekeeper blocks malware proactively. It works by thwarting the execution of processes that didn’t pass app Notarization checks.
Another module known as XProtect leverages a classic antivirus technology fueled by malware signatures to pull the plug on known-harmful code or apps that have been modified in a shady way. The macOS Malware Removal Tool (MRT) purges threats that have bypassed other defenses and infiltrated a system.
These protection components may interact with users in a few ways. An example is a popup alert appearing in the following format: “[App name] will damage your computer. You should move it to the Trash”. On a side note, this one has a controversial track record in terms of false positives. Another type of a notification triggered by the operating system says, “macOS cannot verify that this app is free from malware”.
In other words, Apple may alert users to security issues under certain circumstances. But it never sends virus warnings via a web browser. This is the fundamental gap between legit warnings and fake ones. The Tapsnake scam described in this article is isolated to the browser ecosystem and relies on adware that repeatedly redirects the victim to deceptive landing pages that report imaginary infections.
Why do I keep getting a virus warning on my Mac?
It depends on what kind of a warning you are encountering. If it says, “[app name] will damage your computer” or “macOS cannot verify that this app is free from malware”, then you are likely dealing with a real virus scenario and Apple’s automated protection mechanisms are trying to give you a heads up. In this case, sticking to the recommendations in the alert is the best way to err on the side of caution.
On the other hand, if you are being shelled by incessant virus warnings that appear on dubious websites, you are better off browsing away. This is a common tactic used by Mac malware distributors and tech support scammers to hoodwink users into downloading real threats such as rogue optimizers or pseudo-AVs. Adware tailor-made to hijack Safari, Chrome, or Firefox is the top source of these annoying notifications.