- What is the “Hello pervert” scam email?
- Pegasus spyware claims for extra pressure
- Other intimidation techniques in play: Creepy but vanilla
- Check your Mac for malware related to the Pegasus spyware email scam
- Get rid of "Hello pervert" virus in web browser on Mac
- Fix Mac malware issues using Combo Cleaner removal tool
What is the “Hello pervert” scam email?
The themes of email-borne scams have assumed a bevy of conceptual shades over the years. One reason is that these subjects quickly become the talk of the town and most users can identify them easily enough to ignore. Another motivation behind such non-stop tweaks relates to the evasion of secure email gateways (SEGs) that filter known-fraudulent messages. The tactic at the core of a new campaign in massive rotation combines both of the above, plus it adds novel flavors to the whole bitterness. The email begins with an attention-grabbing intro that goes, “Hello pervert”. This, in and of itself, signals a sextortion attempt that pulls the strings with many people due to the delicacy of the matter. While this opening phrase bears a resemblance to quite a few “Hello, my perverted friend” spin-offs, the modus operandi here is much more intricate.
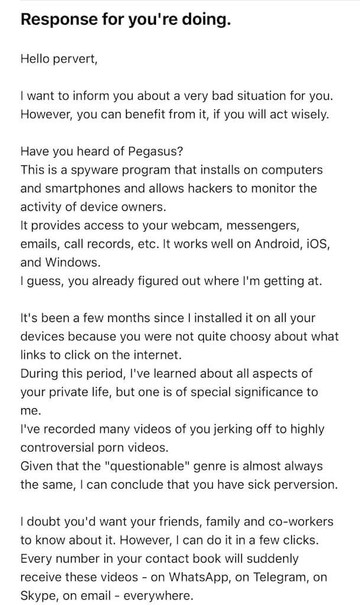
The subject of the message can vary from a weird “Response for you’re doing” (doesn’t sound very English, does it?) to a more accurate “You have been hacked”. Furthermore, the text may include a statement that it has been sent from the recipient’s iCloud email. This particular quirk can point to the notorious email spoofing style of attack that piggybacks on imperfections of the SMTP protocol; or it can as well mean that the email account credentials were leaked to the dark web as a result of an earlier breach. Regardless of the message template, the gist of the con artist’s story has a common denominator: they claim to have footage of the victim watching NSFW stuff, including a video furtively taken by the device’s webcam and the materials that were displayed on the screen at the moment. The culmination of the scare is that all this embarrassing “evidence” will be allegedly sent to the target’s contacts list grabbed from email, WhatsApp, Telegram, and Skype unless they cough up a ransom for nondisclosure. The amount can be anything from 900 to 2,000 USD, depending on the impostor’s greed or whim.
Pegasus spyware may re-infect your Mac multiple times unless you delete all of its fragments, including hidden ones. Therefore, it is recommended to download Combo Cleaner and scan your system for these stubborn files. This way, you may reduce the cleanup time from hours to minutes.
Download Now Learn how Combo Cleaner works. If the utility spots malicious code, you will need to buy a license to get rid of it.Pegasus spyware claims for extra pressure
To make sure that the narrative doesn’t sound far-fetched, the ne’er-do-wells in charge of the “Hello pervert” email scam leverage several persuasiveness tricks. First, they claim that the user’s device is contaminated with Pegasus, a “spyware program that installs on computers and smartphones and allows hackers to monitor the activity of device owners”, as the message goes. Well, here is some wiki info on the point so that you get the bigger picture: Pegasus is a real high-profile strain of malicious code that can infect Android and iOS devices. Its early development dates back to 2016 and has been attributed to an Israeli cyber-intel company focused on surveillance technology. This questionably ethical project is reportedly a work in progress, and the culprit has since evolved considerably in terms of attack vectors and user snooping capabilities.
However, a few facts about Pegasus dispel the very idea behind the “Hello pervert” scam. One is that it only runs on mobile devices, whereas the email under scrutiny mentions computers as well. Another aspect is that it’s a powerful spyware program whose reported uses never went beyond surveillance initiatives of iron-fisted government regimes. The chance is close to zero that its source code has ended up in garden-variety fraudsters’ hands. Plus, you won’t be in the crosshairs unless you are a political dissident, business executive, investigative journalist, or a human rights activist. Judging from the demographics of the sextortion scam, none of that is the case. The takeaway is that the Pegasus element of the bait is all bark and no bite, so there’s no need to worry.
Other intimidation techniques in play: Creepy but vanilla
To perplex the would-be victims who realize the empty threat of spyware, the latest derivative of the “Hello pervert” scam has no more trump card up its sleeve that might pose tangible risk. The email can mention a password for one of the user’s personal accounts. To top it off, this secret string can relate to an active account, although in most cases it’s an old one. Either way, this can create a false sense of legitimacy. Why false? Because it’s a password obtained from a data breach incurred by a web services provider – unfortunately, these types of incidents are happening all the time and they result in the exposure of credentials belonging to millions of people.
Worse yet, the data dumped on the dark web can be verbose enough for crooks to determine the person’s whereabouts, whether through immediate physical address or IP address details that correlate with geolocation. The scammers weaponize this knowledge by fetching a picture of the victim’s home or neighborhood off of a publicly available service such as Google Maps. Again, while it takes a bit of time and effort to personalize the “Hello pervert” scam email that way, there is no indication that you are dealing with a professional extortionist who has outstanding hacking skills. It’s just an aftermath of a past breach that spilled some of that information.
To recap, this scam attempt is a nice try, but it’s a bluff. Your device doesn’t have Pegasus on board, nor do the swindlers have the footage they purport to. The campaign is well-tailored and reminiscent of spear-phishing backed by thorough research, but all the threats it includes are false. One red flag that potentially deserves extra insights is the presence of a password (whether an old or an active one) in the email. This can be a symptom of a leaked personal footprint resulting from a breach. Think of it as a call to action and consider changing all your passwords. To err on the side of caution, it’s also recommended to check your device for malware that might have facilitated that leak of credentials, in the first place.
Check your Mac for malware related to the Pegasus spyware email scam
The steps listed below will walk you through the removal of this malicious application. Be sure to follow the instructions in the specified order.
Expand the Go menu in your Mac’s Finder bar and select Utilities as shown below.

Locate the Activity Monitor icon on the Utilities screen and double-click on it.

In the Activity Monitor app, look for a process that appears suspicious. To narrow down your search, focus on unfamiliar resource-intensive entries on the list. Keep in mind that its name isn’t necessarily related to the way the threat is manifesting itself, so you’ll need to trust your own judgement. If you pinpoint the culprit, select it and click on the Stop icon in the upper left-hand corner of the screen.

When a follow-up dialog pops up asking if you are sure you want to quit the troublemaking process, select the Force Quit option.

Click on the Go menu icon in the Finder again and select Go to Folder. You can as well use the Command-Shift-G keyboard shortcut.

Type /Library/LaunchAgents in the folder search dialog and click on the Go button.

Examine the contents of the LaunchAgents folder for dubious-looking items. Be advised that the names of files spawned by malware may give no clear clues that they are malicious, so you should look for recently added entities that appear to deviate from the norm.
As an illustration, here are several examples of LaunchAgents related to mainstream Mac infections: com.updater.mcy.plist, com.avickUpd.plist,and com.msp.agent.plist. If you spot files that don’t belong on the list, go ahead and drag them to the Trash.

Use the Go to Folder lookup feature again to navigate to the folder named ~/Library/Application Support (note the tilde symbol prepended to the path).

When the Application Support directory is opened, identify recently generated suspicious folders in it and send them to the Trash. A quick tip is to look for items whose names have nothing to do with Apple products or apps you knowingly installed. A few examples of known-malicious folder names are ProgressSite and IdeaShared.

Enter ~/Library/LaunchAgents string (don’t forget to include the tilde character) in the Go to Folder search area.

The system will display LaunchAgents residing in the current user’s Home directory. Look for dodgy items related to Search Marquis redirect virus (see logic highlighted in subsections above) and drag the suspects to the Trash.

Type /Library/LaunchDaemons in the Go to Folder search field.

In the LaunchDaemons path, try to pinpoint the files the malware is using for persistence. Several examples of such items cropped by Mac infections are com.pplauncher.plist, com.startup.plist, and com.ExpertModuleSearchDaemon.plist. Delete the sketchy files immediately.

Click on the Go menu icon in your Mac’s Finder and select Applications on the list.

Find the entry for an app that clearly doesn’t belong there and move it to the Trash. If this action requires your admin password for confirmation, go ahead and enter it.

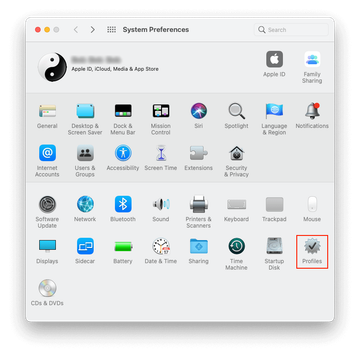
Expand the Apple menu and select System Preferences.


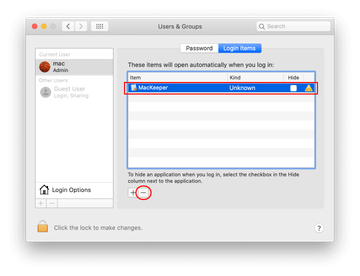
Proceed to Users & Groups and click on the Login Items tab.

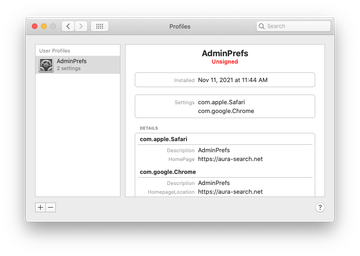
Now select Profiles under System Preferences. Look for a malicious item in the left-hand sidebar. Several examples of configuration profiles created by Mac adware include TechSignalSearch, MainSearchPlatform, AdminPrefs, and Safari Settings. Select the offending entity and click on the minus sign at the bottom to eliminate it.
Get rid of "Hello pervert" virus in web browser on Mac
To begin with, the web browser settings taken over by the "Hello pervert" virus should be restored to their default values. Although this will clear most of your customizations, web surfing history, and all temporary data stored by websites, the malicious interference should be terminated likewise. The overview of the steps for completing this procedure is as follows:
- Remove "Hello pervert" virus from Safari
Open the browser and go to Safari menu. Select Preferences in the drop-down list.

Once the Preferences screen appears, click on the Advanced tab and enable the option saying “Show Develop menu in menu bar”.

Now that the Develop entry has been added to the Safari menu, expand it and click on Empty Caches.

Now select History in the Safari menu and click on Clear History in the drop-down list.

Safari will display a dialog asking you to specify the period of time this action will apply to. Select all history to ensure a maximum effect. Click on the Clear History button to confirm and exit.

Go back to the Safari Preferences and hit the Privacy tab at the top. Find the option that says Manage Website Data and click on it.

The browser will display a follow-up screen listing the websites that have stored data about your Internet activities. This dialog additionally includes a brief description of what the removal does: you may be logged out of some services and encounter other changes of website behavior after the procedure. If you’re okay with that, go ahead and click on the Remove All button.

Restart Safari
- Remove "Hello pervert" in Google Chrome
Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down

When on the Settings pane, select Advanced
Scroll down to the Reset settings section.

Confirm the Chrome reset on a dialog that will pop up. When the procedure is completed, relaunch the browser and check it for malware activity.

- Remove "Hello pervert" from Mozilla Firefox
Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).


When on the Troubleshooting Information screen, click on the Refresh Firefox button.

Confirm the intended changes and restart Firefox.
Fix Mac malware issues using Combo Cleaner removal tool
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove "Hello pervert" virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the "Hello pervert" issue using Combo Cleaner:
Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove "Hello pervert" threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.
