With the release of iOS 14, users can personalize the look and feel of their iPhone home screen, but this could be a source for security issues.
The latest version of Apple’s operating system for mobile devices comes with awesome UI tweaks, important vulnerability patches, Siri improvements, Safari privacy enhancements, and many more bells and whistles under the hood. One of the features most welcomed by iPhone fans is that the home screen can finally be personalized via widgets, custom wallpapers, and favorite apps library. These functionalities have been gaining a great deal of traction among users, many of whom are posting screenshots of their nifty new home screen layouts on social networks. However, the whole hype around this novelty eclipses potentially serious security and privacy risks. By sharing an iPhone home screen, a user unwittingly discloses information that might be mishandled by online scammers to prep and execute effective phishing attacks or malware attacks.
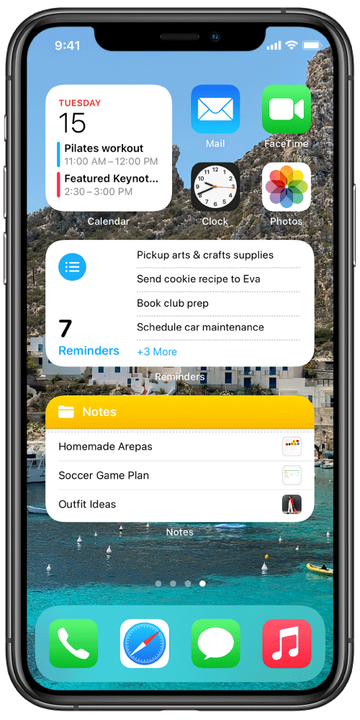
To better grasp the security and privacy implications of the iPhone home screen personalization feature, let’s go over the new capabilities it brings to one’s fingertips. It allows a user to add widgets that reflect the essential data from most-used apps. In this regard, the Smart Stack service can come in handy as it intelligently displays the appropriate widgets based on the current location, time of the day, and activity. The other perks include the option to set a personal photo as the wallpaper, rearrange pages, and quickly open apps that are most frequently accessed.

New iPhone home screen includes sensitive data
The reverse side of this nifty overhaul is that the iPhone home screen may reveal personally identifiable information (PII) that should be kept away from prying eyes. For instance, the weather widget displays a user’s location, and the music widget reflects their favorite audio tracks. These details aren’t as verbose as the info that can be retrieved by looking at widgets for apps such as Notes and Reminders. Furthermore, the home screen displays apps that the person uses the most.
By knowing what a user’s iPhone home screen looks like, a competent cybercriminal may be able to connect the dots and extract a lot of information for orchestrating an e-fraud. Social engineering is the pivot point of potential exploitation in this case. One of the plausible scenarios is as follows: if your home screen includes the Amazon Prime Video icon (which means you use it a lot), an adversary may concoct an email impersonating that service and supposedly offering a free subscription or a discount. The message will lead to a credential phishing page, where every piece of sensitive information being entered will go to the con artist.
If a malefactor finds out that you use an app that has a known or zero-day security vulnerability, they may try to send you a payload that exploits that loophole and installs iOS malware on your device or opens a backdoor for future abuse. All in all, there are plenty of attack vectors hinging on that info. Thankfully, it’s easy to steer clear of trouble – simply avoid uploading images of your iPhone home screen to publicly available resources such as social media.
