Hackers claim to have discovered a flaw in several generations of the Secure Enclave chip that cannot be fixed because it’s exploitable at the hardware level.
Secure Enclave, the proprietary technology used by Apple to step up the security of users’ data, is front-page news once again – this time, in a negative context. In late July 2020, a Chinese hacking group dubbed the Pangu Team reported a previously unknown loophole in this chip that puts all sensitive information stored on a device at risk. Given that Secure Enclave is used on a vast range of modern Apple products, from iPhone and iPad to Apple Watch, HomePod, Apple TV HD, and Macs with T1 or T2 co-processor onboard, the impact of this discovery can be mind-boggling. By compromising the hardware facet of the tech, attackers may be able to access the most valuable data belonging to a user, including passwords, Apple Pay credentials, and biometric authentication details.

What does Secure Enclave do, anyway?
To grasp the breadth and depth of the issue, it makes sense dwelling on the functional aspects of Secure Enclave. Technically, it is a security architecture manifested as a standalone chip in most Apple devices released since 2013. The underlying co-processor is isolated from the rest of the system so that no app can possibly tamper with the information it handles. Its goal is to store every bit of sensitive data in an encrypted form, with the private keys being inaccessible by any entity other than Secure Enclave itself.
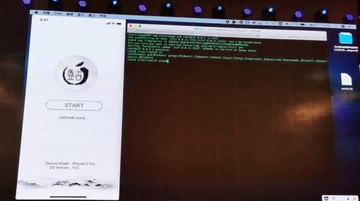
The info secured this way spans, among other things, your passwords, Touch ID and Face ID related biometrics, and credit card details tied to the Apple Pay feature. Even if a device is jailbroken, the data safeguarded by Secure Enclave stays protected from interference. Essentially, this is an autonomously operating, closed environment tasked with ensuring that the most valuable information is off limits to third-party code.
Why does the exploit make a difference?
Because Secure Enclave is the fundamental link in the user data integrity implementation by Apple, anything that undermines its defenses is a huge concern. For the record, this isn’t the first time hackers have identified imperfections in this technology. Back in 2017, a crew of programmers managed to decrypt the associated firmware. However, this attack vector didn’t entail access to the private keys, and therefore users’ important information was safe regardless.
The recent findings of the Pangu Team hackers are potentially much more unnerving. Their exploit allegedly allows an adversary to obtain private keys. Furthermore, the bug circumvents Secure Enclave defenses at the hardware level, which means that Apple’s efforts to patch it down the road may turn out futile.
According to the report, the chips susceptible to this vulnerability include A7 through A11 Bionic. Newer co-processors (A12 and A13) are in the clear. No additional details are known about the latest exploit at the time of this publication. By the way, since the Pangu Team never makes its hacking tools public, it might stay that way. The other good news is that the exploit cannot be weaponized remotely. So, even if a perpetrator is “armed” with it, they can do no harm unless they have physical access to a vulnerable device.