Get the lowdown on cryptojacking campaigns targeting Mac computers, the history of this phenomenon and the most massive outbreaks of such malware to date.
Any new technology that gains significant worldwide popularity is fated to be abused by threat actors in the long run. A major flip side of Bitcoin and other cryptocurrencies, with all their numerous benefits for users, circles around the immense efforts of cybercriminals to steal coins or otherwise get hold of virtual funds whose value is constantly soaring. Unfortunately, black hats have had some tangible success doing it.
It is common knowledge that new units of cryptocurrency come into existence via a routine called mining. It designates a process where computation power is leveraged to perform complex mathematical calculations for verifying the validity of transactions on the blockchain, a decentralized cryptocurrency ledger keeping record of all fund transfers. Normally, people who are up to the mining business invest in costly equipment with high data processing capacity and join the worldwide coin rush. This type of activity is legit, and it’s gearing up for a rise.

As always, online perpetrators go the easy route. They have come up – and keep coming up – with methods to harness other people’s CPU and GPU for coin mining. This phenomenon is referred to as cryptojacking. The target users are meanwhile unaware of this exploitation going on behind their backs. In order to pull off attacks of this sort, the adversaries leverage malicious code. Having taken root on a host, the malware will configure the system to dedicate most or all of its processing power to the mining job.
Mac computers have been conventionally considered safer than Windows in terms of combatting harmful code. When it comes to cryptojacking, though, machines running macOS are pretty much the same low-hanging fruit as their Windows counterparts. Here’s some outright evidence of this disconcerting resemblance: the second most common Mac malware strain is a stealthy cryptocurrency mining application.
DevilRobber, an oldie that keeps evolving
The newsmaking cyber culprit called DevilRobber is also known to security community under other aliases, including OSX.Coinbitminer and Miner-D. It gained notoriety for being one of the most prolific samples of Mac malware to date, having been discovered in October 2011 and still boasting active circulation. The issue was so big and serious back then that Apple had to release ad-hoc security updates to address this outbreak.
The infection featured a robust, well-thought-out architecture from the get-go and was a unique combo of several different threat categories. It had characteristics of a Trojan as it spread via booby-trapped BitTorrent trackers. Its backdoor facet consisted in the ability to communicate with the Command & Control server. The data stealing hallmarks revolved round the fact that it could pilfer victims’ personal data and Bitcoin, with subsequent exfiltration of the sensitive information to the crooks-maintained C2.
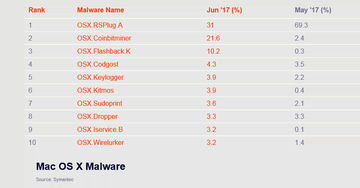
Having taken its niche on the Mac malware landscape, this pest hadn’t shown any significant spikes until 2017. According to malware analysts’ findings, the number of DevilRobber detections skyrocketed to 21.6% in June 2017 versus 2.4% in May. This leap forward made it the second most widespread Mac infection, with the first position occupied by the infamous DNS changer dubbed RSPlug.
The likely reason why the numbers increased nearly tenfold in only a month was because the price of Bitcoin and other major cryptocurrencies started to soar, so surreptitious mining quickly because a much more profitable activity. Furthermore, mining altcoins such as Monero and Ethereum shaped up to be a trend outperforming Bitcoin-borne environment in this context.
While keeping the original source code, the malefactors behind DevilRobber made some tweaks to the infection before it went viral last June. Its mining potential now covers a broader range of cryptocurrencies. It still tends to enter Mac computers alongside legitimate applications, sticking to a bundling-based modus operandi. When on board a machine, it drives the GPU usage to its peak and keeps it there. To add insult to injury, this mod of DevilRobber steals data related to cryptocurrency wallets, harvests the victim’s Safari history details and keychain files.
The scourge of in-browser mining
Cryptojacking reached new unprecedented heights with the release of the game-changing Coinhive script. It is a JavaScript entity that mines Monero (XMR) cryptocurrency. Coinhive stands out from the crowd as it can be integrated in a website. What this means is, every Windows or Mac user visiting a web page with this script embedded in it will have a portion of their machine’s CPU allocated to mine Monero for the site owner. The duration of this routine matches the time the user spends on that particular page.
This technology has revolutionized traffic monetization, allowing webmasters to make a living without engaging in ad schemes that can be obtrusive. Moreover, it isn’t illegal as long as site admins notify their visitors properly.
Cybercrooks, however, have found workarounds to leverage the likes of Coinhive in a clever, yet clearly malicious way. All it takes is injecting the script into a popular website covertly. Doing so is mostly a matter of good ol’ hacking. The interesting part is that the perpetrators don’t necessarily have to compromise specific websites to reach their goals. It suffices them to poison a certain third-party component, such as a widget, and thereby involve all the sites using this component in the fraudulent mining campaign.
This is precisely what happened in the BrowseAloud widget incident from February 2018. Hackers stealthily added the Coinhive script to this product and were able to drag more than 4,200 sites into an underhand mining wave. This tactic ended up so successful due to the popularity of BrowseAloud. It is a site accessibility widget delivering speech, translation and reading features. Thousands of online resources run this script to extend their reach, including UK and U.S. government websites such as manchester.gov.uk, gmc-uk.gov, and uscourts.gov.
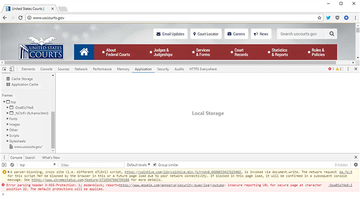
The perpetrating component of this widget used 40% of the hosts’ CPU, therefore some victims might have failed to identify the fraud when visiting a compromised website. Due to Coinhive’s privacy practices, it is impossible to determine accurately how much Monero the hackers earned this way. However, given the high-profile sites involved, the amount must be significant.
A similar third-party compromise took place around Thanksgiving 2017. Crooks were able to inject the Coinhive miner into LiveHelpNow, a widely used site plugin delivering live chat feature. More than 1,400 websites were hit in the aftermath of this attack, including big online retail stores such as Everlast and Crucial. Unlike the BrowseAloud case, this time the script was configured to use up 100% of a visiting machine’s processing power.
Some site owners even go the slippery cryptojacking route as their revenue model. For instance, the U.S. news portal Salon.com has adopted this tactic since February 2018. Here’s how it works: if the website identifies that a visitor – Windows or Mac user – has disabled ads in their browser, it will trigger the Coinhive script to leverage spare CPU resources of that person’s computer for Monero mining. As opposed to the incidents above, though, there is no hacking involved here. Salon.com displays a permission request before it starts the in-browser mining process. Hopefully, it will stay that way.
All in all, in-browser cryptocoin mining is a mixed blessing. On the one hand, it helps webmasters get their hard work rewarded. On the other, it is the best thing since sliced bread to hackers. Obviously, this unsettling duality isn’t the way Coinhive intended for their brainchild to evolve. And yet, it takes cryptojacking to a whole new level.
Cryptojacking prevention tips for Mac
If you are a Mac user and you don’t want your computer’s CPU and GPU to play into somebody else’s hands, there are some simple, best practice tips to stay away from the cryptojacking craze.
• Install a browser plugin that blocks cryptocurrency miners. Look for one that specifically supports your preferred web browser (Safari, Chrome, Firefox, etc.).
• Disable JavaScript in your browser. This technique will stop unauthorized cryptocoin mining in its tracks, because tools like Coinhive are based on JavaScript. Be advised, though, it may affect your overall web surfing experience as some site content may not be rendered.
• Use a reputable Mac antimalware app with Internet security module on board. Make sure the solution monitors web traffic in real time and produces alerts on cryptojacking scripts.
• Apply macOS patches as soon as they are released.
These methods work proactively and are highly recommended in light of the rampant cryptojacking epidemic. Being able to identify such an attack when it’s already underway is also very important. Permanent sweating of your processor is a major red flag to look out for. Be sure to peak in on your Activity Monitor once in a while and check the current CPU consumption. If it’s stuck at 100% or simply much higher than usual for an unreasonably long time, spot the process that’s eating up system resources and quit the culprit right away. A little bit of extra prudence should help you outwit cybercrooks and unscrupulous site owners.
