OSX.Proton, the notorious info-stealing malware, has made a reappearance via a campaign involving booby-trapped editions of the popular Elmedia Player app.
The unscrupulous devs of the ill-famed OSX.Proton malware have recently proven that they’ve got a novel proliferation mechanism up their sleeve. The current generation of this contagion, referred to as OSX.Proton.C, is making the rounds in quite an unusual fashion. Specifically, it arrives at Mac computers with a trojanized copy of Elmedia Player, a free multimedia solution by Eltima Software. The situation gets yet more disconcerting due to the fact that users were downloading the weaponized app from Eltima’s official website for an unknown period of time. The trick is, when a would-be victim opens the hijacked software it looks just like the benign edition. However, malicious processes running in the background cause a great deal of security and privacy issues.

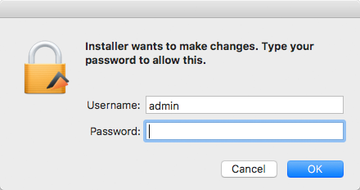
There is a red flag, though, signaling that the user is dealing with a rogue build of Elmedia Player. It is a popup request asking for the victim’s admin password when the software is first triggered, which is something the genuine app doesn’t display. If these privileges are granted, things start to quickly get out of hand, and the worst part is that the user won’t even know it. A new entry named com.Eltima.UpdaterAgent.plist will appear under /Library/LaunchAgents. This process gets triggered every time the contaminated Mac boots up so that the malicious effect persists.
The main vector of OSX.Proton’s activity is reconnaissance. It harvests various information about the computer and the user. These include operating system details, such as full name of the current user, time zone, hardware serial number, and hostname. The infection also collects personally identifiable information relating to web browsers, including Safari, Chrome, Firefox and Opera. In particular, it zeroes in on website login credentials, cookies, browsing history and the like. To add insult to injury, the OSX.Proton malware compromises keychain and 1Password data in an attempt to get hold of the victim’s stored passwords. Yet another unsettling effect is the theft of information associated with cryptocurrency wallets, including Bitcoin Core, Electrum, and Armory.
The impact of OSX.Proton can, obviously, get really bad. The threat actors obtain a sufficient volume of data to steal cryptocurrency and breach banking accounts, and that’s only part of the effect. Having discovered this virus on a Mac, the user should change passwords for all online accounts immediately. But before, OSX.Proton needs to be removed.
OSX.Proton malware manual removal for Mac
The steps listed below will walk you through the removal of this application. Be sure to follow the instructions in the order specified.
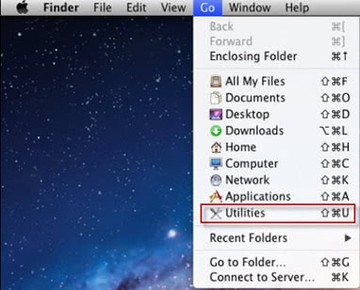
• Open up the Utilities folder as shown below
• Locate the Activity Monitor icon on the screen and double-click on it
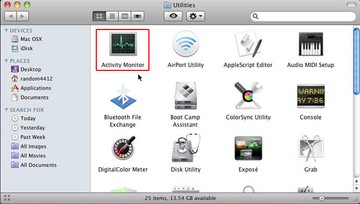
• Under Activity Monitor, find the entry for UpdaterAgent, select it and click Quit Process
• A dialog should pop up, asking if you are sure you would like to quit the troublemaking process. Select the Force Quit option
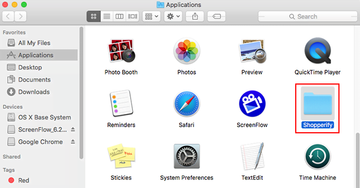
• Click the Go button again, but this time select Applications on the list. Find the entry for UpdaterAgent on the interface, right-click on it and select Move to Trash. If user password is required, go ahead and enter it
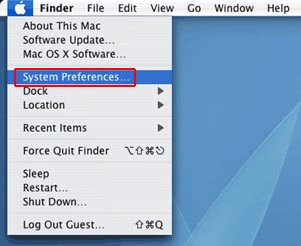
• Now go to Apple Menu and pick the System Preferences option
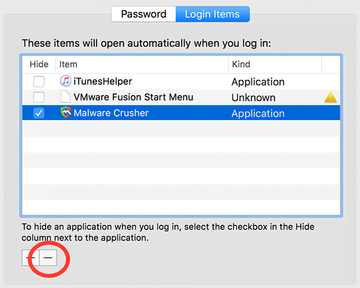
• Select Accounts and click the Login Items button. The system will come up with the list of the items that launch when the box is started up. Locate UpdaterAgent there and click on the “-“ button
Use automatic tool to uninstall OSX.Proton malware from your Mac
Unless you are a power user, you run the risk of failing to find and delete some components of this infection on your own. Overlooking dodgy LaunchAgents, LaunchDaemons, and malicious configuration profiles means that the threat will continue to cause problems. A more efficient alternative to manual cleanup is to use MacBooster 8, an application that will scan your Mac for issues and fix them automatically.
The app comes with a competitive toolkit that includes Virus & Malware Scan as well as a decent range of optimization features. Therefore, not only does it identify and vanquish mainstream Mac viruses but it also releases disk space and memory so that your computer gets a performance tune-up. Here’s how to go the route of OSX.Proton malware removal with MacBooster:
Download and install MacBooster 8.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Pro version of MacBooster.
Open the app. When on the System Status screen, click the Scan button to check your Mac for viruses, junk files, and memory hogs.

Once the scan is completed, inspect the report to see what security threats and performance issues have been found. To get rid of the detected items, click the Fix button at the bottom.

As an extra step, you might want to make sure that the OSX.Proton malware infection leftovers are no longer riddling your web browser. This can be the case in an adware scenario. Proceed to the Privacy Protection feature in the left-hand sidebar, select the default browser in the list, and click the Clean button.

In case your web browser is still acting up, follow the steps provided in the previous section of this guide to get rid of the adverse web surfing interference for good.
