Get a quick fix for the unlock.device@mail.com screen lock problem on iPhone, iPad or MacBook and learn how to avoid such frauds in the future.
Robust security architecture is one of the key benefits of using an Apple device. It explains how come iOS and Mac users aren’t targeted nearly as heavily as Windows aficionados. Applications are thoroughly checked for suspicious behavior before they reach the official software download sources. Unfortunately, though, everything connected to the Internet is potentially vulnerable, and cybercrooks sure know it. They have come up with a workaround for these defenses, turning a useful feature provided by Apple against end users. The fraud scheme to be dissected in this article does not involve any installation of booby-trapped apps or obfuscated infiltration of perpetrating code. A lock screen on iPhone or Mac that coerces the user to write to unlock.device@mail.com is nothing but a defiant instance of weaponizing what’s meant to help.
So here’s the anatomy of this attack. At the first stage, remote hackers get hold of one’s Apple ID credentials. There is an ongoing discussion regarding the methodology of this theft – they felons might brute-force a potential victim’s iCloud account password, or they take advantage of a dump of such sensitive information that may have recently taken place in the cybercriminal underground. One way or another, somebody with bad intensions signs into a targeted user’s iCloud dashboard and then enables a feature called “Find My iPhone”. When used in a benign way, this function allows any user to track the location of their lost or stolen iPhone, iPad, iPod Touch, MacBook, AirPod, or Apple Watch. It also provides an option of locking a device remotely and defining a custom message to be shown on the home screen.
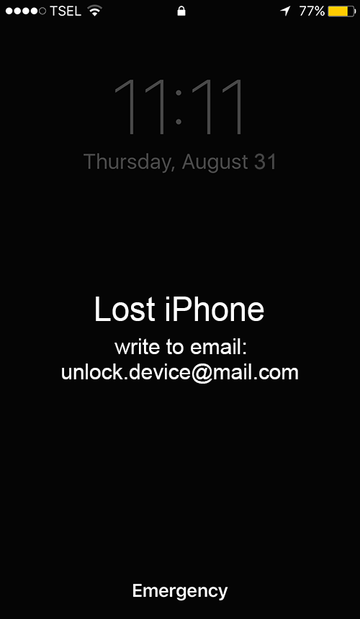
Next on the attack workflow, the ne’er-do-wells go ahead and use the functionality of “Find My iPhone” app to their own advantage. Specifically, they remotely lock down the gadget and make it display the following text on the screen, “Lost iPhone. Write to email: unlock.device@mail.com.” A different reported variant of the message is as follows, “Wrong passcode. Try again. Write to email: unlock.device@mail.com.” An obvious reaction of the plagued user is to try and sort things out by shooting a message to the indicated email address. The auto-reply goes, “Hello. Your device is locked. To activate the device, pay $50 (USD) to the Bitcoin address {attackers’ BTC address}. After payment inform us and we will send the passcode. If we do not receive payment within 24 hours, your devices will be blocked.”
Again, although this extortion is reminiscent of ransomware, there is no virus on board the iPhone, Mac or whatever device has been locked. It’s just online criminals abusing a benign feature. Fortunately, the fix isn’t too hard. Look below for details.
Unlock iPhone hijacked via unlock.device@mail.com hoax
As per the anatomy of this con, an efficient workaround is to reset the iCloud login credentials. To do this, go to iforgot.apple.com on a computer or other non-infected device and follow the steps below:
• Select the option that says "Forgot Apple ID?"

• Enter the requested details, including your first name, last name and email address and click Continue.

• Fill out the personally identifiable information as instructed and answer security questions you had configured when creating your Apple ID. Alternatively, you can select the "Get an email" option and receive an email to reset your password.

• Follow any further directions until you reset your iCloud password. In some cases, you may have to give Apple Support a phone call to explain your issue and get the reset job completed.
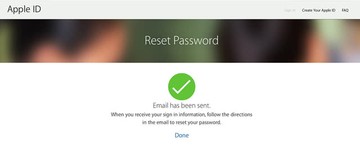
• Use the new password to regain access to your iOS or macOS device.
Protect your iPhone / iPad from being locked
Infections like the unlock.device@mail.com locker can obtain your sensitive credentials through unprotected connections. Logging into public Wi-Fi networks and visiting compromised sites can get the gadget exposed to malware and man-in-the-middle attacks. It’s therefore strongly recommended to use automatic protection during web surfing.
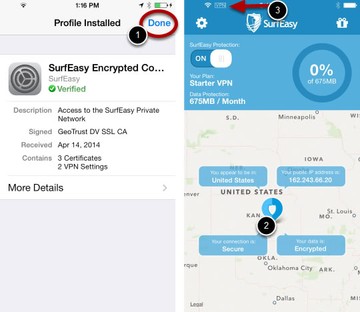
1. Download and install SurfEasy VPN (read review). This app accommodates Wi-Fi security as well as privacy and identity protection features
2. Make sure SurfEasy Protection is turned on throughout Internet browsing sessions. The application will encrypt all traffic, prevent ad tracking, anonymize online activities and secure the iOS device when it’s connected to Wi-Fi hotspots.