Read previous part: Reverse Engineering Mac Malware
Sarah Edwards provides an extensive review of Mach-O binaries, including the types thereof, file signatures, and tools applicable to reverse engineer them.
So, Mach-O – all the Macs use Mach-O. This is your PE executable of the Mac world, however it doesn’t look like a PE executable at all, not even close.
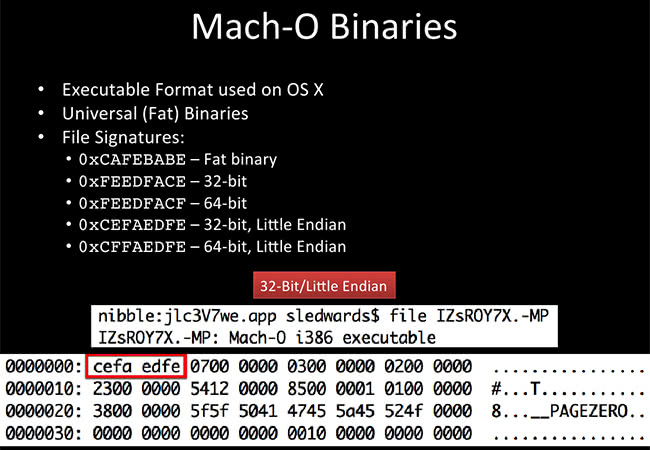
Mach-O binaries may have one or more architectures associated with them. If they have two or more architectures, they are called “fat binaries”, which I find hilarious. It gets even better with all of the tools that we use. So it can have a 32-bit executable and a 64-bit executables. It can have these executables all packed into the same executable format, and the system will determine which one to execute, depending on what type of system you have. The exact one up here is a 32-Bit/Little Endian. All of these listed at the top are different file signatures, so if you are doing file signature analysis, be sure to look more than for just ‘cefa’, which is kind of a well-known signature. There are also four more to look for, so make sure you’re looking for all of them.
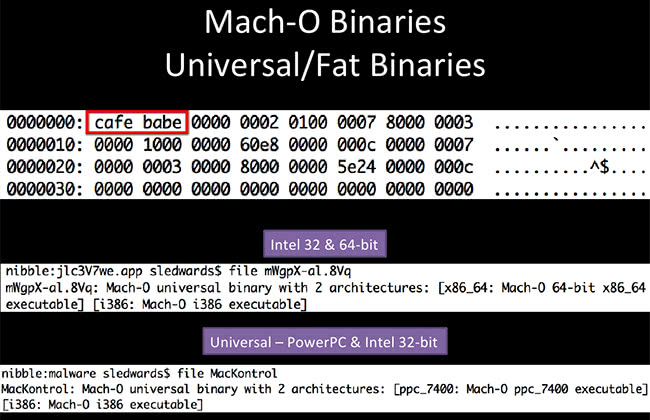
On the example here we have ‘cafe babe’, which is a universal/fat binary. On the middle image - this is a Crisis example - you can see it has a 32- and 64-bit executable in there. It’s a universal binary with two architectures, x86 and i386. And MacKontrol – this one has a PowerPC component as well as Intel 32-bit, so multiple architectures, kind of neat.
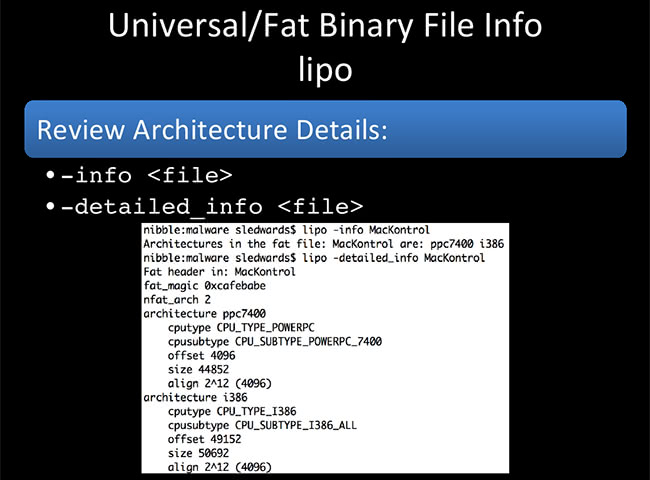
lipo – this is how you work with the fat binaries. It’s an easy command to remember. lipo lets you review the architecture details, which is shown on the screenshot. MacKontrol is used here, saying yes, okay, I have a PowerPC and an i386, which is 32-bit. If you do a ‘-detailed_info’, you get a little bit more information about the CPU: cputype, the offset in the binary where the actual binary starts. There are two binaries; first one starts at 4096, second one starts at 49152.
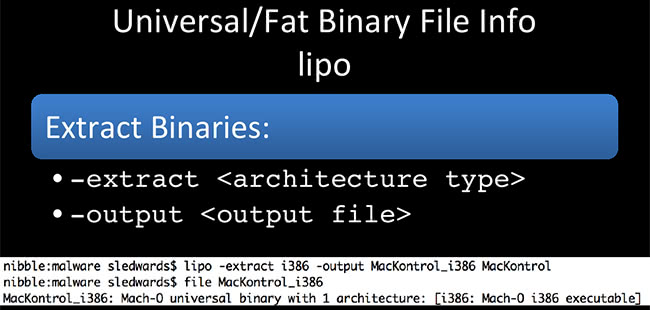
We can actually extract the executables with lipo: ‘-extract <architecture type>’ and ‘-output <output file>’. On the screenshot I have MacKontrol again, and I want to extract the 32-bit component of it. I extracted that with lipo: ran the file command to make sure I’d have one executable with one architecture, so now I can throw that into IDA and convert it.
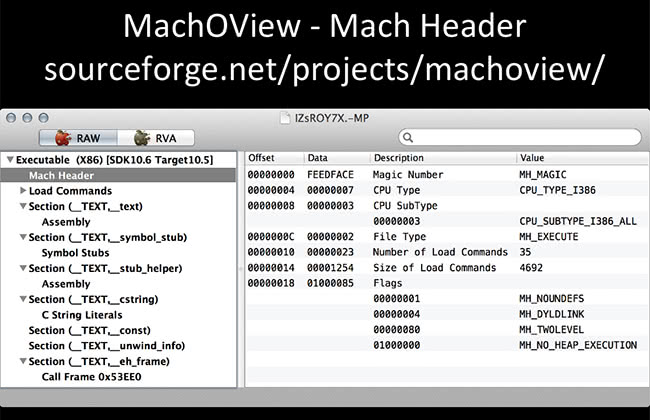
During this whole presentation I’m going to be showing you command line stuff and GUI stuff. I try to have one of each for all the analyses I’m going to be looking at. Some people are more comfortable in a GUI, some people are more comfortable in a command line, so I try to provide that for both parties to have fun. MachOView is a great application to view Mach-O executables. On the screenshot here I have the Mach Header, it has a lot of the same information that we just saw in lipo: architecture information, offsets, this one has flags and all the other static stuff you might want to know as a hardcore reverser.
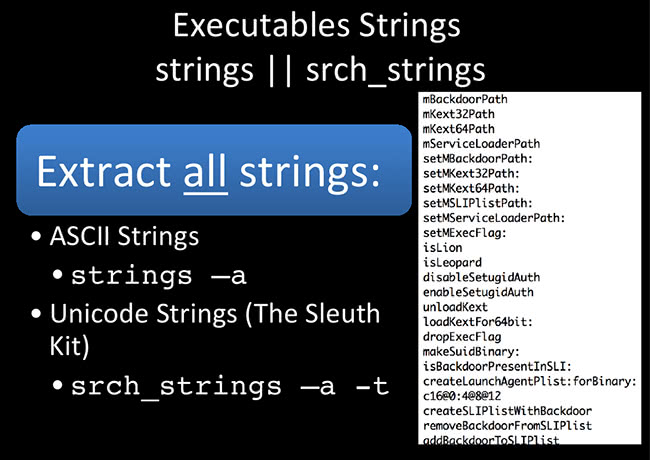
Strings – everybody loves strings. I don’t know any reverser that doesn’t just run a quick ‘strings’ on an executable once they get it, just to get the gist of what’s going on. So, up here I have ‘strings’ and ‘srch_strings’; ‘srch_strings’ is from The Sleuth Kit. The native ‘strings’ on a Mac OS X system does not do Unicode strings. Be aware of that, because there might be some strings that are missing. That’s why I gave the second option of ‘srch_strings’, because that will also get all the Unicode strings and all the ASCII strings. You should be good to go with that. On the example here, you get a lot of function names and variable names. This particular one, I believe, is from Crisis; it checks for ‘isLion’ and ‘isLeopard’, ‘setMKext32Path’ (kernel extension path), ‘unloadKext’, so it’s obviously doing something with the kernel extension – good things to know and good things to look for.
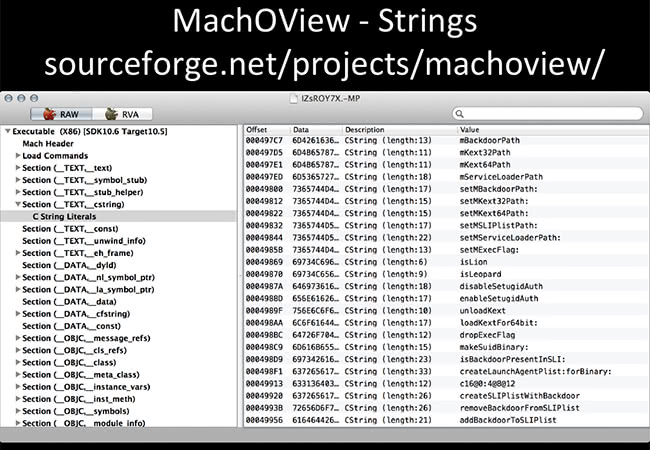
In the MachOView, I found the exact same strings in Mach-O that I found with just the ‘strings’ utility. Again, we have the ‘isLion’, ‘isLeopard’, all the Kext stuff (‘loadKext’, ‘unloadKext’) – same thing, but it’s in a GUI version.
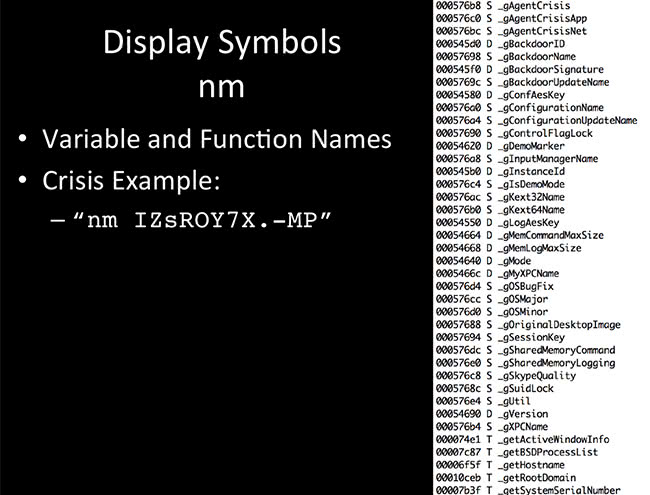
So, symbol table – it’s good so we can view variable and function names. OS X has a native tool called ‘nm’. In most cases you are going to have to install Xcode to get a lot of the problematic utilities like lipo, like nm and stuff like that. I imagine if you are already doing this anyway, you probably already have Xcode installed. Again, this is a Crisis example, using a simple command – nm - you get a whole lot of symbols here. They are symbol names, function names. Again, you get the gist of what might be happening in the binary.
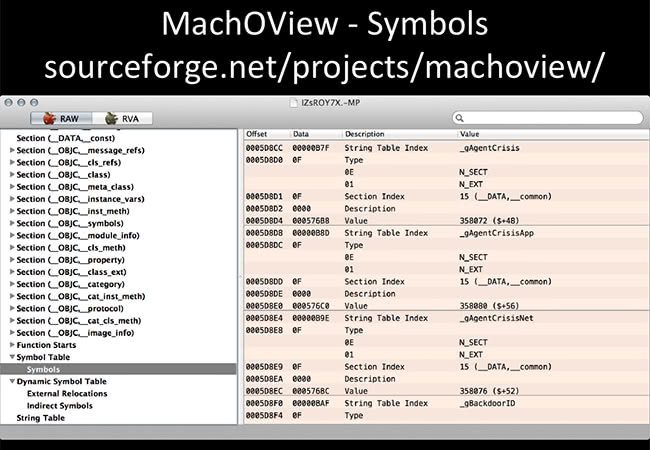
Now the MachOView GUI – same thing here. They have a whole section just for symbol table and symbols. Plus it gives you the offset, it gives you other information. It’s a little bit more verbose than nm is, but same general information.
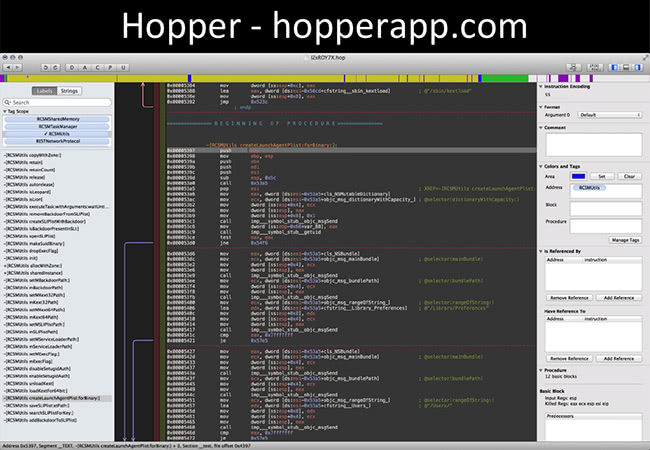
… Which brings me to the Hopper. This is just a screenshot, it’s obviously very difficult to see because it’s dark and it’s a giant screenshot. So, Hopper app – anybody who has used IDA can probably just go right in there, fool around a bit and get used to it. IDA is how much now? 1500? This one is 70 or 80 bucks now; it went up with version 3. The guy actually, I guess, quit his job and now he is doing this fulltime. Dude needs to make some money. So go ahead and buy this, because as far as reverse engineering software goes, this is cheap and it’s good stuff.
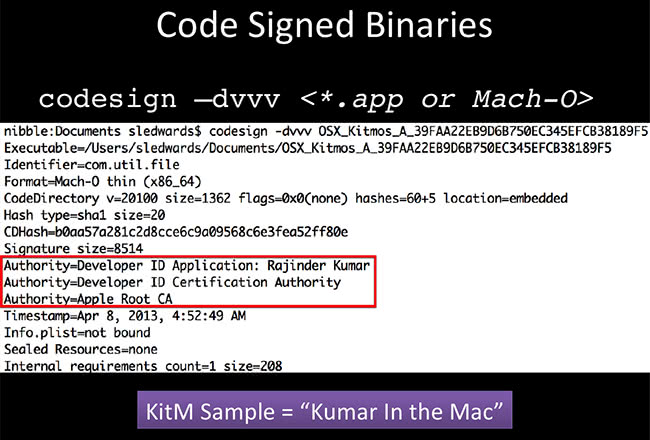
Alright, one thing with Mac that you don’t awfully often see with a lot of Windows executables is code signed binaries. Anything off the App Store and developer stuff – you can sign your binaries. This became an issue with a popular malware called Kumar in the Mac, or KitM. This was actually signed by a developer, which means – and I’ll get into this a little bit later – it was able to bypass Gatekeeper, which is one of the AV products on Mac, so this was a big deal. So use the command, check the code signatures. It actually took Apple quite a long time to revoke that certificate, but there are other ones out there, so be aware. It’s not just Kumar doing this, it’s other folks too, not that I personally know any of them.
Read next part: Reverse Engineering Mac Malware 3 - Dynamic Analysis