Operating systems running on Apple mobile devices and wearables have been updated to address a security gap that may have been used in real-world attacks.
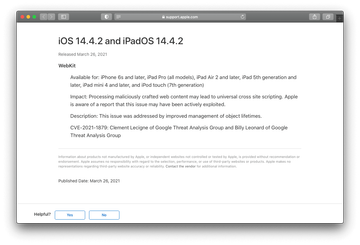
WebKit, the browser engine at the heart Safari, has been in the news a lot lately – not because of its sophistication and efficiency, but due to loopholes in its architecture. Earlier this month, we posted a summary of an arbitrary code execution vulnerability that undermined the security of a vast range of Apple products. The company was quick to release a patch after being notified of the flaw. A series of similar updates took place on March 26, 2021, except that the culprit is a universal cross-site scripting (UXSS) bug in WebKit. The remediation arrived with the new iOS 14.4.2, iPadOS 14.4.2, watchOS 7.3.3, and a refined build of the older iOS 12.5.2.
The now-patched bug is more than a hypothetical threat
So, how exactly does the patch enhance the defenses of the iPhone, iPad, iPod touch, and Apple Watch? According to official security content notes, the WebKit vulnerability was reported by Google Threat Analysis Group. Tracked as CVE-2021-1879, it allows an adversary to pull off a universal cross-site scripting attack and thereby furtively inject malicious scripts into web pages. As a result, the site’s appearance may be misrepresented, or a piece of malware can be executed on unsuspecting visitors’ devices without any red flags being raised.
The worst thing about USXX is that the would-be victim’s browser doesn’t prevent the script from running since it’s incapable of identifying an anomaly in this scenario. One more concern is that Apple admits to the active exploitation of this vulnerability, although there are no details on who is behind these attacks and who may have been targeted. To avoid ending up in the latter category, owners of the supported devices shouldn’t postpone the installation of this recent patch.
