Researchers unveiled a trojanized version of the Xcode development kit dubbed XcodeSpy that gives attackers broad backdoor access to infected Mac machines.
Back in September 2015, developers using Apple’s Xcode development framework found themselves in the crosshairs of malware called XcodeGhost. It was a knock-off variant of the original kit that, when installed on software engineers’ devices, would poison apps compiled by the unsuspecting victim. The worst part was that the culprit didn’t make any changes to the source code and therefore the booby-trapped software flew under the radar of App Store verification mechanisms. More than five years later, a new pest codenamed XcodeSpy splashed onto the scene. It uses a similar style of attack but differs in terms of the infection logic and the promoted payload.
The new supply chain attack
According to analysts at SentinelLabs who discovered this foul play, XcodeSpy currently lurks inside TabBarInteraction, an open-source library uploaded to GitHub by someone nicknamed Potato04. The user is reportedly not in cahoots with malware operators, who were somehow able to plague his or her code with a toxic script. Once extracted, the script creates several Bash shell components and then combines them into a fully-fledged command.
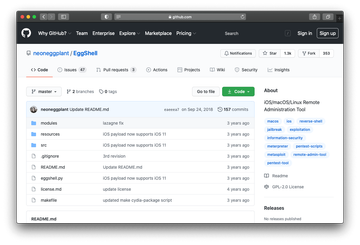
By furtively entering two specially crafted command lines, the malware allows its authors to get a reverse shell on the target Mac. In plain words, it means that the attacker can log into the computer remotely while circumventing firewall protection and authentication barriers. In this scenario, the backstage access is abused to execute a sample of EggShell (detected as OSX/EggShell-A), a post-exploitation tool that establishes and maintains a command line session with a compromised computer. This paves the crook’s way toward downloading or uploading arbitrary files, taking photos with the webcam, pilfering passwords, tracking the victim’s location, and more.
To avoid being hit by XcodeSpy and the EggShell backdoor, users should stick with official app development tools by Apple. Another tip is to configure the firewall solution to filter traffic on port 443 that the makers of this malware use to connect to contaminated systems remotely.
